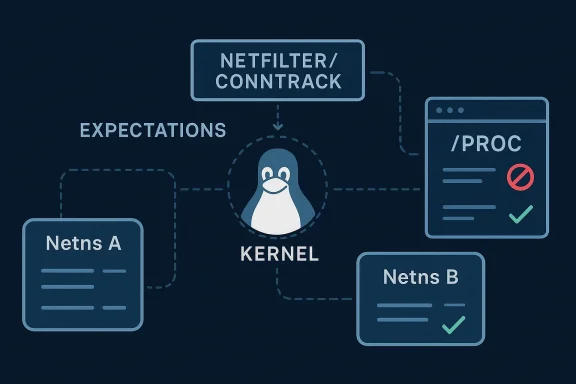
CVE-2026-31496 is a narrowly scoped Linux kernel vulnerability, but it sits in one of the kernel’s most security-sensitive corners: netfilter and conntrack expectations. The newly published record says the bug was resolved by skipping expectation entries that do not belong to the current network namespace when they are dumped through
Linuare one of the core technologies that make modern container networking and multi-tenant isolation possible. They let the kernel maintain separate networking state for different workloads, so one namespace’s conntrack, routing, and netfilter state should not bleed into another. That isolation is not just a convenience feature; it is part of the security model for workloads that share the same kernel but are supposed to behave as if they were on separate machines. The kernel documentation for conntrack makes clear that connection tracking is a stateful subsystem exposed through nfnetlink and
Conntrack expectations are a specialized part of that subsystem. They exist so the kernel can anticipate that one flow will lead to another related flow, such as when a control channel opens a separate data channel. Helpers interpret protocol-specific behavior and attach metadata that the kernel later uses for tracking and policy decisions. That metadata is visible to userspace through administrative interfaces, which makes accuracy and boundaally important.
The vulnerability record for CVE-2026-31496 says the kernel fix is to skip expectations that do not reside in the current network namespace when the
At a policy level, the interesting thing here is that the vulnerability is not described as packet parsing failure, memory corruption, or a direct privilege escalation. Instead, it is about where the kernel allows expectation objects to be seen. That makes it a good example of the modern Linux hardening trend: many of the important fixes now protect boundaries, not just buffers. Those boundaries are often quiet until a multi-tenant or heavilynt reminds everyone why they matter.
The kernel’s choice to align the expectation dump logic with earlier conntrack boundary fixes suggests a deliberate engineering philosophy: if one class of state should be namespace-local, then related metadata should obey the same rule. That is a sound design choice because mismatched visibility rules create debugging surprises and audit gaps. In a system where network namespsecurity story, consistency is not cosmetic; it is the point.
A subtle but important point is that this is a procfs exposure fix, not a packet-path rewrite. That means the primary impact is on observability and administrative interfaces, not on how packets are forwarded in the hot path. Those fixes still matter enormously, because admin tooling often becomes part of the attack surface in container-heavy environments. What looks like “just a dump path” can still leak state at exactly the wrong layer.
That is why the kernel has been tightening dump behavior around conntrack state. Earlier work stopped
This matters more in 2026 than it did in the early days of netfilter because modern systems routinely run many isolated workloads on the same host. Containers, service meshes, firewall appliances, and multi-tenant edge systems all depend on exact namespace semantics. A failure in that semantics is not an academic bug; it can become an operational issue in environments where administrators assume that every namespace sees only its own state.
The fact that NVD has not yet assigned a final severity score should not be interpreted as low urgency. Fresh kernel CVEs frequently enter public systems before all enrichment is complete, and Microsoft’s advisoat this one is already part of the broader ecosystem view. In practical terms, the upstream fix and stable backport trail are stronger signals than a temporarily blank CVSS field.
Another reason to take this seriously is the growing overlap between Linux namespaces and orchestration tooling. Kubernetes nodes, network appliances, and container runtimes often depend on exact procfs and netfilter semantics. When visibility rules are inconsistent, the resulting confusion can cascade into monitoring blind spots or mistaken policy assumptions. That is especially dangerous in systems where operators use procfs output as an audit or troubleshooting source.
That lag is not unusual, but it is important. A CVE can be publicly known while a lot of deployed systems remain exposed simply because their update streams move at the pace of certification or long-term support policy. For kernel issues that affect observability or container isolation, that delay can matter even when the bug is not remotely exploitable in the obvious sense.
