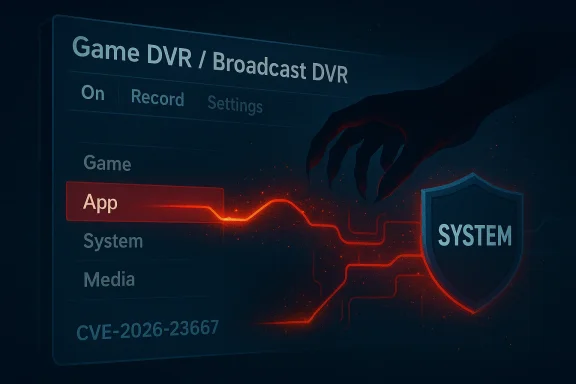
Microsoft’s security tracker has recorded CVE-2026-23667 as an elevation-of-privilege vulnerability in the Windows Broadcast DVR component, and early third‑party aggregators describe the flaw as a use‑after‑free that can be abused by a locally authorized attacker to gain higher privileges on affected hosts. (msrc.microsoft.com)
The Windows Broadcast DVR User Service (commonly surfaced to end users as Game DVR / Xbox Game Bar recording and broadcasting features) has long been an on‑by‑default capability on consumer and many enterprise Windows SKUs. It provides background recording, clip capture, and broadcast APIs for games and UWP apps; the service exposes logic and IPC surfaces that make it a pragmatic attack surface for local exploitation when memory‑safety defects appear. Technical explainers and how‑to guides from multiple Windows‑focused outlets document the presence, behavior, and user‑visible processes for Game DVR and the Broadcast DVR Server process.
Microsoft’s public tracking page for CVE‑2026‑23667 appears in the vendor’s Update Guide (the interactive MSRC entry), and vendor guidance uses a “confidence” metric to communicate how certain Microsoft is about the existence and technical specifics of a recorded vulnerability — a factor that materially affects how defenders should triage, patch, and hunt. The “confidence” explanation itself is part of the MSRC guidance language and is intended to guide operational prioritization. (msrc.microsoft.com)
This entry follows a familiar pattern: Broadcast DVR and related multimedia/game services have been the subject of prior elevation‑of‑privilege records (notably in 2025), where Mtkers documented use‑after‑free class defects in user‑mode Broadcast DVR components. These historical records are important context because they show repeated memory‑corruption risk in the same component family and typical mitigation patterns used by enterprise defenders.
Historical internal patch and alert threads (the community’s patch triage archives) note multiple Broadcast DVR EoP CVEs in 2025 and early 2026 and the operational work patterns used by admins to map the Update Guide entry to per‑SKU KB articles. That institutional history informs how administrators should approach CVE‑2026‑23667: map, test, deploy, and monitor.
Operationally: map the vendor entry to per‑SKU KBs, test and deploy patches urgently, and in the interim apply conservative mitigations (disable Broadcast DVR where possible, enforce least privilege, and enable OS exploit mitigations). Historical patterns in Broadcast DVR advisories and user‑mode use‑after‑free exploitation show that timely patching and host hardening materially reduce attacker success.
