Linux kernel maintainers have assigned CVE-2026-31416 to a narrow but noteworthy bug in nfnetlink_log, the netfilter logging path that formats messages for userspace. The issue is not a classic memory-corruption headline; instead, it is a correctness fix that ensures NLMSG_DONE accounts for the netlink header size as well as the attribute payload. According to the kernel’s own CVE policy, that kind of bug can still earn a CVE because the project intentionally tags many fixes that may have security relevance even when exploitation is not obvious at first glance. (docs.kernel.org)
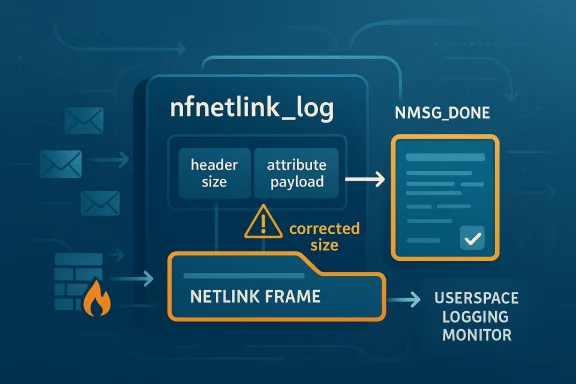
The basic technical story is straightforward. A follow-up fix corrected a size calculation so the kernel would not undercount the total space needed for a netlink message. That matters because netlink framing is strict: if the kernel builds a message with a size that is too small, it can trigger a WARN splat and the message may be dropped rather than delivered cleanly. The published description explicitly says the visible effect is a warning plus message loss, and that there are no other known ill effects.
That makes this CVE unusual in the way many Linux kernel CVEs are unusual: the bug is real, the fix is real, but the immediate blast radius appears modest. The Linux kernel community has long noted that CVEs are often assigned to bug fixes where exploitability is not yet proven, because the kernel sits so close to the hardware and so many subsystems can turn “just a bug” into a security-relevant issue depending on context. The kernel documentation says the team is deliberately cautious and that applicability depends on the system and kernel paths involved. (docs.kernel.org)
This case also reflects the stable-kernel workflow. The CVE record ties back to upstream stable commits, which is how Linux often maps a security identifier to a specific code change. The important operational takeaway is not that the world is on fire; it is that maintainers found a bug in a netlink accounting path, fixed it, and then tracked that fix through the kernel’s usual security-assignment machinery.
For WindowsForum readers, the more interesting question is what this says about Linux kernel hardening in 2026. The answer is that a lot of the kernel’s security work now centers on precision: message sizes, lifetimes, accounting, state transitions, and edge cases that rarely make headlines but can destabilize production systems. That trend is visible across modern kernel CVEs, including the one at hand. (docs.kernel.org)
Netlink itself is a structured kernel-to-userspace messaging system with strict framing rules, and those rules matter because many higher-level tools depend on accurate message construction. A message that is only a few bytes off can be rejected, truncated, or warned about depending on the code path. In practical terms, that means a low-level accounting mistake can become visible as a dropped event, incomplete logging, or noisy kernel diagnostics. That is not dramatic, but it is operationally important.
The CVE description says this bug is a follow-up to an older fix. That phrase is worth emphasizing because it shows the layered nature of kernel maintenance. One bug gets corrected, but then a related path turns out to have a slightly different accounting assumption, and that second-order issue has to be fixed too. In other words, kernel security work is often iterative rather than one-and-done.
The broader Linux CVE process also explains why a bug like this becomes public. The kernel docs say CVEs are assigned after a fix lands in a stable tree, not before, and that the assignment is tracked by the commit ID of the original fix. They also say the kernel team may assign CVEs to fixes even when the exploitability is unclear, because that is part of how the project keeps its vulnerability catalog coherent. (docs.kernel.org)
That approach has a downstream benefit for enterprises: it creates a machine-readable trail from source fix to public advisory to distro update. Microsoft’s Security Update Guide has increasingly become part of that ecosystem, and Microsoft has documented its broader effort to surface Linux-related security information in the same disclosure model used for Microsoft products. The result is a more centralized intake path for defenders, even when the underlying bug lives far from Windows.