The larger signal here is that the kernel community considered the fix worth carrying across supported lines, not just the newest development branch. That tends to mean the maintainers see a reality boundary problem, not a cosmetic oddity. Stable backports are often the best clue that a bug has production significance even before the formal scoring catches up.
This is especially relevant in cloud and Kubernetes environments, where multiple workloads share the same host kernel while still expecting clear separation of network state. In such systems, a small procfs visibility defect can have an outsized effect because operators often rely on low-level introspection tools to understand behavior. When the kernel’s view is not properly scoped, the tooling may be accurate only for the wrong namespace.
There is also a downstream support dimension. Vendors that ship firewall appliances or managed network software need clean namespace semantics because customers often use those devices as security anchors. If a support engineer data from another namespace, the resulting confusion can extend troubleshooting and muddy root-cause analysis. That is not a dramatic security exploit, but it is a real operational cost.
The consumer story also matters because the line between consumer Linux and embedded infrastructure is thinner than it looks. Home routers, small-office appliances, and even some consumer edge devices run Linux kernels with netfilter features enabled. Those systems may not look like “enterprise infrastructure,” but they are often handling precisely the kind of networking state where namespace correctness matters.
That said, consumer users should not overreact. This does not read like the kind of CVE that demands immediate panic or extraordinary mitigation steps. It is a kernhat should be folded into normal update discipline, with urgency scaled to whether the device actually depends on the affected netfilter paths. Patch it when your vendor ships it; prioritize it if the box is doing routing, firewalling, or container work.
Microsoft’s inclusion of the CVE in its Security Update Guide also reflects a broader trend: Linux CVEs increasingly show up in enterprise vulnerability workflows that are not strictly Linux-only. That gives mixed-platform organizations one more place to notice and track the issue, but it also raises the bar for clarity. A bug like this needs to be understood in the context of Linux namespaces and conntrack, not just scored generically.
The ecosystem lesson is that infrastructure trust depends on quiet correctness. A fix that prevents one namespace from dumping another namespace’s expectation data may never generate headlines, but it still improves the reliability of the Linux platform as a whole. In a market where cloud, container, and edge providers all compete on trust and operational integrity, that kind of incremental hardening has real value.
The second strength is that the issue is understandable to operators. The namespace boundary is a concept most Linux administrators already know, which means the risk can be communicated without deep kernel archaeology. That matters because a fix that is easy to explain is also easier to deploy responsibly.
A second concern is patch lag. Many systems that matter most here are not direct upstream consumers; they are distribution kernels, appliance images, or vendor-maintained builds. That means the bug can remain present long after the upstream fix is public, especially in environments with certification or slow maintenance windows.
A final concern is that namespace bugs often cluster. Once one boundary mistake is found in a subsystem, maintainers and operators should ask whether adjacent dump or helper code carries the same assumption. The danger is rarely the single bug; it isthe bug possible.
In the end, this CVE does not tell a story about dramatic exploitatiabout discipline: namespace discipline, reporting discipline, and the slow, necessary work of making sure the kernel only reveals what it should, where it should. That is the kind of hardening that rarely gets applause, but it is also the kind that keeps modern Linux deployments trustworthy when the pressure is on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
/proc, which closes an information boundary issue that could otherwise expose state from another namespace. The change is explicitly compared to the earlier conntrack fix that stopped /proc from dumping other namespaces’ conntrack entries, underscoring that this is part of a broader hardening pattern rather than an isolated mistake. th attention is not flashy exploitability, but the fact that Linux is tightening the rules around what privileged networking state can be observed across network namespaces. That matters for container hosts, gateways, firewalls, and any system that relies on conntrack helpers for complex traffic handling. Microsoft’s Security Update Guide now lists the CVE as published and linked to the kernel.org fix trail, even though NVD’s enrichment is still incomplete, which is often the first sign that a kernel issue is moving from upstream reality into downstream patch workflows.
