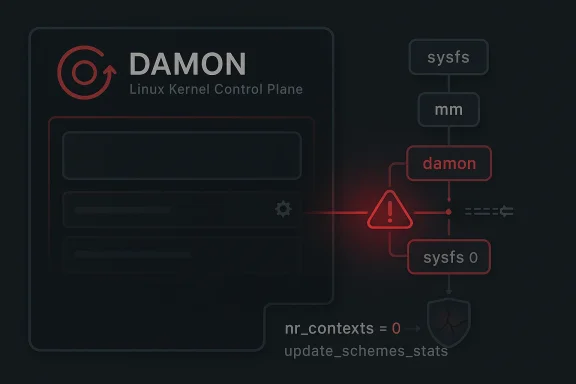
A newly published Linux kernel CVE is shining a light on a deceptively small but consequential bug in DAMON’s sysfs command handling: CVE-2026-31458 can trigger a NULL pointer dereference when
DAMON, the Data Access MONitor, is one of those Linux subsystems that rarely attracts attention until something goes wrong. It is designed to observe memory access patterns and support memory-tiering and optimization workflows, which makes it especially relevant on modern servers where memory efficiency matters as much as raw throughput. Because DAMON is exposed through sysfs, administrators can configure and adjust it at runtime, and that convenience also makes input validation and object lifetime rules absolutely critical.
The CVE description says the problem lies in
What makes this bug interesting is not just the crash itself, but the shape of the control path. The report identifies a sequence in which a privileged user starts DAMON, navigates to the relevant sysfs directory, sets
Historically, Linux kernel security work has repeatedly shown that sysfs interfaces are only as safe as the assumptions behind them. A sysfs knob is not inherently dangerous, but it becomes dangerous when it can invalidate an object graph the code later still treats as intact. That is the pattern here: the command handler appears to have been written with the expectation that the contexts array remains populated, while another management path can make that assumption false. The fix therefore needs to happen at the point where commands are handled, not only at the point where the crash eventually occurs.
The vulnerability is particularly notable because the published description is explicit about the workaround logic: “Guard all commands (except OFF) at the entry point of
The record also makes clear that the issue was recently published to the CVE list and absorbed into NVD’s dataset, while still lacking finalized CVSS scoring at the time shown in the advisory text . That absence of a score should not be mistaken for a lack of urgency. Kernel bugs ” in the abstract because they describe one missing check, but the operational consequences can be severe when the fault sits on a privileged management path.
Microsoft’s Security Update Guide entry is also a reminder that Linux kernel CVEs now circulate quickly across the broader vulnerability ecosystem, including vendor advisory portals that track the same upstream fix references. The CVE record includes stable-kernel commit links, which implies the issue has already moved through the normal upstream-to-stable remediation process . That matters because administrators generally need to know not just that a problem exists, but whether flowing into supported branches.
The list of vulnerable commdescription specifically names
Why
A zero context count is not merely an empty configuration. In this code path, it is effectively an invalid execution environment for several commands. If the handler still reaches for
The most practical lesson is that state transitions matter as much as state values. A system may be safe at boot, safe after configuration, and unsafe after a later management action changes the topology. That is exactly the kind of edge case that slips past basic unit tests and survives until a real administrator, orchestration tool, or stress harness hits the bad combination.
This is a common kernel-hardening pattern: validate once, early, and close to the trust boundary. If the command is invalid in the current state, the kernel should refuse it rather than trying to recover deeper in the stack. Early rejection is cleaner than late rescue.
This is especially true for a subsystem like DAMON, whose job is tied to memory observation and resource tuning. Those are not peripheral features. They are part of the kernel’s adaptive machinery, and misbehavior there can affect performance-sensitive environments in subtle ways. If the host is a server, a cloud node, or a VM platform, a crash in this layer can have effects that go far beyond the immediate sysfs write.
