 Overview
Overview
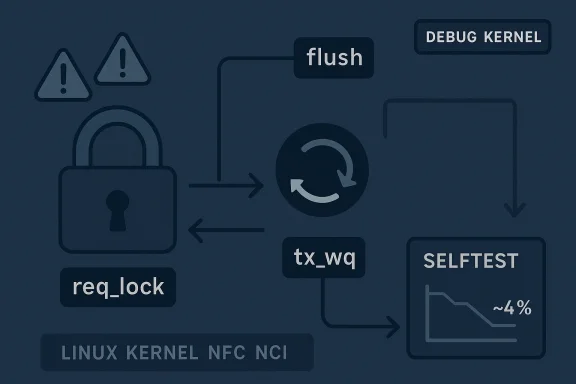
CVE-2026-31509 is a Linux kernel vulnerability in the NFC NCI path that was published on April 22, 2026, and quickly drew attention because the bug is not a flashy memory corruption issue but a locking-order failure with real stability implications. The upstream fix is narrowly scoped: move a workqueue flush out from under req_lock in nci_close_device so the close path no longer risks a circular dependency with nci_rx_work acquiring the same mutex later in the call chain lassic kernel concurrency bug: subtle, intermittent, and easy to underestimate until lockdep or selftests start screaming.The vulnerability was reported upstream by kernel.org and is already reflected in the NVD record and Microsoft’s advisory page, though NVD had not yet assigned a CVSS score at publication time. Kernel maintainers reproducible in the NCI selftest on a debug kernel, with the problem appearing in roughly 4% of runs, which is exactly the kind of flaky-but-real behavior that makes race bugs difficult to dismiss. In practical terms, this is less about rnd more about preserving kernel correctness in a subsystem where device teardown, workqueues, sockets, and target deactivation all overlap.
The important takeaway for administrators is that small-looking kernel fixes can still matter a great deal. NFC is not a headline subsystem for most server fleets, but concurrency bugs in close/shutdown logic can destabilize systems, complicate debugging, and expose latent ordering problems elsewhere. The fact that the fix is already in stable references means the remediation path is straightforward: confirm whether your vendor kernel has picked it up, and if not, treat it as a routine but important kernel update item.
Background
Linux kernel CVEs are often assigned once a feam or stable tree, and the kernel community has long documented that it tends to be deliberately cautious in classifying bug fixes that may have security relevance. That context matters here because CVE-2026-31509 is not the sort of issue that immediately suggests code execution. Instead, it is a concurrency flaw in a device-close path, which is exactly the kind of bug that can sit quietly until a sanitizer, lock validator, or stressful selftest exposes it.The NCI layer is part of the Linux NFC stack, and the close path is where the kernel has to unwind device state while background work may still be running. That is always a sensitive moment in kernel design because teardown paths have to coordinate the lifetime of workqueues, mutexes, protocol state, and transport state all at once. If the order is wrong, a thread that is “supposed” to be going away can still reach back into shared state and create a deadlock or an ordering cycle.
What makes CVE-2026-31509 especially interesting is the exact chain involved. According to the kernel.org description reproduced in the NVD entry,
nci_close_device flushes rx_wq and tx_wq while holding req_lock, but nci_rx_work can eventually call back into nci_request and try to lock that same mutex through a long socket and NFC teardown path. In other words, the problemous lock inversion at the top of the stack; it is a cascading dependency that emerges only when asynchronous work, socket cleanup, and target deactivation intersect.The kernel fix is therefore elegantly small. It releases
req_lock before flushing rx_wq, relying on the fact that NCI_UP has already been cleared and the transport is closed, so the work item should see the device as down and return -ENETDOWN instead of doing useful work. That is a good example of how kernel maintainersncy bugs: not by adding more locking, but by changing the sequence so the dangerous combination never exists in the first place.What the Bug Actually Is
At the heart of CVE-2026-31509 is a circular locking dependency.nci_close_device acquires req_lock and then waits for workqueues to drain. That sounds reasonable on the surface, because close paths often need to block until asynchronous processing is gone. But in this case the receive-side worker can reach a path that takes req_lock again, which means the close path can end up waiting for work that is itself waiting on the very mutex the closer is holding.That is the kind of deadlock pattern lockdep is built to catch. It m run, and it may never occur on a lightly loaded system, but once the dependency graph exists the kernel is relying on timing luck rather than correctness. The NVD description says NIPA had been hitting this while running the NCI selftest on a debug kernel at roughly a 4% hit rate, which is a strong sign that this is not a theoretical issue.
The dependency chain matters
The published chain is long, and that length is revealici_rx_data_packet -> nci_data_exchange_complete -> __sk_destruct -> rawsock_destruct -> nfc_deactivate_target -> nci_deactivate_target -> nci_request -> mutex_lock(&ndev->req_lock)` shows that the lock cycle is not confined to the NFC core alone. It crosses receive work, socket destruction, raw sockets, NFC deactivation, and request handling before finallyThat matters because the bug is not a simple “wrong lock order in one function” problem. It is a lifecycle bug in which one subsystem’s teardown semantics leak into another’s concurrency expectations. Those are the hardest kernel bugs to reason about because each individual function can look fine in isolation while the combined execution path is not.- The issue involves asynchronous workqueue teardown.
- The locking cycle spans multiple kernel subsystems.
- The problem can manifest only under certain timing conditions.
- The fix is sequencing, not redesign.
- Debug kernels and selftests are especially likely to surface it.
Why this is not just “a warning”
Kernel lockdep warnings can be easy to ignore if they appear only in test environments, but that would be a mistake here. A circular dependency in a close path usually means the system has a teardown sequence that is not robust under concurrency. Even if the most visible symptom is a warning, the same flaw can later become a hang or a difficult-to-reproduce outage.That is why the fix should be read as a correctness hardening measure with operational value. The kernel does not need to “almost” close the device safely; it needs to close it in a way that cannot back itself into a locked state. This patch moves the design closer to that goal.
Why the Fix Works
The fix described by kernel.org is simple: move the flush ofrx_wq until after req_lock has been released. This preserves the intent of nci_close_device—stop outstanding work before final teardown—without allowing the close path to holrker chain might need.That sequencing change is important because it avoids introducing a new lock acquisition order across the workqueue and socket teardown path. Instead of trying to prove that the worker can never reach
req_lock, the fix accepts that it can and prevents the closer from waiting while holding the lock. That is a healthier design, especially in code that already deals with asynchronous state transitions.Why the return value matters
The upstream note says the work should see thatNCI_UP has already been cleared and the transport is closed, then return -ENETDOWN. That is a subtle but important guarantee. The fix is not merely “let the work run later”; it depends on the work recognizing that the device is no longerafely.In practice, that makes the patch feel surgical rather than broad. The code is not rewriting the state model. It is relying on a pre-existing down state to make deferred work harmless once the lock is released.
Design lessons from the patch
This is one of those cases where a small patch teaches a larger lesson. The best concurrency fixes often remove an impossible assumption rather than add more synchronization. If a close path assumes that work queues are inert while a mutex is held, but reality says the work can re-enter the same state machine, then the close path has to be restructured.- Release locks before waiting on work that may need those locks.
- Treat teardown as part of the concurrency design, not an afterthought.
- Prefer state checks that force workers to exit cleanly.
- Avoid over-synchronizing during device shutdown.
- Use debug kernels and sanitizers to validate teardown ordering.
Impact on the Linux Kernel NFC Stack
The immediate impact is likely limited to systems that actually exercise the NFC NCI path, but that does not make the bug trivial. Kernel bugs in specialized subsystems still matter because they can be triggered by device attach/detach cycles, selftests, automated lab rigs, or distribution-level hardware validation. The fact that NIPA hit the issue in selftest suggests it is reachable in realistic test scenarios, not just in contrived lab conditions.For consumer desktops, the exposure may be low if NFC is not actively used. But low exposure does not mean no exposure, especially on laptops and embedded systems with integimity-based payment hardware, or device discovery features. If the device path exists and the kernel version predates the fix, the bug is part of the attack surface whether or not it is commonly exercised.
Enterprise and embedded implications
The enterprise story is more nuanced. Large fleets rarely think about NFC first, but laptops, ruggedized handhelds, kiosk devices, and point-of-sale systems can all use NFC stacks. If a teardown path can deadlock the kernel under load or during device removal, that becomes an operational issue, not just a code-quality problem.This is especially true in debug, test, and CI environments, where device plug/unplug and repeated close/open cycles are common. The bug may not bring down an entire production server farm, but it can absolutely waste engineering time, poison regression test results, and obscure real failures.
- More relevant to hardware-rich endpoints than to server-only fleets.
- More likely to show up in test labs and fuzzing environments.
- Potentially disruptive to automated device lifecycle testing.
- Important for embedded products that expose NFC hardware.
- Worth tracking even if the subsystem is not broadly deployed.
Reliability as a security concern
Kernel CVEs do not have to be remote code execution to matter. A deadlock in a device shutdown path can still be a security-relevant availability problem, especially if it occurs in a process that manages sensitive hardware or is difficult to recover remotely. In operational terms, a stuck kernel is often just as painful as a more dramatic bug.That is why this vulnerability belongs in the same patch management bucket as other kernel stability fixes. It is a reminder that concurrency bugs can be denial-of-service class problems even when they are not classic exploit primitives.
The Role of Workqueues and Mutexes
Workqueues are one of the Linux kernel’s essential tools for deferring work out of interrupt or event contexts, but they are also a common source of lifetime and ordering bugs. Once a function schedules or flushes a workqueue, the developer has to think very carefully about what locks are held, what objects are still live, and what other callbacks may run before the flush returns.In CVE-2026-31509, the dangerous combination was holding
req_lock while waiting for rx_wq and tx_wq to empty. The receive worker could still proceed far enough into the NFC deactivation path to need the same mutex, and that creates a dependency cycle that the kernel cannot resolve cleanly.Why this pattern recurs
This is not an NFC-only problem. It is a recurring kernel design issue wherever deferred work and teardown intersect. A close path wants to stop future work, but thel need to consult shared state to decide whether it should stop. If the closer holds a lock that the worker needs for that decision, the close path can accidentally freeze the system in the middle of cleanup.That is why lock ordering reviews are so valuable in kernel code. They force maintainers to reason about the sequence in which the system becomes quiescent, not merely whether the code compiles or passes basic tests.
Practical lessons for subsystem maintainers
For maintainers, the lesson is straightforward but important: flush work only when you are sure the work cannot re-enter a lock you still hold. If that cannot be guaranteed, move the flush later or change the state so workers will self-abort without needing to acquire the contested lock.- Audit close and unregister paths for flush-under-lock patterns.
- Map every callback that can be reached from deferred work.
- Check whether workers may re-enter teardown functions.
- Use lockdep on debug builds before shipping fixes.
- Prefer explicit “device is down” checks to speculative waiting.
Why the CVE Was Catchable
One reason this bug is reassuring, despite being a real problem, is that it was exposed by selftest and debug tooling. That means the kernel’s own validation ecosystem is doing what it is supposed to do: turn rare race conditions into reproducible signals before they become user-facing failures. The NVD note that NIPA was hitting this in roughly 4% of NCI selftest runs suggests a race that is elusive, but not invisible.That is exactly the sort of bug sanitizers, lock validators, and stress tests are meant to catch. It is also a reminder that “intermittent” is not synonymous with “harmless.” In kernel development, intermittent probes that matter most, because they point to real concurrency assumptions being violated.
Debug kernels tell the truth
Production builds often hide ordering issues simply because they lack the right instrumentation or because timing differs enough to avoid triggering the bug. Debug kernels and selftests remove some of that luck. They increase the chance that race windows and lock cycles become visible quickly.That does not mean the problem is only a test artifact. It means the issue has already survived long enough to be caught by a deliberately hostile environment, which is an excellent reason to trust the fix and push it downstream.
What this says about kernel quality
The broader lesson is encouraging: the Linux kernel’s development process is still catching subtle concurrency mistakes before they become widespread incidents. The fact that the problem was severe enough to become a CVE, yet narrow enough to be fixed with a sequencing change, is a sign of a mature maintenance ecosystem.- Instrumentation still matters in modern kernel development.
- Selftests can reveal bugs that ordinary workloads never will.
- Rare races are still real races.
- Fixes that simplify ordering are often the safest.
- Debug-only failures should never be dismissed out of hand.
Microsoft’s Advisory and the Patch Trail
Microsoft’s vulnerability guide includes CVE-2026-31509, reflecting the way Linux kernel security information now travels through a broader ecosystem than the upstream mailing lists alone. That matters because enterprises increasingly consume vulnerability intelligence through centralized security platforms, not by reading kernel patch notes directly. Even when the root cause is Linux-native, remediation workflows often run through vendor-specific advisories and update guides.The NVD entry notes that enrichment and scoring were not yet complete at publication time, which is common for fresh kernel CVEs. In practice, that means defenders should not wait for a polished severity label before tracking the fix. The upstream description is already precise enough to justify patch planning.
Why “no CVSS yet” does not mean “no urgency”
A m pass. Kernel vulnerabilities frequently move from disclosure to stable backports faster than scoring databases can fully enrich them, so the practical signal is the fix itself. Once a patch is in stable references and vendor advisories begin to appear, operators should treat the issue as real and trackable.That is especially true when the bug touches concurrency, because the impact is often operational rather than easily summarized in a single severity number. A hang, deadlock, or stuck teardown can be devastating even when no exploit primitive is obvious.
How organizations should read the advisory trail
The best approach is to treat Microsoft, NVD, and kernel.org as complementary rather than competing sources. Kernel.org tells you what was fixed. NVD helps with cataloging and downstream tracking. Microsoft’s guide helps the enterprise side map the issue into update workflows.- Track the upstream fix first.
- Verify vendor backports in your own kernel line.
- Use advisory pages for inventory and compliance mapping.
- Do not wait for a final CVSS score to begin triage.
- Treat stable references as the strongest signal of real-world relevance.
Strengths and Opportunities
The good news is that CVE-2026-31509 appears to be the kind of kernel issue that can be fixed cleanly and backported without major functional risk. That makes it ideal for stable maintenance, and it gives downstream vendors a straightforward path to ship the correction. It also reinforces a useful operational opportunity: organizations can use the CVE as a prompt to review broader NFC and device-teardown behavior in their fleets.- The patch is narrow and easy to reason about.
- The fix preserves intended shutdown semantics.
- The bug is reproducible enough to be actionable.
- Backporting should be comparatively low-risk.
- The CVE helps teams audit NFC-related lifecycle code.
- Debug and selftest coverage already caught the flaw.
- The issue is a strong reminder to review flush-under-lock patterns.
Risks and Concerns
The main concern is not that this bug is flashy, but that it is easy to ignore because it lives in a specialized subsystem. That is exactly how concurrency issues linger in codebases: the visible symptom is a warning or flaky test, while the underlying flaw can still become a hang under the right timing conditions. Another concern is that a close-path lock cycle can hide related bugs elsewhere in the same subsystem.- Specialized hardware paths are often under-tested in production.
- Intermittent failures can be misdiagnosed as test noise.
- Deadlocks in teardown paths can create hard-to-debug outages.
- Similar lock-order problems may exist nearby.
- Embedded and kiosk systems may be more exposed than desktop fleets.
- Vendor backport delays can leave mixed versions in the field.
- Users may assume NFC is irrelevant and miss the patch window.
What to Watch Next
The next thing to watch is how quickly downstream vendors incorporate the fix into supported Linux kernel lines. Because the upstream description is already precise and the change is small, this should not be a long-tail patch, but distribution latency still matters. The second thing to watch is whether maintainers find similar flush-under-lock patterns elsewhere in the NFC stack or in adjacent device teardown code.It will also be worth watching how the advisory gets classified once enrichment catches up. That may not change the technical reality, but it will affect enterprise prioritization workflows that depend on severity labels. In the meantime, the safest approach is to treat this as a real kernel maintenance item, not a theoretical one.
Key items to monitor
- Stable backports in supported kernel branches.
- Vendor advisories and distro patch notes.
- Any follow-on NFC concurrency fixes.
- Lockdep or selftest regressions in debug kernels.
- Enterprise inventory of systems with active NFC hardware.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center