 Background
Background
Linuare one of the core technologies that make modern container networking and multi-tenant isolation possible. They let the kernel maintain separate networking state for different workloads, so one namespace’s conntrack, routing, and netfilter state should not bleed into another. That isolation is not just a convenience feature; it is part of the security model for workloads that share the same kernel but are supposed to behave as if they were on separate machines. The kernel documentation for conntrack makes clear that connection tracking is a stateful subsystem exposed through nfnetlink and /proc, which means careful namespace scoping is essential.Conntrack expectations are a specialized part of that subsystem. They exist so the kernel can anticipate that one flow will lead to another related flow, such as when a control channel opens a separate data channel. Helpers interpret protocol-specific behavior and attach metadata that the kernel later uses for tracking and policy decisions. That metadata is visible to userspace through administrative interfaces, which makes accuracy and boundaally important.
The vulnerability record for CVE-2026-31496 says the kernel fix is to skip expectations that do not reside in the current network namespace when the
/proc path emits them. That sounds simple, but it is exactly the kind of rule that prevents cross-namespace leakage in a subsystem that routinely handles privileged internal state. The upstream description explicitly ties the fix to an earlier commit that stopped conntrack dumps from showing objects belonging to other namespaces, which suggests the kernel maintainers are cleaning up a family of related exposure pas also fits the Linux kernel’s broader security trajectory in 2026: less reliance on implicit assumptions, more reliance on explicit ownership and namespace checks. The more containerized Linux becomes, the more dangerous it is to assume that “it is just diagnostic output” and leave edge-case state visible outside the right namespace. In practice, a bug in a procfs dump path can become an information exposure issue, a debugging confusion problem, or a trust problem for orchestration tools that rely on clean separation.At a policy level, the interesting thing here is that the vulnerability is not described as packet parsing failure, memory corruption, or a direct privilege escalation. Instead, it is about where the kernel allows expectation objects to be seen. That makes it a good example of the modern Linux hardening trend: many of the important fixes now protect boundaries, not just buffers. Those boundaries are often quiet until a multi-tenant or heavilynt reminds everyone why they matter.
What the Fix Actually Does
The published description says the kernel should “skip expectations that do not reside in this netns” when dumping them through/proc. In plain English, the output routine now refuses to report expectation entries that belong to a different network namespace. That makes the dump path behave like the conntrack dump fix referenced in the advisory, where the kernel similarly stopped espaces’ state.Why that matters
This is not just housekeeping./proc has a long history of being useful for troubleshooting and automation, which is exactly why it has to be conservative about visibility. If a process can see expectation objects from another namespace, it can potentially infer traffic behavior, helper usage, or protocol relationships that were supposed to remain internal. Even when the information is not enough for direct compromise, it can still weaken isolation and give away operational details.The kernel’s choice to align the expectation dump logic with earlier conntrack boundary fixes suggests a deliberate engineering philosophy: if one class of state should be namespace-local, then related metadata should obey the same rule. That is a sound design choice because mismatched visibility rules create debugging surprises and audit gaps. In a system where network namespsecurity story, consistency is not cosmetic; it is the point.
A subtle but important point is that this is a procfs exposure fix, not a packet-path rewrite. That means the primary impact is on observability and administrative interfaces, not on how packets are forwarded in the hot path. Those fixes still matter enormously, because admin tooling often becomes part of the attack surface in container-heavy environments. What looks like “just a dump path” can still leak state at exactly the wrong layer.
Practical implications
- Namespace isolation is reinforced at the reporting layer.
/procoutput becomes less likely to reveal unrelated conntrack-related state.- Tools that inspect expectations should see a cleaner, more accurate view.
- The patch follows an established Linux pattern of restricting cross-namespace dumps.
- Operational debugging becomes more predictable because the output maspace.
Conntrack Expectations in Context
Conntrack is one of those Linux subsystems that many users never think about until it breaks, yet it quietly underpins a huge amount of real-world networking. It tracks state across flows so NAT, firewalling, and protocol helpers can make decisions that depend on prior traffic. The kernel documentation shows conntrack exposed through nfnetlink, with dump and get operations designed to retrieve tracked entries and related metadata.Helpers and related flows
Helpers are where conntrack becomes more specialized. They understand protocol-specific behaviors and can create or manage expectations for related traffic. That is useful for protocols that negotiate follow-on connections, but it also means the helper layer carries a lot of semantic weight. If the kernel reports the wrong helper state, or reports it across namespace boundaries, the information is still “just metadata” only in the narrowest sense. In practice, it afpolicy interpretation, and trust in the kernel’s internal model.That is why the kernel has been tightening dump behavior around conntrack state. Earlier work stopped
/proc from dumping other namespaces’ conntrack entries. CVE-2026-31496 extends that same idea to expectations, which are closely related objects and therefore should obey the same isolation rules. The logic is straightforward: if the namespace is part of the objthe dump path should respect it every time.This matters more in 2026 than it did in the early days of netfilter because modern systems routinely run many isolated workloads on the same host. Containers, service meshes, firewall appliances, and multi-tenant edge systems all depend on exact namespace semantics. A failure in that semantics is not an academic bug; it can become an operational issue in environments where administrators assume that every namespace sees only its own state.
