CVE-2026-31551 is a medium-severity Linux kernel vulnerability that deserves attention not because it is flashy, remote, or wormable, but because it exposes how small concurrency mistakes in performance-sensitive networking code can still produce serious availability failures. The flaw sits in mac80211, the Linux wireless networking stack used by many Wi-Fi drivers, and involves an underflow in the handling of aql_disable, a debugfs-controlled switch tied to Airtime Queue Limits. For WindowsForum readers, the issue matters most in mixed Windows-Linux environments: WSL2, dual-boot laptops, Azure Linux workloads, Linux-based appliances, developer machines, and enterprise fleets that treat Linux kernels as invisible plumbing until they crash.
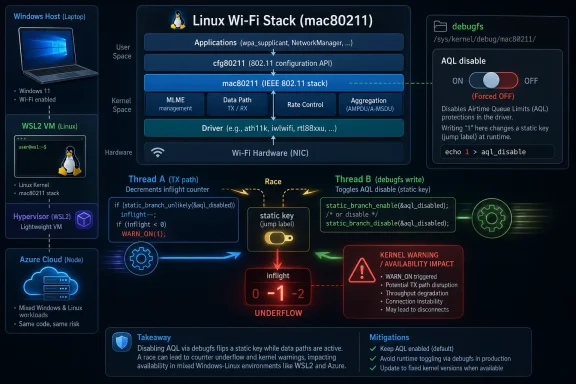
CVE-2026-31551 was published after kernel maintainers resolved a bug in the Linux Wi-Fi subsystem where concurrent writes to a debugfs control path could race against each other. The vulnerable function, aql_enable_write(), checked the state of a static key and later attempted to increment or decrement that key, but the state could change between the check and the update. That created the possibility of a static_branch_dec() underflow, triggering a kernel warning and potentially causing a denial-of-service condition.
The immediate trigger was found by syzbot, the automated fuzzing infrastructure that continuously batters Linux kernel interfaces looking for crashes, warnings, memory bugs, and concurrency failures. The trace associated with the report shows the failure inside the kernel jump label machinery, not in a traditional packet parser or Wi-Fi frame handler. That makes this CVE less about hostile radio traffic and more about the safety of writable kernel control surfaces.
The fix is conceptually simple: stop treating this switch as a reference-counted toggle. Instead of calling static_branch_inc() and static_branch_dec(), the patched code uses static_branch_enable() and static_branch_disable(), which better match the binary nature of the setting. That is the kind of patch that looks obvious after the fact, but only after fuzzing exposes the timing window.
This is not a Windows kernel vulnerability, and ordinary Windows users should not read it as a Wi-Fi emergency on Windows 11. Still, Microsoft tracks the CVE because Microsoft ships and supports Linux-based components and services, including Azure Linux and the Windows Subsystem for Linux ecosystem. In 2026, Linux kernel security is no longer a topic outside the Windows world; it is part of the same operational reality.
The result was not data theft or privilege escalation in the usual sense. Instead, the kernel could hit a warning path because the reference count behind the static branch was decremented below zero. In low-level kernel code, that kind of accounting error is not cosmetic; it signals that internal state has become inconsistent.
A simplified way to view the failure is this:
The CVSS 3.1 score is 5.5 Medium, with local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. That profile tells administrators something useful: the likely consequence is system disruption rather than data compromise. Medium does not mean ignorable when the affected asset is a laptop fleet, wireless gateway, lab host, or production Linux node.
Because mac80211 sits between drivers and the broader networking stack, bugs there can have wide reach. A flaw in a single vendor driver may affect one chipset family, but a flaw in shared mac80211 logic can touch many devices indirectly. That breadth is why even a local debugfs-triggered issue receives careful attention.
Airtime Queue Limits, or AQL, were introduced to improve Wi-Fi scheduling behavior by accounting for airtime rather than treating all queued packets as equal. Wi-Fi is a shared medium, so the cost of a packet is not just its size in bytes; it also depends on data rate, retries, contention, and transmission time. AQL helps prevent excessive buffering and improves latency, especially in congested environments.
AQL is significant because modern Wi-Fi performance is not only about maximum throughput. Users notice video call jitter, gaming latency, roaming behavior, and responsiveness under load. Queue management improvements in mac80211 directly affect the experience of Linux desktops, access points, test rigs, and embedded wireless products.
