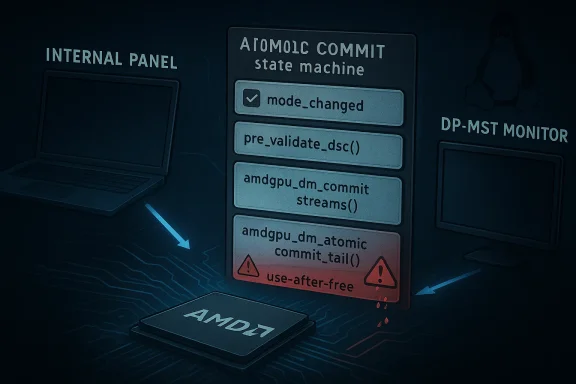
CVE-2026-31488 is a reminder that in the Linux graphics stack, seemingly small state-machine mistakes can cascade into serious memory-safety failures. The flaw sits in amdgpu’s Display Core path, where DSC validation incorrectly clears the CRTC mode_changed flag even when other, unrelated mode changes are still pending in the same atomic commit. That misclassification can prevent the driver from releasing an old stream while also failing to take a reference on the new one, creating both a leak and a later use-after-free path, which is exactly the kind of kernel bug that can turn ordinary display activity into a stability and security problem VE is not about a flashy remote exploit or a dramatic privilege-escalation primitive. It is about a failure to preserve the distinction between “this stream’s DSC timing didn’t change” and “this CRTC has no other mode changes pending.” That distinction matters because atomic KMS commits often bundle multiple display changes together, and the AMD display stack must keep each affected stream’s lifecycle consistent across the validation phase and the commit tail phase
The vulnerability’s DSC pre-validation was allowed to overwrite a broader bit of commit intent. In the scenario described in the advisory, a laptop’s internal panel might be reconfigured at the same time an external DP-MST display is attached, and the internal panel’s mode_changed state could be dropped simply because its DSC timing did not need adjustment. That is incorrect because the panel may still have an unrelated mode change in the same atomic transaction, and the driver must not conflate the two
The result is subtle but dangerous. By ttc_state
To understand why this bug matters, it helps to step back and ux display architecture is layered. The kernel documentation describes Display Core (DC) as the OS-agnostic half and Display Manager (DM) as the OS-dependent wrapper that sits between DRM and DC. DC handles hardware programming and resource management, while DM handles atomic plumbing and integration with DRM’s state model
That architecture is powerful, but it also creates a lot of room for state to be transformed more than once. Atomic display commits do not simply “set a mode.” They carry connector changes, plane changes, CRTC changes, and sometimes bandwidth-related recalculations, all of which may be validated before any hardware programming occurs. In AMD’s case, the display manager has to map DRM’s atomic state into a DC state, validate it, and then later commit it without losing the meaning of any of the original transitions
The issue in CVE-2026-31488 surfaced after a prior change, commit 17ce8a6907f7, introduced DSC pre-validation in atomic check. That earlier logic apparently treated a no-timing-change result for one stream as reason enough to clear the CRTC’s
This is why thbeyond the immediate memory-safety impact. It exposes a broader truth about atomic graphics code: when a subsystem tries to “optimize away” work, it must be absolutely certain it is not also erasing the record of a different, unrelated update. That is especially critical in kernel display code, where reference counting and state cleanup are tied directly to whether the old and new stream objects are considered live at commit time
The trap is that DSC validation is only one part of a larger atomic commit. If DSC precomputation concludes that no timing change is necessary for a stream, it may be tempting to treat the CRTC as effectively unchanged. But the advisory makes clear that there is no reliable way to know whether unrelated mode changes are pending when DSC validation runs, so that inference is invalid by design
That ernel’s atomic helpers do not operate in a vacuum. By the time the validation function gets involved, other pieces of state have already been populated, and some streams may already have been recreated. Clearing
In practical terms, that can happen when a laptred based on the presence of external screens. The user may only see “plug in monitor, display changes,” but internally the kernel may be processing a multi-object update where one CRTC needs a topology adjustment and another needs a panel-mode update. The CVE says the AMD path could treat the latter as irrelevant if DSC pre-validation concluded its own timing data did not change
That is what makes this a real security issue rather than a mere correctness bug. The advisory includes a KASAtream_release` writing through freed memory in a workqueue context. A bug that manifests as a later use-after-free in the display stack is exactly the sort of defect that kernel hardening tools are designed to catch, and the presence of a KASAN report strongly suggests the issue was reproducible and concrete enough to merit a CVE
