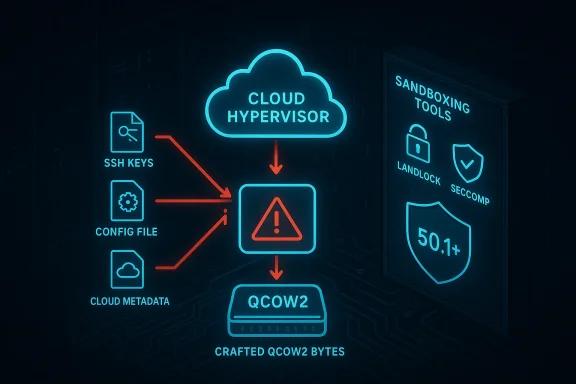
A crafty alteration to a VM disk header can make a guest VM read sensitive host files — that is the practical risk discovered in CVE-2026-27211, a high‑severity information‑disclosure flaw in Cloud Hypervisor that reintroduces a long‑standing class of image‑format parsing problems into modern cloud stacks.
Cloud Hypervisor is a lightweight, Rust‑based virtual machine monitor (VMM) aimed at cloud workloads and used by a growing number of cloud and edge projects. It supports multiple disk image formats and exposes virtio block devices to guests. The vulnerability tracked as CVE‑2026‑27211 affects Cloud Hypervisor releases from 34.0 through 50.0 and permits a malicious or compromised guest to induce the host VMM to expose arbitrary files to the guest under realistic conditions. The vendor fixed the bug in 50.1; operators running older builds must treat exposed deployments as at‑risk until they update.
This bug is an evolution of an old pattern: hypervisors and orchestration stacks often accept VM images or raw disks whose internal metadata can reference external files. If the hypervisor, image tooling, or management plane misclassifies an image and later interprets that crafted metadata, the hypervisor can be tricked into reading host files and making their contents available to the guest. CVE‑2026‑27211 follows that pattern but is notable for the trigger points and the low management‑plane interaction required to exploit it.
Key technical points, in plain language:
Two recurring failure modes are evident:
However, residual risks remain:
CVE‑2026‑27211 is a stark reminder that convenience features in virtualization — image auto‑detection, writable base images, and permissive format handling — can have outsized security costs. For cloud operators, the immediate imperative is to patch and harden; the strategic imperative is to eliminate assumptions of trust where arbitrary binary data flows into highly privileged code paths. Take the patch, lock down images, and treat image parsing like any other interface to untrusted input: parse it in a sandbox, with the strictest rules, and expect attackers to look for the smallest chink in the armor.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Cloud Hypervisor is a lightweight, Rust‑based virtual machine monitor (VMM) aimed at cloud workloads and used by a growing number of cloud and edge projects. It supports multiple disk image formats and exposes virtio block devices to guests. The vulnerability tracked as CVE‑2026‑27211 affects Cloud Hypervisor releases from 34.0 through 50.0 and permits a malicious or compromised guest to induce the host VMM to expose arbitrary files to the guest under realistic conditions. The vendor fixed the bug in 50.1; operators running older builds must treat exposed deployments as at‑risk until they update.This bug is an evolution of an old pattern: hypervisors and orchestration stacks often accept VM images or raw disks whose internal metadata can reference external files. If the hypervisor, image tooling, or management plane misclassifies an image and later interprets that crafted metadata, the hypervisor can be tricked into reading host files and making their contents available to the guest. CVE‑2026‑27211 follows that pattern but is notable for the trigger points and the low management‑plane interaction required to exploit it.