That optimization is powerful, but it demands correct lifecycle management. A reference-counted static branch is appropriate when multiple independent users may enable a feature and each must later release it. A simple on/off setting, however, should not pretend to be a reference counter unless the surrounding locking and ownership model justifies it.
Important takeaways include:
For many consumer systems, the exploitability question hinges on debugfs. Debugfs is usually mounted at /sys/kernel/debug, and by default its root is generally restricted to root. That matters because a bug behind a root-only debug interface is very different from one reachable by untrusted Wi-Fi packets or an ordinary website.
However, local-only does not mean harmless. In real environments, local access may come from shell users, misconfigured containers, CI jobs, developer scripts, system tuning tools, or compromised low-privilege accounts. Once a machine hosts multiple users or automated workloads, availability bugs become security bugs.
The vulnerability is best understood as a denial-of-service risk. It does not appear to provide a direct route to read secrets or modify protected data. But kernel crashes and warnings can still interrupt work, corrupt test results, trigger failovers, and create operational noise.
It is also not a Windows Wi-Fi driver flaw. Windows uses its own networking and driver model, and mac80211 is part of the Linux kernel. Windows users encounter the issue only where Linux kernels are present: WSL2, Linux virtual machines, dual-boot installations, cloud workloads, appliances, or developer hardware.
A quick triage summary:
Those ranges are unusually broad to casual readers, but not surprising for a subsystem bug that was introduced upstream and later carried through multiple supported branches. Linux stable maintenance is a living backport operation. A small upstream fix may need separate commits for each supported series because code around the fix evolves over time.
The presence of several kernel.org stable patch references indicates that the fix was backported, not merely landed in one development tree. That is important for administrators because most production systems do not run mainline kernels directly. They run vendor kernels derived from Ubuntu, Debian, Red Hat, SUSE, Amazon Linux, Azure Linux, or appliance-specific trees.
A practical verification sequence looks like this:
The most obvious Windows-adjacent surface is WSL2, which runs a real Linux kernel inside a lightweight virtual machine. Microsoft maintains a WSL2 Linux kernel source tree and delivers kernel updates on a cadence separate from core Windows updates. Users who build custom WSL kernels, pin older releases, or rely on enterprise update rings should pay attention to the exact kernel they are running.
The practical risk for WSL2 users is narrower than for a Linux laptop with active Wi-Fi hardware. WSL2 does not normally expose a physical Wi-Fi mac80211 device in the same way a native Linux installation does. Still, the presence of Linux kernel code in Windows workflows means administrators should not dismiss Linux CVEs simply because the endpoint fleet is Windows-branded.
For WindowsForum readers who run Hyper-V labs, WSL2 development stacks, Docker Desktop backends, Linux VMs, or dual-boot gaming rigs, the message is straightforward: Windows and Linux security boundaries increasingly overlap at the operational layer. You may not be patching the Windows kernel for this CVE, but you may still be patching a Linux kernel on a Windows-managed machine.
Key Windows-adjacent exposure points include:
On hardened servers, debugfs may be unmounted or inaccessible to non-root users. On lab systems, it may be mounted frequently for tracing, driver debugging, or performance analysis. On embedded platforms, vendors sometimes expose debug hooks during development and forget to fully disable them in production images. Configuration decides exploitability.
Security teams should coordinate with endpoint engineering and Linux platform owners. This CVE crosses traditional silos because it involves a wireless subsystem, a debug filesystem, kernel static keys, and vendor patch cadence. A scanner finding is only the start of the conversation.
Recommended enterprise actions:
Kernel updates still require care because wireless regressions are disruptive. Linux Wi-Fi stacks vary by chipset, firmware version, regulatory domain, power management behavior, and distribution patch set. Testing should include suspend/resume, roaming, VPN usage, captive portals, high-throughput transfers, and latency-sensitive applications.
A balanced rollout plan should include pilot groups, hardware diversity, rollback options, and clear reboot messaging. Kernel fixes do not help systems that install updates but continue running the old kernel for weeks. In vulnerability management, pending reboot debt is often the quiet failure mode.