That may sound like an implementation detail, but in graphics code it is the implementation details that keep the object graph coherent. A driver can often survive a harmlesan unnecessary recomputation. It cannot survive losing track of whether an object should be released, referenced, or retained. That is where the wrong assumption becomes an exploitable memory-lifecycle bug
The kernel documentation explicitly notes that atomic checking constructs a DC state reflecting the desired hardware state, then validates it without modifying the current state. That principle is sound, but it also means that any post-validation mutation of flags must preserve intent with surgical precision. Clearing
KASAN catches bugs that otherwise might sit silently in production until a later operation reuses freed memory. So the fact that this CVE includes a KASANect more credible and more serious, not less. It means the bad state was not hypothetical; it had enough structure to trigger a concrete memory-safety violation in testing or debugging
For consumer systems, the risk is concentrated on laptops and desktops using AMD graphics in modesetting scenarios that mix internal panels and external DP-MST monitors. For enterprise fleets, theat a display crash on a managed workstation or thin-client system can still become an availability event, especially if it interrupts interactive sessions, remote assistance, or kiosk-style workflows
That kind of change reflects mature kernel engineering. The goal is not to make validation smarter in the abstract; it is to make it less presumptive. When the driver cannot know whether another mode change is pending, the safe behavior is to preserve the bro overwriting it with a local optimization result
By fixing the flag at its source, the patch avoids trying to compensate for corrupted intent later in the pipeline. That matters in the Linux graphics stack, where later commit phases are often constrained by decisions already made during atomic check. In other words, once validation has lied about s pipeline can only react to the lie
This is a common pattern in display-driver history. As code becomes more efficient, it also becomes more stateful. As soon as an optimization depends on earlier validation results, the code must maintain a precise paper trail of what is known, what is inferred, and what remains unresolved. Losing that paper traiith a leak or a use-after-free instead of a cleaner display commit
That matters because graphics bugs are notoriously sensitive to regressions, and vendors often move cautiously. A fix that is minimal, easily understood, and directly tied to the failure mode is exactly the kind of change downstream maintainers prefer. In practice, that impro vulnerable logic will disappear from shipping kernels rather than linger in customized vendor trees
That said, the patch itself appears narrow enough that it should be easier to absorb than a broad display rewrite. The ideal outcome for enterprises is that the fix lands through normal kernel updates without changing user-facing behavior except to remove a rare instability. In other words, this is exactly the sort of bug that should be boring after it is patched
There is also a broader maintenance concern. When code uses opg rewrites, future contributors may assume those flags are authoritative even when they were derived from a narrower context. That kind of assumption tends to breed follow-on bugs. The best outcome from this CVE would be not just the fix itself, but a stronger review culture around state preservation in the AMD display stack
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
The vulnerability’s DSC pre-validation was allowed to overwrite a broader bit of commit intent. In the scenario described in the advisory, a laptop’s internal panel might be reconfigured at the same time an external DP-MST display is attached, and the internal panel’s mode_changed state could be dropped simply because its DSC timing did not need adjustment. That is incorrect because the panel may still have an unrelated mode change in the same atomic transaction, and the driver must not conflate the two
The result is subtle but dangerous. By ttc_state
has already built new streams for the relevant CRTCs, the later logic inamdgpu_dm_commit_streamsmay no longer release the old stream, whileamdgpu_dm_atomic_commit_tailmay fail to acquire the new one. That leaves the kernel with mismatched ownership bookkeeping, which the advisory says can manifest as a memory leak first and a **KASAN-detected use-after-free** later when the stream is disabled The fix is correspondingly narrow: remember the preexisting [ICODE]rom before a CRTC was marked as potentially affected by DSC configuration changes, and restore that earlier value inpre_validate_dsc[/ICODE] instead of blindly clearing it. The patch is therefore not a redesign of the display pipeline; it is a correction to state preservation at the exact point where validation logic was trampling unrelated commit intent