What the bug does — technical overview
At a high level, CVE‑2026‑27211 lets a guest overwrite part of its disk metadata (specifically the disk header) to embed a crafted QCOW2 structure that points at an arbitrary host path. When Cloud Hypervisor later scans or probes the image (for example, during a VM boot or a disk resize/inspection operation), its image auto‑detection logic recognizes the manipulated header as a QCOW2 image and proceeds to resolve the QCOW backing file or external data reference. Because the backing file path can be an absolute or otherwise crafted reference into the host filesystem, the result is that the hypervisor reads and serves the referenced host file contents back to the guest as if the file were part of the disk image.Key technical points, in plain language:
- QCOW2 and some other image formats include fields that can reference an external backing file or external data. These fields are not inherently dangerous — they are a legitimate format feature intended to support copy‑on‑write chains and external metadata — but only if image parsing is constrained to trusted environments and formats.
- The exploit path requires the guest to be able to write the underlying image bytes that the host later interprets. That means either the backing image bytes must be writable by the guest, or the initial image came from an untrusted source that can contain malicious headers.
- The hypervisor’s image auto‑detection and subsequent parsing logic is the attack surface. If a raw image is misinterpreted as a QCOW2 image because the first bytes were overwritten to contain a QCOW2 magic/header, the parser can be tricked into resolving external references.
- The attack does not require interactive cooperation from cloud management systems or the host administrator — a guest‑initiated reboot or a hypervisor‑driven disk scan is sufficient to trigger the problem, and the Cloud Hypervisor process continues running across the event.
- The amount of data exfiltrated depends on the host process privileges (what the hypervisor process can read) and the target file’s readable size, but certain sensitive files (for example, service credentials, local credentials files, or cloud metadata) are commonly accessible to hypervisor processes, making the impact severe.
Why this is important — threat and impact analysis
This class of vulnerability is highly relevant to multi‑tenant cloud providers, Platform as a Service (PaaS) operators, and anyone who runs untrusted or semi‑trusted workloads on shared infrastructure.- Confidentiality risk: The attack targets sensitive host files. In many cloud setups the hypervisor process or management agents have read access to host configuration files, temporary directories, cloud provider metadata, SSH keys, or other secrets. A guest obtaining those files can escalate or pivot substantially.
- Minimal privileges for exploitation: The exploit does not need privileged network access or complex race conditions; it hinges on the ability to write crafted bytes to a writable disk image or to supply images from untrusted origins. In many IaaS workflows, customers upload or manipulate images, making the attack surface realistic.
- Low interaction required: Because the guest can trigger the disk re‑probe with a reboot, unitary attacker control over a VM instance is sufficient to perform the operation; no further actions on the host or management plane are necessary.
- Widespread potential exposure: Cloud Hypervisor is used in diverse environments — from standalone VMs to lightweight VM‑based container runtimes — increasing the likelihood of real‑world exposure. When VMMs provide advanced features like live disk resizing or image format auto‑probing, the attack vectors multiply.
- Difficulty of detection: The hypervisor is reading a host file and copying it into a disk stream to the guest; from the host side that activity can look like legitimate image handling or maintenance. Without specialized detection (see below), exfiltration can be subtle and blend with normal disk operations.
Root causes and systemic lessons
CVE‑2026‑27211 traces back to several recurring systemic issues in virtualization stacks:- Trusting image metadata: Image formats (QCOW2, VMDK, etc.) were designed to be flexible and support external references. That flexibility is safe only when images come from trusted sources and when image handling code enforces strict rules about resolving external references.
- Auto‑detection complexities: Convenience features that auto‑detect image formats based on header bytes or magic numbers increase parsing complexity and can be abused by crafted headers. When detection is optimistic and permissive, attackers can label arbitrary bytes as a different format.
- Loose privilege boundaries: Hypervisor processes often run with broader privileges than necessary or are granted filesystem reachability that includes secrets. Minimizing the host filesystem surface that image‑handling code can access is critical.
- Management layer assumptions: Many orchestration tools assume uploaded images are benign and perform limited content validation. Without strict image validation and sandboxed parsing, these tools can be a vector for poisoning host‑visible data.
Exploitation prerequisites and realistic attacker models
For defenders, understanding the realistic exploitation scenarios is essential:- The guest must be able to modify the bytes of its own disk image (or provide an image at creation time) such that the overwritten header contains a QCOW2 backing‑file reference pointing to a host path.