SteamOS-like handhelds, home servers with wireless adapters, and Linux laptops used for development may all carry mac80211 code. Whether the vulnerable debug path is reachable depends on configuration and permissions. Most users will be protected simply by installing their distribution’s next kernel update and rebooting.
The bug is also a reminder that kernel version chasing cuts both ways. Newer kernels bring better hardware support, performance work, and driver fixes, but they also move fast enough that subtle regressions and security bugs can appear. Stable distribution kernels exist because someone needs to absorb that churn and backport fixes coherently.
Consumer guidance is simple:
At the same time, enthusiasts often run unusual configurations. They mount debugfs, test experimental kernels, compile driver branches, run fuzzers, and grant broad sudo access to scripts. Those habits are useful for learning and development, but they increase exposure to bugs that mainstream desktop users may never encounter.
The right response is neither complacency nor alarm. Patch, reboot, and keep debug interfaces locked down. That is enough for most systems.
This is a recurring pattern in systems engineering. Developers reach for a familiar primitive because it works under normal sequencing, but concurrency exposes the difference between “works in one thread” and “is correct under all interleavings.” The fix does not merely paper over the warning; it changes the primitive to match the intended state model.
The case also demonstrates the value of fuzzing. Human reviewers are good at design intent, but fuzzers are relentless at violating assumptions. syzbot found a path where concurrent writes could trigger a condition that ordinary testing might never hit. That is exactly why automated kernel fuzzing has become a core part of modern Linux hardening.
Engineering lessons include:
But the mechanism works by changing branch behavior at runtime, often with architecture-specific patching underneath. That makes state correctness critical. When a static branch is reference-counted, every increment must be matched by a decrement. When that balance breaks, the kernel rightly complains.
This is not a reason to avoid static keys. It is a reason to reserve reference-counted static branch operations for cases that genuinely require multiple independent holders. In all other cases, explicit enable and disable calls are safer and clearer.
CVE-2026-31551 illustrates the upside of that model. Without a CVE, the fix might look like just another stable patch buried among hundreds of updates. With a CVE, enterprises can track it, correlate it across vendors, and prove remediation. The downside is that teams need enough kernel literacy to avoid treating every Linux CVE as equally catastrophic.
The supply-chain path is layered. Upstream Linux accepts a fix, stable maintainers backport it, distributions integrate it, cloud vendors validate it, endpoint tools detect it, and administrators reboot into it. Any break in that chain creates lag.
This is especially relevant for Microsoft-related Linux environments. WSL2 kernels, Azure Linux kernels, and container host kernels may follow Microsoft-specific release channels. Administrators should verify against the vendor’s actual package metadata and release notes, not only against generic CPE entries.
A good vulnerability program should maintain:
The more strategic issue is how organizations classify Linux kernel vulnerabilities in Windows-centered environments. WSL2, Hyper-V Linux guests, developer containers, Azure Linux components, and dual-boot workstations blur old boundaries. A Windows endpoint can host multiple Linux security contexts, and each may have a different update path.
Watch these areas over the next few weeks:
CVE-2026-31551 is not a reason to fear Wi-Fi on Linux, and it is not a reason for Windows users to panic. It is a precise reminder that small concurrency bugs in low-level control paths can become real availability vulnerabilities, especially when debug interfaces are exposed and kernel updates lag. The best response is disciplined rather than dramatic: verify affected kernels, restrict debugfs, apply vendor patches, reboot promptly, and treat Linux components in Windows-era infrastructure as first-class citizens in the security program.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-31551 was published after kernel maintainers resolved a bug in the Linux Wi-Fi subsystem where concurrent writes to a debugfs control path could race against each other. The vulnerable function, aql_enable_write(), checked the state of a static key and later attempted to increment or decrement that key, but the state could change between the check and the update. That created the possibility of a static_branch_dec() underflow, triggering a kernel warning and potentially causing a denial-of-service condition.The immediate trigger was found by syzbot, the automated fuzzing infrastructure that continuously batters Linux kernel interfaces looking for crashes, warnings, memory bugs, and concurrency failures. The trace associated with the report shows the failure inside the kernel jump label machinery, not in a traditional packet parser or Wi-Fi frame handler. That makes this CVE less about hostile radio traffic and more about the safety of writable kernel control surfaces.
