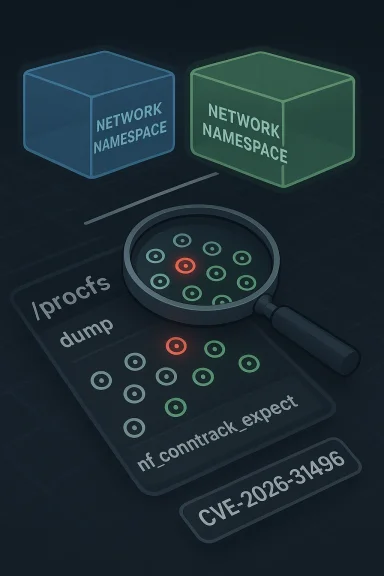
The Linux kernel’s latest netfilter CVE, tracked as CVE-2026-31496, is a small-sounding change with outsized importance for anyone who relies on conntrack visibility in production. The bug lives in
That matters because conntrack is not a niche feature reserved for firewall experts. It is part of the plumbing for home routers, enterprise gateways, container hosts, VPN endpoints, load balancers, and security appliances. When a bug lands in expectation handling, the issue may look minor in isolation, but the operational surface area can be broad. The CVE description here is not about packet parsing or memory corruption in the classic sense; it is about the kernel exposing state that belongs to another namespace, which is the sort of bug thaetween correctness and security.
Historically, the Linux networking maintainers have already dealt with a closely related problem in conntrack dumping. The CVE text explicitly points to the earlier change
The timing also tells a story. The CVE was published on April 22, 2026, and the public record already includes multiple stable-branch references from kernel.org, which strongly suggests the fix has been backported rather than left as a mainline-only correction. That is a practical signal to operators: this is not the sort of issue maintainers are waiting to “see if it matters.” They have already decided it matters enough to carry into suppo What the Vulnerability Actually Is
At its core, the flaw is a namespace isolation failure in a procfs dump path. The kernel should only report expectations that belong to the namespace being inspected, but the vulnerable logic could include expectations from other namespaces as well. In a modern Linux system, network namespaces are not cosmetic; they are an explicit isolation boundary used by containers, sandboxing stacks, and multi-tenant network setups. When proc output crosses that boundary, the bug becomes more than a bookkeeping mistake.
The worstructive: skip expectations that do not reside in this netns. That is a defensive rule, not a broad architectural change. It means the kernel does not try to infer intent or reconstruct ownership from adjacent state; it simply refuses to dump objects outside the current namespace. That is exactly the right posture for privileged metadata exposure, because it reduces the possibility that an inspection interface becomes a side channel.
kernel’s oldest and most convenience-oriented user interfaces, which makes it deceptively risky. It is often treated as “just read-only text,” but it is still a kernel export surface, and any mistakes in object filtering become visible to userspace tools. In a networking stack, those tools may be debugging, monitoring, policy-validation, or orchestration components that assume each namespace is self-contained. If the dump crosses namespace lines, the result may be inaccurate operational data even when no crash occurs.
This is why the issue has security significance even without an obvious exploit narrative. Information leakage in the kernel is rarely harmless; it can break tenant isolation, undermine observability assumptions, or reveal state that other processes were not meant to see. In container-heavy environments, that can be enough to justify a fix on its own. The vulnerability is narrow, but the trust boundary it touches is broad. cross-namespace visibility, not packet parsing.
That bridge is alsdling is security-sensitive. If the kernel exposes expectations incorrectly, it can give userspace an incomplete or misleading map of active networking state. If it keeps the wrong expectations in view, policy tools may behave as though a flow exists where it does not, or as though a flow belongs to the wrong tenant. In a container platform, those mistakes are especially annoying because they look like ordinary debugging noise until they affect one workload consistently and another never.
The pu matters. NVD notes that the entry has recently been published and that enrichment is not yet complete, while the Microsoft advisory mirrors the CVE entry. That is typical of fresh kernel disclosures: the upstream technical fix appears first, downstream scoring and severity analysis lag behind, and enterprise visibility tools ingest the identifier before a final numeric rating is available. In practice, that means administrators should read the code-path description, not wait for the scorecard to settle.