Finally, treat the vendor’s confidence signal as a key triage input: when Microsoft marks a high‑impact entry as confirmed, escalate scheduling and communications accordingly; when technical specifics remain intentionally sparse, compensate with accelerated inventory, temporary mitigations, and heightened hunting on endpoints that host the affected service. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Windows Broadcast DVR User Service (commonly surfaced to end users as Game DVR / Xbox Game Bar recording and broadcasting features) has long been an on‑by‑default capability on consumer and many enterprise Windows SKUs. It provides background recording, clip capture, and broadcast APIs for games and UWP apps; the service exposes logic and IPC surfaces that make it a pragmatic attack surface for local exploitation when memory‑safety defects appear. Technical explainers and how‑to guides from multiple Windows‑focused outlets document the presence, behavior, and user‑visible processes for Game DVR and the Broadcast DVR Server process.Microsoft’s public tracking page for CVE‑2026‑23667 appears in the vendor’s Update Guide (the interactive MSRC entry), and vendor guidance uses a “confidence” metric to communicate how certain Microsoft is about the existence and technical specifics of a recorded vulnerability — a factor that materially affects how defenders should triage, patch, and hunt. The “confidence” explanation itself is part of the MSRC guidance language and is intended to guide operational prioritization. (msrc.microsoft.com)
This entry follows a familiar pattern: Broadcast DVR and related multimedia/game services have been the subject of prior elevation‑of‑privilege records (notably in 2025), where Mtkers documented use‑after‑free class defects in user‑mode Broadcast DVR components. These historical records are important context because they show repeated memory‑corruption risk in the same component family and typical mitigation patterns used by enterprise defenders.
What we know right now (verified facts)
- MSRC lists CVE‑2026‑23667 in the Security Update Guide as an elevation‑of‑privilege vulnerability tied to the Broadcast DVR component. This is the vendor‑record of the issue and the authoritative signal that the vulnerability exists. (msrc.microsoft.com)
- Public vulnerability aggregators that index MSRC and vendor feeds describe the issue as a use‑after‑free condition that permits a local, authorized user to escalate privileges. These aggregators include mainstream CVE feeds and threat‑intelligence indexes.
- The vulnerability requires local access to the target host — it is not described as a remote code execution or network‑facing remote vulnerability (the attack vector is local privilege escalation). Aggregators and prior MSRC descriptions for Broadcast DVR defects consistently classify these as local elevation issues.
- Public details remain sparse in vendor‑facing pages (MSRC often publishes an interactive entry that gives impact class, confidence level, and per‑SKU remediation mapping rather than a full exploit write‑up). That protective disclosure posture is typical until vendors ship or coordinate patches. Defenders should therefore rely on the vendor’s entry to map to specific KBs and apply updates as soon as they are available. (msrc.microsoft.com)
Why Broadcast DVR vulnerabilities matter
The Broadcast DVR feature is widely present and, in many builds, enabled by default. It exposes user‑mode services and helper processes that are reachable from an authenticated user session — exactly the condition that makes local privilege escalation (LPE) attractive for attackers who already have a foothold on a host (for example, via credential theft, social engineering, or an earlier remote foothold).- A successful local elevation to SYSTEM (or equivalent) immediately pivots an adversary from user‑level nuisance to complete host control, with lateral movement, persistence, and tamper capabilities.
- Use‑after‑free (UAF) defects often lead to powerful exploitation primitives because they let an attacker substitute attacker‑controlled data at a freed memory location; on Windows, such primitives have historicakernel or SYSTEM‑level code execution or token manipulation. Alerts and past CVEs for similar Windows components show this exploitation pattern repeatedly.
- Broadcast DVR’s multimedia and IPC code paths are non‑trivial, involve complex memory handling, and are frequently patched for stability and security. Repeated fixes in the same component family indicate both complexity and a persistent risk profile. Historical MSRC and community records for Broadcast DVR EoPs in 2025 reinforce this point.
Technical analysis — use‑after‑free and exploitation mechanics (conceptual)
Use‑after‑free (CWE‑416) means a program retains a pointer to a memory object after it has been freed and then later operates on that stale pointer. That old pointer can be coerced into referencing attacker‑controlled memory, yield corrupted state, or trigger code paths that use adversary data in privileged contexts.- Why UAFs are high‑value for privilege escalation:
- They can produce arbitrary read/write primitives when carefully groomed.
- On Windows, UAFs in user‑mode services that cross into privileged APIs or manipulate impersonation tokens can be used to alter process tokens or create SYSTEM level objects.
- Exploitability depends on timing, heap grooming, and any available mitigation like ASLR, DEP, SMEP, CFG, and Kernel‑mode protections.
