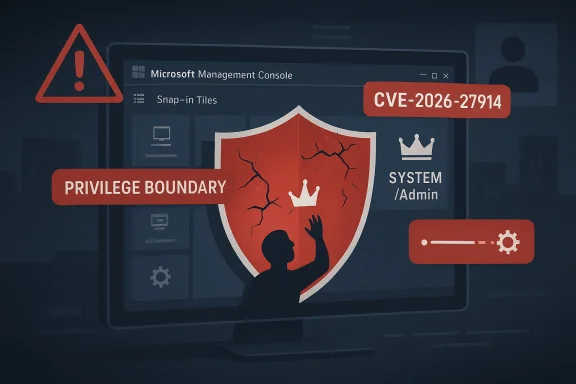
Microsoft has assigned CVE-2026-27914 to a Microsoft Management Console (MMC) elevation-of-privilege vulnerability, and the timing matters as much as the label. The record indicates a local flaw with low attack complexity and high confidentiality, integrity, and availability impact, which is exactly the combination administrators tend to treat as urgent once a fix is available. The vendor description is still terse, but the current public signal suggests a real privilege boundary failure rather than a speculative theory. (cvefeed.io)
Microsoft Management Console has sat at the center of Windows administration for decades. MMC is the shell behind many of the snap-ins that IT staff use to manage local and remote systems, so any weakness in its privilege handling has outsized consequences. In practical terms, if MMC allows a user to cross from an ordinary administrative context into a more privileged one, the result can range from local system compromise to broader domain movement.
This is not the first time the console ecosystem has intersected with privilege issues. Microsoft’s older security bulletins show that console-adjacent components and management workflows have historically been attractive attack surfaces, in part because they are trusted, widely deployed, and deeply integrated into administrative workflows. The reason defenders keep paying attention is simple: management tools often run with more authority than the applications they control, and that asymmetry is exactly what attackers want to exploit.
The public description for CVE-2026-27914 is currently short, but it is still meaningful. Cvefeed’s entry mirrors Microsoft’s record closely enough to confirm the basic shape of the issue: improper access control in Microsoft Management Console lets an authorized attacker elevate privileges locally. That wording matters because it suggests the attacker already has some level of legitimate access, but can use a weakness in the console’s authorization logic to gain a stronger foothold. (cvefeed.io)
The scoring also gives defenders a rough sense of urgency. The advisory is currently shown with CVSS 3.1 7.8 High, and the vector implies a local attack requiring low privileges and no user interaction. That combination is especially important in enterprise environments, because it usually means the exploit path begins with a foothold that could come from a compromised endpoint, a misused admin account, or malicious software already running under a limited context. (cvefeed.io)
That uncertainty should not be confused with weakness in the report. On the contrary, a vendor-assigned CVE usually means Microsoft has enough confidence to track, patch, or at least formally document the issue. In operational terms, that is stronger evidence than a generic claim of “possible privilege escalation,” and defenders should treat it as a confirmed problem even before the technical breakdown becomes public. (cvefeed.io)
The description also says the attacker must be authorized, which implies the exploit is local and likely relies on an already authenticated user or process. That does not make the vulnerability less serious; it changes the threat model. In modern Windows incidents, initial access is often only the first step, and local elevation is what turns a contained compromise into a full-system event. (cvefeed.io)
The 7.8 High score suggests this is not a niche bug. A local elevation-of-privilege issue with high impact can often be chained with phishing, malware, malicious scripts, or abuse of an over-permissioned endpoint to move from a limited account to a stronger one. In the real world, many attacks are not single-step compromises; they are chains, and local privilege escalation is one of the most valuable links in that chain. (cvefeed.io)
This is also why Microsoft’s historical guidance around elevation prompts and privilege boundaries remains relevant. Windows has long treated elevation as a sensitive operation because it changes the trust relationship between the user and the system. When the management plane itself fails that trust test, administrators lose one of the operating system’s core defense layers.
Historically, management tooling has been a soft spot whenever access control goes wrong. The core problem is the same across generations of Windows administration tools: if a low-privilege user can coerce a high-privilege component into doing something on their behalf, the system’s boundary is no longer enforcing the intended policy. CVE-2026-27914 appears to sit squarely in that category. (cvefeed.io)
From a defender’s perspective, this is the kind of issue that deserves attention even before weaponization appears. Tools like MMC are deeply embedded in enterprise workflow, which means they are often installed everywhere and used by many people. The larger the deployment footprint, the greater the chance that a single access-control mistake will matter in production. That is the hidden cost of ubiquitous administration tooling.
