CVE-2026-43052 is a Linux kernel Wi-Fi vulnerability disclosed by kernel.org on May 1, 2026, affecting mac80211 TDLS handling when
At first glance, CVE-2026-43052 looks like the sort of bug that should stay buried in a kernel mailing list. The affected code lives in
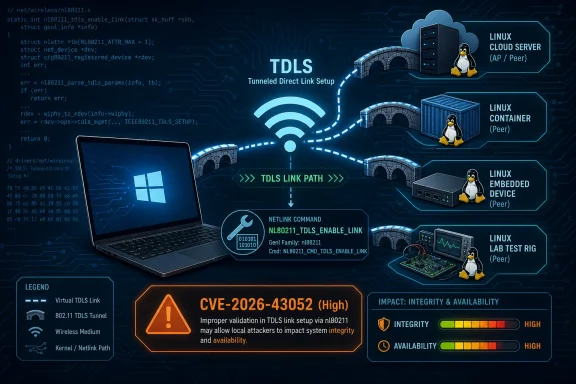
The flaw is conceptually simple. When userspace asks the kernel to enable a TDLS link through
That is the sort of bug kernel developers fix with a small conditional and security teams describe with a long CVSS vector. The patch adds an early check for
The security consequence is not remote code execution over Wi-Fi, at least based on the public description. NVD’s vector is local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality impact, and high integrity and availability impact. That paints a familiar kernel-security picture: an attacker already on the machine, with enough privilege to reach the relevant netlink operation, can potentially disturb kernel networking state in ways that matter.
For administrators, the temptation is to file this under “Linux laptop nuisance” and move on. That would be too narrow. Linux kernel CVEs now flow into Windows-adjacent environments through developer workstations, dual-boot machines, lab hardware, security appliances, hypervisors, CI runners, embedded gear, and cloud images. Even when the vulnerable code path is wireless-specific, the affected package may sit inside images and systems that security dashboards simply label as “kernel.”
That distinction matters because CVSS is a sorting mechanism, not a deployment plan. A High score on a Linux kernel Wi-Fi bug should draw attention, but it should not automatically outrank every exposed service, identity-control flaw, or actively exploited browser vulnerability in an enterprise queue. The right response is not panic; it is accurate scoping.
The lack of confidentiality impact also narrows the story. CVE-2026-43052 is not described as a data-leak vulnerability. The public record instead points to unintended state changes before failure, with integrity and availability consequences. In kernel terms, changing state in the wrong place can be enough to cause disruption, misconfiguration, or undefined behavior that defenders do not want an attacker to influence.
The “low privileges required” element is the part that deserves attention. Local kernel-adjacent bugs become more interesting when paired with containers, sandbox escapes, misconfigured capabilities, or desktop environments where users have broad networking permissions. Not every Linux system exposes the same path to the same users, and not every distro packages wireless tools and policies identically. But the CVSS vector is a reminder that this is not limited to root-only theoretical manipulation.
The more honest reading is that CVE-2026-43052 is a high-priority maintenance update, not a red-alert incident by itself. If your Linux endpoints, test rigs, or wireless-capable servers are on affected kernels, patch them through the normal kernel update process. If the machine has no Wi-Fi hardware, no untrusted local users, and no realistic path to
This is where Windows administrators entering Linux patch management often get tripped up. The upstream version number is not the same as the distro package state. Ubuntu, Debian, Red Hat, SUSE, Amazon Linux, Azure Linux, and appliance vendors routinely backport security fixes into kernel builds whose version strings do not look “new enough” if judged only against upstream kernel.org tags.
That means a vulnerability scanner may report an affected upstream range while a vendor advisory says a specific distribution kernel has already received the fix. Both can be true. The scanner is describing source lineage; the vendor is describing the patched package actually shipped to customers. In Linux kernel security, version comparison without vendor context is often worse than no version comparison at all.
The kernel.org references attached to the CVE are patch commits in stable trees. For hands-on Linux users, those commits are useful because they show the exact logic change: validate the TDLS flag before the enable-link path performs operations with side effects. For enterprise teams, the commits are less important than whether the distribution’s kernel package has absorbed the fix.
WindowsForum readers who manage mixed fleets should resist the urge to chase kernel.org versions directly unless they build their own kernels. The safer operational question is: has the vendor channel for this system shipped a kernel update that includes the CVE-2026-43052 fix? If yes, install it. If no, decide whether the machine’s exposure justifies a temporary mitigation.