- Specific to Broadcast DVR:
- The service is designed to accept local requests (IPC or API calls) to start/stop recordings, configure streaming endpoints, and hand off capture buffers.
- If an attacker can trigger a UAF during buffer lifecycle management or callback dispatch, it may be possible to force the service to operate on attacker‑controlled memory or manipulated objects — opening a path to escalate privileges within the host session or as a service account.
What the MSRC “confidence” metric means operationally
Microsoft’s Update Guide includes a confidence metric that indicates how certain the vendor is about:- The vulnerability’s existence (confirmed vs suspected)
- The technical detail available (full root cause vs high‑level classification)
- The amount of exploit‑related information Microsoft is releasing publicly
Cross‑referenced verification: what independent trackers say
Independent CVE aggregators and threat feeds that index MSRC and vendor feeds list CVE‑2026‑23667 with the same high‑level classification (Broadcast DVR, local elevation, use‑after‑free). Feed and threat intelligence entries that scanned the Update Guide and public feeds confirm Cmpact as local EoP. Because MSRC’s interactive entry is the originating vendor source, aggregators derive their summarization from that vendor record. These independent confirmations reduce ambiguity about whether the CVE exists, even when technical depth is being withheld.Historical internal patch and alert threads (the community’s patch triage archives) note multiple Broadcast DVR EoP CVEs in 2025 and early 2026 and the operational work patterns used by admins to map the Update Guide entry to per‑SKU KB articles. That institutional history informs how administrators should approach CVE‑2026‑23667: map, test, deploy, and monitor.
Immediate actions for administrators (practical playbook)
Follow this prioritized checklist. Assume local exploitation is possible and that the vulnerability impacts any host where Broadcast DVR is installed and enabled.- Confirm vendor mapping:
- Check the Microsoft Update Guide entry for CVE‑2026‑23667 and map the CVE to the exact KBs for the SKUs present in your estate. The Update Guide page is the canonical vendor source. (msrc.microsoft.com)
- Prioritize patch deployment:
- Where Microsoft provides per‑SKU updates, test the vendor KB in a pilot ring and push to high‑risk assets (jump boxes, admin workstations, VDI hosts) immediately.
- If you manage many endpoints, use WSUS, Windows Update for Business, or your patch management tool to orchestrate the rollout.
- If an immediate patch is not yet available or you must delay:
- Disable Game DVR / Broadcast DVR features via Group Policy or Settings and, if necessary, stop the service until you confirm remediation. End‑user guidance and registry/group policy options are widely documented.
- Enforce least privilege: remove unnecessary local admin rights, audit service accounts, and restrict interactive logon rights for sensitive users.
- Harden hosts:
- Enable Exploit Protection / Windows Defender mitigations (where available) such as mandatory ASLR, DEP, and Control Flow Guard for user processes.
- Deploy Credential Guard on supported devices and enable Device Guard/WDAC in sensitive environments to reduce post‑exploit impact. Vendor guidance for UAF mitigations frequently recommends exploit‑mitigations at the OS level.
- Monitor and hunt:
- Monitor for process creation and service events tied to Broadcast DVR processes (for example, process names historically associated with Game DVR/Broadcast DVR).
- Look for suspicious local privilege escalation patterns: sudden token elevation, unexpected scheduled task creation, new service installations, or processes spawning under SYSTEM from a user context.
Detection and hunting recipes (operational examples)
- Host telemetry:
- Alert on creation of Broadcast DVR service processes under unusual contexts (for example, spawned by non‑interactive system installers, or by child processes performing network I/O).
- Monitor for event sequences where a user‑level process calls APIs commonly associated with token duplication or CreateProcessAsUser followed by process creation as SYSTEM.
- EDR/IDS signatures:
- Tune EDR rules to flag suspicious calls to raw heap allocation/Free sequences within DVR‑related binary modules if your vendor exposes module names in telemetry.
- Detect sudden use of previously unused local admin tools following Game DVR process activity.