 Background
Background
To understand why this bug matters, it helps to step back and ux display architecture is layered. The kernel documentation describes Display Core (DC) as the OS-agnostic half and Display Manager (DM) as the OS-dependent wrapper that sits between DRM and DC. DC handles hardware programming and resource management, while DM handles atomic plumbing and integration with DRM’s state modelThat architecture is powerful, but it also creates a lot of room for state to be transformed more than once. Atomic display commits do not simply “set a mode.” They carry connector changes, plane changes, CRTC changes, and sometimes bandwidth-related recalculations, all of which may be validated before any hardware programming occurs. In AMD’s case, the display manager has to map DRM’s atomic state into a DC state, validate it, and then later commit it without losing the meaning of any of the original transitions
The issue in CVE-2026-31488 surfaced after a prior change, commit 17ce8a6907f7, introduced DSC pre-validation in atomic check. That earlier logic apparently treated a no-timing-change result for one stream as reason enough to clear the CRTC’s
mode_changed flag. The new CVE shows why that shortcut was too aggressive: a stream can be unrelated to another concurrent mode change, and the validation routine cannot assume the absence of a DSC delta means the absence of all relevant display upd example is especially realistic because modern laptops often behave differently when external monitors are present. An internal panel may switch behavior depending on whether HDR, refresh-rate constraints, or panel-aware power logic are active, while external DP-MST displays can force topology changes elsewhere in the same KMS transaction. In that kind of environment, the driver must preserve separate state transitions even when one subpath appears unchangedThis is why thbeyond the immediate memory-safety impact. It exposes a broader truth about atomic graphics code: when a subsystem tries to “optimize away” work, it must be absolutely certain it is not also erasing the record of a different, unrelated update. That is especially critical in kernel display code, where reference counting and state cleanup are tied directly to whether the old and new stream objects are considered live at commit time
How the Bug Emerges
At a high level, the failure is a lifecycle mismatch. A CRTC that should remain marked as mode-changed is instead normalized back to a state that suggests no active mode transition remains. That altered bit then shapes the later commit path, meaning the driver’s object-management logic operates on incomplete information. Once that happens, the stream ownership bookkeeping divergeshe validation trapThe trap is that DSC validation is only one part of a larger atomic commit. If DSC precomputation concludes that no timing change is necessary for a stream, it may be tempting to treat the CRTC as effectively unchanged. But the advisory makes clear that there is no reliable way to know whether unrelated mode changes are pending when DSC validation runs, so that inference is invalid by design
That ernel’s atomic helpers do not operate in a vacuum. By the time the validation function gets involved, other pieces of state have already been populated, and some streams may already have been recreated. Clearing
mode_changed at that point can make the subsequent commit phase believe it is safe to skip release or reference acquisition logic that would otherwise be requiredWhy unrelated mode chager
The word unrelated is doing a lot of work in this CVE. The bug is not that DSC mode changes are mishandled in isolation. It is that a completely separate mode change on the same atomic transaction can be erased by a validation path that only sees one stream’s timing result. That means the bug crosses a conceptual boundary: the display stack is confusing stream-local timing decisions with transaction-wide CRTC stateIn practical terms, that can happen when a laptred based on the presence of external screens. The user may only see “plug in monitor, display changes,” but internally the kernel may be processing a multi-object update where one CRTC needs a topology adjustment and another needs a panel-mode update. The CVE says the AMD path could treat the latter as irrelevant if DSC pre-validation concluded its own timing data did not change
- The bug is rooted in state conflation, not a single arithmeticdecision occurs during DSC pre-validation.
- The failure only becomes dangerous when other mode changes coexist in the same commit.