That sort of bug often does not lead to an immediate crash. More commonly, it produces a warning, a rejected packet, or a silent failure in message delivery. Those outcomes can still matter a great deal for logging, telemetry, or debugging workflows, especially in environments that rely on nfnetlink output for security visibility. A message that never arrives is a security problem if the whole point of the path is to observe what happened.
Still, kernel CVEs often begin with modest language. The Linux project’s own documentation warns that applicability is highly system-dependent and that any bug may become security-relevant in a specific deployment. That is why defenders should treat “low impact” as a triage clue, not a dismissal. (docs.kernel.org)
For userspace consumers, the practical effect is likely to be missing log records or noisy diagnostics rather than a visible system failure. That distinction matters because security teams often triage by symptom, and a dropped logging message can look like a harmless telemetry glitch until it undermines an audit trail. If your monitoring depends on complete kernel-side event delivery, “just a warning” is not always just a warning.
That makes this a classic example of a bug that is security-adjacent rather than obviously exploitable. A malformed accounting path can still matter because kernel warnings can destabilize workloads, pollute logs, and break assumptions in management tooling. In long-running production systems, those side effects can become expensive even when the kernel itself survives.
This is also why the vulnerability should not be dismissed as duplicate noise. A second-order fix can reveal that the earlier correction was incomplete in one specific message path, and incomplete fixes are exactly the kind of thing stable trees try to catch before they spread widely. (docs.kernel.org)
Because netfilter is so central, kernel maintainers tend to be careful about how they classify defects there. A bug that only affects message sizing might look tame in isolation, but it still affects a subsystem that is used by security software, traffic inspection tools, and diagnostic pipelines. That alone makes the issue worth tracking as a CVE instead of burying it in a changelog footnote. (docs.kernel.org)
That distinction is particularly important in security operations centers. Loss of telemetry is dangerous because it creates blind spots, and blind spots are exactly where attackers try to hide. Even if this CVE is not exploitable in the classic sense, it still deserves attention from teams that treat logging as a first-class control.
That is why patching discipline matters here even if severity looks low. The kernel documentation explicitly advises taking released kernel changes as a unified whole rather than cherry-picking individual fixes, because many issues are solved by the sum of several related corrections. (docs.kernel.org)
The public language strongly suggests a low-to-moderate operational issue rather than a high-severity exploit primitive. Still, Linux’s own CVE policy warns that the absence of obvious exploitability at the time of fix does not mean a bug is irrelevant to security. The project assigns CVEs conservatively, precisely because later analysis may reveal broader implications. (docs.kernel.org)
That does not make the CVE less real. It just means teams must read the description carefully and apply it to their own kernel build, workload, and netfilter usage. In practice, that is often better than blindly following a score that may not reflect the local attack surface. (docs.kernel.org)
For consumers, the likelihood of direct impact is lower unless they run specialized Linux networking stacks, custom firewalling, or developer-oriented packet inspection tools. That said, many consumer-adjacent devices use Linux under the hood, so the distinction between “consumer” and “embedded infrastructure” is often thinner than it looks. The patch may be tiny, but the deployment surface is broad. (docs.kernel.org)
That model also explains why the same issue can surface in multiple downstream channels. Microsoft, for example, has positioned the Security Update Guide as a unified place to surface CVEs and related advisories, including non-Microsoft issues that matter to customers. In practice, that means a Linux CVE can become visible to Windows-heavy IT teams because their vulnerability management systems ingest those feeds.
That lag is why a low-severity kernel bug can still produce meaningful risk. If the flawed path is part of a compliance or monitoring chain, delayed patching can preserve a blind spot long after the advisory is public. Operational fragility is often the real cost of “minor” bugs. (docs.kernel.org)
That broader visibility is good news, but it also creates a responsibility for administrators to read the technical detail instead of treating every CVE as equally urgent. A precise bug in a specialized kernel module should be prioritized differently from a remotely exploitable flaw in a public service. (docs.kernel.org)
This is especially relevant for security appliances, containers hosts with custom packet filtering, and embedded devices that rely on kernel-generated logs for audit trails. In those environments, a dropped netlink message can become a troubleshooting problem first and a security problem second. The order matters less than the result.
If your fleet uses multiple kernel streams, this is a good reminder that “patched upstream” does not always mean “patched here.” Stable-tree fixes still need to be carried into distro builds, and that can take time depending on support policy and maintenance cadence.
