 Understanding CVE-2026-26173 and Microsoft’s AFD.sys Confidence Metric
Understanding CVE-2026-26173 and Microsoft’s AFD.sys Confidence Metric
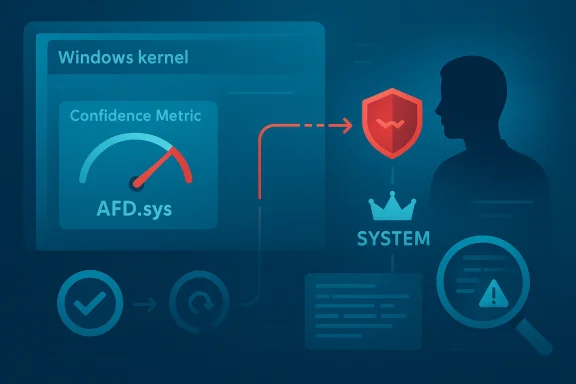
Microsoft’s CVE-2026-26173 entry points to a familiar but still dangerous Windows pattern: a kernel-adjacent privilege-escalation issue in the Ancillary Function Driver for WinSock (AFD.sys), the long-lived networking component that sits close to the Windows socket stack. What makes this advisory especially interesting is not just the class of bug, but the confidence metric Microsoft attaches to the vulnerability description, which speaks to how certain the vendor is that the flaw exists and how credible the known technical details are. In practical security terms, that confidence signal matters because it helps defenders distinguish between confirmed engineering risk and speculative or partially characterized weakness.The public record around AFD.sys vulnerabilities is substantial, and that history matters here. Microsoft has repeatedly patched AFD-related elevation-of-privilege issues over the years, including documented cases where a local attacker could gain complete system control if they already had logon access and could run a crafted program. That track record makes any new AFD.sys advisory worth immediate attention, even when the advisory text is sparse, because kernel-mode bugs in this component tend to be high-value targets for attackers seeking to move from local footholds to full administrative control. Microsoft’s own historical bulletins describe AFD.sys as a kernel-mode driver that validates input before passing it from user mode into the Windows kernel, underscoring why mistakes in this path can be so damaging.
Overview
AFD.sys is one of those Windows components most users never think about, yet it quietly underpins much of Windows networking behavior. It sits in the driver layer that supports Winsock and handles low-level socket primitives, which means it lives close to privileged kernel code and processes data that can originate from less trusted user-mode callers. That architecture is efficient, but it also means a logic error, memory bug, or access-control failure can become a direct route into SYSTEM-level compromise.Microsoft’s historical security bulletins show that AFD-related vulnerabilities are rarely theoretical. In the past, the company has documented issues ranging from improper input validation to double-free conditions, always with the same broad consequence: a local attacker could escalate privileges after logging on and executing a specially crafted application. Microsoft’s older guidance for AFD vulnerabilities consistently notes that the affected systems are often workstations and terminal servers, because they are the most plausible places for an attacker to obtain a local foothold and then abuse it for elevation. That pattern is not new, but it remains relevant because the same attack model still defines the practical risk surface today.
The confidence metric in Microsoft’s Security Update Guide is important because it adds a second layer of interpretation beyond the CVE label itself. The metric is meant to communicate how sure Microsoft is about the vulnerability’s existence and how trustworthy the technical characterization is. A high-confidence entry suggests that the vendor has enough evidence to treat the issue as real and actionable, even if the root cause details are not fully public. A lower-confidence entry, by contrast, may indicate an issue that is still being corroborated, triaged, or technically refined.
That distinction matters to defenders because not all advisories carry the same operational urgency. A vulnerability can be harmful even if the exact exploit mechanics are not disclosed, but a higher-confidence classification generally means the vendor believes the issue is concrete enough to prioritize patching and hunting. In other words, the confidence metric is not just metadata; it is a warning about the credibility and maturity of the vulnerability record itself.
Why AFD.sys keeps showing up
AFD.sys has appeared repeatedly in Microsoft security history because it occupies a sensitive interface boundary. It bridges user-mode network operations and kernel-mode handling, which means malformed requests, race conditions, or memory-management mistakes can become privilege escalation opportunities. That makes it a perennial candidate for local exploitation chains, especially once an attacker has already landed on a system through phishing, abuse of a vulnerable service, or credential theft.There is also a structural reason AFD bugs are attractive: they often enable post-exploitation movement rather than initial compromise. That makes them particularly useful to advanced intruders, because a low-privileged shell is often enough to begin the climb to SYSTEM. Once a kernel-mode weakness is available, the attacker’s next step is often persistence, defense evasion, or credential extraction.