Why administrative visibility is part of the security boundary
There is a temptation to downplay dump-path bugs because they do not directly alter packet forwarding. That is a mistake. In kernel code, visibility is often part of the control plane, and control-plane mistakes can be security issues even when the data plane stays intact. If a privileged state object from one namespace lespace’s view, the system has crossed a boundary it was supposed to enforce.- Conntrack tracks state, not just packets.
- Expectations model related future flows.
- Helpers introduce protocol-aware behavior.
/procand nfnetlink are administrative interfaces, so they must be namespace-aware.- Cross-namespace dumps can erode trust in isolation, even without a crash.
Why This Bug Is Security-Relevant
The official language does not spell out a crash or memory corruption, but that does not make the issue trivial. Security relevance in kernel networking often comes from information boundaries, not only from classic memory-safety failures. In a namespace-aware kernel, eect to the wrong observer can be enough to justify a CVE because it breaks the model that higher-level tooling and operators rely on.Isolation bugs are often underestimated
The risk here is partly psychological. Administrators tend to prioritize issues that promise obvious remote compromise, while namespace-boundary bugs can look “minor” because they are closer to correctness problems. But correctness in the kernel is a security property when the correctness determines who can see what. If a process in one namespace can see expectation objects from another, that creates a visibility defect that could assist lateral discovery, debugging confusion, or exposure of sensitive network topology details.The fact that NVD has not yet assigned a final severity score should not be interpreted as low urgency. Fresh kernel CVEs frequently enter public systems before all enrichment is complete, and Microsoft’s advisoat this one is already part of the broader ecosystem view. In practical terms, the upstream fix and stable backport trail are stronger signals than a temporarily blank CVSS field.
Another reason to take this seriously is the growing overlap between Linux namespaces and orchestration tooling. Kubernetes nodes, network appliances, and container runtimes often depend on exact procfs and netfilter semantics. When visibility rules are inconsistent, the resulting confusion can cascade into monitoring blind spots or mistaken policy assumptions. That is especially dangerous in systems where operators use procfs output as an audit or troubleshooting source.
What kind of harm could happen?
This vulnerability is best seen as a boundary breach and potential information disclosure. The exact severity will depend on how the affected output is used and how much of the expectation metato another namespace. Even a small leak can be meaningful in environments where helper names, related-flow relationships, or traffic patterns are sensitive. Not every kernel bug needs to be dramatic to matter.- It could expose internal networking state across namespaces.
- It could confuse administrative tooling that assumes strict isolation.
- It could reveal protocol-helper relationships useful for reconnaissance.
- It could undermine confidence in container and tenant separation.
- It could create a compliance concern if procfs output is trusted as scoped telemetry.
The Stable Backport Signal
The CVE record includes multiple kernel.org commit references, which is a strong indication that the fix has already been moved through the Linux stable pipeline. That matters because most organizations do not run mainline kernels directlynels that backport upstream patches. In other words, the practical question is less “Has upstream fixed it?” and more “Has my vendor picked up the fix yet?”Why backports are the real operational milestone
Linux security advisories often become actionable only when a fix lands in a stable branch and distribution maintainers can absorb it. That is especially true for networking issues, because vendors want to preserve behavior while closing the bug. The fact that this CVE is already appearing in Microsoft’s Security Update Guide and the NVD dataset means visibility is spreading, but the remediation path still depends on distro and appliance release cadence.That lag is not unusual, but it is important. A CVE can be publicly known while a lot of deployed systems remain exposed simply because their update streams move at the pace of certification or long-term support policy. For kernel issues that affect observability or container isolation, that delay can matter even when the bug is not remotely exploitable in the obvious sense.
The larger signal here is that the kernel community considered the fix worth carrying across supported lines, not just the newest development branch. That tends to mean the maintainers see a reality boundary problem, not a cosmetic oddity. Stable backports are often the best clue that a bug has production significance even before the formal scoring catches up.