This is also why support cadence matters more than headlines. A CVE with no score can still already be on the path to broad remediation if maintainers have shipped it into supported branches. Conversely, a neatly scored vulnerability can remain practically exposed for a long time if vendors lag in shipping the backport. In other words, the operational risk is governed less by the number attached to the bug and more by whether the fix has actually reached the kernel you boot.
For administrators, the practical implication is simple: check vendor advisories, not just version numbers. A kernel can be “new enough” in terms of release date and still miss the backported commit if your distribution has not pulled it in yet. That is especially true in long-term-support environments where stability policies intentionally slow the flow of changes.
The operational downside is subtle but serious. If a fleet’s observability or debugging stack consumes conntrack expectation data, a cross-namespace dump can make two unrelated workloads appear coupled. That can waste incident-response time, confuse policy validation, and obscure the real source of a network problem. In security-sensitive environments, misleading state is often almost as dangerous as missing state.
There is also a compliance angle. If a namespace is supposed to represent a tenant boundary, then a proc export that reveals state from another tenant may create audit noise or even ponding on how the environment is built. That is why an issue like this can matter even without exploitation proof: the business risk is tied to integrity and isolation, not just to code execution.
That means the “consumer” label can be misleading. A user might think of a box as a personal machine while it quietly acts as a gateway for the whole house or office. In that scenario, a kernel bug in a networking dump path is not just a theoretical concern; it is part of the trust chain that keeps traffic segmentation and monitoring coherent. The fix remains worth applying even if the immediate day-to-day symptom is invisible.
The broader lesson is that consumer-versus-enterprise distinctions in Linux are often about role, not device class. A small box can be the core of a home network, and a desktop can host lab workloads that mimic enterprise behavior. Security teams should treat the actual network role as the deciding factor, not the sticker on the hardware.
This also helps explain why the fix is small. Whe boundary check, the remedy is usually to make the boundary check stricter. The kernel already knows how to identify the current namespace; the bug was that it failed to apply that knowledge consistently in expectation dumping. A broader rewrite would have been unnecessary and riskier.
In that sense, CVE-2026-31496 is part of a recurring maintenance theme: fewer indirect lookups, fewer assumptions, and tighter ownership rules around what the kernel exposes to userspace. That is the kind of progress that rarely makes headlines but steadily improves the reliability of the Linux networking stack.
The best triage path is straightforward. First, determine whether the system uses conntrack expectations in a meaningful way. Second, identify whether
There is also a broader opportunity here for better tooling discipline. Teams that depend on conntrack output can use this CVE as a reminder to verify that their observability stack is actually reading the namespace they think it is reading. In multi-tenant systems, silent boundary drift is often more dangerous than obvious failure, because it undermines trust before anyone notices.
Another concern is patch lag. Even after the fix is public, many fleets run vendor kernels that may not pick it up immediately, especially in appliance and long-term-support channels. That creates a window where the vulnerability is known but still present in the exact kernels that matter most. That lag is often where real exposure lives, not in the upstream commit log.
It is also worth watching for follow-on hardening work in adjacent netfilter paths. Once one namespace leak is fixed, maintainers often revisit similar dump code for the same class of mistake. That is how kernel hardening usually advances: one narrow correction at a time, each one making the next review slightly easier. The long-term trend is favorable, but only if administrators actually pull the fixes through their maintenance channels.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
nf_conntrack_expect, where the kernel could expose expectations from a different network namespace through procfs instead of limiting the dump to the current namespace. The published fix is narrowly framed — skip expectations that do not reside in this netns — but that restraint is exactly why it matters: it closes a cross-namespace information exposure path without rewriting the subsystem’s behavior. Microsoft’s Security Update Guide has already picked up the CVE, underscoring how Linux kernel issues now travel quickly through mixed-platform enterprise tooling even when Windows itself is not affected. ilter is one of the Linux kernel’s most consequential subsystems because it sits on the boundary between packet processing and system policy. Conntrack adds memory to that boundary by tracking flows over time, which is how Linux knows whether traffic is new, established, related, or expected. Expectations are the mechanism that lets the kernel anticipate follow-on traffic after a control connection or protocol negotiation, and that makes them central to helpers, NAT traversal, and a long tail of stateful networking features. The kernel documentation’s treatment of conntrack exposes just how deeply embedded this machinery is in the networking stack, including procfs-facing knobs and helper-related behavior.That matters because conntrack is not a niche feature reserved for firewall experts. It is part of the plumbing for home routers, enterprise gateways, container hosts, VPN endpoints, load balancers, and security appliances. When a bug lands in expectation handling, the issue may look minor in isolation, but the operational surface area can be broad. The CVE description here is not about packet parsing or memory corruption in the classic sense; it is about the kernel exposing state that belongs to another namespace, which is the sort of bug thaetween correctness and security.
Historically, the Linux networking maintainers have already dealt with a closely related problem in conntrack dumping. The CVE text explicitly points to the earlier change
e77e6ff502ea, which stopped /proc from dumping conntrack entries belonging to other namespaces. In other words, CVE-2026-31496 is not an isolated surprise; it is part of an ongoing cleanup of namespace boundaries inside netfilter. That pattern is familiar in kernel hardening: once one cross-namespace leak is closed, reviewers often discover a second path that reaches the same class of data throent object.The timing also tells a story. The CVE was published on April 22, 2026, and the public record already includes multiple stable-branch references from kernel.org, which strongly suggests the fix has been backported rather than left as a mainline-only correction. That is a practical signal to operators: this is not the sort of issue maintainers are waiting to “see if it matters.” They have already decided it matters enough to carry into suppo What the Vulnerability Actually Is
At its core, the flaw is a namespace isolation failure in a procfs dump path. The kernel should only report expectations that belong to the namespace being inspected, but the vulnerable logic could include expectations from other namespaces as well. In a modern Linux system, network namespaces are not cosmetic; they are an explicit isolation boundary used by containers, sandboxing stacks, and multi-tenant network setups. When proc output crosses that boundary, the bug becomes more than a bookkeeping mistake.
The worstructive: skip expectations that do not reside in this netns. That is a defensive rule, not a broad architectural change. It means the kernel does not try to infer intent or reconstruct ownership from adjacent state; it simply refuses to dump objects outside the current namespace. That is exactly the right posture for privileged metadata exposure, because it reduces the possibility that an inspection interface becomes a side channel.
 Why procfs matters here
Why procfs matters here
kernel’s oldest and most convenience-oriented user interfaces, which makes it deceptively risky. It is often treated as “just read-only text,” but it is still a kernel export surface, and any mistakes in object filtering become visible to userspace tools. In a networking stack, those tools may be debugging, monitoring, policy-validation, or orchestration components that assume each namespace is self-contained. If the dump crosses namespace lines, the result may be inaccurate operational data even when no crash occurs.This is why the issue has security significance even without an obvious exploit narrative. Information leakage in the kernel is rarely harmless; it can break tenant isolation, undermine observability assumptions, or reveal state that other processes were not meant to see. In container-heavy environments, that can be enough to justify a fix on its own. The vulnerability is narrow, but the trust boundary it touches is broad. cross-namespace visibility, not packet parsing.
- The affected path is procfs output, which is often consumed by tooling.
- The fix is to filter out expectations from other netns.
- The impact is strongest where namespace isolation is part of the security model.
How Conntrack Expectations Fit Into the Bigger Picture
Conntrack expectations are best understood as promises the kernel makes about future traffic. A helper that understands a protocol may observe an initial control flow and then register an expectation for a related flow that should be treated as part of the same session. This is useful for protocols that negotiate separate data channels or otherwise split control and payload behavior. The expectation object becomes a tiny piece of kernel memory that bridges what the system knows now and what it expects to see later.That bridge is alsdling is security-sensitive. If the kernel exposes expectations incorrectly, it can give userspace an incomplete or misleading map of active networking state. If it keeps the wrong expectations in view, policy tools may behave as though a flow exists where it does not, or as though a flow belongs to the wrong tenant. In a container platform, those mistakes are especially annoying because they look like ordinary debugging noise until they affect one workload consistently and another never.