- The host hypervisor process must have the ability to interpret that header later — via boot‑time probes, image scanning, or image conversion utilities invoked by the host or orchestration stack.
- The host process must have read access to the referenced host file. Many hypervisors and management agents run as users that can read certain system files, configuration files, or cloud provider metadata.
- The most straightforward attackers are tenants that control VMs (untrusted or rogue tenants), or adversaries able to supply VM images to a deployment that are later used by other tenants or by the same adversary in a different context.
What was fixed and how
The upstream maintainers patched the relevant image‑parsing and format‑detection logic in Cloud Hypervisor and released fixes that eliminate the insecure resolution path. The fix strategy followed several complementary lines:- Tighter image detection and handling: The VMM now avoids treating a raw image as a QCOW2 image simply because a few header bytes were present. Format probing was constrained and the code refuses to resolve external backing files for images that were explicitly opened as raw or in contexts that don’t permit external file resolution.
- Disallow resolving external references from untrusted images: The hypervisor enforces a policy that backing‑file/ external‑data resolution is permitted only when the image source is trusted and read‑only; images provided by tenants (or read/write images) are treated with maximum skepticism.
- Privilege and sandbox hardening: The maintainers added options and recommendations to constrain the image‑handling process with sandboxing primitives (process privilege reduction, Landlock where available, seccomp profiles, and stricter file‑permission checks).
- Default behavior changes: Where possible, safer defaults were introduced — for example, refusing to follow backing file references by default for images created or uploaded by unprivileged users.
Immediate mitigations and recommended actions for operators
If you run Cloud Hypervisor and cannot immediately upgrade, apply the following mitigations in order of urgency:- Patch to the fixed release as soon as possible. The definitive mitigation is to update the VMM to the patched release line that closes CVE‑2026‑27211.
- Make images immutable where possible. Do not expose writable image files to untrusted guests. Boot from read‑only images or use copy‑on‑write mechanisms that do not allow guests to mutate base image headers.
- Disable image format auto‑resolution for untrusted images. Configure the environment so that images uploaded by tenants are explicitly treated as raw, or are strictly validated, and ensure the hypervisor or management layer does not resolve backing files for such images.
- Enable sandboxing for hypervisor processes. Use Landlock (on supporting kernels), seccomp, AppArmor, or SELinux to limit the hypervisor’s ability to read arbitrary host files. Restrict the process’s working directories and mount namespaces.
- Harden file permissions and service accounts. Limit the set of host files readable by the hypervisor and management services. Move secrets out of world‑readable locations and restrict access to cloud metadata and credentials.
- Block use of untrusted images. Implement image‑validation gates in your upload pipeline: reject images with suspicious or non‑standard headers or any images that claim external backing files unless those references are validated.
- Audit and monitor image‑handling calls. Detecting unexpected calls to image utilities or unusual disk‑read patterns can provide early warning of attempts to abuse image parsing.
Detection and incident response guidance
Detecting this particular exfiltration method requires focusing on image handling, not just network egress:- Monitor for unusual image probe or conversion activity. Look for qemu‑img invocations, libguestfs, or any image‑conversion utilities running in contexts where they normally shouldn’t.
- Watch for frequent or unexpected VM reboots tied to image events. An attacker can trigger a reboot to force a disk scan; correlate reboots with image operations and management‑plane events.
- Audit hypervisor file reads. If possible, instrument the hypervisor process with file‑access auditing (via kernel audit or in‑process logging) to flag reads of sensitive host files (for example configuration, cloud metadata, or secret stores).
- Scan image files for embedded backing file strings. Running a policy check that inspects image headers for backing file fields or non‑conforming magic bytes can detect poisoned images before they are used.
- Capture and analyze disk traffic from the guest. If a disk device suddenly contains host file contents at sectors where previously there was only guest data, that indicates a successful exfiltration.