That makes this CVE a good case study in why log integrity matters. A security tool can only alert on what it receives, and missing kernel events can create a false sense of normality in environments that depend on netfilter telemetry.
It also highlights a healthy maintenance culture in the Linux kernel ecosystem. Small follow-up fixes are not a sign of weakness; they are a sign that maintainers are willing to keep tightening code paths until accounting is right. That reduces long-term technical debt and improves confidence in stable backports.
There is also the risk of false confidence. Because the record currently lacks a CVSS score, teams may be tempted to postpone action until scoring appears. That can be a mistake if the affected kernel path is already central to a production logging pipeline.
It is also worth watching whether additional commentary emerges about the scope of the bug. Some kernel CVEs start with a tightly worded description and later gain a more nuanced operational interpretation as distributions and maintainers weigh in. If that happens here, it will likely be about observability impact rather than a major expansion of exploitability. (docs.kernel.org)
CVE-2026-31416 is therefore best understood as a small bug with real operational meaning. It does not look like the kind of flaw that defines a news cycle, but it does fit the kind of kernel maintenance issue that rewards careful patching and disciplined validation. In 2026, that may be the most important lesson of all: the quiet fixes are often the ones that keep the rest of the stack honest.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The basic technical story is straightforward. A follow-up fix corrected a size calculation so the kernel would not undercount the total space needed for a netlink message. That matters because netlink framing is strict: if the kernel builds a message with a size that is too small, it can trigger a WARN splat and the message may be dropped rather than delivered cleanly. The published description explicitly says the visible effect is a warning plus message loss, and that there are no other known ill effects.That makes this CVE unusual in the way many Linux kernel CVEs are unusual: the bug is real, the fix is real, but the immediate blast radius appears modest. The Linux kernel community has long noted that CVEs are often assigned to bug fixes where exploitability is not yet proven, because the kernel sits so close to the hardware and so many subsystems can turn “just a bug” into a security-relevant issue depending on context. The kernel documentation says the team is deliberately cautious and that applicability depends on the system and kernel paths involved. (docs.kernel.org)
This case also reflects the stable-kernel workflow. The CVE record ties back to upstream stable commits, which is how Linux often maps a security identifier to a specific code change. The important operational takeaway is not that the world is on fire; it is that maintainers found a bug in a netlink accounting path, fixed it, and then tracked that fix through the kernel’s usual security-assignment machinery.
For WindowsForum readers, the more interesting question is what this says about Linux kernel hardening in 2026. The answer is that a lot of the kernel’s security work now centers on precision: message sizes, lifetimes, accounting, state transitions, and edge cases that rarely make headlines but can destabilize production systems. That trend is visible across modern kernel CVEs, including the one at hand. (docs.kernel.org)
Background
Netfilter is one of the Linux kernel’s most important networking subsystems. It sits in the packet-processing path and provides the hooks that firewalls, packet classifiers, and traffic-control tools depend on. nfnetlink_log is part of that broader machinery, and its job is to package netfilter events into netlink messages that userspace listeners can consume for logging and monitoring. When that packaging is wrong, the impact tends to land first on observability and reliability.Netlink itself is a structured kernel-to-userspace messaging system with strict framing rules, and those rules matter because many higher-level tools depend on accurate message construction. A message that is only a few bytes off can be rejected, truncated, or warned about depending on the code path. In practical terms, that means a low-level accounting mistake can become visible as a dropped event, incomplete logging, or noisy kernel diagnostics. That is not dramatic, but it is operationally important.
The CVE description says this bug is a follow-up to an older fix. That phrase is worth emphasizing because it shows the layered nature of kernel maintenance. One bug gets corrected, but then a related path turns out to have a slightly different accounting assumption, and that second-order issue has to be fixed too. In other words, kernel security work is often iterative rather than one-and-done.
The broader Linux CVE process also explains why a bug like this becomes public. The kernel docs say CVEs are assigned after a fix lands in a stable tree, not before, and that the assignment is tracked by the commit ID of the original fix. They also say the kernel team may assign CVEs to fixes even when the exploitability is unclear, because that is part of how the project keeps its vulnerability catalog coherent. (docs.kernel.org)
That approach has a downstream benefit for enterprises: it creates a machine-readable trail from source fix to public advisory to distro update. Microsoft’s Security Update Guide has increasingly become part of that ecosystem, and Microsoft has documented its broader effort to surface Linux-related security information in the same disclosure model used for Microsoft products. The result is a more centralized intake path for defenders, even when the underlying bug lives far from Windows.