The fix is conceptually simple: stop treating this switch as a reference-counted toggle. Instead of calling static_branch_inc() and static_branch_dec(), the patched code uses static_branch_enable() and static_branch_disable(), which better match the binary nature of the setting. That is the kind of patch that looks obvious after the fact, but only after fuzzing exposes the timing window.
This is not a Windows kernel vulnerability, and ordinary Windows users should not read it as a Wi-Fi emergency on Windows 11. Still, Microsoft tracks the CVE because Microsoft ships and supports Linux-based components and services, including Azure Linux and the Windows Subsystem for Linux ecosystem. In 2026, Linux kernel security is no longer a topic outside the Windows world; it is part of the same operational reality.
The Bug in Plain English
A race in a debug control path
At the heart of CVE-2026-31551 is a classic time-of-check to time-of-use problem. The vulnerable code checked whether the aql_disable static key appeared to be false, then later performed an increment or decrement based on that earlier observation. With multiple writers hitting the same debugfs file at the same time, that assumption could become stale before the update happened.The result was not data theft or privilege escalation in the usual sense. Instead, the kernel could hit a warning path because the reference count behind the static branch was decremented below zero. In low-level kernel code, that kind of accounting error is not cosmetic; it signals that internal state has become inconsistent.
A simplified way to view the failure is this:
- Thread A checks the static key state.
- Thread B changes the static key state before Thread A updates it.
- Thread A proceeds using an outdated assumption.
- The decrement path runs when the counter is already zero.
- The kernel detects the underflow and emits a warning.
Why underflow matters
An integer underflow occurs when a value is reduced below its minimum valid range. In this case, the practical concern is not a neat arithmetic wraparound exploit chain, but a kernel integrity failure in a sensitive subsystem. The National Vulnerability Database maps the issue to CWE-191, which is the weakness category for integer underflow and wraparound.The CVSS 3.1 score is 5.5 Medium, with local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. That profile tells administrators something useful: the likely consequence is system disruption rather than data compromise. Medium does not mean ignorable when the affected asset is a laptop fleet, wireless gateway, lab host, or production Linux node.
Why mac80211 and AQL Matter
The Wi-Fi stack below the desktop
The Linux mac80211 subsystem is a central framework for software-based 802.11 wireless networking. Many Wi-Fi drivers rely on it for common behavior instead of implementing every wireless management and data-path feature on their own. That common layer is one reason Linux can support such a wide variety of wireless chipsets, from Intel laptop adapters to embedded boards and USB dongles.Because mac80211 sits between drivers and the broader networking stack, bugs there can have wide reach. A flaw in a single vendor driver may affect one chipset family, but a flaw in shared mac80211 logic can touch many devices indirectly. That breadth is why even a local debugfs-triggered issue receives careful attention.
Airtime Queue Limits, or AQL, were introduced to improve Wi-Fi scheduling behavior by accounting for airtime rather than treating all queued packets as equal. Wi-Fi is a shared medium, so the cost of a packet is not just its size in bytes; it also depends on data rate, retries, contention, and transmission time. AQL helps prevent excessive buffering and improves latency, especially in congested environments.
AQL is significant because modern Wi-Fi performance is not only about maximum throughput. Users notice video call jitter, gaming latency, roaming behavior, and responsiveness under load. Queue management improvements in mac80211 directly affect the experience of Linux desktops, access points, test rigs, and embedded wireless products.
The performance-security tradeoff
Static branches exist because kernel developers need very fast paths. Wireless networking is one of those places where extra condition checks can add up, especially when packets are flowing at high rates. Static keys allow rarely changed features or modes to be patched into efficient branch behavior at runtime.That optimization is powerful, but it demands correct lifecycle management. A reference-counted static branch is appropriate when multiple independent users may enable a feature and each must later release it. A simple on/off setting, however, should not pretend to be a reference counter unless the surrounding locking and ownership model justifies it.
Important takeaways include:
- mac80211 is shared infrastructure, not a niche driver.
- AQL affects latency and fairness in real Wi-Fi workloads.
- debugfs controls can influence live kernel behavior.
- static keys optimize fast paths but complicate state management.
- concurrency bugs often appear only under fuzzing or stress.