Why namespace boundaries are so imppaces are one of Linux’s strongest isolation primitives because they let the kernel present each workload with a different view of interfaces, addresses, routes, conntrack state, and related metadata. When a proc dump leaks expectations across those boundaries, it weakens that promise in a way that is easy to underestimate. The problem is not just confidentiality; it is also correctness. A tool that reads the wrong namespace’s expectations may draw the wrong conclusion about routing behavior, helper configuration, or NAT state.
That is why the fix is so surgically phrased. It does not attempt to redesign conntrack expectation reporting. It simply restores the assumption that proc output is namespace-local. That kind of patch is typically low-risk to backport, because it tightens a boundary without changing the semantics of valid in-namnntrack expectations** model future related traffic.- Helpers derive those expectations from protocol behavior.
- Procfs dumps are administrative interfaces, not just diagnostics.
- Namespace isolation is part of the kernel’s security contract.
Why This Became a CVE
Not every kernel bug becomes a CVE, and not every CVE implies remote code execution. This one appears to have been assigned because it crosses a clear security boundary: procfs output is leaking or exposing information outside the namespace where it belongs. The description itself ties the issue to a known prior fix, which suggests maintainers recognized the bug as a variant of an already security-relevant namespace filtering problem. That pattern is common in kernel security work: once a family of leaks is discovered, adjacent code paths are reviewed and corrected as separate CVEs or follow-on fixes.The pu matters. NVD notes that the entry has recently been published and that enrichment is not yet complete, while the Microsoft advisory mirrors the CVE entry. That is typical of fresh kernel disclosures: the upstream technical fix appears first, downstream scoring and severity analysis lag behind, and enterprise visibility tools ingest the identifier before a final numeric rating is available. In practice, that means administrators should read the code-path description, not wait for the scorecard to settle.
Why “no score yet” is nA missing or pending CVSS score is not a sign that the bug is low risk. It usually means classification has not caught up to the public advisory. Kernel teams and stable maintainers often act on the technical evidence long before vulnerability databases finish enrichment, especially when the fix is small and the boundary is clear. The Linux kernel documentation also makes clear that supported fixes are backported to specific maintained release families, which is another strong indicator that the issue has been deemed production-relevant.
That is the operational takeaway: this is a patch management item, not a theoretical note for a future hardening sprint. If your fleet depends on Linux networking, you should care about whether your vendor kernel has already absorbed the fix. Upstream publication and downstream availability are not the same thing, and the gap between them is where exposure lives.- CVE assignment reflects a real boundary violation.
- NVD enrichment lag is normal for fresh kernel issues.
- Stable backports are the practical signal that matters.
- Vendor kernel status matters more than upstream commit presence.
The Stable-Backport Signal
The reference list attached to the CVE includes multiple kernel.org stable commits, which is a strong sign that the issue was deemed fit for long-term and production branches. That matters because most operators never run raw mainline kernels. They run distro builds, appliance firmware, or vendor-maintained kernels, and those inherit fixes only after the backport lands in the relevant maintenance stream. The stable process is not bureaucracy; it is how the Linux ecosystem turns an upstream patch into a deployable correction.This is also why support cadence matters more than headlines. A CVE with no score can still already be on the path to broad remediation if maintainers have shipped it into supported branches. Conversely, a neatly scored vulnerability can remain practically exposed for a long time if vendors lag in shipping the backport. In other words, the operational risk is governed less by the number attached to the bug and more by whether the fix has actually reached the kernel you boot.
What the references imply
The multiple commit references suggest the fix has already been staged across several maintained Linux branches rather than left as a one-off patch. That is usually a sign of confidence in the minimal scope of the change and the importance of restoring the boundary quickly. It also hints that downstream distributions have a clear path to integrate the fix witho subsystem churn.For administrators, the practical implication is simple: check vendor advisories, not just version numbers. A kernel can be “new enough” in terms of release date and still miss the backported commit if your distribution has not pulled it in yet. That is especially true in long-term-support environments where stability policies intentionally slow the flow of changes.
- Confirm whether your distribution has shipped the backport.
- Verify whether your workloads rely on conntrack helpers or proc-based inspection.
- Audit any container, firewall, or gateway stacks that depend on namespace isolation.
- Treat vendor kernel advisories as the source of truth, not the upstream commit alone.
Enterprise Impact
For enterprise users, the biggest question is not whether the bug is elegant; it is whether it breaks an assumption they rely on. In this case, the answer is yes. Any environment that treats network namespaces as a tenant boundary, a container security boundary, or an operational isolation layer has reason to care. A proc path that shows expectations from anad administrators, monitoring tools, or automation that expect clean separation.The operational downside is subtle but serious. If a fleet’s observability or debugging stack consumes conntrack expectation data, a cross-namespace dump can make two unrelated workloads appear coupled. That can waste incident-response time, confuse policy validation, and obscure the real source of a network problem. In security-sensitive environments, misleading state is often almost as dangerous as missing state.
Why this is especially relevant for container and cloud platforms
Containers and microservice platforms frequently use separate namespaces precisely to keep kernel-visible state scoped to each workload. When a networking tool leaks objects from outside the current namespace, it weakens that model in a place where automation depends on it. The larger the fleet, the more likely the effect is to become a troubleshooting tax rather than a dramatic outage, but the cumulative cost can still be high.There is also a compliance angle. If a namespace is supposed to represent a tenant boundary, then a proc export that reveals state from another tenant may create audit noise or even ponding on how the environment is built. That is why an issue like this can matter even without exploitation proof: the business risk is tied to integrity and isolation, not just to code execution.
- Container hosts are likely to feel this more than single-user desktops.
- Monitoring systems can misread the state if proc output is mixed.
- Tenant isolation assumptions are directly affected.
- Incident response can waste time chasing the wrong namespace.
Consumer Impact
Consumer impact is probably narrower, but not irrelevant. A typical desktop Linux installation may never exercise the affected proc path in a way that surfaces a problem, and most users do not live inside multiple network namespaces. Still, home routers, homelabs, custom firewall boxes, and small-office gateway systems often use Linux in exactly the kinds of network-control roles where conntrack and namespace semantics matter.That means the “consumer” label can be misleading. A user might think of a box as a personal machine while it quietly acts as a gateway for the whole house or office. In that scenario, a kernel bug in a networking dump path is not just a theoretical concern; it is part of the trust chain that keeps traffic segmentation and monitoring coherent. The fix remains worth applying even if the immediate day-to-day symptom is invisible.
Where consumer systems are most likely to be exposed
The most plausible exposure points are systems that do more than basic browsing and email. If the machine is running a firewall, a lab VM stime, or a network appliance workload, the bug becomes more relevant. If it is a stock laptop with minimal namespace use, the practical risk is lower, but a vendor update is still the right answer because kernel fixes rarely arrive in isolation.The broader lesson is that consumer-versus-enterprise distinctions in Linux are often about role, not device class. A small box can be the core of a home network, and a desktop can host lab workloads that mimic enterprise behavior. Security teams should treat the actual network role as the deciding factor, not the sticker on the hardware.
- Home gateways and lab routers deserve attention.
- Stock desktops are less likely to exercise the path.
- Custom firewall or container setups raise the relevance.
- Kernel updates should follow workload role, not device label.
Comparison With Other Netfilter Issues
Netfilter vulnerabilities often fall into familiar buckets: memory safety bugs, logasses, or information leaks. CVE-2026-31496 sits closest to the information-exposure family, but it is more precisely a namespace filtering failure. That distinction matters because it tells defenders what to look for in adjacent code: not malformed packets, but object ownership rules and dump-path scoping.This also helps explain why the fix is small. Whe boundary check, the remedy is usually to make the boundary check stricter. The kernel already knows how to identify the current namespace; the bug was that it failed to apply that knowledge consistently in expectation dumping. A broader rewrite would have been unnecessary and riskier.
Why subtle bugs linger longer
Subtle netfilter bugs often survive because they do not immediately look exploitable. A cross-namespace leak may not crash the system, and it may not even affect common consumer scenarios. But it can still be serious because it undermines the confidence users have in kernel-managed isolation. Those are exactly the kinds of flaws that tend to be rediscovered during cleanup or hardening passes rather than by dramatic failure.In that sense, CVE-2026-31496 is part of a recurring maintenance theme: fewer indirect lookups, fewer assumptions, and tighter ownership rules around what the kernel exposes to userspace. That is the kind of progress that rarely makes headlines but steadily improves the reliability of the Linux networking stack.