What operators should infer
- The fix is likely already in one or more downstream vendor kernels.
- Version numbers alone may not tell the whole story.
- Stable backports are more meaningful than the upstream commit date by themselves.
- Mixed-vendor environments should validate the presence of the patch explicitly.
- Appliance firmware may lag behind mainstream distribution kernels.
Enterprise Impact
Enterprise environments are where CVE-2026-31496 is most likely to matter. That is because enterprises are the ones most likely to run Linux as a multi-tenant platform: container hosts, network appliances, virtualization nodes, and security gateways. In those settings, namespace boundaries are not an abstract concept; they are part of the operational architecture.Why the bug lands harder in mixed or shared environments
If an enterprise uses/proc-based tooling to inspect conntrack expectations, the integrity of that output becomes important to debugging, automation, and policy verification. A namespace leak can lead administrators to chase the wrong issue, misread traffic relationships, or assume that a helper is active in a namespace where it should not be visible. Those mistakes can waste time during incidents and complicate compliance review.This is especially relevant in cloud and Kubernetes environments, where multiple workloads share the same host kernel while still expecting clear separation of network state. In such systems, a small procfs visibility defect can have an outsized effect because operators often rely on low-level introspection tools to understand behavior. When the kernel’s view is not properly scoped, the tooling may be accurate only for the wrong namespace.
There is also a downstream support dimension. Vendors that ship firewall appliances or managed network software need clean namespace semantics because customers often use those devices as security anchors. If a support engineer data from another namespace, the resulting confusion can extend troubleshooting and muddy root-cause analysis. That is not a dramatic security exploit, but it is a real operational cost.
Enterprise priorities
- Confirm whether the affected kernel branch includes the backport.
- Check whether any tooling reads conntrack expectations from
/proc. - Review container-host and firewall-appliance kernelvendor advisories rather than assuming upstream fixes are already deployed.
- Treat the issue as a namespace-isolation hardening item, not just a bookkeeping patch.
Consumer Impact
For most consumer desktops, the practical exposure is probably lower than it is in enterprise or cloud environments. A typical laptop or workstation is less likely to depend on conntrack expectations, and many users will never notice the affected path. But “lower” is not the same as “zero,” especially on systems that double as lab machines, routers, or home gateways.Where consumer users might still care
Home users running custom firewall rules, experimenting with containers, or using Linux as a gateway may stillh. In those cases, the kernel’s expectation dump behavior could surface in diagnostic tools or maintenance scripts. If the bug leaks state across namespaces, the impact is still bounded but no longer irrelevant.The consumer story also matters because the line between consumer Linux and embedded infrastructure is thinner than it looks. Home routers, small-office appliances, and even some consumer edge devices run Linux kernels with netfilter features enabled. Those systems may not look like “enterprise infrastructure,” but they are often handling precisely the kind of networking state where namespace correctness matters.
That said, consumer users should not overreact. This does not read like the kind of CVE that demands immediate panic or extraordinary mitigation steps. It is a kernhat should be folded into normal update discipline, with urgency scaled to whether the device actually depends on the affected netfilter paths. Patch it when your vendor ships it; prioritize it if the box is doing routing, firewalling, or container work.
Consumer takeaways
- Desktop-only exposure is likely limited.
- Router and gateway roles increase relevance.
- Container hobbyists may be closer to the affected path than they think.
- Vendor kernel updates matter more than upstream commit awareness.
- This is still a worthwhile routine security update.
Competitive and Ecosystem Implications
Even though this is a Linux kernel issue, the way it is handled says a lot about the broader ecosystem. Kernel maintenance has become a competitive feature for distributions, appliance vendors, and managed infrastructure providers. The ability to absorb small but important fixes quickly is part of what customers buy when they choose a vendor stream over a raw upstream tree.Why this matters for vendors
Vendors that can backport cleanly and accurately gain credibility in exactly the environments where neost. Security teams do not only compare CVSS scores; they compare how quickly fixes appear in supported builds and how confidently they can be deployed. A narrow namespace-leak fix like this one is the sort of issue where patch quality can become a differentiator.Microsoft’s inclusion of the CVE in its Security Update Guide also reflects a broader trend: Linux CVEs increasingly show up in enterprise vulnerability workflows that are not strictly Linux-only. That gives mixed-platform organizations one more place to notice and track the issue, but it also raises the bar for clarity. A bug like this needs to be understood in the context of Linux namespaces and conntrack, not just scored generically.