Microsoft now ships, hosts, or supports enough Linux-connected infrastructure that Linux CVEs can appear in Microsoft-facing security workflows. Azure Linux, Azure host components, Microsoft container images, Linux workloads on Azure, WSL-backed developer environments, and third-party marketplace images all blur the old boundary between “Microsoft patching” and “Linux patching.” The point is not that CVE-2026-43052 is a Windows kernel flaw. It is not. The point is that Microsoft customers can encounter it inside Microsoft-managed or Microsoft-adjacent operational surfaces.
That distinction is worth preserving. A Linux kernel CVE in a Microsoft guide should not be misread as “Windows is vulnerable to a Linux Wi-Fi bug.” Windows’ native Wi-Fi stack is a different codebase. A standard Windows 11 client is not affected merely because NVD lists Linux kernel CPEs or because Microsoft’s security ecosystem indexes the CVE.
But many Windows-first organizations now run Linux as a dependency rather than as a separate estate. Developers use WSL. Security teams deploy Linux-based sensors. Cloud teams build on Linux containers. Edge devices and appliances ship Linux kernels under vendor branding. A vulnerability like this may surface in Microsoft Defender, cloud security posture management, container inventory, or third-party asset tools even if nobody in the Windows desktop team has ever touched
That is the real lesson: Microsoft’s security universe has become a catalog of dependencies, not just a catalog of Microsoft-authored code. CVE-2026-43052 is a small example of the larger administrative burden. The Windows admin now needs enough Linux literacy to know when a scary-looking kernel CVE is urgent, when it is irrelevant, and when it is a vendor-patching question.
That is a surprisingly common class of systems bug. A data structure can be valid but semantically wrong for the operation. A handle can point to a real object that is in the wrong state. An account can exist but lack the right role. A device can be present but not configured for the requested transition. The dangerous part is when code performs state-changing work before completing those semantic checks.
The public description says the operation could modify channel context and HT protection before failing. HT, or high throughput, refers to 802.11n-era wireless behavior, and channel context is central to how the kernel tracks radio operating state. Those are not cosmetic fields. They are part of the machinery that keeps wireless networking consistent across stations, channels, capabilities, and driver expectations.
The fix is therefore not glamorous, but it is exactly what secure kernel code should do: fail early, before side effects. In security engineering, that pattern is more valuable than it sounds. Validation should happen before mutation, especially in subsystems where state is shared across drivers, firmware, userspace tools, and hardware behavior.
This also explains why a local, non-confidentiality bug can still earn a High rating. The kernel is a state machine with privileges. If a low-privileged local actor can push that state machine through an invalid transition, the resulting integrity and availability consequences can be significant even without reading secrets or executing arbitrary code.
The Linux wireless stack is also layered.
TDLS adds another wrinkle because it is designed to optimize station-to-station traffic inside a Wi-Fi network. In ordinary infrastructure mode, two clients often communicate through the access point. With TDLS, they can establish a direct link while remaining associated with the same AP. That requires careful coordination because the kernel must track which peer relationships have which capabilities and state.
CVE-2026-43052 is not a dramatic failure of cryptography or a rogue access point attack. It is a bookkeeping failure in a privileged state transition. But bookkeeping failures are exactly how stable systems become unstable under adversarial input. The phrase “unintended side effects” in a kernel CVE should always make administrators pay attention, because kernel side effects rarely stay politely confined to the line of code that caused them.
The practical risk will vary sharply. A headless Linux server in a rack with no wireless hardware is unlikely to care. A fleet of Linux laptops used by engineers, penetration testers, or field staff deserves faster attention. A lab full of custom kernels and wireless experimentation deserves the fastest attention of all.
The trouble is that “Linux kernel” is both a product and an ingredient. It appears in distributions, appliances, Android-derived systems, routers, security tools, industrial devices, NAS boxes, and cloud images. NVD can list upstream kernel versions, but it cannot fully enumerate every downstream product that includes affected code, applies backports, disables features, or ships kernels with vendor patches.
That leaves vulnerability management teams in an awkward middle. If they rely only on NVD CPEs, they may miss embedded or vendor-branded devices using affected kernel code. If they rely only on product advisories, they may wait days or weeks for vendors to translate upstream CVEs into their own bulletins. If they rely only on scanner version checks, they may drown in false positives against backported distro kernels.
The better model is layered. Use NVD for the initial technical scope. Use distribution and vendor advisories for package status. Use endpoint inventory to identify systems with wireless hardware and Linux kernels in the affected families. Use compensating context to decide urgency: local users, privilege boundaries, exposed netlink capabilities, and operational importance.