The fact that the CVE is explicitly framed as a NULL dereference also matters from a defensive perspective. There is no indication in the description of memory corruption, code execution, or data disclosure. That makes this primarily an availability issue, but availability failures in privileged code still deserve prompt treatment because they can be weaponized into denial-of-service conditions. On shared infrastructure, a reliable crash path is often enough to become a real security concern.
CVE-2026-31458 sits squarely in that family. The code is not failing because of complex arithmetic or a deep race condition; it is failing because it trusted a structural assumption that another management operation could invalidate. That kind of bug is often easier to fix than to discover, which is why early disclosure and stable backports are so valuable.
In a controlled workstation, DAMON is not usually the center of daily life. In a production fleet, however, anything exposed under
This is why kernel bugs that require elevated permissions still get tracked carefully. The issue is not whether an untrusted browser tab can trigger it directly. The issue is whether the bug can crash the machine once a trusted subsystem, script, or operator applies a valid but unsafe configuration sequence. In practice, that is often enough to matter.
Enterprise environments are more likely to care about this CVE because they are more likely to automate sysfs configuration and more likely to run kernel builds with advanced tuning features enabled. A crash in a memory-management path can also be more disruptive on systems that host multiple workloads, where one system-level outage affects many dependent services. That is why availability bugs in kernel management paths are usually treated as operationally urgent even when exploitation requires privilege.
That is what makes this CVE important beyond its narrow code path. It is a reminder that the kernel’s internal control surfaces need the same level of validation rigor as externally exposed interfaces. A bad management action should fail safely, not destabilize the subsystem.
A centralized guard also improves code readability. If every command after a certain point assumes there is exactly one valid context, then the handler should make that assumption true before proceeding. If it cannot, then the command should be rejected. That is a much cleaner contract than having multiple helpers each defend themselves against an empty
The fix also appears designed for stable backporting. Narrow entry-point checks usually backport cleanly because they change behavior only in the invalid case. That lowers regression risk and makes it easier for downstream vendors to apply the patch to long-term support branches without disturbing unrelated DAMON behavior.
That matters because kernel hardening has to balance safety with stability. A patch that overcorrects can create new compatibility issues. A patch that simply refuses to execute commands when
A good fix should preserve that nuance. The aim is not to block legitimate administration, but to distinguish between commands that need a live context and commands that do not.
That lesson is that object lifetime must be treated as part of the public contract, even inside the kernel. If a sysfs write can remove the last context, then any command that depends on a context must verify its presence before proceeding. The code should not assume state just because the caller is privileged. Privilege does not replace validation.
The wider ecosystem also benefits from this kind of disclosure. Once the CVE is public, downstream vendors can map their own backports, administrators can verify whether their kernel branch includes the fix, and security teams can prioritize review of any automation that touches DAMON settings. That is how a small upstream patch turns into a real-world reduction in exposure.
Here, the bug sits in a privileged kernel management path. It can be triggered by valid sysfs operations. And it can crash the kernel. Those three facts are enough to justify taking it seriously.
That is exactly the situation here, and it argues for prompt patching rather than waiting for formal scoring to settle.
It will also be worth watching whether follow-ok appears in related command paths. Bugs like this often reveal neighboring assumptions once maintainers start examining the handler structure more closely. If one command trusted
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
nr_contexts is reduced to zero while DAMON is running, yet sysfs command paths still assume contexts_arr[0] exists. The issue is already documented in the kernel.org-derived CVE text and in Microsoft’s update guide, which ties the flaw to several state commands that can trip the fault after a privileged user empties the contexts directory quires elevated access, its impact is still meaningful because a kernel crash in a management path can take down a host, disrupt automation, and expose weak assumptions in the kernel’s control plane.