The most likely danger is post-compromise escalation. If a workstation, jump host, or admin workstation is already exposed to malware or an attacker with a low-privilege account, a local EoP in MMC may be enough to gain the authority needed for credential dumping, persistence, or policy tampering. In enterprise environments, that can be the difference between one infected device and a domain incident. (cvefeed.io)
Administrators should also think about tooling inventory. If MMC snap-ins or scripts are launched through automation, remote support, or third-party management tools, the attack surface can be broader than the console icon suggests. This is one of those cases where the visible app is only the front door.
That means the consumer story here is really about post-infection amplification. A browser exploit, malicious installer, or trojan that gets only limited rights can become more dangerous if it can trigger a local privilege escalation afterward. Consumers rarely think in those terms, but attackers absolutely do. (cvefeed.io)
It is also worth remembering that Windows privileges are not abstract. When malware gains administrative control, it can disable protections, persist across reboots, or tamper with system settings in ways that are much harder to unwind than a normal app infection. That is why an EoP CVE is never “just” a lower-tier issue. (cvefeed.io)
Patch management for local privilege escalations should be more aggressive than usual on systems that host sensitive work. If an administrator can use MMC from a machine that is also used for browsing, email, or third-party tools, then the attack chain becomes easier. Separating high-value admin activity from general-purpose use remains one of the best compensating controls.
There is also an indirect competitive angle. Enterprise buyers compare platforms not only by functionality but by the security burden each platform imposes on administrators. When a management interface carries privilege risk, the response is rarely “abandon the product.” Instead, customers demand better isolation, stronger guardrails, and more resilient privilege boundaries, which is the kind of pressure that reshapes product design over time.
The lesson is consistent with Microsoft’s own historic security guidance: elevation is a sensitive boundary, and anything that weakens it deserves priority attention. Attackers often need only one successful escalation to turn a manageable incident into a large one, and enterprise defenders know that one step up can be enough.
The broader opportunity is to use the incident as a forcing function for tighter administrative controls. A good security team treats every local EoP as a chance to reduce the privilege surface that made it dangerous in the first place. That can improve resilience long after this specific CVE is patched.
Another concern is the current lack of technical detail in the public browser view. When details are sparse, defenders may struggle to determine whether they need a narrow fix, a broad mitigation, or a temporary operational workaround. That ambiguity is not a reason to ignore the vulnerability; it is a reason to monitor Microsoft’s update channel closely.
The second milestone will be whether third-party researchers, exploit trackers, or threat intelligence vendors identify a practical attack chain. A local EoP only becomes more urgent when the ecosystem demonstrates how it can be chained, particularly if the flaw becomes useful in real-world intrusion sets. Historically, that is the point where a vulnerability moves from “important to patch” to “essential to prioritize immediately.”
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Microsoft Management Console has sat at the center of Windows administration for decades. MMC is the shell behind many of the snap-ins that IT staff use to manage local and remote systems, so any weakness in its privilege handling has outsized consequences. In practical terms, if MMC allows a user to cross from an ordinary administrative context into a more privileged one, the result can range from local system compromise to broader domain movement.This is not the first time the console ecosystem has intersected with privilege issues. Microsoft’s older security bulletins show that console-adjacent components and management workflows have historically been attractive attack surfaces, in part because they are trusted, widely deployed, and deeply integrated into administrative workflows. The reason defenders keep paying attention is simple: management tools often run with more authority than the applications they control, and that asymmetry is exactly what attackers want to exploit.
The public description for CVE-2026-27914 is currently short, but it is still meaningful. Cvefeed’s entry mirrors Microsoft’s record closely enough to confirm the basic shape of the issue: improper access control in Microsoft Management Console lets an authorized attacker elevate privileges locally. That wording matters because it suggests the attacker already has some level of legitimate access, but can use a weakness in the console’s authorization logic to gain a stronger foothold. (cvefeed.io)
The scoring also gives defenders a rough sense of urgency. The advisory is currently shown with CVSS 3.1 7.8 High, and the vector implies a local attack requiring low privileges and no user interaction. That combination is especially important in enterprise environments, because it usually means the exploit path begins with a foothold that could come from a compromised endpoint, a misused admin account, or malicious software already running under a limited context. (cvefeed.io)
What the Advisory Currently Tells Us
The most important thing to understand about the advisory is what it does and does not say. Microsoft has already acknowledged the CVE, which gives the vulnerability a level of certainty that rumors and third-party writeups cannot match. But the public page itself is still not rendering its full content in the browser view, so the exact mechanism, affected versions, and patch details remain opaque for the moment. (msrc.microsoft.com)That uncertainty should not be confused with weakness in the report. On the contrary, a vendor-assigned CVE usually means Microsoft has enough confidence to track, patch, or at least formally document the issue. In operational terms, that is stronger evidence than a generic claim of “possible privilege escalation,” and defenders should treat it as a confirmed problem even before the technical breakdown becomes public. (cvefeed.io)
Why the wording matters
The phrase “improper access control” is broad, but it often points to authorization mistakes rather than memory corruption. That can mean a broken permission check, an insecure trust boundary, or an object that can be manipulated in a way the original designers did not intend. Those classes of flaws can be deceptively dangerous because they frequently survive code hardening that would stop classic buffer-overflow style exploits. (cvefeed.io)The description also says the attacker must be authorized, which implies the exploit is local and likely relies on an already authenticated user or process. That does not make the vulnerability less serious; it changes the threat model. In modern Windows incidents, initial access is often only the first step, and local elevation is what turns a contained compromise into a full-system event. (cvefeed.io)
- Confirmed CVE assignment increases confidence in the issue.
- Local exploitability makes the flaw especially relevant after initial compromise.
- Low attack complexity means the path may be easier to weaponize.
- High impact raises the stakes for enterprise systems.
- No public remote-exploit indication limits one attack path, but not the risk. (cvefeed.io)
Confidence, Severity, and What They Imply
The user-provided definition of the metric fits this case well: confidence rises when a vulnerability is acknowledged by the vendor, and urgency rises when the issue is believed to exist with certainty. That is exactly why a named CVE matters. Even if the exploit mechanics are not public, the existence of the flaw is no longer hypothetical, which is a meaningful distinction for patch planning and incident response. (cvefeed.io)The 7.8 High score suggests this is not a niche bug. A local elevation-of-privilege issue with high impact can often be chained with phishing, malware, malicious scripts, or abuse of an over-permissioned endpoint to move from a limited account to a stronger one. In the real world, many attacks are not single-step compromises; they are chains, and local privilege escalation is one of the most valuable links in that chain. (cvefeed.io)
Why local bugs still matter
Defenders sometimes underestimate local vulnerabilities because they are not remotely reachable on their own. That is a mistake. Once an attacker lands a user session, a browser foothold, or an agent running under a constrained identity, a local EoP can become the bridge to credential theft, persistence, and lateral movement. In that sense, a local flaw can have network-wide consequences. (cvefeed.io)This is also why Microsoft’s historical guidance around elevation prompts and privilege boundaries remains relevant. Windows has long treated elevation as a sensitive operation because it changes the trust relationship between the user and the system. When the management plane itself fails that trust test, administrators lose one of the operating system’s core defense layers.
- A high CVSS score signals substantial risk, not just a theoretical flaw.
- Low privileges required means an attacker may only need a weak foothold.
- No user interaction generally increases real-world exploitability.
- Local attack vector makes endpoint protection and least privilege more important.
- High impact on CIA suggests serious business disruption if exploited. (cvefeed.io)
Microsoft Management Console as an Attack Surface
MMC is not just another utility. It is a framework through which administrators load snap-ins, inspect policies, manage services, and administer critical Windows components. That makes it attractive to attackers because it is already trusted by users and systems, and because many administrators run it from privileged accounts as part of their daily routine.Historically, management tooling has been a soft spot whenever access control goes wrong. The core problem is the same across generations of Windows administration tools: if a low-privilege user can coerce a high-privilege component into doing something on their behalf, the system’s boundary is no longer enforcing the intended policy. CVE-2026-27914 appears to sit squarely in that category. (cvefeed.io)
The administrative trust problem
MMC often runs in a context that assumes the operator is trusted. That is convenient for administrators, but dangerous if an attacker can affect how the console interprets objects, snap-ins, or permissions. A bug in access control can therefore have consequences that go beyond the console itself, because MMC is frequently the doorway to services, policies, certificates, or other privileged configuration surfaces.From a defender’s perspective, this is the kind of issue that deserves attention even before weaponization appears. Tools like MMC are deeply embedded in enterprise workflow, which means they are often installed everywhere and used by many people. The larger the deployment footprint, the greater the chance that a single access-control mistake will matter in production. That is the hidden cost of ubiquitous administration tooling.