- Rotate keys and credentials after suspected exposure. If you find evidence that a host file containing credentials was read, rotate secrets and treat the affected host as compromised until proven otherwise.
Long‑term remediation: architecture and policy changes
This vulnerability is a reminder to re‑examine how image formats and convenience features are trusted in cloud stacks. Suggested long‑term controls:- Adopt signed, immutable images for production tenants. Signed image catalogs and attested images reduce the risk that untrusted content can reach a host.
- Never give user‑supplied images the same trust level as vendor images. Treat images from tenants as potentially hostile by default and run parsing in isolated, ephemeral sandboxes.
- Move secrets out of host files where feasible. Use short‑lived credentials, IAM roles, and metadata endpoints that require explicit scopes and protections rather than long‑lived host files.
- Limit privileged hypervisor code paths. Where hypervisor features need to access host files, require explicit operator approval and isolate those tasks to dedicated, minimal‑privilege helper processes.
- Increase automation in image validation. Integrate format checks and header inspections into CI pipelines and upload workflows so invalid artifacts are rejected upstream.
- Harden management primitives used for live operations. Live disk resize, image conversion, and format probing are high‑risk operations; consider requiring operator confirmation or additional access checks before such operations run on images supplied by tenants.
Broader context — why image parsing keeps biting us
Image formats are powerful and complex because they need to support features like compression, copy‑on‑write chains, and external metadata. That complexity, combined with decades of legacy format behavior and tricky edge cases in auto‑detection, makes parsing code a perennial target for attackers.Two recurring failure modes are evident:
- Format features used innocently for performance or functionality become attack vectors when inputs are untrusted. Backing files and external data make sense in controlled environments but are dangerous when user‑controlled images can inject reference paths.
- Convenience features (auto‑detection, permissive fallback behavior) expand the attack surface. A system that silently tries multiple parsers invites crafted headers to mislabel an image and get parsed by the wrong code path.
Practical checklist: what to do in the next 72 hours
- Update all Cloud Hypervisor instances to the vendor‑released fixed version.
- Block new image uploads from untrusted sources until image validation gates are in place.
- Make guest images read‑only where possible and avoid exposing writable host image files to untrusted guests.
- Apply sandboxing and process‑hardening to the hypervisor and image‑handling helpers; enable Landlock or equivalent where available.
- Audit for suspicious reboots, qemu‑img activity, and any unexpected file reads by hypervisor processes.
- Rotate any host credentials that may have been exposed if you detect signs of exploitation.
- Document and test an incident response playbook specific to VM image manipulation and host‑file exfiltration.
Final assessment — strengths of the fix and remaining risks
The upstream patch addresses the immediate parsing and format‑resolution logic that allowed this exploitation chain, and the maintainers introduced safer defaults and sandboxing recommendations. Those are strong, targeted fixes that materially reduce the risk.However, residual risks remain:
- Operational drift: Even patched VMMs remain vulnerable if operators reintroduce permissive configuration settings (for example, explicitly enabling backing‑file resolution for convenience).
- Ecosystem fragmentation: The same pattern can appear in other VMMs, management tools, or downstream projects that embed image parsing code; operators must track the entire stack (libvirt, QEMU, orchestration layers).
- Legacy images and tooling: Older images or conversion tools may still present attack paths if they are run in contexts that assume image content is trusted.
- Detection gaps: Exfiltration via modified images is subtle and may evade conventional network‑centric monitoring unless teams add specific checks for image parsing activity and hypervisor file reads.
CVE‑2026‑27211 is a stark reminder that convenience features in virtualization — image auto‑detection, writable base images, and permissive format handling — can have outsized security costs. For cloud operators, the immediate imperative is to patch and harden; the strategic imperative is to eliminate assumptions of trust where arbitrary binary data flows into highly privileged code paths. Take the patch, lock down images, and treat image parsing like any other interface to untrusted input: parse it in a sandbox, with the strictest rules, and expect attackers to look for the smallest chink in the armor.
Source: MSRC Security Update Guide - Microsoft Security Response Center