 Background
Background
DAMON, the Data Access MONitor, is one of those Linux subsystems that rarely attracts attention until something goes wrong. It is designed to observe memory access patterns and support memory-tiering and optimization workflows, which makes it especially relevant on modern servers where memory efficiency matters as much as raw throughput. Because DAMON is exposed through sysfs, administrators can configure and adjust it at runtime, and that convenience also makes input validation and object lifetime rules absolutely critical.The CVE description says the problem lies in
mm/damon/sysfs, where multiple sysfs command paths dereference contexts_arr[0] without first confirming that kdamond->contexts->nr == 1. In practical terms, the code assumes there is at least one context available, but users can reduce nr_contexts to zero while DAMON is still active, leaving later state commands with nothing valid to dereference . The result is a clailure: a pointer that should have been checked is used anyway.What makes this bug interesting is not just the crash itself, but the shape of the control path. The report identifies a sequence in which a privileged user starts DAMON, navigates to the relevant sysfs directory, sets
contexts/nr_contexts to zero, and then writes commands such as update_schemes_stats or update_tuned_intervals to state, triggering the fault . That means the weakness is reachable thrt activity, not some exotic attack primitive. In other words, the bug lives where policy meets runtime state.Historically, Linux kernel security work has repeatedly shown that sysfs interfaces are only as safe as the assumptions behind them. A sysfs knob is not inherently dangerous, but it becomes dangerous when it can invalidate an object graph the code later still treats as intact. That is the pattern here: the command handler appears to have been written with the expectation that the contexts array remains populated, while another management path can make that assumption false. The fix therefore needs to happen at the point where commands are handled, not only at the point where the crash eventually occurs.
Overview
At a high level, CVE-2026-31458 is a state-consistency bug. The sysfs control plane allows a privileged actor to alter the number of DAMON contexts, but some commands still behave as if the first context is always present. This mismatch creates a null dereference window, and because the vulnerable code runs in kernel space, the failure can escalate from a simple exception to a full system panic depending on the kernel’s crash behavior and deployment profile.The vulnerability is particularly notable because the published description is explicit about the workaround logic: “Guard all commands (except OFF) at the entry point of
damon_sysfs_handle_cmd().” That phrasing is important. It suggests the correct repair is not to scatter more checks through the body of the code, but to reject unsafe commands before the handler reaches any code path that depends on contexts_arr[0] being valid . That is a very Linux-kernel kind of fix: precise, narrow, and existing valid behavior.The record also makes clear that the issue was recently published to the CVE list and absorbed into NVD’s dataset, while still lacking finalized CVSS scoring at the time shown in the advisory text . That absence of a score should not be mistaken for a lack of urgency. Kernel bugs ” in the abstract because they describe one missing check, but the operational consequences can be severe when the fault sits on a privileged management path.
Microsoft’s Security Update Guide entry is also a reminder that Linux kernel CVEs now circulate quickly across the broader vulnerability ecosystem, including vendor advisory portals that track the same upstream fix references. The CVE record includes stable-kernel commit links, which implies the issue has already moved through the normal upstream-to-stable remediation process . That matters because administrators generally need to know not just that a problem exists, but whether flowing into supported branches.
How the Crash Happens
The reproduction sequence is straightforward, which is often the warning sign that a kernel bug is more than theoretical. According to the description, the user starts DAMON, changes into/sys/kernel/mm/damon/admin/kdamonds/0, empties the contexts directory by writing 0 to contexts/nr_contexts, and then issues one of several state commands that are supposed to update monitoring or tuning metrics . Instead of handling the empty state cleanly, the kernel dereferences a missing context pointer.The list of vulnerable commdescription specifically names
update_schemes_stats, update_schemes_tried_regions, update_schemes_tried_bytes, update_schemes_effective_quotas, and update_tuned_intervals as commands that can trigger the null dereference once the contexts array is empty . That indicates a shared flaw in the command dispatcher rather than a single buggy leaf function. It also suggests the issue is architectural: theis accepting commands whose implementation requires a context, even when the context count is zero.Why nr_contexts == 0 is so dangerous
A zero context count is not merely an empty configuration. In this code path, it is effectively an invalid execution environment for several commands. If the handler still reaches for contexts_arr[0], it is dereferencing an element that does not exist. That kind of bug is often invisible during normal testing because most validation suites exercise “happy path” configurations with at least one context already present.The most practical lesson is that state transitions matter as much as state values. A system may be safe at boot, safe after configuration, and unsafe after a later management action changes the topology. That is exactly the kind of edge case that slips past basic unit tests and survives until a real administrator, orchestration tool, or stress harness hits the bad combination.