- Kernel proximity increases the consequence of coding mistakes.
- Local footholds are often enough to make the bug useful.
- Privilege escalation bugs are valuable in chained attacks.
- AFD.sys has a long history of being security-sensitive.
What the Confidence Metric Means
Microsoft’s confidence metric is best understood as a quality signal for the advisory itself. It does not replace severity ratings or CVSS scores, and it is not the same thing as proof-of-exploit. Instead, it tells readers how much faith they should place in the existence and character of the issue as described. That is useful because security teams often need to decide whether to move immediately or wait for more evidence.A high-confidence advisory is different from a vague rumor. It suggests the vendor has enough technical grounding to believe the bug is real, even if public details are limited. That makes the advisory operationally meaningful for patch planning, threat hunting, and exposure review. In a world where attackers move quickly, the difference between confirmed and possible can be the difference between routine patching and emergency response.
Confidence versus exploitability
It is easy to confuse confidence with active exploitation, but they are not the same thing. A vulnerability can be well confirmed and still not be seen in the wild, while another issue can be lightly documented yet aggressively exploited. The confidence metric is about the reliability of the disclosure, not the criminal popularity of the flaw.That said, there is still a practical relationship between the two. High-confidence bugs in kernel components tend to attract attention from offensive researchers and threat actors because they are valuable escalation primitives. So while confidence does not prove exploitation, it increases the likelihood that defenders should take the issue seriously and assume that further details may emerge quickly.
- High confidence means Microsoft believes the issue is real.
- Low confidence means the advisory may still be under refinement.
- Exploitability is a separate question.
- Operational urgency rises when confidence and impact align.
Why Local Elevation Matters So Much
Local elevation of privilege vulnerabilities are often underestimated because they are not the dramatic, internet-facing bugs that dominate headlines. But in enterprise environments, local privilege escalation is frequently the bridge from limited access to full compromise. Once an attacker gets a standard user session, a local EoP bug can unlock SYSTEM access, credential dumping, tampering with security controls, and broader lateral movement.That is why AFD.sys issues remain strategically important even when they require some initial access. In real-world intrusions, attackers often obtain that foothold through unrelated vectors such as phishing, token theft, remote service abuse, or exploited browser and application bugs. A local kernel escalation then becomes the second stage of the campaign, not the first.
Enterprise and consumer exposure differ
For consumers, the immediate risk may be lower if the device is already patched and account hygiene is strong. But home systems can still be exposed if malware gains a standard user context and then leverages an unpatched local privilege escalation. Consumers also tend to underestimate how often local admin rights, unsafe software, or unattended remote-support tools increase the blast radius.For enterprises, the stakes are more serious. Endpoint fleets routinely host privileged management agents, remote support tools, development software, and service accounts. That creates a larger local attack surface, and it also means successful privilege escalation can unlock domain access paths, credential material, and security tooling disruption. In short, the same bug is more expensive to ignore at scale.
- Consumer devices are at risk when malware already has a foothold.
- Enterprise endpoints offer richer privilege targets and broader blast radius.
- Admin accounts make local EoP far more dangerous.
- Defense-in-depth matters because patching alone is not always instantaneous.
Historical Context Around AFD.sys
Microsoft has been patching AFD-related issues for well over a decade, and the historical bulletins are remarkably consistent in their framing. Earlier advisories described vulnerabilities where AFD improperly processed user-supplied input, leading to privilege escalation or kernel code execution. Microsoft’s own wording repeatedly emphasized that the vulnerabilities could allow an attacker who already logged on locally to run a specially crafted application and gain complete control of the system.That history gives today’s advisory a recognizable shape. Even if the public details for CVE-2026-26173 are limited, the pattern is easy to interpret: a kernel-facing bug in a networking driver, a local privilege boundary crossing, and a likely payoff measured in SYSTEM rights. Security teams should not assume novelty means uncertainty; often it simply means the bug is newly cataloged, not newly dangerous.
