A new SFTP vulnerability reported under the identifier CVE-2026-23942 claims a root escape in the Erlang/OTP SFTP server implementation (ssh_sftpd) that stems from a component‑agnostic prefix check in path handling — but as of March 17, 2026, there is no publicly accessible, authoritative advisory page that documents the technical details or proof-of-concept for this specific CVE, and the Microsoft Security Response Center (MSRC) landing page for CVE-2026-23942 is not directly readable without browser JavaScript, so defenders must treat the claim with caution until vendor or database entries appear. (msrc.microsoft.com)
Erlang/OTP’s SSH application includes an SFTP server component named ssh_sftpd. The module provides a configurable SFTP root, pluggable file-handler callbacks, and options that determine how file paths and directories are presented to connected users. In standard configurations the server uses the
Historically, SFTP and SSH-related software have had several subtle path-handling and expansion bugs that allowed clients to reach files outside an intended root or cause other privilege issues. Notable past examples include SFTP path parsing quirks such as tilde (˜) expansion mistakes that led to path traversal in libcurl’s SFTP support, and prior bugs in ssh/ssh_sftpd that caused resource exhaustion. Those precedents illustrate how easy it is for small parsing differences to convert a harmless-seeming path into an escape vector.
Because the MSRC page linked by the original reporter is either unavailable or client-side rendered, the public record for CVE-2026-23942 cannot be verified at the vendor-of-record (Microsoft) at the time of writing. That absence matters: without a vendor advisory, patch notes or a public CVE record in major databases, we cannot confirm affected versions, exploitability, or a remediation timeline for this specific identifier. Treat any operational claims about CVE-2026-23942 as provisional until vendor documentation or NVD / CERT / distribution advisories are published. (msrc.microsoft.com)
Because ssh_sftpd supports configurable file-handler callbacks and lists the
The operational takeaway: even mature codebases can carry a brittle assumption that a textual prefix check is sufficient. That assumption must be actively tested with adversarial input during security reviews.
For context and triage reference, consult prior SFTP-related advisories and the ssh_sftpd documentation to understand the module’s configuration semantics when designing mitigations; these materials show why a prefix-check mismatch can become a pragmatic escape vector and where to focus detection and hardening efforts.
If you’re tracking this issue operationally: prioritize inventory and access restriction, monitor SFTP logs for abnormal path strings or file reads, and be ready to deploy vendor-supplied updates the moment an official advisory or patch is published.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Erlang/OTP’s SSH application includes an SFTP server component named ssh_sftpd. The module provides a configurable SFTP root, pluggable file-handler callbacks, and options that determine how file paths and directories are presented to connected users. In standard configurations the server uses the root option to restrict the user’s view and limit filesystem access to a subtree; implementations rely on careful path normalization and prefix checks to prevent clients from escaping that subtree.Historically, SFTP and SSH-related software have had several subtle path-handling and expansion bugs that allowed clients to reach files outside an intended root or cause other privilege issues. Notable past examples include SFTP path parsing quirks such as tilde (˜) expansion mistakes that led to path traversal in libcurl’s SFTP support, and prior bugs in ssh/ssh_sftpd that caused resource exhaustion. Those precedents illustrate how easy it is for small parsing differences to convert a harmless-seeming path into an escape vector.
Because the MSRC page linked by the original reporter is either unavailable or client-side rendered, the public record for CVE-2026-23942 cannot be verified at the vendor-of-record (Microsoft) at the time of writing. That absence matters: without a vendor advisory, patch notes or a public CVE record in major databases, we cannot confirm affected versions, exploitability, or a remediation timeline for this specific identifier. Treat any operational claims about CVE-2026-23942 as provisional until vendor documentation or NVD / CERT / distribution advisories are published. (msrc.microsoft.com)
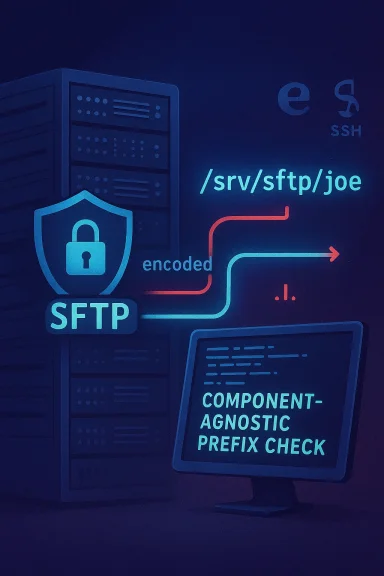
What the reported issue name implies: “component‑agnostic prefix check” explained
The phrase component‑agnostic prefix check is not a standard vulnerability taxonomy, so it’s useful to unpack what it likely means in practical terms.- Component‑agnostic: the path- or prefix-checking logic does not distinguish between types of path components (for example: plain names, tilde expansions, percent or URI-encoded components, zero-byte-terminated strings, or exotic SFTP-specific encodings).