Why header size bugs matter
The key technical phrase here is netlink header size. In kernel message construction, the payload is only part of the space calculation; the framing header also consumes bytes, and that overhead must be counted every time. If a path accounts for only the attribute payload, it can end up creating a message that is structurally too small.That sort of bug often does not lead to an immediate crash. More commonly, it produces a warning, a rejected packet, or a silent failure in message delivery. Those outcomes can still matter a great deal for logging, telemetry, or debugging workflows, especially in environments that rely on nfnetlink output for security visibility. A message that never arrives is a security problem if the whole point of the path is to observe what happened.
Why this is not being treated as a panic-level issue
The description attached to CVE-2026-31416 is unusually restrained. It explicitly says the bug can produce a warning and a dropped message, but “no other ill effects.” That suggests the kernel maintainers viewed the issue as a correctness defect with limited direct impact, not as a memory-safety escape hatch or privilege-escalation primitive.Still, kernel CVEs often begin with modest language. The Linux project’s own documentation warns that applicability is highly system-dependent and that any bug may become security-relevant in a specific deployment. That is why defenders should treat “low impact” as a triage clue, not a dismissal. (docs.kernel.org)
The Vulnerability in Plain English
At the center of CVE-2026-31416 is a bookkeeping error. The kernel’s nfnetlink_log path was apparently calculating NLMSG_DONE completion size based on the attribute length alone, without including the netlink message header overhead. That means the final message size could be underreported, which in turn can trip kernel warnings and cause the message to be dropped.For userspace consumers, the practical effect is likely to be missing log records or noisy diagnostics rather than a visible system failure. That distinction matters because security teams often triage by symptom, and a dropped logging message can look like a harmless telemetry glitch until it undermines an audit trail. If your monitoring depends on complete kernel-side event delivery, “just a warning” is not always just a warning.
The likely user-facing symptom set
From the published description, the visible symptoms are limited. The kernel can emit a WARN splat, and the netlink message may be discarded. There is no indication in the public record that this leads to arbitrary code execution, memory disclosure, or privilege escalation.That makes this a classic example of a bug that is security-adjacent rather than obviously exploitable. A malformed accounting path can still matter because kernel warnings can destabilize workloads, pollute logs, and break assumptions in management tooling. In long-running production systems, those side effects can become expensive even when the kernel itself survives.
Why the follow-up wording matters
The phrase “followup to an old bug fix” is doing a lot of work here. It signals that maintainers already knew about a related netlink sizing issue and that the current fix is part of a chain of incremental corrections. That is common in mature kernel subsystems, where one accounting fix exposes a nearby assumption that also needs to be tightened.This is also why the vulnerability should not be dismissed as duplicate noise. A second-order fix can reveal that the earlier correction was incomplete in one specific message path, and incomplete fixes are exactly the kind of thing stable trees try to catch before they spread widely. (docs.kernel.org)
Netfilter and nfnetlink_log
The netfilter stack is foundational to Linux networking. nfnetlink_log sits in the part of the system that exports packet- and rule-related events to userspace, making it relevant to administrators who rely on kernel logging for visibility into firewall behavior and packet filtering decisions. Even small failures in that path can have outsized effects on troubleshooting and incident response.Because netfilter is so central, kernel maintainers tend to be careful about how they classify defects there. A bug that only affects message sizing might look tame in isolation, but it still affects a subsystem that is used by security software, traffic inspection tools, and diagnostic pipelines. That alone makes the issue worth tracking as a CVE instead of burying it in a changelog footnote. (docs.kernel.org)
What users should understand about the path
Netlink is not just another internal kernel buffer. It is a user-visible protocol boundary, and protocol boundaries are where bookkeeping errors often become operational bugs. A size mismatch can lead to message rejection, which means the bug may surface as lost visibility rather than broken connectivity.That distinction is particularly important in security operations centers. Loss of telemetry is dangerous because it creates blind spots, and blind spots are exactly where attackers try to hide. Even if this CVE is not exploitable in the classic sense, it still deserves attention from teams that treat logging as a first-class control.