- The downstream consequence is lifecycle mismatch for stream objects.
- The eventual symptom can be a memory leak, a use-after-free, or both
The memory-management failure
Once the old stream is no longer released, the kernel it should have dropped. That alone is a resource-management bug, but in kernel graphics code it also destabilizes object ownership, because the rest of the commit path may assume the stream transition happened cleanly. When the new stream is never properly referenced, the object can later be freed out from under code that still believes it is validThat is what makes this a real security issue rather than a mere correctness bug. The advisory includes a KASAtream_release` writing through freed memory in a workqueue context. A bug that manifests as a later use-after-free in the display stack is exactly the sort of defect that kernel hardening tools are designed to catch, and the presence of a KASAN report strongly suggests the issue was reproducible and concrete enough to merit a CVE
Why DSC Validation Is a Sharp Edge
Display Stream Compression is a bandwidth-management feature, but the security storDSC itself and more about the extra complexity it adds to commit-time reasoning. Every time the driver tries to validate whether a stream can be compressed without changing timings, it is adding another conditional branch to a state machine that already has to track modes, connectors, planes, and topologiesTiming changes versus mode changes
The key conceptual mistake is to equate “no timing change” with “no mode change.” Those are not the same thing, t model where a stream may be affected by a separate transformation elsewhere in the atomic state. The CVE’s wording makes clear that the driver had no safe basis for deducing that unrelated state was absent, and so it should not have rewritten the CRTC’s mode flag as though the entire transaction were DSC-onlyThat may sound like an implementation detail, but in graphics code it is the implementation details that keep the object graph coherent. A driver can often survive a harmlesan unnecessary recomputation. It cannot survive losing track of whether an object should be released, referenced, or retained. That is where the wrong assumption becomes an exploitable memory-lifecycle bug
Why AMD’s pipeline is vulnerable here
AMD’s DM/DC split makes this class of bug more likely because the display manager has to bridge two different concepts of state. DRM atomic state exprefiguration changes, while DC state expresses hardware-programmable streams. Any logic that tries to optimize between them must be very careful not to collapse one layer’s semantics into the other’s bookkeeping rulesThe kernel documentation explicitly notes that atomic checking constructs a DC state reflecting the desired hardware state, then validates it without modifying the current state. That principle is sound, but it also means that any post-validation mutation of flags must preserve intent with surgical precision. Clearing
mode_changed too aggressively is the opposite of that discipline- DSC validation is a bandwidth decision, not a complete modeset oracle.
- Commit-time state must remain transaction-aware.
- Validation shortcuts are risky when they reassign ownership semantics.
- The AMD display path depends on keeping DRM and DC concepts aligned.
- A single boolean can determine whether kernel objects are freed correctly or leaked indefinitely
The Exploitability Question
This CVE does not read like a classic attacker-controlled exploit where a remote adversary can directly steer memory into arbitrary code execution. Instead, it is a kernel lifecycle corruption problem that becomes security-relevant because it can produce a use-after-free under realistic display activity. That means the practical risk is heavily tied to local system usage, graphical session churn, and the presence of affected AMD hardwareWhat KASAN is telling us
The advisory’s included crash trace is important. It shows a write indc_stream_release while a str in an invalid state, and the call chain runs through destruction and atomic state clearing. That is the hallmark of an ownership bug, not a benign warning. In kernel space, especially in a driver that manages complex object graphs, a use-after-free is always a red flag even if the immediate effect is “just” a crashKASAN catches bugs that otherwise might sit silently in production until a later operation reuses freed memory. So the fact that this CVE includes a KASANect more credible and more serious, not less. It means the bad state was not hypothetical; it had enough structure to trigger a concrete memory-safety violation in testing or debugging
Likely impact profile
The most likely real-world impact is local denial of service or a graphics-stack crash, but kernel use-after-free bugs deserve more caution than Even when the primary symptom is instability, memory corruption can sometimes become a stepping stone to higher-impact exploitation if the surrounding allocation patterns are favorable. The disclosure does not claim such an escalation path, but it would be unwise to dismiss the issue simply because the published symptom begins with a leak and a crashFor consumer systems, the risk is concentrated on laptops and desktops using AMD graphics in modesetting scenarios that mix internal panels and external DP-MST monitors. For enterprise fleets, theat a display crash on a managed workstation or thin-client system can still become an availability event, especially if it interrupts interactive sessions, remote assistance, or kiosk-style workflows