- Prefix check: server code commonly prevents escapes by verifying that the normalized absolute path of an operation begins with the configured SFTP root prefix. If that check is performed without normalizing or without recognising certain component encodings, then crafted inputs can bypass it.
Because ssh_sftpd supports configurable file-handler callbacks and lists the
root option as the mechanism to confine users to a subtree, any normalization bug in the path-handling pipeline is a plausible origin for a root escape vulnerability. Administrators should therefore treat assertions about prefix-check weaknesses seriously even while the specific CVE record remains unverified.Evidence, verification status, and what we can and cannot confirm
- MSRC page and vendor record
- The MSRC "Update Guide" entry for the URL the user supplied is not directly viewable without executing client-side JavaScript in a browser; the raw server response visible via a simple fetch returns only a client-side shell message ("You need to enable JavaScript to run this app."). That prevents straightforward scraping and indicates the MSRC page is a single‑page app that may be present but not immediately indexable. Until Microsoft publishes plain-text advisory content (or a KB / patch entry), the vendor’s authoritative details remain inaccessible to automated indexing. (msrc.microsoft.com)
- Public CVE / NVD / distro advisories
- A comprehensive web search and major vulnerability feeds (as of this writing) do not show a corroborating, public technical write-up for CVE‑2026‑23942. No NVD entry matching that ID with technical details is discoverable at the time of publication, and we found no vendor release notes describing a fix for an ssh_sftpd prefix-check bug under that CVE number. This absence may indicate one of several possibilities: the CVE was very recently assigned and vendor advisories are pending; the MSRC listing exists but is not yet populated with details; the CVE ID was misquoted; or a private coordinated disclosure is in progress. Because of that uncertainty we must explicitly flag the claim as unverifiable until independent, authoritative advisories appear. (msrc.microsoft.com)
- Context from related, documented vulnerabilities
- Similar SFTP path-parsing vulnerabilities are well documented and inform realistic threat models. For example, libcurl’s SFTP tilde/traversal behavior (CVE-2023-27534) demonstrates how small parsing differences permit unexpected path resolution, and prior issues affecting Erlang’s ssh_sftpd (such as resource-handling bugs) show the component is not immune to security defects. These precedent cases are not proof that CVE‑2026‑23942 is real, but they justify urgent attention when claims of an SFTP root escape appear.
Technical analysis: plausible attack mechanics based on the wording
If the reported vulnerability behaves like other path‑normalization issues in SFTP stacks, the following attack path is plausible — useful as a triage model for defenders but not a statement of confirmed facts for this CVE:- An SFTP client sends file operation requests (READ, OPEN, STAT, RENAME, REMOVE, SYMLINK) that include a path string.
- The ssh_sftpd code applies a component‑agnostic prefix check: it tests whether the client-supplied path textually begins with the configured root prefix (for example, "/srv/sftp/joe"). If the check is performed without:
- canonicalizing path components (resolving ".", "..", multiple separators),
- recognising tilde (~) or numeric tilde forms, or
- decoding percent / UTF-8 / SFTP-specific encodings,
then a crafted path can bypass the check while resolving to a filesystem location outside the root. Example tricks seen historically: - using path components like "/srv/sftp/joe/../etc/passwd" where textual prefix test is naive
- using encoded or multi-byte sequences that compare equal after normalization but not in the raw string test
- exploiting symlink handling differences between the server’s file handler and the prefix check
- If the file-handler module (which is pluggable in ssh_sftpd) resolves symlinks or decodes components differently than the prefix checker expects, the effective path used for the filesystem operation may lie outside the chroot-like restriction.