- The bug class is information exposure, not packet corruption.
- The remedy is a stricter namespace check.
- The pattern fits broader kernel hardening work.
- Subtle bugs often remain hidden until a cleanup pass finds them.
Administration and Patch Prioritization
The safest operational stance is to treat this as a routine but real kernel maintenance issue. The fix appears narrow, which is good news from a regression-risk standpoint, but kernel networking changes still deserve controlled rollout in production environments. If your environment relies on network namespaces for isolation, there is little reason to postpone once your vendor ships the backport.The best triage path is straightforward. First, determine whether the system uses conntrack expectations in a meaningful way. Second, identify whether
/proc or related tooling is used to inspect those expectations across namespaces. Third, verify whether the vendor kernel includes the stable backport. That sequence is boring, but boring is good when the bug is in infrastructure plumbing.Suggested triage steps
- Check the vendor kernel changelog for the specific CVE backport.
- Confirm whether your workloads use network namespaces for security or multi-tenancy.
- Review tooling that reads conntrack expectation data from procfs.
- Prioritize hosts that act as gateways, container nodes, or firewall appliances.
- Roll the update through a controlled maintenance window if the system is production-critical.
- Check distro backports first.
- Map the fix to actual subsystem use.
- Treat observability dependencies as exposure points.
- Use maintenance windows where service criticality demands it.
Strengths and Opportunities
The best thing about this fix is that it is precise. It dan abstract security problem in the whole networking stack; it blocks a specific cross-namespace leak in a specific dump path. That makes it easy for maintainers to audit, easy for vendors to backport, and easy for operators to understand. It also reflects a healthy kernel design principle: if an object does not belong to the current namespace, do not show it.There is also a broader opportunity here for better tooling discipline. Teams that depend on conntrack output can use this CVE as a reminder to verify that their observability stack is actually reading the namespace they think it is reading. In multi-tenant systems, silent boundary drift is often more dangerous than obvious failure, because it undermines trust before anyone notices.
- The fix is narrow and low-risk to backport.
- The affected path is easy to identify.
- The bug reinforces namespace hygiene.
- The patch improves trust in diagnostic output.
- The issue is a good prompt to audit proc-based tooling.
- Stable branches can absorb it without broad behavior changes.
- It supports a cleaner, more predictable **kerne## Risks and Concerns
Another concern is patch lag. Even after the fix is public, many fleets run vendor kernels that may not pick it up immediately, especially in appliance and long-term-support channels. That creates a window where the vulnerability is known but still present in the exact kernels that matter most. That lag is often where real exposure lives, not in the upstream commit log.
- Security teams may treat the issue as informational rather than actionable.
- Vendor backports can lag behind the upstream fix.
- Mixed fleets may have inconsistent exposure.
- Namespace leaks can confuse troubleshooting and monitoring.
- Procfs-driven tooling can mask the problem until it matters.
- Compliance-sensitive environments may care more than they first realize.
- The absence of a final score should not be mistaken for safety.
Looking Ahead
The key thing to watch next is how quickly the fix propagates into mainstream vendor kernels and long-term support builds. For most organizations, that will matter more than the upstream commit date itself, because the production kernel is what defines exposure. If your vendor has already shipped the backport, the risk should drop quickly; if not, the issue remains open regardless of how public the CVE already is.It is also worth watching for follow-on hardening work in adjacent netfilter paths. Once one namespace leak is fixed, maintainers often revisit similar dump code for the same class of mistake. That is how kernel hardening usually advances: one narrow correction at a time, each one making the next review slightly easier. The long-term trend is favorable, but only if administrators actually pull the fixes through their maintenance channels.
Things to monitor
- Vendor advisories naming the CVE explicitly.
- Backport notes for supported LTS kernels.
- Container and firewall appliances that bundle older kernels.
- Any subsequent netfilter fixes with similar namespace wording.
- Tooling updates that rely on conntrack expectation dumps.
- Changes in how enterprise vulnerability scanners classify the issue.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center