The Kernel Fix and Why It Works
The remediation strategy is to preserve the earlier mode_changed value rather than recomputing it from a narrower DSC-specific condition. That is a classic kernel fix patte validation lacks enough global context, it must not overwrite broader transactional state with a guess derived from partial informationA deliberately narrow correction
The fix’s restraint is its strength. It does not attempt to infer whether unrelated mode changes exist. It does not add a speculative new synchronization mechanism. It simply restores the mode flag to value from before the CRTC was marked as potentially DSC-affected. That makes the patch easier to reason about, easier to backport, and less likely to introduce collateral regressions in stable kernelsThat kind of change reflects mature kernel engineering. The goal is not to make validation smarter in the abstract; it is to make it less presumptive. When the driver cannot know whether another mode change is pending, the safe behavior is to preserve the bro overwriting it with a local optimization result
Why the fix belongs in pre_validate_dsc
Placing the correction inpre_validate_dsc is also telling. The bug originates at the point where DSC-related evaluation occurs, so the fix belongs there rather than downstream in commit-tail cleanup. That is a strong signal thatod the issue as one of state provenance: once the wrong flag has been written, later paths are already making decisions on bad assumptionsBy fixing the flag at its source, the patch avoids trying to compensate for corrupted intent later in the pipeline. That matters in the Linux graphics stack, where later commit phases are often constrained by decisions already made during atomic check. In other words, once validation has lied about s pipeline can only react to the lie
- The fix restores truthful transaction state.
- It avoids guessing about unrelated mode changes.
- It prevents the commit phase from skipping stream release.
- It ensures the new stream can be referenced correctly.
- It reduces the risk of future KASAN-visible use-after-free failures
Historical Context
The CVE is best understood as a consequence of an earlier optimization path. Commit 17ce8a6907f7 added DSC pre-validation in atomic check, presumably to avoid unnecessary work when compression-related re-evaluation would not alter timings.ation is common in display code because bandwidth and latency tradeoffs matter, but every optimization that rewrites state early must be careful not to discard unrelated intentThe “good idea, wrong boundary” problem
Many kernel bugs arise not because a feature is bad, but because a feature’s safe boundary is narrower than the implementation assumed. Here, the boundary appears to have been the relationship between a stream’s DSC timing and **the CRTC’s wide former can be locally unchanged even when the latter is still active, and collapsing them into the same boolean was too aggressiveThis is a common pattern in display-driver history. As code becomes more efficient, it also becomes more stateful. As soon as an optimization depends on earlier validation results, the code must maintain a precise paper trail of what is known, what is inferred, and what remains unresolved. Losing that paper traiith a leak or a use-after-free instead of a cleaner display commit
Why this matters for stable kernels
The CVE was published with a stable backport trail, which is significant. Stable backports are often the bridge between an upstream bug and real-world remediation, especially in enterprise distributions and OEM device firmware. The fact that this issue has already been cherry-picked into stable references suggests maintainers considered it sufficiently concrete and risky to warrant propagation beyond mainline reviewThat matters because graphics bugs are notoriously sensitive to regressions, and vendors often move cautiously. A fix that is minimal, easily understood, and directly tied to the failure mode is exactly the kind of change downstream maintainers prefer. In practice, that impro vulnerable logic will disappear from shipping kernels rather than linger in customized vendor trees
Enterprise and Consumer Impact
For consumers, the most relevant scenario is a desktop or laptop using AMD graphics with external monitor setups, especially multi-display configurations where the system may dynamically alter panel behavior. Users are unlikely to notice a CVE label, buplay instability, a black screen, or a rare crash when docking, undocking, or toggling monitor arrangementsConsumer risk profile
The consumer threat model is usually not about deliberate exploitation. It is about reliability in normal use. A use-after-free in a display driver can surface as a hard crash, compositor failure, or graphical session reset, all of which are bad enough on a personal machine and worse on a s updates. Quiet bugs like this can survive longer than headline-grabbing ones because users tend to blame hardware, monitors, or desktop environments before they blame the kernel- Docking stations and multi-monitor setups are the most relevant consumer trigger.