- SIEM queries:
- Hunt for lateral movement indicators following local elevation attempts from endpoints that host Game DVR and related multimedia services.
Risk assessment for different environments
- Consumer desktops and gaming rigs:
- High exposure if Game DVR is enabled; the impact is host compromise and potential data loss for a single machine.
- Recommended action: patch quickly; if patching is delayed, disable Game DVR.
- Enterprise notebooks / admin workstations:
- Very high exposure. Admin we higher privileges and are a prime pivot target.
- Recommended action: immediate patching priority, aggressive monitoring, and possible temporary disabling of the service pending remediation.
- Servers (non‑interactive, server‑core, locked‑down builds):
- Exposure is typically lower because Game DVR is often absent on server SKUs; however, custom server images that include Xbox/Game features or multimedia components should be inventoried.
- Recommended action: inventory to confirm presence and patch only the affected hosts.
- VDI and multi‑user images:
- Elevated risk if images include the Broadcast DVR binaries — a single compromised golden image could lead to widespread host compromise.
- Recommended action: remediate and update images first, then roll updates to sessions.
Gaps, uncertainties, and what to watch for
- Public technical details: Microsoft’s Update Guide entry confirms the CVE and classifies impact, but per‑line exploit details and public PoCs are not being published immediately — this is consistent with vendor protective disclosure practices. Because of that, defenders must treat the MSRC entry as the authoritative source and avoid relying on incomplete third‑party writeups for mapping. (msrc.microsoft.com)
- CVSS and exploitability scoring: At the time of writing, some public feeds have not converged on a consistent CVSS base score or EPSS estimate for CVE‑2026‑23667. This can create ambiguity in automated triage systems; always prioritize vendor mapping and asset criticality over raw aggregator scores until they are normalized.
- Proof‑of‑concepts: No confirmed public PoC exploit for CVE‑2026‑23667 was present in mainstream code repositories or public exploit databases while this article was prepared. If a PoC appears, treat it as a significant escalation and move affected assets up the remediation queue.
Strategic recommendations for defenders (beyond immediate triage)
- Tighten local admin and endpoint posture:
- Enforce least privilege and application control to limit what a local attacker can do if they escalate.
- Harden EDR coverage on admin workstations and jump boxes.
- Harden patch pipelines:
- Improve the speed of per‑SKU KB mapping and automated deployment for security updates, including pilot rings for enterprise images and golden VDI images.
- Image hygiene:
- Remove unnecessary multimedia and consumer components from locked‑down images where possible.
- Build image inventories that flag optional components (Game DVR, Xbox overlays) so that attack surface is known and can be removed in sensitive classes of hosts.
- Incident readiness:
- Prepare rollback and remediation playbonfirmed exploitation. Because local privilege escalation often precedes persistence that survives reboots (service installations, scheduled task-based persistence, WMI providers), defenders should assume forensic reimaging for fully compromised hosts.
Conclusion — measured urgency and pragmatic next steps
CVE‑2026‑23667 is a vendor‑recorded elevation‑of‑privilege vulnerability impacting Windows’ Broadcast DVR component. Microsoft’s Update Guide confirmation plus independent aggregators reporting the issue as a use‑after‑free give defenders a high degree of confidence that the CVE exists and that local privilege escalation is the realistic threat model. (msrc.microsoft.com)Operationally: map the vendor entry to per‑SKU KBs, test and deploy patches urgently, and in the interim apply conservative mitigations (disable Broadcast DVR where possible, enforce least privilege, and enable OS exploit mitigations). Historical patterns in Broadcast DVR advisories and user‑mode use‑after‑free exploitation show that timely patching and host hardening materially reduce attacker success.
Finally, treat the vendor’s confidence signal as a key triage input: when Microsoft marks a high‑impact entry as confirmed, escalate scheduling and communications accordingly; when technical specifics remain intentionally sparse, compensate with accelerated inventory, temporary mitigations, and heightened hunting on endpoints that host the affected service. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center