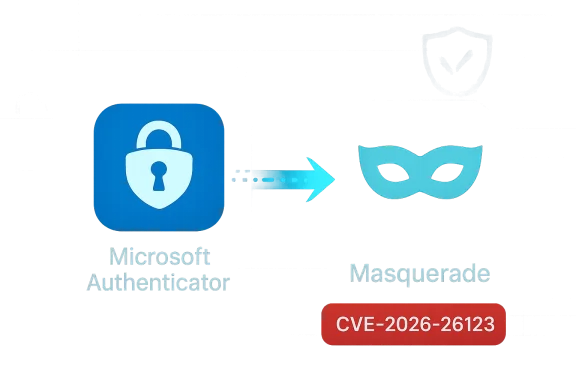
Microsoft's March 10, 2026 security update includes a newly assigned CVE—CVE-2026-26123—that affects the Microsoft Authenticator mobile application and is classified as an information disclosure vulnerability. The problem is notable because the attack vector exploits how mobile platforms hand off authentication actions to apps, allowing a malicious application that masquerades as Microsoft Authenticator to receive enough data during a sign-in flow to impersonate a user under certain conditions. Microsoft rates the issue as Important, assigns a CVSS v3 base score of 5.5, and lists the underlying weakness as related to improper authorization in a handler for custom URL schemes (CWE-939). Organizations and users should treat this as a real but bounded risk: exploitation requires user interaction and specific conditions, but the potential impact on mobile-based multifactor authentication (MFA) and passwordless flows demands immediate, pragmatic mitigation.
Microsoft Authenticator is widely used for consumer and enterprise MFA, providing time-based one-time passwords (TOTP), push notifications, passwordless sign-in options, and enterprise (Entra ID) credential handling on both Android and iOS devices. Because many organizations rely on phone-based authentication for both consumer and high-value corporate accounts, an information-disclosure weakness in an authenticator app raises both usability and security questions.
CVE-2026-26123 was disclosed as part of Microsoft's March 2026 Patch Tuesday on March 10, 2026. The vendor's advisory and multiple independent patch-day analyses describe the attack narrative as involving a malicious app that convinces the user to select it as the handler for the sign-in or QR-code-driven authentication flow. When that happens, the malicious app can receive data that it should not—enough, in some scenarios, to impersonate the user to relying parties. Microsoft classifies exploitation as less likely than trivial and the vulnerability as requiring user interaction, but it still places the issue in the Important severity band.
Immediate actions (first 24–72 hours)
What to look for
Microsoft’s CVE-2026-26123 is an important reminder that mobile authentication depends on many pieces—OS, app, user behavior, and enterprise controls—and that weaknesses in the handoff logic between them can yield meaningful opportunities for attackers. The good news is that the conditions required for exploitation raise the bar: a malicious app must be present and a user must be tricked into selecting it. The bad news is that social engineering, app masquerading, and permissive BYOD policies make that bar achievable for determined attackers.
Defenders should respond pragmatically: patch, enforce MDM policies, harden high-value workflows with hardware-backed factors, and educate users. These measures, applied urgently and consistently, will reduce the window of opportunity for attackers who would try to exploit mobile authentication flows. Confronted with an evolving threat model where apps and handlers interact across applications, defenders who combine technical controls with clear user guidance will close the gaps that CVE-2026-26123 exposes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Microsoft Authenticator is widely used for consumer and enterprise MFA, providing time-based one-time passwords (TOTP), push notifications, passwordless sign-in options, and enterprise (Entra ID) credential handling on both Android and iOS devices. Because many organizations rely on phone-based authentication for both consumer and high-value corporate accounts, an information-disclosure weakness in an authenticator app raises both usability and security questions.CVE-2026-26123 was disclosed as part of Microsoft's March 2026 Patch Tuesday on March 10, 2026. The vendor's advisory and multiple independent patch-day analyses describe the attack narrative as involving a malicious app that convinces the user to select it as the handler for the sign-in or QR-code-driven authentication flow. When that happens, the malicious app can receive data that it should not—enough, in some scenarios, to impersonate the user to relying parties. Microsoft classifies exploitation as less likely than trivial and the vulnerability as requiring user interaction, but it still places the issue in the Important severity band.
What the vulnerability is — technical overview
The attack surface: URL scheme / handler confusion
At a high level, the vulnerability stems from how mobile platforms and apps negotiate which application handles an authentication action initiated by a web or QR code flow. Modern mobile authentication often uses:- Custom URL schemes or universal links/intents to move a sign-in flow from a browser or web view into the authenticator app.
- QR-code-driven enrollment flows that launch a handler app to complete pairings or token exchanges.
- Inter-app handoffs where the authenticator receives credentials, tokens, or handshake material necessary to complete MFA or provisioning.
Root cause class: CWE-939
Microsoft’s advisory points to a weakness consistent with CWE-939: Improper Authorization in Handler for Custom URL Scheme. In practical terms, that means the code that processes a handler registration or validates which handler is the legitimate recipient did not perform sufficient authorization checks, allowing an attacker-controlled handler to claim results intended for the authentic authenticator. The true root-cause details beyond Microsoft’s executive summary are limited in public documentation; vendors and researchers note the general mechanism but have not published a full proof-of-concept, and Microsoft’s classification indicates the weakness is in handler authorization logic rather than, for example, cryptographic token leakage.Attack prerequisites and likelihood
This vulnerability’s exploitation is not a silent remote compromise. Key prerequisites are:- A malicious app must be present on the target device and able to register as an authentication handler. On Android, this is more straightforward via intent filters; on iOS, the operating system is generally stricter, but social engineering and enterprise-signed apps complicate the threat model.
- The user must interact with the attack flow—typically by selecting the malicious app as the handler when prompted, scanning a crafted QR code, or following a link that initiates the vulnerable handoff.
- The malicious app must be able to receive, store, and then misuse the information transferred during the handoff. Microsoft’s advisory cautions that exploitation succeeds when the malicious app receives enough information to impersonate the user, which implies the payload could include tokens, codes, or other credential material.
Why this matters: risks to enterprises and individuals
The threat to BYOD and unmanaged devices
The most acute exposure is for bring-your-own-device (BYOD) scenarios and devices outside strict enterprise management. In BYOD models, users can install apps from app stores, sideload apps (Android), or receive enterprise-signed packages—creating multiple pathways for a malicious handler to reach a device. If the attacker can trick a user into choosing the malicious handler during an authenticator onboarding or sign-in flow, the attacker may obtain credentials or token material required to impersonate the user against services that rely on that authenticator.Impact on high-value workflows
Many organizations now use mobile authenticators not only for low-privilege logins but for:- Passwordless or single-tap login flows.
- Admin-level account recovery and privileged elevation.
- Push-based MFA approvals tied to administrative operations.
Supply-chain and app masquerading risks
The advisory highlights the classic app-masquerading problem: a malicious app can copy package names, icons, or names that look similar to the legitimate app. App stores and OS policies aim to mitigate this, but the presence of many third-party markets, sideloading on Android, and corporate app deployment methods mean the risk cannot be fully mitigated purely by store policies. Attackers also employ social engineering—QR codes posted in public places, phishing links, or in-app messaging—to trigger the handoff.What Microsoft says (and what remains unclear)
Microsoft’s public advisory and the March 10, 2026 Patch Tuesday documentation make three points clear:- CVE-2026-26123 exists and affects Microsoft Authenticator on mobile platforms.
- The vulnerability allows an unauthorized local actor to disclose information when a malicious app is selected as the sign-in handler.
- Microsoft rates the vulnerability as Important and gives it a CVSS v3 base score of 5.5.
- The exact contents of the data disclosed during a successful exploit—Microsoft’s public document describes the impact in general terms and does not publish full technical artifacts or payload examples.
- A working public proof-of-concept (PoC) or detailed exploit chain is not available at the time of publication in order to limit risk of widespread abuse.
- Platform-by-platform nuances (exact behavior differences between Android and iOS) are summarized at a high level but not exhaustively documented for public consumption.
Practical mitigation and deployment guidance (prioritized)
Organizations should treat this as a near-term security action for all mobile fleets that use Microsoft Authenticator for enterprise access.Immediate actions (first 24–72 hours)
- Update Microsoft Authenticator on all managed iOS and Android devices to the patched version Microsoft released on March 10, 2026.
- For unmanaged BYOD, push strong user communications instructing users to update the app immediately and to avoid selecting unknown apps when asked to handle authentication flows.
- If your environment uses Microsoft Intune or another MDM/UEM, enforce an application allowlist that restricts which authenticator apps can be used for work accounts. Consider temporarily blocking unknown or unapproved authenticator apps from accessing managed resources.
- Revoke high-risk sessions and reissue tokens for high-privilege accounts where mobile authentication is the primary second factor—particularly if there is reason to suspect a user or device may have interacted with a malicious QR code or app.
- Configure conditional access policies to require device compliance and app protection for MFA and passwordless sign-ins. Increase requirements for high-risk operations to require hardware-backed FIDO2 security keys or additional verification.
- Add telemetry detection: monitor for unusual app installs, multiple handler registrations for authentication-related intents, or increased authentication failures followed by new app installs on the same device.
- Educate staff on the specific social engineering vectors: malicious QR codes, fake app prompts, and links that initiate a sign-in flow. Include clear instructions to decline unknown handlers and to report suspicious prompts.
- For critical accounts, require hardware-backed authenticators (security keys) or enroll alternative MFA factors that do not rely on inter-app handoffs.
- Review BYOD policies. If BYOD is allowed, require app attestation or endpoint attestation via MDM before allowing Entra or enterprise credential use.
- Re-evaluate your account recovery and break-glass processes. Ensure that recovery flows cannot be trivially abused via a compromised authenticator app on a device.
- Test and document a rapid-response runbook: how to revoke tokens, force MFA re-enrollment, and isolate potentially compromised sessions for privileged accounts.
- Prioritize adoption of FIDO2/passkeys and hardware-backed keys for administrative and high-value users; these methods reduce reliance on mobile app handoffs.
- Encourage or require the use of device- or platform-level app attestation and safety-net features that bind authenticator behavior to specific app signatures or hardware-backed attestation.
- Engage with platform vendors on improving OS-level policies for handler registration and clearer UI to prevent handler confusion and spoofing.
Detection and incident response guidance
Because public technical details remain limited, detection will be a mix of proactive telemetry and behavior-based hunting.What to look for
- New or unexpected authenticator-style apps installed on endpoints, especially ones that declare intent filter/URL scheme handling for authentication flows.
- User reports of authentication prompts that appear to be from the authenticator app but have unexpected UI changes or iconography.
- Authentication flows where the user approves a sign-in but the expected push or in-app approval does not appear in Microsoft Authenticator logs.
- Suspicious device activity following an authentication event, such as immediate sign-in attempts to cloud services from unusual geolocations or IP addresses.
- Elevated numbers of MFA fallback requests or helpdesk recovery calls from users who recently installed an app or scanned a QR code.
- Isolate the affected device from the corporate network and cloud services.
- Remove the suspicious app and any associated packages; require a fresh installation of Microsoft Authenticator from the official store.
- Revoke tokens and sessions issued around the suspect timeframe for any affected accounts; force re-authentication using a patched authenticator.
- If administrative or sensitive accounts were used, rotate credentials, reset privileged sessions, and perform a full audit of recent privileged actions.
- Device inventory and app install logs, including timestamps and package identifiers.
- Authentication logs: token issuance, device identifiers, IP addresses, and session start times.
- Any captured QR codes, links, or messages that initiated the vulnerable flow.
- MDM/UEM logs showing handler registrations, policy changes, and app attestation results.
Why CVSS 5.5 and “Important” severity fit this issue
CVSS v3 base score of 5.5 reflects the balanced nature of the risk:- Attack Vector: Local (the malicious app must be present on the device).
- Attack Complexity: Medium — user interaction is required and the attacker must convince the user to select the malicious handler.
- Privileges Required: None in terms of OS privileges; installation of an app may require permissions consistent with the platform and user acceptance.
- User Interaction: Required — a notable mitigator of large-scale automatic abuse.
- Impact: Confidentiality impact is considered but limited by exploitation preconditions and scope.
Platform-specific considerations: Android vs iOS
Android- Android’s intent system and third-party app ecosystem make it comparatively easier for apps to declare handlers for schemes and actions.
- Sideloading, multiple app stores, and less rigid naming controls increase the risk of malicious handler apps reaching users.
- MDM controls can mitigate by restricting allowed apps, enforcing Play Protect, and requiring app attestation.
- iOS historically restricts third-party app capabilities more tightly; custom URL schemes and universal links behave differently, and Apple review reduces the likelihood of obviously malicious apps landing in the App Store.
- However, enterprise-signed apps, developer profiles, and the occasional app that evades detection mean iOS is not immune.
- The app experience on iOS often shows clearer UI when switching handlers, but users often click through prompts—so social engineering remains a viable route.
Communication: what to tell users
- Be explicit and timely: inform users that Microsoft released an update on March 10, 2026 that fixes a vulnerability affecting Microsoft Authenticator, and instruct them to update the app immediately.
- Provide concrete guidance: do not accept or select unknown apps when asked to handle a sign-in or QR-code flow; only approve handlers that match the official Microsoft Authenticator branding and store listing.
- Explain why: make it clear that an app selected as the handler during a sign-in can receive authentication data and that a malicious app could misuse that information to sign in as the user.
- Offer alternatives for high-risk users: temporary use of hardware security keys or other approved second-factor methods while you complete your review and enforcement.
Critical analysis: strengths of Microsoft’s response and residual risks
Strengths- Microsoft issued a timely advisory with a CVE and included the vulnerability in the March 10, 2026 Patch Tuesday release—this demonstrates mature vulnerability triage and coordinated disclosure.
- The vendor publicly categorized the weakness (CWE-939), assigned a severity, and produced a fix—enabling defenders to act quickly.
- Microsoft’s ecosystem-level controls (Intune, conditional access policies, app protection) provide enterprise customers with immediate levers to reduce exposure.
- The public advisory intentionally limits deep technical disclosure. While this is appropriate to reduce abuse, it leaves defenders with unanswered questions about exactly what token material could be captured and how broadly the exploit could be automated under some conditions.
- BYOD environments and unmanaged devices remain the weak link. Many organizations with permissive BYOD policies will struggle to enforce the immediate mitigations necessary to fully eliminate risk.
- App masquerading and social engineering remain powerful attacker tools. Fixing the handler authorization does not remove the user-click problem—attackers who can convincingly mimic the authenticator’s UI could still attempt credential capture via other vectors.
- Sideloading and third-party distribution channels on Android keep the possibility of malicious handler apps in circulation even after patching; platform-level controls and user behavior must evolve in parallel.
Final recommendations — an operational checklist
- Update: Deploy the March 10, 2026 Authenticator update to all managed devices immediately.
- Enforce: Use MDM/UEM to restrict which apps may be used for enterprise authentication and require app attestation where supported.
- Harden: Require FIDO2 or hardware-backed keys for administrators and high-risk users.
- Communicate: Push clear instructions to users about not selecting unfamiliar handler apps and about verifying app identity before approving handoffs.
- Hunt: Add detection for handler registrations, unusual app installs, and anomalous authentication sessions; collect forensic artifacts where suspicious activity is observed.
- Revoke: For confirmed incidents or plausible contamination, revoke tokens and force MFA re-enrollment and session termination.
- Review: Reassess BYOD policies and account recovery flows to ensure high-value procedures cannot be trivially subverted by a compromised mobile authenticator.
Microsoft’s CVE-2026-26123 is an important reminder that mobile authentication depends on many pieces—OS, app, user behavior, and enterprise controls—and that weaknesses in the handoff logic between them can yield meaningful opportunities for attackers. The good news is that the conditions required for exploitation raise the bar: a malicious app must be present and a user must be tricked into selecting it. The bad news is that social engineering, app masquerading, and permissive BYOD policies make that bar achievable for determined attackers.
Defenders should respond pragmatically: patch, enforce MDM policies, harden high-value workflows with hardware-backed factors, and educate users. These measures, applied urgently and consistently, will reduce the window of opportunity for attackers who would try to exploit mobile authentication flows. Confronted with an evolving threat model where apps and handlers interact across applications, defenders who combine technical controls with clear user guidance will close the gaps that CVE-2026-26123 exposes.
Source: MSRC Security Update Guide - Microsoft Security Response Center