Practical impact scenarios
If an SFTP root escape is present and exploitable in an environment, realistic impacts include:- File disclosure: an authenticated SFTP user (or client that persuades a server to process crafted operations) can read sensitive files outside their designated subtree, such as /etc/passwd, private keys, configuration blobs, or other tenants’ data on multi-tenant hosts.
- File modification & integrity loss: depending on server permissions, writes could overwrite system files, injected web content, or authorized_keys to enable further persistence.
- Credential theft and lateral movement: reading authentication or token files can enable privilege escalation and lateral movement inside a network.
- Supply-chain risk: embedded systems, appliances, or managed services that bundle ssh_sftpd can carry the vulnerability into many downstream products; attackers often weaponize unattended SFTP endpoints in IoT and enterprise appliance fleets.
- Stealth & persistence: SFTP protocol operations can be difficult to distinguish from benign file transfers, complicating detection timelines.
Immediate action checklist for administrators (prioritize this now)
Until an authoritative advisory for CVE‑2026‑23942 appears, take these defensive steps immediately to reduce exposure and buy time for a proper patch rollout.- Inventory and exposure
- Identify all hosts running Erlang/OTP’s ssh_sftpd (or any SFTP server based on Erlang’s ssh app) and list their service endpoints and responsible owners.
- Restrict access
- Limit SFTP access to trusted networks and management hosts by firewall rules, VPNs, or allow‑lists. Remove internet exposure where possible.
- Harden SFTP configuration
- Disable direct root logins and prefer dedicated unprivileged SFTP users.
- Use the built-in
rootchroot option where appropriate and ensure that chroot roots are on dedicated filesystems. - Where the implementation supports it, prefer a simple, well-tested
file_handlerand avoid custom/third-party callback modules until the situation is clearer. - Monitor and hunt
- Look for suspicious SFTP operations that include unusual path encodings, sequences of
..,~or percent-encoded payloads, or repeated failed open/stat attempts. - Watch for unexpected reads of sensitive files (e.g., /etc/passwd, /etc/shadow, /root/.ssh/authorized_keys) and notifications of changed file hashes on critical files.
- Temporary mitigations
- If you operate SFTP front-ends or proxies (load balancers, application firewalls), consider blocking or sanitizing suspicious path characters such as embedded nulls, encoded separators, and repeated slash patterns.
- In high-risk contexts, consider taking SFTP services offline for public access until a patch/patch guidance is published.
- Patch management readiness
- Place affected packages on a high‑priority update list and be prepared to apply vendor patches or distribution updates immediately when they are released.
Detection guidance and hunting queries (concrete steps)
Use the following detection ideas and queries as starting points in your logs and EDR tooling. Do not treat these as guaranteed indicators — they are patterns consistent with path‑normalization abuse.- Search SFTP server logs (or syslog) for file paths containing:
..sequences mixed with paths that should be chrooted- percent-encoded separators like
%2e%2e%2f - tilde expansions such as
/~or forms like/~2/that have been used in tilde-handling bugs - Audit for unexpected reads or opens on high-value system files, especially events showing read or open on
/etc/passwd,/etc/shadow,/root/.ssh/*, or application secrets files. - Hunt for unexpected writes to
authorized_keysfiles or sudden changes in/etc/cron.*or systemd unit files following SFTP sessions. - On Linux, use inotify-based monitors or periodic integrity checks (AIDE/Tripwire/sha256sum audits) for critical binaries and configuration files.
- Network-level detection: look for SFTP sessions that transfer small control files or issue sequences of STAT / READDIR / OPEN that deviate from normal user behavior.
Responsible disclosure, vendor coordination, and timelines
If you have internal telemetry that indicates exploitation or proof-of-concept code for CVE‑2026‑23942, follow established responsible-disclosure steps:- Preserve evidence (logs, pcap, file system snapshots) and isolate affected hosts.
- Report to the vendor-of-record (if the service is shipped with a vendor product) and to distribution maintainers (Debian, Ubuntu, Red Hat, etc.) including your technical findings and sample artifacts.