The ecosystem lesson is that infrastructure trust depends on quiet correctness. A fix that prevents one namespace from dumping another namespace’s expectation data may never generate headlines, but it still improves the reliability of the Linux platform as a whole. In a market where cloud, container, and edge providers all compete on trust and operational integrity, that kind of incremental hardening has real value.
Market implications
- Distribution quality now includes namespace-boundary hygiene.
- Appliance vendors need to ship clean backports quickly.
- Mixed-platform enterprises benefit from Microsoft surfacing Linux CVEs.
- Trust in Linux observability tools improves when output scoping is consistent.
- Small kernel fixes can shape the perceived maturity of a vendor platform.
Strengths and Opportunities
The strongest aspect of CVE-2026-31496 is that it is a surgical fix with a clear security rationale. The kernel is not reinventing conntrack or changing packet behavior; it is simply enforcing the rule that a namespace-local object should stay loca/proc. That kind of precision makes the fix easier to reason about, easier to backport, and less likely to introduce collateral damage.The second strength is that the issue is understandable to operators. The namespace boundary is a concept most Linux administrators already know, which means the risk can be communicated without deep kernel archaeology. That matters because a fix that is easy to explain is also easier to deploy responsibly.
Opportunities created by the fix
- Better consistency between conntrack and expectation dump behavior.
- Reduced chance of namespace confusion in container environments.
- Cleaner operator tooling and more trustworthy
/procoutput. - Stronger precedent for future boundary checks in netfilter.
- Easier downstream backporting because the change is narrowly scoped.
- A useful reminder to audit other procfs dump paths for similar mistakes.
/proc, this is a good moment to confirm they are not relying on assumptions that were only incidentally true before the patch. A small fitest of how much you trust your telemetry path.Risks and Concerns
The main risk is underestimation. Because the advisory does not describe a crash or overt privilege escalation, it would be easy for organizations to rank it below more dramatic Linux CVEs. That would miss the point: in a namespace-aware kernel, boundary violations are security issues eke output hygiene problems.A second concern is patch lag. Many systems that matter most here are not direct upstream consumers; they are distribution kernels, appliance images, or vendor-maintained builds. That means the bug can remain present long after the upstream fix is public, especially in environments with certification or slow maintenance windows.
Operational concerns
- Vulnerability scanners may not reflect local backports accurately.
- Mixed fleets may have inconsistent patch status.
- Container hosts can hide the issue behind complex orchestration layers.
- Monitoring scripts may assume procfs output is more isolated than it is.
- Older appliances may lag behind mainstream kernel updates.
/proc output to understand conntrack expectations, any cross-namespace leakage can distort incident response or policy validation. Even if the exposure is limited, it still undermines confidence in the debugging path. That kind of ertify but easy to feel during an outage.A final concern is that namespace bugs often cluster. Once one boundary mistake is found in a subsystem, maintainers and operators should ask whether adjacent dump or helper code carries the same assumption. The danger is rarely the single bug; it isthe bug possible.
Looking Ahead
The immediate thing to watch is how quickly the fix lands in distro kernels and appliance firmware. The upstream record is already public, but most production systems will be protected only when their vendor stream absorbs the patch. For many organizations, that downstream timeline will matter more than the original kIt will also be worth watching whether more netfilter dump paths receive similar namespace scoping cleanups. The comparison to the earlier conntrack proc fix strongly suggests the maintainers view this as part of a pattern, not a one-off. That makes adjacent procfs and netlink reporting code natural candidates for further review.What to watch next
- Vendor backports for supported Linux kernel branches.
- Distribution advisories that mention conntrack or netfilter namespace dumps.
- Additional stable commits in the same procfs or conntrack area.
- Whether container-focused platforms flag the issue in their own advisories.
- Any follow-up cleanup that applies the same namespace rule to related objects.
In the end, this CVE does not tell a story about dramatic exploitatiabout discipline: namespace discipline, reporting discipline, and the slow, necessary work of making sure the kernel only reveals what it should, where it should. That is the kind of hardening that rarely gets applause, but it is also the kind that keeps modern Linux deployments trustworthy when the pressure is on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center