Why the fix belongs at the command boundary
The published remedy is to guard commands atdamon_sysfs_handle_cmd() itself, except for OFF commands that presumably do not depend on context internals in the same way . That is a sound design choice because it keeps unsafe requests from flowing further into the subsystem. It also reduces the chance that future commands added to the stally inherit the same bug.This is a common kernel-hardening pattern: validate once, early, and close to the trust boundary. If the command is invalid in the current state, the kernel should refuse it rather than trying to recover deeper in the stack. Early rejection is cleaner than late rescue.
Why This Matters for Kernel Reliability
Null pointer dereferences are often described as “just crashes,” but in kernel space that shorthand undersells the problem. A kernel crash can interrupt services, trigger reboots, corrupt in-flight work, or leave management tooling in a confused state. Even when the attacker needs elevated privileges, the operational consequence can still be serious because the bad state is reachable through ordinary system administration interfaces.This is especially true for a subsystem like DAMON, whose job is tied to memory observation and resource tuning. Those are not peripheral features. They are part of the kernel’s adaptive machinery, and misbehavior there can affect performance-sensitive environments in subtle ways. If the host is a server, a cloud node, or a VM platform, a crash in this layer can have effects that go far beyond the immediate sysfs write.
The fact that the CVE is explicitly framed as a NULL dereference also matters from a defensive perspective. There is no indication in the description of memory corruption, code execution, or data disclosure. That makes this primarily an availability issue, but availability failures in privileged code still deserve prompt treatment because they can be weaponized into denial-of-service conditions. On shared infrastructure, a reliable crash path is often enough to become a real security concern.
A familiar pattern in Linux bug history
The Linux kernel has a long record of vulnerabilities caused by lifetime assumptions: a pointer is expected to exist, a list is expected to contain one entry, a structure is expected to remain initialized, or a configuration is expected not to change while a command runs. When any of those assumptions break, the result can be a null dereference, use-after-free, or out-of-bounds access.CVE-2026-31458 sits squarely in that family. The code is not failing because of complex arithmetic or a deep race condition; it is failing because it trusted a structural assumption that another management operation could invalidate. That kind of bug is often easier to fix than to discover, which is why early disclosure and stable backports are so valuable.
- The bug is state-dependent, not purely input-dependent.
- The vulnerable path is reachable through legitimate sysfs operations.
- The failure is a kernel-space NULL dereference.
- The remedy is likely a boundary check rather than a redesign.
- The issue is more about invariant enforcement than about raw memory safety.
Attack Surface and Privilege Model
One reason this CVE should not be dismissed is that “privileged only” does not mean harmless. Many real-world Linux environments delegate a surprising amount of power to automation, configuration managers, orchestration agents, and operational scripts. If one of those paths can touch DAMON sysfs, the bug becomes reachable by processes that are privileged in practice, even if they are not human administrators.In a controlled workstation, DAMON is not usually the center of daily life. In a production fleet, however, anything exposed under
/sys/kernel/mm/ may be touched by performance tuning frameworks or system-management agents. That makes the effective attack surface broader than it first appears, especially in environments where different teams share the same machine and privileges are distributed through tooling rather than direct login access.This is why kernel bugs that require elevated permissions still get tracked carefully. The issue is not whether an untrusted browser tab can trigger it directly. The issue is whether the bug can crash the machine once a trusted subsystem, script, or operator applies a valid but unsafe configuration sequence. In practice, that is often enough to matter.