- Laptop internal panels may participate in the problematic state transition.
- Symptoms can look like ordinary display flakiness before they look like security issues.
- Long-lived consumer kernels can remain exposed if update cadence is slow.
- The bug oy users first and worry security teams second
Enterprise risk profile
Enterprises also have to think about fleet diversity. Some machines will have docked dual-monitor setups, some will not, and some may switch between both in ways that are hard to reproduce in test labs. That makes this bug especially tricky for endpoint managers, because the triggering condition is not just “installed kernel” but “installed kernel pltopology plus the right commit sequence”That said, the patch itself appears narrow enough that it should be easier to absorb than a broad display rewrite. The ideal outcome for enterprises is that the fix lands through normal kernel updates without changing user-facing behavior except to remove a rare instability. In other words, this is exactly the sort of bug that should be boring after it is patched
Strengths and Opportunitthis fix is that it addresses a specific state-handling flaw without broad collateral damage. It preserves the existing display model, respects atomic commit semantics, and should be comparatively friendly to stable backporting. More importantly, it exposes a class of validation mistakes that maintainers can now watch for in adjacent AMD display paths and other DRch is surgical rather than structural.
- It preserves the distinction between local DSC timing and global commit state.
- It is likely to be a good stable backport candidate.
- It reduces the chance of stream leak behavior.
- It reduces the chance of KASAN-visible use-after-free crashes.
- It clarifies the contract between validation and ownership.
- It creates an opportunity to audit similar flag-reset logic elsewhere in the graphics stack
Risks and Concerns
The biggest cg sits in a part of the kernel where state mistakes are cumulative. Even if the first symptom is just a leak, the same broken ownership model can later become a use-after-free or another memory-management defect. In graphics drivers, those issues are often intermittent and hardware-dependent, which makes them difficult to reproduce and easy to underestimate.- The flaw may be hard to reproduce wnitor topology**.
- Users may dismiss it as a mere graphics glitch.
- Vendor kernels can lag behind mainline fixes.
- The impact may vary across laptops, desktops, and docked systems.
- Testing may miss it if no one exercises concurrent mode changes.
- A fix not yet present in all downstream branches can leave exposure windows open.
- Similar boolean-state shortcuts may still exist in nearby code paths
There is also a broader maintenance concern. When code uses opg rewrites, future contributors may assume those flags are authoritative even when they were derived from a narrower context. That kind of assumption tends to breed follow-on bugs. The best outcome from this CVE would be not just the fix itself, but a stronger review culture around state preservation in the AMD display stack
Looking Ahead
The immediate question is how quickly the fix lands in the kernel buildistro kernels, OEM images, and enterprise-managed endpoints. Upstream resolution is important, but shipping kernels determine the real exposure window. Because this issue sits in the graphics path, some vendors may be cautious about backport timing, especially if they need to validate the change across a range of laptop and docking configurationsWhat to watch next
The next few weeks will likely show whhis as a routine stability backport or as a more urgent memory-safety correction. Either way, admins should watch for package updates that mention AMD display, DC, DRM, or mode-setting fixes. In heterogeneous fleets, it will also be important to check whether the same kernel version behaves differently depending on display topology and docking behavior- Distribution advisoriesshipped kernel branches.
- OEM firmware and kernel bundles for AMD-powered laptops.
- Regression reports involving docks, MST hubs, or HDR panel toggles.
- Additional cleanup in AMD DC/DM code that touches
mode_changedhandling. - Any follow-on fixes that clarify commit-state preservation in related display paths
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center