Why the issue is hard to overstate or understate
The best way to think about this flaw is as a precision bug rather than a dramatic vulnerability. It is narrow, technically bounded, and apparently limited in observable effect. But narrow kernel bugs still matter because the Linux kernel is a shared platform for countless downstream systems, and small inconsistencies can become support incidents when they hit the wrong workload. (docs.kernel.org)That is why patching discipline matters here even if severity looks low. The kernel documentation explicitly advises taking released kernel changes as a unified whole rather than cherry-picking individual fixes, because many issues are solved by the sum of several related corrections. (docs.kernel.org)
Exploitability and Severity
At the time of the record’s publication, NVD had not yet assigned a CVSS score. That is important because it means defenders do not yet have a standardized severity number to anchor their response, and any urgency assessment must lean on the technical description and local exposure.The public language strongly suggests a low-to-moderate operational issue rather than a high-severity exploit primitive. Still, Linux’s own CVE policy warns that the absence of obvious exploitability at the time of fix does not mean a bug is irrelevant to security. The project assigns CVEs conservatively, precisely because later analysis may reveal broader implications. (docs.kernel.org)
Why severity remains unresolved
The missing CVSS score reflects the reality of how NVD enrichment works. NVD often waits for sufficient public evidence before assigning a vector, especially for kernel issues that may be context dependent. Until that happens, the record stays informational rather than numerically ranked.That does not make the CVE less real. It just means teams must read the description carefully and apply it to their own kernel build, workload, and netfilter usage. In practice, that is often better than blindly following a score that may not reflect the local attack surface. (docs.kernel.org)
Enterprise vs consumer impact
For enterprises, the relevant question is whether the affected kernel path is actually active in production. Firewalls, gateways, routers, and monitoring appliances are far more likely to care about nfnetlink_log than a typical consumer laptop. On those systems, even a dropped kernel log message can interfere with compliance workflows or security telemetry collection.For consumers, the likelihood of direct impact is lower unless they run specialized Linux networking stacks, custom firewalling, or developer-oriented packet inspection tools. That said, many consumer-adjacent devices use Linux under the hood, so the distinction between “consumer” and “embedded infrastructure” is often thinner than it looks. The patch may be tiny, but the deployment surface is broad. (docs.kernel.org)
Numbered triage steps
- Confirm whether your kernel branch includes the stable fix tied to the CVE.
- Check whether your environment uses nfnetlink_log or related netfilter logging paths.
- Review whether kernel warnings or dropped netlink events have already been observed.
- Validate downstream vendor advisories rather than assuming upstream status means you are protected.
- Prioritize systems that use Linux as a security or observability appliance.
Stable Kernel Process and Disclosure
This CVE is a good illustration of how Linux security disclosure works in 2026. The kernel project assigns CVEs after a fix lands in a stable branch, and the CVE is then associated with the commit ID of the original fix. That process keeps the public record tied to a concrete code change instead of an abstract issue label. (docs.kernel.org)That model also explains why the same issue can surface in multiple downstream channels. Microsoft, for example, has positioned the Security Update Guide as a unified place to surface CVEs and related advisories, including non-Microsoft issues that matter to customers. In practice, that means a Linux CVE can become visible to Windows-heavy IT teams because their vulnerability management systems ingest those feeds.
Why downstream visibility matters
The technical fix may live in kernel.org, but remediation often happens through distro kernels, appliance firmware, and vendor maintenance streams. Enterprises rarely patch directly from upstream source; they patch through the versioning model their vendor supports. That creates a lag window in which the CVE is public but the fix has not yet landed everywhere that matters. (docs.kernel.org)That lag is why a low-severity kernel bug can still produce meaningful risk. If the flawed path is part of a compliance or monitoring chain, delayed patching can preserve a blind spot long after the advisory is public. Operational fragility is often the real cost of “minor” bugs. (docs.kernel.org)
What the MSRC angle adds
Microsoft’s role here is not that Windows is affected. Rather, Microsoft’s disclosure infrastructure is one of the places where Linux CVEs now appear for enterprise visibility. The company has documented its push to make the Security Update Guide a more comprehensive source of vulnerability and advisory data, which is helpful for mixed estates that track many platforms in one workflow.That broader visibility is good news, but it also creates a responsibility for administrators to read the technical detail instead of treating every CVE as equally urgent. A precise bug in a specialized kernel module should be prioritized differently from a remotely exploitable flaw in a public service. (docs.kernel.org)
What It Means for Administrators
The practical message for administrators is simple: do not equate “low visible impact” with “safe to ignore.” If your environment uses Linux netfilter logging, you should verify whether your distribution has included the fix and whether any local monitoring depends on that message path.This is especially relevant for security appliances, containers hosts with custom packet filtering, and embedded devices that rely on kernel-generated logs for audit trails. In those environments, a dropped netlink message can become a troubleshooting problem first and a security problem second. The order matters less than the result.