- MMC is widely trusted by operators and endpoints.
- Administrative tools often run with elevated rights.
- Access-control bugs can affect many workflows at once.
- Console-based attacks may chain with stolen credentials.
- Management-plane weaknesses can accelerate lateral movement.
What Enterprises Should Infer Right Now
Enterprises should read CVE-2026-27914 as a patch-priority local privilege escalation rather than a remote outbreak scenario. That distinction affects the response plan. It is less about perimeter blocking and more about endpoint hygiene, account separation, and rapid update deployment on systems where administrators use MMC or where software can invoke it indirectly. (cvefeed.io)The most likely danger is post-compromise escalation. If a workstation, jump host, or admin workstation is already exposed to malware or an attacker with a low-privilege account, a local EoP in MMC may be enough to gain the authority needed for credential dumping, persistence, or policy tampering. In enterprise environments, that can be the difference between one infected device and a domain incident. (cvefeed.io)
Where to focus first
The first systems to review are typically the ones with the highest administrative value. That includes endpoint management stations, servers used for console-based administration, and any shared workstations where privileged staff operate with more than one identity. Segmentation and privileged access workstations matter here because a local flaw is only as useful to the attacker as the foothold they can obtain.Administrators should also think about tooling inventory. If MMC snap-ins or scripts are launched through automation, remote support, or third-party management tools, the attack surface can be broader than the console icon suggests. This is one of those cases where the visible app is only the front door.
- Prioritize admin workstations and jump boxes.
- Review systems where multiple privilege tiers are used.
- Watch for unexpected MMC launches or scripted console use.
- Verify rapid patch deployment in endpoint management rings.
- Recheck least privilege assumptions for administrative staff. (cvefeed.io)
Consumer Impact and Practical Risk
For ordinary consumers, the risk profile is different but still relevant. Most home users do not spend their day inside MMC, and that lowers the chance of direct exposure through normal activity. But if malware already exists on a consumer PC, a local elevation flaw can help it escape a limited user context and become much harder to remove. (cvefeed.io)That means the consumer story here is really about post-infection amplification. A browser exploit, malicious installer, or trojan that gets only limited rights can become more dangerous if it can trigger a local privilege escalation afterward. Consumers rarely think in those terms, but attackers absolutely do. (cvefeed.io)
What home users should take away
The main practical advice is straightforward: install the relevant Windows updates promptly when Microsoft publishes the fix, keep security software active, and avoid running as an administrator for routine work. Those habits do not eliminate the bug, but they reduce the chance that it becomes part of a multi-stage compromise. Good hygiene still matters when the flaw is local.It is also worth remembering that Windows privileges are not abstract. When malware gains administrative control, it can disable protections, persist across reboots, or tamper with system settings in ways that are much harder to unwind than a normal app infection. That is why an EoP CVE is never “just” a lower-tier issue. (cvefeed.io)
- Keep Windows and Defender updates current.
- Avoid everyday use of administrator accounts.
- Treat unknown installers and scripts with caution.
- Reboot after patching if prompted.
- Watch for unusual system prompts or console behavior. (cvefeed.io)
Patch Management and Response Strategy
Because the public advisory page is still not rendering in the browser, the exact patch package and affected build numbers were not available in the content we could directly inspect. That means the safe operational assumption is to watch the Microsoft Security Response Center advisory closely and prepare to deploy the update as soon as it appears in the standard servicing channel. Delay is the enemy here. (msrc.microsoft.com)Patch management for local privilege escalations should be more aggressive than usual on systems that host sensitive work. If an administrator can use MMC from a machine that is also used for browsing, email, or third-party tools, then the attack chain becomes easier. Separating high-value admin activity from general-purpose use remains one of the best compensating controls.
A practical response sequence
- Identify any systems that regularly use MMC for administration.
- Track Microsoft’s release of the fix in the servicing channels you manage.
- Prioritize pilot deployment on admin endpoints before broad rollout.
- Verify that least-privilege accounts are enforced where possible.
- Review incident logs for unusual MMC invocation or privilege changes. (cvefeed.io)
- Treat the issue as a patch-now candidate.
- Focus on admin endpoints first.
- Keep an eye on privilege changes and console activity.
- Use segmentation to reduce the blast radius.
- Coordinate with help desk and security operations teams. (cvefeed.io)
Competitive and Ecosystem Implications
Microsoft’s rapid disclosure of a console-related EoP matters beyond a single CVE. Windows remains the dominant enterprise management platform, and every high-profile privilege issue reinforces why endpoint hardening, role separation, and defensive telemetry continue to be central to enterprise security strategy. The broader ecosystem interprets these advisories as signals about where attackers may next concentrate effort.There is also an indirect competitive angle. Enterprise buyers compare platforms not only by functionality but by the security burden each platform imposes on administrators. When a management interface carries privilege risk, the response is rarely “abandon the product.” Instead, customers demand better isolation, stronger guardrails, and more resilient privilege boundaries, which is the kind of pressure that reshapes product design over time.
Why this matters to security teams
Security teams increasingly judge management tools by how well they reduce blast radius. If a console can be abused to elevate privileges, then it becomes part of the threat model for every admin workstation it touches. That means the security conversation is not just about patching; it is about redesigning administrative habits around trust minimization. (cvefeed.io)The lesson is consistent with Microsoft’s own historic security guidance: elevation is a sensitive boundary, and anything that weakens it deserves priority attention. Attackers often need only one successful escalation to turn a manageable incident into a large one, and enterprise defenders know that one step up can be enough.
- Reinforces the value of privileged access workstations.
- Encourages least-privilege administration models.
- Highlights the need for console hardening.
- Nudges vendors toward stronger authorization checks.
- Expands interest in behavioral detection over signature-only defenses.
Strengths and Opportunities
The positive reading of this event is that Microsoft has already acknowledged the issue, which means defenders are not waiting on rumor or reverse-engineered speculation. A formal CVE provides a clean handle for patch tracking, risk registers, and asset management workflows. It also gives organizations a specific issue to hunt for in their vulnerability management systems.The broader opportunity is to use the incident as a forcing function for tighter administrative controls. A good security team treats every local EoP as a chance to reduce the privilege surface that made it dangerous in the first place. That can improve resilience long after this specific CVE is patched.
- Formal CVE assignment improves clarity and tracking.
- The local nature of the issue supports targeted hardening.
- High impact makes executive attention easier to secure.
- Microsoft’s ecosystem can roll the fix into standard servicing.
- Enterprises can use the event to review admin separation.
- Security teams can improve telemetry around console usage.
- The advisory can strengthen least-privilege governance across Windows fleets.
Risks and Concerns
The biggest concern is that local privilege escalations are often underappreciated until they are chained into larger compromises. If CVE-2026-27914 becomes part of an intrusion path, the result could be far more serious than the standalone score suggests. Because the issue touches a trusted Windows management component, it also carries a higher-than-average risk of misuse by attackers who are already inside the environment.Another concern is the current lack of technical detail in the public browser view. When details are sparse, defenders may struggle to determine whether they need a narrow fix, a broad mitigation, or a temporary operational workaround. That ambiguity is not a reason to ignore the vulnerability; it is a reason to monitor Microsoft’s update channel closely.
- Local EoPs are ideal post-compromise tools.
- Sparse technical detail can slow risk triage.
- Console trust makes exploitation potentially hard to notice.
- Attackers may chain this with phishing or malware.
- Shared admin systems increase the blast radius.
- Delayed patching raises the odds of weaponization.
- Misconfigured privilege boundaries could amplify the impact.
Looking Ahead
The next key milestone will be Microsoft’s publication of the full advisory details, including affected versions, patch availability, and any mitigations or workarounds. Once that information appears, defenders will be able to turn a high-level warning into a concrete remediation plan. Until then, the safest posture is to assume this is a real and important local escalation flaw and plan accordingly. (msrc.microsoft.com)The second milestone will be whether third-party researchers, exploit trackers, or threat intelligence vendors identify a practical attack chain. A local EoP only becomes more urgent when the ecosystem demonstrates how it can be chained, particularly if the flaw becomes useful in real-world intrusion sets. Historically, that is the point where a vulnerability moves from “important to patch” to “essential to prioritize immediately.”
What to watch next
- Microsoft’s full MSRC advisory text and patch notes.
- Any update to the reported affected product versions.
- Evidence of proof-of-concept code or exploit chaining.
- Telemetry indicating unusual MMC activity on admin systems.
- Security vendor guidance on temporary mitigations or detection logic.
Source: MSRC Security Update Guide - Microsoft Security Response Center