Enterprise versus consumer exposure
For consumers, the practical likelihood of encountering DAMON sysfs directly is fairly low. Most desktop users never touch these controls, and most consumer-facing Linux distributions do not expose them in ordinary workflows. The exposure story changes on servers, test fleets, and custom builds where memory-management tuning is part of routine operations.Enterprise environments are more likely to care about this CVE because they are more likely to automate sysfs configuration and more likely to run kernel builds with advanced tuning features enabled. A crash in a memory-management path can also be more disruptive on systems that host multiple workloads, where one system-level outage affects many dependent services. That is why availability bugs in kernel management paths are usually treated as operationally urgent even when exploitation requires privilege.
The importance of management-plane bugs
Management-plane flaws often receive less attention than packet-path or file-parsing bugs, but they can be just as disruptive. A sysfs interface is effectively a control surface for the kernel. If the control plane does not validate its own assumptions, then every script, admin tool, and automation pipeline that uses it inherits the risk.That is what makes this CVE important beyond its narrow code path. It is a reminder that the kernel’s internal control surfaces need the same level of validation rigor as externally exposed interfaces. A bad management action should fail safely, not destabilize the subsystem.
- Automation can amplify a single bad change across many hosts.
- Privileged access is often distributed through tools, not humans.
- Management-plane bugs can cause wide outage effects.
- Sysfs interfaces deserve strict state validation.
- Local crashes are still security issues when they hit shared infrastructure.
What the Fix Tells Us
The description’s explicit instruction to guard all commands exceptOFF at the entry point of damon_sysfs_handle_cmd() reveals a lot about how the maintainers think about the problem. It suggests the most robust fix is to centralize the state check, not to rely on every downstream helper to remember the invariant. That is generally the right approach in kernel code because it reduces the chance of future regressions.A centralized guard also improves code readability. If every command after a certain point assumes there is exactly one valid context, then the handler should make that assumption true before proceeding. If it cannot, then the command should be rejected. That is a much cleaner contract than having multiple helpers each defend themselves against an empty
contexts_arr.The fix also appears designed for stable backporting. Narrow entry-point checks usually backport cleanly because they change behavior only in the invalid case. That lowers regression risk and makes it easier for downstream vendors to apply the patch to long-term support branches without disturbing unrelated DAMON behavior.
Why this is likely a low-regression patch
The strongest kernel fixes are often the smallest ones. Here, the bug is not a subtle algorithmic error that requires redesigning DAMON’s runtime model. It is a missed precondition check. As a result, the fix can almost certainly be implemented without altering the semantics of valid command execution.That matters because kernel hardening has to balance safety with stability. A patch that overcorrects can create new compatibility issues. A patch that simply refuses to execute commands when
contexts->nr is not what the command expects is both understandable and maintainable. That is the sweet spot for a reliability patch.Commands that remain safe
The exception forOFF is revealing too. It implies that some state transitions may be valid even when the contexts array is empty, likely because shutting something off does not require dereferencing the active context. That kind of special-case handling is normal in subsystem code, but it reinforces the need for precise checks rather than broad assumptions.A good fix should preserve that nuance. The aim is not to block legitimate administration, but to distinguish between commands that need a live context and commands that do not.
- Validate command preconditions at the top of the handler.
- Preserve legitimate
OFFsemantics. - Avoid scattering checks throughout helper functions.
- Keep the patch narrow for stable backports.
- Favor explicit rejection over implicit recovery.
The Broader Linux Security Pattern
CVE-2026-31458 fits a recurring pattern in Linux kernel security: a subsystem exposes a flexible configuration interface, another path changes the object graph behind that interface, and a later command assumes the old structure still exists. The resulting fault is often a NULL dereference, use-after-free, or out-of-bounds access. Each case looks different at the code level, but the security lesson is nearly the same.That lesson is that object lifetime must be treated as part of the public contract, even inside the kernel. If a sysfs write can remove the last context, then any command that depends on a context must verify its presence before proceeding. The code should not assume state just because the caller is privileged. Privilege does not replace validation.
The wider ecosystem also benefits from this kind of disclosure. Once the CVE is public, downstream vendors can map their own backports, administrators can verify whether their kernel branch includes the fix, and security teams can prioritize review of any automation that touches DAMON settings. That is how a small upstream patch turns into a real-world reduction in exposure.
Why kernel CVEs are often “small” but not trivial
Kernel CVEs frequently describe a single bad assumption with a concrete reproduction path. That can make them sound minor compared with high-profile remote-execution bugs. But the scale of the bug is not determined by the length of the description. It is determined by where the bug sits, who can reach it, and what failure mode it causes.Here, the bug sits in a privileged kernel management path. It can be triggered by valid sysfs operations. And it can crash the kernel. Those three facts are enough to justify taking it seriously.
What defenders should infer
Even before a formal CVSS score is published, defenders can usually infer the rough shape of the risk. A privileged local NULL dereference usually maps to denial of service rather than compromise. If it is in a server subsystem used by automation, the operational risk goes up. If the issue has upstream fixes and stable references already, the remediation path is probably straightforward.That is exactly the situation here, and it argues for prompt patching rather than waiting for formal scoring to settle.
- Kernel bugs can be operationally serious without being remotely exploitable.
- Privileged management paths are still security-relevant.
- Public backports are a strong signal of real-world importance.
- A simple crash can still become a production outage.
- Validation bugs are often the first step toward deeper failures if left uncorrected.
Strengths and Opportunities
The good news is that this CVE appears to have a clean, targeted fix path. Because the defect is a missing guard rather than a structural corruption problem, the kernel can likely close it with a small change at the command entry point. That lowers regression risk and makes downstream backports easier to land quickly.- The reproduction path is clearly described.
- The bug is easy to reason about once the state transition is understood.
- The fix location is obvious:
damon_sysfs_handle_cmd(). - The issue appears suitable for stable-branch backporting.
- The vulnerability description helps administrators audit their own usage.
- The public record makes it easier for vendors to align fixes.
- The problem reinforces the value of strict sysfs validation.
Risks and Concerns
The obvious risk is that this is a local privileged crash, which means it can be overlooked in organizations that focus too narrowly on remote exploitability. That would be a mistake. A local crash in a server kernel can still become a serious incident if the affected machine is part of a critical workflow or automation pipeline.- Systems with automated DAMON tuning may be more exposed than expected.
- Vendor kernels may lag behind upstream fixes.
- Scripts may be reusing unsafe sysfs sequences without testing.
- The bug may only surface under edge-case state changes.
- Administrators may incorrectly assume privileged-only equals low priority.
- A crash in a management path can still interrupt production workloads.
- Similar assumption bugs may exist in neighboring sysfs handlers.
Looking Ahead
The next thing to watch is how quickly major Linux vendors fold the fix into supported kernel streams. The CVE record already includes stable-kernel reference links, which strongly suggests the patch has moved into the normal upstream and backport pipeline . That is encouraging, but it does not eliminate the usual lag between upstream publication and broad deployment in enterprise environments.It will also be worth watching whether follow-ok appears in related command paths. Bugs like this often reveal neighboring assumptions once maintainers start examining the handler structure more closely. If one command trusted
contexts_arr[0] too much, adjacent commands may deserve similar scrutiny even if they are not yet publicly flagged.What to watch next
- Vendor kernel advisories that include the DAMON sysfs fix.
- Backports into long-term-support Linux kernel branches.
- Any additional DAMON sysfs hardening patches.
- Distribution package updates that mention the CVE explicitly.
- Automation or orchestration tooling that touches DAMON state.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center