A sensible response plan
The right response is not emergency panic. It is disciplined inventory, version checking, and vendor guidance review. Administrators should confirm the kernel version, identify whether the affected subsystem is enabled or reachable in their workloads, and then apply the vendor’s backport when available. (docs.kernel.org)If your fleet uses multiple kernel streams, this is a good reminder that “patched upstream” does not always mean “patched here.” Stable-tree fixes still need to be carried into distro builds, and that can take time depending on support policy and maintenance cadence.
Enterprise monitoring implications
From an operations perspective, nfnetlink_log bugs should be treated as observability issues with security implications. If a logging path drops messages, you may never see the failure unless you are watching for kernel warnings or comparing expected and actual event volume.That makes this CVE a good case study in why log integrity matters. A security tool can only alert on what it receives, and missing kernel events can create a false sense of normality in environments that depend on netfilter telemetry.
Strengths and Opportunities
The strongest aspect of this disclosure is its clarity. The description is specific enough to tell administrators what changed, why it changed, and what the likely consequence is. That is exactly what defenders need when triaging a kernel fix that is not obviously catastrophic.It also highlights a healthy maintenance culture in the Linux kernel ecosystem. Small follow-up fixes are not a sign of weakness; they are a sign that maintainers are willing to keep tightening code paths until accounting is right. That reduces long-term technical debt and improves confidence in stable backports.
- Precise technical scope makes the issue easier to evaluate.
- Low apparent severity reduces the chance of overreaction.
- Stable-tree linkage gives operators a concrete patch target.
- Netfilter visibility helps security teams map exposure quickly.
- Vendor aggregation through MSRC improves enterprise awareness.
- Kernel discipline reinforces trust in the patch process.
- Observability value reminds teams why logging correctness matters.
Risks and Concerns
The main concern is not remote exploitation; it is underestimation. A bug that only triggers a warning and drops a message can be dismissed too easily, especially when it sits in a subsystem that most users never touch directly. That attitude can delay remediation in precisely the environments where the fix matters most.There is also the risk of false confidence. Because the record currently lacks a CVSS score, teams may be tempted to postpone action until scoring appears. That can be a mistake if the affected kernel path is already central to a production logging pipeline.
- Potential log loss can weaken security monitoring.
- Warning storms can distract from more serious issues.
- Delayed backports may leave older enterprise kernels exposed.
- Specialized hardware often updates more slowly than general-purpose servers.
- Misclassification as “just stability” can slow remediation.
- Version drift can cause admins to assume they are protected when they are not.
- Limited visibility into nfnetlink use can obscure real exposure.
Looking Ahead
The next thing to watch is how quickly the fix propagates into long-term-support kernel streams and vendor distributions. Once that happens, the practical risk should shrink sharply for most systems, but only for systems that actually update and verify the result. That is the classic Linux security pattern: public disclosure first, operational normalization later.It is also worth watching whether additional commentary emerges about the scope of the bug. Some kernel CVEs start with a tightly worded description and later gain a more nuanced operational interpretation as distributions and maintainers weigh in. If that happens here, it will likely be about observability impact rather than a major expansion of exploitability. (docs.kernel.org)
Items to monitor
- Distribution advisories that confirm backported kernel builds.
- Vendor changelogs that mention nfnetlink_log or netfilter logging fixes.
- Internal log-monitoring alerts tied to kernel warnings or dropped netlink events.
- Whether enterprise vulnerability tools classify the issue as informational or required.
- Any follow-up stable commits that refine the same accounting path.
CVE-2026-31416 is therefore best understood as a small bug with real operational meaning. It does not look like the kind of flaw that defines a news cycle, but it does fit the kind of kernel maintenance issue that rewards careful patching and disciplined validation. In 2026, that may be the most important lesson of all: the quiet fixes are often the ones that keep the rest of the stack honest.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: