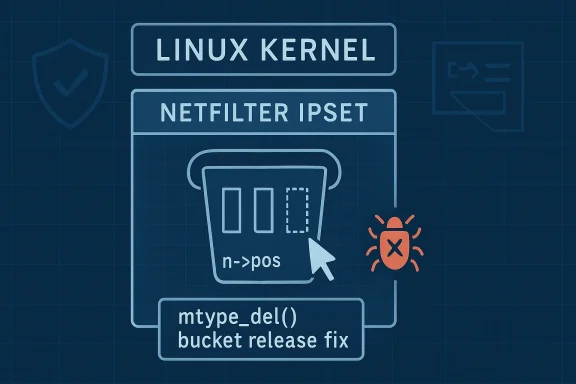
CVE-2026-31418 is a narrowly scoped Linux kernel bug, but it sits in a part of the stack where small accounting mistakes can still create real operational pain. The flaw affects netfilter ipset and, according to the published description, centers on
Linux kernel CVEs often look deceptively simple when they first appear in public records. In this case, the description ties the vulnerability to a specific bookkeeping flaw in the ipset deletion path, and the language suggests a correctness bug rather than a classic memory-safety exploit. That distinction matters because correctness issues in the networking stack can still become availability problems, especially when they occur in packet-handling code that administrators rely on for filtering and policy enforcement.
Netfilter is one of the kernel’s central traffic-control and packet-filtering frameworks. It underpins firewall rules, connection tracking, packet mangling, and related policy logic, which means a defect in that layer can have consequences that range from noisy logs to lost packets or degraded service. ipset sits within that ecosystem as a tool for efficiently matching packet attributes against sets, so even a small inconsistency in how buckets are retired or compacted can ripple outward into performance and reliability concerns.
The wording of the fix is especially revealing. The bug was not that the kernel failed to notice a bucket had become empty in the absolute sense; it was that the deletion logic only dropped a bucket when both
This also fits the broader pattern of Linux kernel vulnerability handling in 2026: a fix lands in stable, the issue gets a CVE, and downstream visibility follows through vendor channels. Microsoft’s Security Update Guide is one place where those kernel issues become visible to enterprise defenders, even though the underlying bug lives upstream in kernel.org. For mixed estates, that matters because a Linux kernel issue can still show up in a Windows-centric vulnerability workflow.
The NVD entry is still marked as awaiting enrichment, with no published CVSS score at the time of the record. That leaves defenders without a neatly packaged severity number and forces them to judge risk from the technical description and their own exposure to the affected subsystem. For kernel issues, that is often the right way to think about it anyway: the operational impact depends heavily on where and how the vulnerable code is used.
That distinction sounds small, but it is central to why kernel maintenance is so unforgiving. A deletion path is supposed to converge toward a clean empty state. If the code instead keeps chasing stale positional metadata, it can preserve dead structure longer than intended, increasing the chance of inconsistent behavior or later edge-case failures. This is not the same as a flashy memory-corruption primitive, but in the kernel, a persistent state inconsistency is still security-relevant when it sits in packet-processing code.
The published record also points to a set of stable-tree references, which indicates the issue was fixed upstream and then propagated through the kernel’s normal backport machinery. That is important because most real-world exposure is not about the abstract fix in source control; it is about whether your distribution, appliance image, or vendor kernel actually contains the patch. In enterprise environments, that lag window is often where the practical risk lives.
From a security operations perspective, this CVE is likely to be triaged as a lower-severity kernel issue than something involving arbitrary code execution or privilege escalation. But low-severity is not the same as low-value. In packet-processing subsystems, even a “just” correctness bug can matter if it affects firewall logic, service continuity, or observability. That is why kernel maintainers continue to assign CVEs to issues that are not obviously weaponizable on day one.
There is also a broader maintenance lesson here. The fix does not appear to redesign ipset or alter the semantics of set operations; it simply recognizes that a bucket with no live entries below
Another reason is that “empty” is often overloaded in kernel data structures. A bucket can be physically allocated, logically retired, partially compacted, or effectively dead depending on which counter or cursor you inspect. If the code uses the wrong notion of emptiness, it can make the wrong cleanup choice while still appearing internally consistent. That sort of ambiguity is classic kernel territory.
That means the deletion logic was too conservative in one case and too literal in another. It was asking whether the bucket had reached a very specific structural state, rather than asking whether any meaningful live entries remained. In a cleanup routine, that distinction is crucial. The right question is not “does the cursor look tidy?” but “is there anything left worth keeping?”
The consequence of this design flaw is not described in the record as arbitrary memory access or corruption, which is important. The visible issue is framed as an accounting bug that can leave logically empty buckets in place longer than they should survive. That makes the CVE more about incorrect state transitions than about classic exploit primitives, but it still matters because the kernel is responsible for enforcing consistency in privileged packet-filtering paths.
Why
The patch’s response is conceptually clean: treat a bucket as empty when all positions below
This is the kind of repair operators generally prefer because it does not change the public API or force users to rethink their rulesets. It changes the internal retirement logic and nothing more. That matters for stable backports, because the least risky security fix is the one that leaves the externally visible behavior intact while correcting the internal invariant.
That is a pattern worth noticing across kernel development. Developers often discover that a data structure has two truths: what the counters say and what the data path actually means. Bugs emerge when cleanup code follows the wrong truth. Here, the cure is to align cleanup with actual liveness rather than with an incomplete structural test.
Enterprise exposure is likely higher than consumer exposure, simply because enterprises are more likely to run sophisticated firewall, routing, or security-monitoring stacks that rely on netfilter and ipset at scale. Consumer systems may never exercise the affected path unless they are used as routers, gateways, lab machines, or appliances with custom packet-filtering setups. That said, the boundary between consumer Linux and embedded infrastructure is thinner than it looks, so the risk should not be dismissed purely on device class.
For administrators, the practical next step is boring but necessary: confirm whether the vendor kernel contains the stable fix. Do not assume that a distribution is protected just because upstream has already published the fix. In Linux ecosystems, the gap between upstream and downstream is often the gap where exposure lives.
There is also an opportunity here for vendors to improve how they communicate kernel updates. Smaller bugs like this often get delayed because they do not sound dramatic, but they can still be important in systems that depend on netfilter for segmentation and control. Good patch discipline turns those small fixes into fewer downstream support incidents.
Another concern is patch drift. A fix may exist upstream while older vendor branches continue to ship vulnerable builds for some time. That lag is especially problematic in mixed-vendor environments where administrators rely on consolidated dashboards rather than direct kernel inspection.
It is also worth watching whether this CVE prompts broader auditing of ipset and related netfilter cleanup paths. Bugs like this often reveal adjacent assumptions in nearby code, especially where cursor state, deletion logic, and bucket compaction interact. In kernel security, one logic flaw often becomes a roadmap for reviewing the next one.
CVE-2026-31418 is therefore best understood as a small bug with meaningful operational consequences. The fix is narrow, the risk appears bounded, and the public description does not suggest a widespread exploit primitive. Even so, any issue in netfilter deserves serious attention from administrators who depend on Linux for filtering, segmentation, or gateway duties, because the line between a cleanup bug and a service-impacting event is often thinner than it first appears.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
mtype_del() failing to treat a bucket as empty when its live entries have already been removed but n->pos still points past deleted slots. The fix is straightforward: release a logically empty bucket instead of trying to shrink it further. That sounds modest, but in kernel code, modest often means surgical, not trivial.
 Background
Background
Linux kernel CVEs often look deceptively simple when they first appear in public records. In this case, the description ties the vulnerability to a specific bookkeeping flaw in the ipset deletion path, and the language suggests a correctness bug rather than a classic memory-safety exploit. That distinction matters because correctness issues in the networking stack can still become availability problems, especially when they occur in packet-handling code that administrators rely on for filtering and policy enforcement.Netfilter is one of the kernel’s central traffic-control and packet-filtering frameworks. It underpins firewall rules, connection tracking, packet mangling, and related policy logic, which means a defect in that layer can have consequences that range from noisy logs to lost packets or degraded service. ipset sits within that ecosystem as a tool for efficiently matching packet attributes against sets, so even a small inconsistency in how buckets are retired or compacted can ripple outward into performance and reliability concerns.
The wording of the fix is especially revealing. The bug was not that the kernel failed to notice a bucket had become empty in the absolute sense; it was that the deletion logic only dropped a bucket when both
n->pos and k were zero, which missed cases where the remaining live entries had already been cleared but the cursor still pointed beyond deleted slots. In other words, the implementation had a semantic gap between “structurally non-empty” and “logically empty.” That is exactly the kind of subtle mismatch that survives long enough to earn a CVE.This also fits the broader pattern of Linux kernel vulnerability handling in 2026: a fix lands in stable, the issue gets a CVE, and downstream visibility follows through vendor channels. Microsoft’s Security Update Guide is one place where those kernel issues become visible to enterprise defenders, even though the underlying bug lives upstream in kernel.org. For mixed estates, that matters because a Linux kernel issue can still show up in a Windows-centric vulnerability workflow.
The NVD entry is still marked as awaiting enrichment, with no published CVSS score at the time of the record. That leaves defenders without a neatly packaged severity number and forces them to judge risk from the technical description and their own exposure to the affected subsystem. For kernel issues, that is often the right way to think about it anyway: the operational impact depends heavily on where and how the vulnerable code is used.
Overview
At a high level, CVE-2026-31418 is about state cleanup in ipset. The vulnerable code attempts to delete or shrink buckets as entries disappear, but it appears to have relied on a narrow condition that failed to recognize some buckets as fully dead. Once the bucket had no meaningful live entries belown->pos, the better action was to release it outright rather than keep trimming around stale cursor state.That distinction sounds small, but it is central to why kernel maintenance is so unforgiving. A deletion path is supposed to converge toward a clean empty state. If the code instead keeps chasing stale positional metadata, it can preserve dead structure longer than intended, increasing the chance of inconsistent behavior or later edge-case failures. This is not the same as a flashy memory-corruption primitive, but in the kernel, a persistent state inconsistency is still security-relevant when it sits in packet-processing code.
The published record also points to a set of stable-tree references, which indicates the issue was fixed upstream and then propagated through the kernel’s normal backport machinery. That is important because most real-world exposure is not about the abstract fix in source control; it is about whether your distribution, appliance image, or vendor kernel actually contains the patch. In enterprise environments, that lag window is often where the practical risk lives.
From a security operations perspective, this CVE is likely to be triaged as a lower-severity kernel issue than something involving arbitrary code execution or privilege escalation. But low-severity is not the same as low-value. In packet-processing subsystems, even a “just” correctness bug can matter if it affects firewall logic, service continuity, or observability. That is why kernel maintainers continue to assign CVEs to issues that are not obviously weaponizable on day one.
There is also a broader maintenance lesson here. The fix does not appear to redesign ipset or alter the semantics of set operations; it simply recognizes that a bucket with no live entries below
n->pos should be treated as empty and dropped. That kind of narrow correction is exactly what downstream maintainers want for stable branches, because it is easier to backport and less likely to destabilize unrelated code.Why this kind of bug is easy to miss
This vulnerability sits in bookkeeping logic, not in a hot-path feature that developers stare at every day. Bugs in these areas often survive review because the code looks plausible and the failure mode only appears after a particular sequence of inserts and deletes. The state machine may be correct most of the time, which is exactly why it can be dangerous when it is wrong.Another reason is that “empty” is often overloaded in kernel data structures. A bucket can be physically allocated, logically retired, partially compacted, or effectively dead depending on which counter or cursor you inspect. If the code uses the wrong notion of emptiness, it can make the wrong cleanup choice while still appearing internally consistent. That sort of ambiguity is classic kernel territory.
What the stable references imply
The multiple stable references attached to the record are a strong clue that the fix was treated as an important maintenance correction, not a speculative cleanup. Stable branches usually prefer changes that are self-contained, easy to reason about, and tightly tied to a specific bug. That profile fits this CVE well: small patch, clear cause, clear correction.Technical Root Cause
The core issue is the mismatch between cursor position and actual liveness.mtype_del() counts empty slots below n->pos in k, but the bug was that the code only released a bucket when both n->pos and k were zero. If live entries had already been removed, the bucket could be functionally empty even while n->pos still pointed past stale slots.That means the deletion logic was too conservative in one case and too literal in another. It was asking whether the bucket had reached a very specific structural state, rather than asking whether any meaningful live entries remained. In a cleanup routine, that distinction is crucial. The right question is not “does the cursor look tidy?” but “is there anything left worth keeping?”
The consequence of this design flaw is not described in the record as arbitrary memory access or corruption, which is important. The visible issue is framed as an accounting bug that can leave logically empty buckets in place longer than they should survive. That makes the CVE more about incorrect state transitions than about classic exploit primitives, but it still matters because the kernel is responsible for enforcing consistency in privileged packet-filtering paths.
Why n->pos matters
n->pos appears to act like a cursor into bucket state, and cursors are notoriously tricky in deletion-heavy code. Once entries are removed, the cursor can lag behind the semantic truth of the structure. If cleanup logic keys too tightly to cursor value, it can miss the point where the object should be reclaimed entirely. That is the failure mode here.The patch’s response is conceptually clean: treat a bucket as empty when all positions below
n->pos are unused, and drop it directly. That avoids a slower or more fragile attempt to keep shrinking a structure that no longer has any useful contents. In kernel terms, it is a recognition that reclamation should follow liveness, not stale positional state.Why this is security-relevant
A bug does not need to be remotely exploitable to deserve a CVE. In the kernel, especially in networking code, a correctness flaw can still become a denial-of-service issue or create inconsistent policy behavior. If the affected path is in a firewalling or packet-classification stack, the practical impact can be outage-like even when the technical root cause is “only” improper cleanup.How the Fix Changes the Behavior
The published description makes the fix sound intentionally narrow. Instead of continuing to shrink buckets while keeping dead structure around, the kernel now releases a bucket directly once it is logically empty. That is a cleaner lifecycle decision and removes the awkward case where the code keeps trying to compress an object that should already be gone.This is the kind of repair operators generally prefer because it does not change the public API or force users to rethink their rulesets. It changes the internal retirement logic and nothing more. That matters for stable backports, because the least risky security fix is the one that leaves the externally visible behavior intact while correcting the internal invariant.
What “logically empty” means here
The phrase “logically empty” is doing a lot of work. A structure may still exist in memory, but if all live positions below the cursor have been removed, then from the subsystem’s perspective there is nothing left that deserves to keep the bucket alive. The fix embraces that semantic meaning and translates it into a reclamation decision.That is a pattern worth noticing across kernel development. Developers often discover that a data structure has two truths: what the counters say and what the data path actually means. Bugs emerge when cleanup code follows the wrong truth. Here, the cure is to align cleanup with actual liveness rather than with an incomplete structural test.
Why this is likely backportable
The patch is well suited to stable kernels because it is targeted and understandable. There is no sign in the record of a broad semantic rewrite or a dependency chain that would make backporting difficult. For distro maintainers, that is exactly the kind of fix you want to land quickly without destabilizing adjacent netfilter behavior.- The fix is small and local.
- It preserves the existing ipset model.
- It clarifies when a bucket should be freed.
- It reduces the chance of stale state surviving deletion.
- It should be easier to backport than a behavioral rewrite.
Exposure and Practical Risk
The most honest reading of the public description is that this is primarily a correctness and availability issue, not a dramatic exploit primitive. That does not make it ignorable. In privileged networking code, even a narrow accounting flaw can become user-visible if it affects set maintenance under load or in unusual firewall configurations.Enterprise exposure is likely higher than consumer exposure, simply because enterprises are more likely to run sophisticated firewall, routing, or security-monitoring stacks that rely on netfilter and ipset at scale. Consumer systems may never exercise the affected path unless they are used as routers, gateways, lab machines, or appliances with custom packet-filtering setups. That said, the boundary between consumer Linux and embedded infrastructure is thinner than it looks, so the risk should not be dismissed purely on device class.
Enterprise impact
For enterprise operators, the main issue is not whether the bug is glamorous; it is whether the affected kernel path exists in production. If your estate uses ipset heavily for firewall policy, rate limiting, or network segmentation, the bug is worth verifying against vendor backports. A mistake in set retirement logic can complicate incident response, especially if it leads to degraded rule-management behavior or unexpected churn in firewall state.Consumer impact
Consumer impact is likely narrower, but not zero. Home users running stock desktop Linux are less likely to hit this path, while power users, homelab operators, and small-office gateway owners are more likely to. The distinction matters because these are the people who often run custom firewall rules precisely because they care about control and visibility.Why availability still counts as security
A lot of teams instinctively rank “memory corruption” above “cleanup bug.” That is a mistake if the cleanup bug can disrupt a security control plane or trigger instability in a packet path. Availability is part of security, and in a firewall subsystem, it is often the first thing operators notice when something goes wrong.- The bug is unlikely to be treated as a high-severity remote exploit.
- It still deserves patch attention in systems that use ipset heavily.
- Network appliances are more exposed than general-purpose desktops.
- Vendor backports are more important than the upstream commit alone.
- Operational impact may show up before formal CVSS scoring does.
Patch Management Implications
The presence of a CVE here is a reminder that kernel security is not just about dramatic memory-safety failures. Modern Linux vulnerability management increasingly tracks logic errors, boundary mistakes, and state-accounting flaws because they can still affect real systems. That is especially true in netfilter, where policy and packet handling intersect with operational visibility.For administrators, the practical next step is boring but necessary: confirm whether the vendor kernel contains the stable fix. Do not assume that a distribution is protected just because upstream has already published the fix. In Linux ecosystems, the gap between upstream and downstream is often the gap where exposure lives.
What administrators should check
A sensible triage process for this CVE is straightforward. First, identify whether your kernel branch has the backport. Second, determine whether your firewall rules or security tooling actively use ipset in ways that might exercise the affected path. Third, look for signs of anomalous kernel warnings or rule-management oddities in systems with heavy netfilter usage.- Confirm the vendor kernel version.
- Verify whether the stable fix is included.
- Check ipset usage in production firewall paths.
- Review kernel logs for unusual warnings.
- Prioritize appliances and gateways first.
Why the MSRC visibility matters
Microsoft’s role here is not that Windows is affected. Rather, Microsoft’s vulnerability guide has become one of the places where Linux CVEs show up for enterprise visibility, which matters in mixed-platform shops. That makes the CVE easier to notice, but it also increases the responsibility on defenders to read the technical detail instead of relying on a severity label alone.- Mixed estates may see the issue through Microsoft’s feed.
- Downstream vendors may lag the upstream fix.
- Automated tools may under-prioritize the bug without context.
- Appliances often patch slower than servers.
- Kernel updates should be mapped to actual subsystem use, not just version numbers.
Strengths and Opportunities
The strongest aspect of this disclosure is its clarity. The description explains the bug in terms of the code path, the mistaken condition, and the corrected behavior, which gives operators a usable mental model for triage. That kind of precision is valuable because it reduces the odds of both overreaction and underreaction.There is also an opportunity here for vendors to improve how they communicate kernel updates. Smaller bugs like this often get delayed because they do not sound dramatic, but they can still be important in systems that depend on netfilter for segmentation and control. Good patch discipline turns those small fixes into fewer downstream support incidents.
- Clear technical description helps defenders assess exposure.
- The fix is narrow enough to be backportable.
- Stable-tree linkage improves patch traceability.
- The issue reinforces the value of lifecycle correctness.
- Vendor aggregation improves enterprise awareness.
- The bug highlights why kernel cleanup paths deserve review.
- Small fixes can have outsized operational value.
A maintenance lesson worth keeping
The deeper lesson is that cleanup logic deserves the same rigor as data-path logic. It is easy to think of deletion code as housekeeping, but in a kernel subsystem it is part of the security boundary. When cleanup is wrong, the system can preserve the wrong state for just long enough to matter.Risks and Concerns
The biggest concern is underestimation. Because the bug does not read like a headline-grabbing exploit, some teams may decide it can wait. That is risky in environments where ipset is used as part of a production firewall or security appliance, because even small kernel inconsistencies can create outsized operational headaches.Another concern is patch drift. A fix may exist upstream while older vendor branches continue to ship vulnerable builds for some time. That lag is especially problematic in mixed-vendor environments where administrators rely on consolidated dashboards rather than direct kernel inspection.
Operational pitfalls
The danger is not only that the bug is overlooked, but also that it is misclassified. If teams treat it as a harmless cleanup issue, they may postpone it in favor of higher-profile items even when the affected path is central to their network policy stack. That is exactly when a supposedly low-risk bug becomes a real support incident.- Patch lag can extend the real exposure window.
- Appliances often update more slowly than general servers.
- Teams may ignore the issue without a CVSS score.
- Netfilter paths can be easy to overlook in audits.
- Hidden reliance on ipset is common in mature firewall setups.
- State-accounting bugs are easy to misread as harmless cleanup.
Why no CVSS score is not reassuring
The lack of an assigned CVSS score should not be read as reassurance. It usually means the enrichment process has not finished, not that the bug is intrinsically harmless. In practice, operators should use the description and their own exposure model, then let formal scoring catch up later.Looking Ahead
The next thing to watch is how quickly the fix reaches downstream kernels and vendor-maintained appliance builds. For many organizations, that matters more than the upstream commit itself, because the production kernel is usually the vendor’s backport, not the original mainline version. Once the fix is broadly propagated, the practical risk should fall sharply for systems that actually update.It is also worth watching whether this CVE prompts broader auditing of ipset and related netfilter cleanup paths. Bugs like this often reveal adjacent assumptions in nearby code, especially where cursor state, deletion logic, and bucket compaction interact. In kernel security, one logic flaw often becomes a roadmap for reviewing the next one.
Items to monitor
- Vendor advisories confirming the backport.
- Distribution kernel changelogs mentioning ipset fixes.
- Appliance firmware updates that include netfilter maintenance.
- Internal testing for ipset-heavy firewall workflows.
- Any follow-up stable commits in the same cleanup path.
What this says about Linux security in 2026
This CVE is a reminder that kernel hardening increasingly lives in the details. It is not just about stopping obvious memory corruption; it is about keeping state transitions honest, cleaning up structures at the right time, and making sure bookkeeping reflects reality. That kind of work is less visible than a dramatic exploit, but it is one of the reasons Linux remains resilient in production.CVE-2026-31418 is therefore best understood as a small bug with meaningful operational consequences. The fix is narrow, the risk appears bounded, and the public description does not suggest a widespread exploit primitive. Even so, any issue in netfilter deserves serious attention from administrators who depend on Linux for filtering, segmentation, or gateway duties, because the line between a cleanup bug and a service-impacting event is often thinner than it first appears.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center