The repeated AFD pattern
AFD.sys vulnerabilities tend to share a common operational profile. They are generally local, they are usually post-compromise primitives, and they often become useful when an attacker already controls a standard user account or a sandbox escape. That makes them less visible to casual observers and more valuable to sophisticated intruders.Microsoft’s older bulletins also show that AFD defects have been addressed through corrected validation of data moving from user mode into kernel mode. That detail matters because it explains why the component is so sensitive: every trust boundary in the path is a potential failure point. If input validation slips, kernel memory safety can fail fast and disastrously.
- AFD.sys has a long vulnerability history.
- Local access is a recurring prerequisite.
- Kernel validation is the central defensive control.
- SYSTEM compromise is the typical end state.
What Defenders Should Infer from Sparse Details
When Microsoft publishes a CVE with limited technical detail, defenders should resist two bad instincts. The first is to dismiss the bug because the advisory is vague. The second is to over-interpret sparse text as proof of a specific exploit chain. The right reaction is to treat the disclosure as actionable while remaining careful about what is known versus inferred.That is where the confidence metric becomes especially useful. If Microsoft signals enough confidence to maintain a public advisory, then defenders can reasonably treat the flaw as present and relevant even before exploit writeups appear. In practice, that means patching first, investigating later, and avoiding the trap of waiting for a proof-of-concept that may arrive only after attackers have already weaponized the issue.
Practical reading of the advisory
A sparse advisory still tells you several things. It tells you the affected component, the vulnerability class, and the vendor’s level of certainty. It also tells you that Microsoft believes the issue is worthy of tracking under a public CVE, which is itself a meaningful operational signal. The absence of detail does not mean the issue is unimportant.The right inference is that defenders should map the CVE to their Windows inventory, check whether the relevant build is exposed, and prioritize patch deployment based on privilege context and endpoint criticality. That is especially true when the vulnerable component is kernel-mode and deeply embedded in system networking behavior.
- Do not equate sparse detail with low risk.
- Do not assume exploitability from the CVE alone.
- Do treat the advisory as operationally real.
- Do validate affected builds in your estate.
Patch Management Implications
Security teams should read AFD.sys advisories as a patch-management test as much as a vulnerability alert. Kernel-level bugs tend to expose weaknesses in update workflows, asset visibility, and reboot coordination. If the fleet cannot quickly identify affected versions or deploy the fix at scale, the advisory becomes a management problem, not just a technical one.This is especially true for Windows environments with mixed endpoint populations. Laptops, desktops, VDI systems, RDS hosts, and application servers may all be exposed in different ways, and some may have update deferral policies that slow remediation. The more complex the fleet, the more important it is to translate the CVE into concrete operational tasks.
What administrators should do first
A disciplined response usually starts with inventory and ends with verification. Teams should identify whether the affected Windows builds are present, confirm which systems have the patch, and check whether any systems are lagging due to maintenance windows or unsupported applications. The process is mundane, but it is also what separates a patch from a security posture.- Identify impacted Windows versions and device classes.
- Confirm whether the relevant March 2026 update is installed.
- Prioritize systems with local admin risk or untrusted-user access.
- Reboot where required and verify post-install status.
- Review logs for suspicious local escalation behavior.
- Inventory is the first line of defense.
- Verification matters as much as deployment.
- Reboots are often the hidden scheduling constraint.
- Critical endpoints should be patched first.
Attack Surface and Likely Abuse Patterns
AFD.sys bugs are usually attractive to attackers because they fit neatly into post-exploitation workflows. A threat actor who has obtained a low-privileged account can use a local escalation to raise privileges and then pivot to more powerful actions. That can include disabling security controls, dumping credentials, or preparing lateral movement within a domain.The most important thing to understand is that local privilege escalation is not a minor footnote. In a modern intrusion, it often marks the transition from access to control. That makes AFD.sys a component that attackers may target not because it is exposed to the internet, but because it is reliably useful once they are inside.
Why AFD.sys is attractive to attackers
Kernel bugs in driver code can be exploited in many ways depending on the exact flaw class. In historical AFD cases, Microsoft has cited improper validation, double free, and other memory-safety or access-control problems. Those bug classes are especially valuable because they can often be turned into stable privilege escalation with enough research and testing.The value proposition for attackers is simple: one successful exploit can upgrade the entire compromise. In that sense, AFD.sys is not merely a driver; it is a privilege boundary worth attacking. That is why defenders should expect interest from both opportunistic malware authors and more advanced operators.
- Post-exploitation value is high.
- Kernel context increases weaponization interest.
- Privilege escalation can unlock persistence and credential theft.
- Stable local exploits are prized by threat actors.
Enterprise Risk Versus Consumer Risk
Enterprises should treat CVE-2026-26173 as a control problem affecting endpoint privilege hygiene. A single compromised workstation with a local escalation path can become the anchor point for a broader incident, especially if the user had access to internal systems, passwords in memory, or management tools. Large organizations also face the reality that patch rollout is rarely uniform, which makes any kernel bug a possible long-tail exposure.Consumers face a different but still meaningful risk profile. The average home device is less likely to be a stepping stone into a corporate environment, but it may still be vulnerable to malware that depends on privilege escalation. In that context, a local AFD.sys bug can help an attacker turn a transient infection into something persistent and harder to remove.
Different priorities, same patch
For enterprises, the priority is reducing blast radius and enforcing patch compliance. For consumers, the priority is simply staying current with Windows updates and minimizing risky local software behavior. Those goals overlap more than they differ: both depend on not leaving kernel drivers unpatched longer than necessary.The deeper lesson is that local vulnerabilities are only “local” until they are chained into broader abuse. That is why even users who rarely think about kernel code should care about a networking driver advisory. The path from ordinary desktop use to system compromise can be shorter than it looks.
- Enterprises must think in terms of blast radius.
- Consumers must think in terms of infection-to-escalation chains.
- Patch lag creates exposure in both environments.
- Local bugs often become stepping stones to bigger incidents.
Strengths and Opportunities
Microsoft’s handling of AFD.sys advisories has one major strength: the company gives defenders enough metadata to act, even when it does not publish every technical detail immediately. That balance can be frustrating for researchers, but it is often the right tradeoff for operational security. The confidence metric, in particular, gives administrators a better sense of how seriously to take the entry.There are also opportunities here for better enterprise discipline. A high-confidence kernel advisory is a useful trigger for asset validation, privileged account review, and patch telemetry checks. The same event can be used to improve update orchestration and to tighten local admin governance in ways that survive beyond a single CVE.
- Clear component identification helps inventory teams.
- Confidence metadata improves patch prioritization.
- Kernel advisories can drive stronger endpoint governance.
- Update verification can be folded into normal compliance checks.
- Privilege audits can reduce exploitation payoff.
- Historical precedent helps defenders interpret sparse advisories.
Risks and Concerns
The biggest risk is complacency. A sparse advisory can lull teams into thinking there is little to do, when the opposite is true: the less detail Microsoft publishes, the more important it is to rely on patch discipline and risk-based prioritization. Another concern is that local privilege escalation bugs often remain unnoticed until they are chained with another compromise, which means detection can lag behind exploitation.There is also a real danger of underestimating the kernel context. A bug in a networking driver is not just another application issue; it lives near the operating system’s trust core. That means even an issue that appears “local” can become a platform-level problem once it is weaponized.
- Sparse detail can create false reassurance.
- Local-only framing may hide broader chain risk.
- Kernel exposure raises the stakes materially.
- Patch drift across fleets can prolong vulnerability windows.
- Privileged local accounts increase attack value.
- Delayed verification can leave systems exposed after updates.
Looking Ahead
The next thing to watch is whether Microsoft or third-party researchers publish more technical detail about CVE-2026-26173, including the exact bug class and whether exploitation becomes public. If that happens, the advisory will move from a vendor-tracked kernel issue to a more concrete hunting and mitigation scenario. In the meantime, defenders should operate on the assumption that the issue is real, relevant, and worth patching promptly.It will also be important to see whether this advisory is part of a broader cluster of AFD.sys or kernel-driver issues. Historically, Windows networking and kernel components do not get singled out in isolation; they often appear in groups during Patch Tuesday or coordinated updates. That context can help security teams anticipate where the next weak point may emerge.
What to watch next
- Microsoft advisory updates or revised wording.
- Third-party technical writeups on the bug class.
- Signs of exploitation in the wild.
- Additional AFD.sys or kernel-driver CVEs in the same cycle.
- Enterprise patch compliance and reboot completion rates.
Source: MSRC Security Update Guide - Microsoft Security Response Center