Severity and Exploitability
Medium severity, high availability impact
The CVSS vector assigned by NVD is useful because it avoids overhyping the bug. AV:L means an attacker needs local access. PR:L means low privileges are required. UI:N means no user interaction is necessary once the attacker has the needed local capability. The high availability impact reflects the possibility of triggering a kernel warning or instability.For many consumer systems, the exploitability question hinges on debugfs. Debugfs is usually mounted at /sys/kernel/debug, and by default its root is generally restricted to root. That matters because a bug behind a root-only debug interface is very different from one reachable by untrusted Wi-Fi packets or an ordinary website.
However, local-only does not mean harmless. In real environments, local access may come from shell users, misconfigured containers, CI jobs, developer scripts, system tuning tools, or compromised low-privilege accounts. Once a machine hosts multiple users or automated workloads, availability bugs become security bugs.
The vulnerability is best understood as a denial-of-service risk. It does not appear to provide a direct route to read secrets or modify protected data. But kernel crashes and warnings can still interrupt work, corrupt test results, trigger failovers, and create operational noise.
What it is not
This CVE is not a remote Wi-Fi takeover. It is not evidence that nearby attackers can crash any Linux laptop simply by transmitting crafted frames. The trace points to debugfs write handling, not over-the-air packet processing.It is also not a Windows Wi-Fi driver flaw. Windows uses its own networking and driver model, and mac80211 is part of the Linux kernel. Windows users encounter the issue only where Linux kernels are present: WSL2, Linux virtual machines, dual-boot installations, cloud workloads, appliances, or developer hardware.
A quick triage summary:
- Remote network attack: not indicated by the public record.
- Local denial of service: plausible under affected configurations.
- Privilege escalation: not the stated impact.
- Data theft: not the stated impact.
- Windows kernel exposure: not applicable.
- Linux kernel exposure: relevant across affected stable lines.
Affected Kernel Lines and Patch Status
Broad backports across stable branches
The affected kernel ranges listed by NVD span several Linux stable families, including older 5.x lines and multiple 6.x branches. The vulnerable configurations include kernel 5.12, versions from 5.12.1 before 5.15.203, versions from 5.16 before 6.1.167, versions from 6.2 before 6.6.130, versions from 6.7 before 6.12.78, versions from 6.13 before 6.18.20, and versions from 6.19 before 6.19.10. NVD also lists Linux 7.0 release candidates rc1 through rc7.Those ranges are unusually broad to casual readers, but not surprising for a subsystem bug that was introduced upstream and later carried through multiple supported branches. Linux stable maintenance is a living backport operation. A small upstream fix may need separate commits for each supported series because code around the fix evolves over time.
The presence of several kernel.org stable patch references indicates that the fix was backported, not merely landed in one development tree. That is important for administrators because most production systems do not run mainline kernels directly. They run vendor kernels derived from Ubuntu, Debian, Red Hat, SUSE, Amazon Linux, Azure Linux, or appliance-specific trees.
How administrators should verify
Version numbers alone can mislead because distribution kernels often carry backported security fixes without changing to the exact upstream version that appears in a generic CPE range. A Red Hat, Ubuntu, SUSE, Debian, or Microsoft-flavored kernel may report a version that looks vulnerable while already containing the relevant patch. Conversely, a custom or mainline build may need direct inspection.A practical verification sequence looks like this:
- Identify the running kernel with the system’s standard kernel version tools.
- Check whether debugfs is mounted and who can write to the relevant mac80211 path.
- Review the distribution’s security advisory, not just the upstream version range.
- Confirm whether the patch replacing inc/dec behavior with enable/disable behavior is present.
- Schedule kernel updates and reboots where live patching does not cover the change.
The Windows and Microsoft Angle
Why this appears in Microsoft security tracking
The Microsoft Security Response Center tracks CVEs that may affect Microsoft products, services, dependencies, or supported open-source components. That includes Linux-related vulnerabilities where Microsoft ships, builds, hosts, or consumes Linux kernels. In 2026, Microsoft is not merely a Windows vendor; it is also a major Linux distributor, cloud operator, and open-source supply-chain participant.The most obvious Windows-adjacent surface is WSL2, which runs a real Linux kernel inside a lightweight virtual machine. Microsoft maintains a WSL2 Linux kernel source tree and delivers kernel updates on a cadence separate from core Windows updates. Users who build custom WSL kernels, pin older releases, or rely on enterprise update rings should pay attention to the exact kernel they are running.
The practical risk for WSL2 users is narrower than for a Linux laptop with active Wi-Fi hardware. WSL2 does not normally expose a physical Wi-Fi mac80211 device in the same way a native Linux installation does. Still, the presence of Linux kernel code in Windows workflows means administrators should not dismiss Linux CVEs simply because the endpoint fleet is Windows-branded.
Azure Linux and hybrid estates
Azure Linux, formerly associated with CBL-Mariner lineage, further expands the relevance. Microsoft services, containers, host components, and appliances may include Linux kernels or Linux-derived packages. CVE tracking across those components is essential for cloud compliance and for customers who need to map third-party CVEs into Microsoft-supported environments.For WindowsForum readers who run Hyper-V labs, WSL2 development stacks, Docker Desktop backends, Linux VMs, or dual-boot gaming rigs, the message is straightforward: Windows and Linux security boundaries increasingly overlap at the operational layer. You may not be patching the Windows kernel for this CVE, but you may still be patching a Linux kernel on a Windows-managed machine.
Key Windows-adjacent exposure points include:
- WSL2 kernels maintained or customized outside normal update channels.
- Linux virtual machines running under Hyper-V or other Windows-hosted hypervisors.
- Dual-boot systems where Linux has direct Wi-Fi hardware access.
- Docker and Kubernetes development environments using Linux backends.
- Azure Linux workloads managed by Microsoft or enterprise platform teams.
- Security scanners that surface Linux CVEs on Windows developer endpoints.
Enterprise Response
Prioritize based on reachability
Enterprises should not rank CVE-2026-31551 solely by its medium CVSS score. They should rank it by where affected kernels exist, whether debugfs is mounted, whether untrusted local users exist, and whether Wi-Fi-capable Linux systems are mission-critical. A developer laptop has a different risk profile from a shared research workstation, and both differ from an embedded access-point appliance.On hardened servers, debugfs may be unmounted or inaccessible to non-root users. On lab systems, it may be mounted frequently for tracing, driver debugging, or performance analysis. On embedded platforms, vendors sometimes expose debug hooks during development and forget to fully disable them in production images. Configuration decides exploitability.
Security teams should coordinate with endpoint engineering and Linux platform owners. This CVE crosses traditional silos because it involves a wireless subsystem, a debug filesystem, kernel static keys, and vendor patch cadence. A scanner finding is only the start of the conversation.
Recommended enterprise actions:
- Inventory Linux kernels across servers, laptops, VMs, containers hosts, appliances, and WSL2 installations.
- Map kernel versions to vendor advisories instead of relying only on generic upstream ranges.
- Check debugfs exposure and restrict access where debugging is not required.
- Update affected kernels through supported distribution channels.
- Reboot systems after kernel updates unless a verified live patch covers the issue.
- Review custom kernels used by engineering, security research, or embedded teams.
- Document exceptions for systems that cannot be patched immediately.
Patch operations without drama
This is the kind of vulnerability that rewards steady operational hygiene. Most organizations should handle it through standard kernel update processes, not emergency overnight maintenance. The high availability impact justifies timely action, but the local attack vector gives teams room to stage testing.Kernel updates still require care because wireless regressions are disruptive. Linux Wi-Fi stacks vary by chipset, firmware version, regulatory domain, power management behavior, and distribution patch set. Testing should include suspend/resume, roaming, VPN usage, captive portals, high-throughput transfers, and latency-sensitive applications.
A balanced rollout plan should include pilot groups, hardware diversity, rollback options, and clear reboot messaging. Kernel fixes do not help systems that install updates but continue running the old kernel for weeks. In vulnerability management, pending reboot debt is often the quiet failure mode.
Consumer and Enthusiast Impact
Linux laptops, SteamOS-style devices, and dual-boot rigs
For home users, the most relevant affected systems are native Linux installations with Wi-Fi hardware, especially rolling-release distributions, custom kernels, or long-lived LTS systems awaiting updates. Dual-boot users may see the CVE in vulnerability feeds and wonder whether Windows is affected. The short answer is no for Windows itself, but yes for the Linux side if it runs an affected kernel.SteamOS-like handhelds, home servers with wireless adapters, and Linux laptops used for development may all carry mac80211 code. Whether the vulnerable debug path is reachable depends on configuration and permissions. Most users will be protected simply by installing their distribution’s next kernel update and rebooting.
The bug is also a reminder that kernel version chasing cuts both ways. Newer kernels bring better hardware support, performance work, and driver fixes, but they also move fast enough that subtle regressions and security bugs can appear. Stable distribution kernels exist because someone needs to absorb that churn and backport fixes coherently.
Consumer guidance is simple:
- Install kernel updates from your Linux distribution.
- Reboot after updating so the fixed kernel actually runs.
- Avoid custom debugfs permissions unless you understand the consequences.
- Do not assume mainline equals safer without checking patch status.
- Keep firmware packages current because Wi-Fi behavior often depends on both kernel and firmware.
- Check WSL separately if you use custom WSL2 kernels on Windows.
Why ordinary users should not panic
There is no public indication that CVE-2026-31551 enables drive-by compromise from a malicious access point. A user browsing from a coffee-shop Wi-Fi network is not facing the same kind of risk as a remote code execution flaw in a browser or a remotely reachable network daemon. That context matters.At the same time, enthusiasts often run unusual configurations. They mount debugfs, test experimental kernels, compile driver branches, run fuzzers, and grant broad sudo access to scripts. Those habits are useful for learning and development, but they increase exposure to bugs that mainstream desktop users may never encounter.
The right response is neither complacency nor alarm. Patch, reboot, and keep debug interfaces locked down. That is enough for most systems.
Lessons for Kernel Engineering
Small API mismatches create real bugs
The most interesting part of CVE-2026-31551 is the mismatch between the semantic need and the API originally used. The aql_disable control did not need reference-count tracking. It needed a binary enable or disable operation. By using increment and decrement operations, the code inherited failure modes that did not match the problem.This is a recurring pattern in systems engineering. Developers reach for a familiar primitive because it works under normal sequencing, but concurrency exposes the difference between “works in one thread” and “is correct under all interleavings.” The fix does not merely paper over the warning; it changes the primitive to match the intended state model.
The case also demonstrates the value of fuzzing. Human reviewers are good at design intent, but fuzzers are relentless at violating assumptions. syzbot found a path where concurrent writes could trigger a condition that ordinary testing might never hit. That is exactly why automated kernel fuzzing has become a core part of modern Linux hardening.
Engineering lessons include:
- Use binary APIs for binary state when reference counting is unnecessary.
- Serialize writable control paths when state transitions are not atomic.
- Treat debugfs writes as hostile input even if the interface is developer-facing.
- Prefer semantic clarity over clever reuse of low-level primitives.
- Expect fuzzers to find timing windows that humans miss.
- Backport simple fixes broadly when shared subsystems are involved.
Static keys are powerful but sharp
Static keys and jump labels exist to make rarely used branches nearly free in hot code paths. They are especially valuable in tracing, debugging, scheduling, networking, and other areas where a single conditional can appear in a path executed millions of times per second. Performance wins at that level can matter.But the mechanism works by changing branch behavior at runtime, often with architecture-specific patching underneath. That makes state correctness critical. When a static branch is reference-counted, every increment must be matched by a decrement. When that balance breaks, the kernel rightly complains.
This is not a reason to avoid static keys. It is a reason to reserve reference-counted static branch operations for cases that genuinely require multiple independent holders. In all other cases, explicit enable and disable calls are safer and clearer.
Supply Chain and Disclosure Dynamics
Kernel CVEs now arrive in volume
Linux kernel CVE handling has changed significantly in recent years, with many resolved kernel bugs receiving CVE identifiers. That has improved visibility, but it has also increased noise for security teams. A medium-severity local denial-of-service flaw may now appear alongside much more urgent vulnerabilities in dashboards and ticket queues.CVE-2026-31551 illustrates the upside of that model. Without a CVE, the fix might look like just another stable patch buried among hundreds of updates. With a CVE, enterprises can track it, correlate it across vendors, and prove remediation. The downside is that teams need enough kernel literacy to avoid treating every Linux CVE as equally catastrophic.