- If the CVE number was provided externally (for example by a third party) and you cannot find a vendor advisory, confirm the identifier with MITRE/CVE Program or the platform that issued the CVE and request the canonical record and advisory link.
- If you are a vendor or package maintainer: provide transparent release notes that list affected versions, CVSS scoring, and mitigation steps; avoid obscuring details that impede defenders from triaging.
Why these kinds of flaws are easy to miss and why that matters
Path-normalization and prefix checks are conceptually simple, but real-world environments introduce many edge cases:- Multiple layers perform normalization (protocol parser, application logic, pluggable file handler, OS filesystem), and inconsistent normalization across layers creates gaps an attacker can exploit.
- Encoding tricks (UTF-8 overlong sequences, percent-encoding, percent-encoded slashes) or platform-specific path semantics (Windows-style backslashes vs POSIX slashes) can produce different logical path results even when textual comparisons look safe.
- Pluggable file handlers (a feature in ssh_sftpd) are especially risky: the module that enforces the prefix check may operate on raw strings while the file handler resolves symlinks or performs additional canonicalization.
- Test suites commonly miss exotic encodings, non‑printable characters, or unusual sequences that have real-world impact under adversarial input.
The operational takeaway: even mature codebases can carry a brittle assumption that a textual prefix check is sufficient. That assumption must be actively tested with adversarial input during security reviews.
Strengths and limitations of current public information
Strengths- The conceptual description (component-agnostic prefix check causing root escape) matches a known, well-understood class of vulnerabilities. That makes the claim plausible and therefore worthy of rapid defensive action.
- Established mitigation and detection patterns for path traversal issues apply here and can reduce risk prior to a formal patch.
- There is no authoritative, technical advisory publicly available for CVE‑2026‑23942 as of March 17, 2026; without it we cannot confirm exact affected versions, language runtimes, or whether the issue is exploitable in default configurations. Treat operational guidance as precautionary rather than definitive. (msrc.microsoft.com)
- Absent a vendor-provided patch or a clear CVSS score, organizations might need to balance service availability against the risk of waiting for a patch; this creates a challenging operational decision for highly-exposed SFTP endpoints.
Recommended next steps for WindowsForum readers and admins
- Immediately inventory SFTP endpoints and limit exposure. Prioritize systems that:
- run Erlang-based SFTP servers (ssh_sftpd),
- are internet‑facing, or
- host high-value system or tenant data.
- Implement the containment checklist above (restrict access, harden config, monitor logs).
- Subscribe to vendor and distribution security advisories (Erlang/OTP GitHub releases, Debian/Ubuntu security trackers, Red Hat errata, MSRC update guide) and prepare for rapid patch deployment.
- If you operate a managed environment or appliance that embeds Erlang/OTP, engage the vendor for confirmation and an ETA for fixes.
- If you find evidence of exploitation, preserve forensic artifacts and coordinate disclosure with vendors and CERTs.
Final assessment and caution
CVE‑2026‑23942 — described by the reporter as an SFTP root escape via a component‑agnostic prefix check in ssh_sftpd — aligns with a recognized vulnerability class that has produced serious incidents before. However, public, authoritative verification for this specific CVE is currently lacking: the MSRC page requires client-side rendering and does not expose plain-text advisory content to automated fetches, and mainstream vulnerability trackers had no consumable technical advisory for CVE‑2026‑23942 at the time this article was prepared (March 17, 2026). Defenders should assume the claim is plausible and act urgently to mitigate exposure, but also avoid speculative operational changes beyond stanhardening until vendors publish concrete, versioned advisories and patches. (msrc.microsoft.com)For context and triage reference, consult prior SFTP-related advisories and the ssh_sftpd documentation to understand the module’s configuration semantics when designing mitigations; these materials show why a prefix-check mismatch can become a pragmatic escape vector and where to focus detection and hardening efforts.
If you’re tracking this issue operationally: prioritize inventory and access restriction, monitor SFTP logs for abnormal path strings or file reads, and be ready to deploy vendor-supplied updates the moment an official advisory or patch is published.
Source: MSRC Security Update Guide - Microsoft Security Response Center