For Windows-centric teams, this may require new inventory habits. It is no longer enough to know that an endpoint is “a developer laptop” or that a VM is “Ubuntu.” You need kernel package status, hardware class, whether wireless interfaces exist, whether untrusted local users can log in, and whether the system is managed by a vendor patch channel. The CPE is the beginning of the conversation, not the answer.
For this specific CVE, however, WSL is unlikely to be the most interesting exposure path for most users. WSL environments typically do not present a normal physical Wi-Fi stack through
That does not mean WSL users should ignore Linux kernel updates. It means the exploit path described for CVE-2026-43052 does not map cleanly onto the usual WSL networking model. If a scanner flags WSL because it sees a Linux kernel version, administrators should verify whether the vulnerable subsystem and operation are reachable, not simply assume equivalence with a native Linux laptop.
This is a broader WSL security lesson. WSL makes Linux real enough that kernel CVEs matter, but virtualized enough that hardware-specific CVEs may not have the same blast radius. Treating every Linux kernel CVE as fully applicable to WSL creates noise. Treating none of them as applicable creates blind spots. The right answer is boring and contextual: check the component, the configuration, and the update channel.
Developers should still update WSL kernels as part of normal hygiene. Organizations should still monitor Microsoft’s guidance for WSL-related servicing. But CVE-2026-43052 is more likely to matter on native Linux systems with wireless stack exposure than inside a default WSL environment on a Windows laptop.
Wireless fixes can be especially annoying on endpoints. A kernel update that resolves a security issue can also expose out-of-tree driver problems, DKMS build failures, firmware mismatches, or regressions in power management. Anyone who has managed Linux laptops at scale knows that “just update the kernel” can turn into “why did half the Realtek adapters disappear after reboot?”
That operational friction is why prioritization matters. Systems with active wireless use, local multi-user exposure, or sensitive operational roles should move first. Systems without Wi-Fi hardware or without untrusted local users can follow the normal maintenance cadence unless a vendor advisory says otherwise. The goal is to patch intelligently, not theatrically.
There are also temporary mitigations, though they are less elegant than a fixed kernel. Removing or disabling unused wireless interfaces, limiting local shell access, tightening capabilities around network configuration, and avoiding unnecessary TDLS tooling can reduce exposure. Those controls are not substitutes for the patch, but they can buy time where reboot windows are constrained.
The key is to avoid two bad extremes. Do not dismiss the CVE because it sounds obscure. Do not escalate it as if it were a remote unauthenticated Windows worm. It is a local Linux kernel Wi-Fi state-validation flaw with meaningful integrity and availability implications. That sentence should drive the response.
That mismatch leads to avoidable confusion. A security dashboard may show “Linux kernel before 6.12.81” and a sysadmin may see a distro kernel labeled 6.8 or 5.15 and assume it is vulnerable forever. In reality, the distro may have backported the exact fix into that older-looking kernel. Conversely, a product may use a custom kernel that does not track the distribution’s advisory cadence at all.
Windows admins do not need to become kernel maintainers. They do need to know enough to ask better questions. Is this upstream version check valid for our distribution? Has the vendor shipped a fixed package? Is the affected subsystem built and reachable? Does the system have the relevant hardware? Are there untrusted local users? Does our scanner understand backports?
Those questions are especially important in hybrid Microsoft environments. A vulnerability may enter the workflow through Microsoft tooling while the fix comes from a Linux distribution. A Linux issue may affect a Windows developer’s workstation only through WSL or a container image. A cloud workload may be “owned” by an application team but patched through a platform image maintained elsewhere.
The administrative boundary has shifted from operating system brand to dependency ownership. CVE-2026-43052 is not a Windows bug, but it is absolutely a Windows admin’s problem if that admin owns the developer fleet, the Azure estate, or the security tooling that reports it.
CVE-2026-43052 is a useful antidote to that habit. The details matter. The attack vector is local. The affected subsystem is Wi-Fi. The vulnerable operation is TDLS enable-link handling through nl80211. The impact is integrity and availability, not confidentiality. The fix is an early semantic check. The affected version ranges are broad, but real exposure depends on hardware, configuration, package status, and local access.
That is exactly the level of specificity modern vulnerability management needs. A generic “Linux kernel High” alert is almost useless. A statement that “native Linux laptops with affected mac80211 kernels should receive the vendor update promptly, while WSL and non-wireless servers require contextual validation” is actionable.