The supply-chain path is layered. Upstream Linux accepts a fix, stable maintainers backport it, distributions integrate it, cloud vendors validate it, endpoint tools detect it, and administrators reboot into it. Any break in that chain creates lag.
Vendor kernels complicate simple answers
Distribution kernels are not pure upstream kernels. They carry backports, vendor patches, configuration differences, driver enablement, and sometimes long-term support changes that do not map neatly to public version ranges. That is why a scanner can report a vulnerable kernel version while the vendor says the fix is already applied.This is especially relevant for Microsoft-related Linux environments. WSL2 kernels, Azure Linux kernels, and container host kernels may follow Microsoft-specific release channels. Administrators should verify against the vendor’s actual package metadata and release notes, not only against generic CPE entries.
A good vulnerability program should maintain:
- Kernel provenance for each environment.
- Vendor advisory mappings for distribution-specific fixes.
- Reboot compliance reporting after kernel updates.
- Exception tracking for pinned or custom kernels.
- Configuration checks for debugfs and local access exposure.
- Owner accountability for lab and developer systems.
Strengths and Opportunities
CVE-2026-31551 is a useful example of the Linux security ecosystem working as intended: fuzzing found a subtle concurrency bug, maintainers produced a targeted patch, stable trees received backports, and vulnerability databases gave administrators a common identifier. The opportunity now is to use this incident to tighten kernel inventory, reduce debugfs exposure, and improve patch verification across Windows-Linux hybrid environments.- Automated fuzzing proved its value by uncovering a race that routine testing could miss.
- The patch is conceptually clean because it replaces reference counting with explicit enable and disable semantics.
- The impact is well bounded compared with remote code execution or credential theft flaws.
- Stable backports are available across multiple kernel families, reducing the need for risky manual fixes.
- Enterprises can improve inventory discipline by tracing where Linux kernels actually run.
- Windows teams get a timely reminder that WSL2 and Azure Linux belong in vulnerability management.
- Debugfs hardening is a practical win that can reduce exposure beyond this single CVE.
Risks and Concerns
The main risk is not that CVE-2026-31551 becomes the next internet-scale exploit. The greater concern is operational: affected kernels may sit unnoticed on developer machines, lab systems, appliances, or custom WSL2 builds because teams assume Linux kernel patching belongs to someone else. That assumption is increasingly dangerous in hybrid Windows estates.- Debugfs may be mounted unnecessarily on systems that do not need active kernel debugging.
- Custom kernels may lag behind vendor-maintained security updates.
- Scanner results may be misread when vendor backports do not change visible version numbers.
- Pending reboots may leave systems vulnerable even after packages are installed.
- Embedded devices may depend on stale kernels that are harder to update quickly.
- Shared Linux workstations may expose local DoS paths to multiple users.
- Patch fatigue may cause teams to ignore medium CVEs that still carry high availability impact.
Looking Ahead
What to Watch Next
The next phase is vendor clarification. Distribution maintainers and Microsoft-adjacent channels will continue mapping the upstream fix into their own package streams, advisories, and release notes. Security teams should watch for whether their scanners update detection logic to account for backported fixes rather than relying only on broad version ranges.The more strategic issue is how organizations classify Linux kernel vulnerabilities in Windows-centered environments. WSL2, Hyper-V Linux guests, developer containers, Azure Linux components, and dual-boot workstations blur old boundaries. A Windows endpoint can host multiple Linux security contexts, and each may have a different update path.
Watch these areas over the next few weeks:
- Distribution advisories confirming fixed kernel package versions.
- Microsoft guidance for Azure Linux and WSL2-related exposure.
- Scanner plugin updates that distinguish fixed backports from vulnerable versions.
- Enterprise reboot compliance after kernel patch deployment.
- Additional syzbot-driven CVEs in mac80211 or nearby networking code.
CVE-2026-31551 is not a reason to fear Wi-Fi on Linux, and it is not a reason for Windows users to panic. It is a precise reminder that small concurrency bugs in low-level control paths can become real availability vulnerabilities, especially when debug interfaces are exposed and kernel updates lag. The best response is disciplined rather than dramatic: verify affected kernels, restrict debugfs, apply vendor patches, reboot promptly, and treat Linux components in Windows-era infrastructure as first-class citizens in the security program.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center