This is also where WindowsForum’s audience has an advantage. Windows administrators already understand the difference between a vulnerability that is technically present and one that is operationally exploitable. They do this every month with optional components, mitigations, role-based exposure, and cumulative update timing. The same discipline now has to extend into Linux dependencies.
The future Windows estate will keep absorbing Linux at the edges: in developer tooling, cloud images, security products, AI infrastructure, network appliances, and embedded systems. CVE-2026-43052 will not be remembered as a landmark vulnerability, but it is a clean example of the new normal. The patch is a small kernel check; the larger fix is teaching our inventories, scanners, and teams to understand the systems they already depend on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
NL80211_TDLS_ENABLE_LINK is invoked against a station that exists but is not actually a TDLS peer. The bug is narrow, local, and deeply technical, but it is not trivial: NVD currently rates it 7.1 High because a privileged local attacker can trigger integrity and availability effects without user interaction. For WindowsForum readers, the interesting part is not that a Linux Wi-Fi edge case exists; it is that this is exactly the kind of kernel flaw that now matters to Windows shops through WSL, Azure Linux, appliances, developer laptops, and mixed endpoint fleets. The modern Windows estate is no longer Windows-only, and vulnerability management has not fully caught up with that fact.
 A Wi-Fi Corner Case Becomes a Fleet-Management Problem
A Wi-Fi Corner Case Becomes a Fleet-Management Problem
At first glance, CVE-2026-43052 looks like the sort of bug that should stay buried in a kernel mailing list. The affected code lives in mac80211, the Linux kernel’s software stack for 802.11 wireless networking. The vulnerable path concerns TDLS, or Tunneled Direct Link Setup, a Wi-Fi feature that allows two stations on the same wireless network to communicate directly rather than routing every frame through the access point.The flaw is conceptually simple. When userspace asks the kernel to enable a TDLS link through
NL80211_TDLS_ENABLE_LINK, the kernel checked whether the station existed, but not whether that station was actually marked as a TDLS station. That missing type check allowed the operation to proceed far enough to modify internal wireless state, including channel context and HT protection, before eventually failing.That is the sort of bug kernel developers fix with a small conditional and security teams describe with a long CVSS vector. The patch adds an early check for
sta->sta.tdls before side effects occur, forcing the operation to fail before it mutates state for a non-TDLS peer. In human terms: the kernel was answering “yes, I know that station” when it should also have asked “is this station eligible for this operation?”The security consequence is not remote code execution over Wi-Fi, at least based on the public description. NVD’s vector is local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality impact, and high integrity and availability impact. That paints a familiar kernel-security picture: an attacker already on the machine, with enough privilege to reach the relevant netlink operation, can potentially disturb kernel networking state in ways that matter.
For administrators, the temptation is to file this under “Linux laptop nuisance” and move on. That would be too narrow. Linux kernel CVEs now flow into Windows-adjacent environments through developer workstations, dual-boot machines, lab hardware, security appliances, hypervisors, CI runners, embedded gear, and cloud images. Even when the vulnerable code path is wireless-specific, the affected package may sit inside images and systems that security dashboards simply label as “kernel.”
The Severity Score Says High, but the Exploit Story Says Local
NVD’s 7.1 High score is doing two things at once. It correctly flags that kernel integrity and availability are serious; it also leaves room for the practical reality that this is not a drive-by web exploit or a wormable remote service. The attack vector is local, and the operation in question is not something a random packet from the parking lot appears to trigger on its own.That distinction matters because CVSS is a sorting mechanism, not a deployment plan. A High score on a Linux kernel Wi-Fi bug should draw attention, but it should not automatically outrank every exposed service, identity-control flaw, or actively exploited browser vulnerability in an enterprise queue. The right response is not panic; it is accurate scoping.
The lack of confidentiality impact also narrows the story. CVE-2026-43052 is not described as a data-leak vulnerability. The public record instead points to unintended state changes before failure, with integrity and availability consequences. In kernel terms, changing state in the wrong place can be enough to cause disruption, misconfiguration, or undefined behavior that defenders do not want an attacker to influence.
The “low privileges required” element is the part that deserves attention. Local kernel-adjacent bugs become more interesting when paired with containers, sandbox escapes, misconfigured capabilities, or desktop environments where users have broad networking permissions. Not every Linux system exposes the same path to the same users, and not every distro packages wireless tools and policies identically. But the CVSS vector is a reminder that this is not limited to root-only theoretical manipulation.
The more honest reading is that CVE-2026-43052 is a high-priority maintenance update, not a red-alert incident by itself. If your Linux endpoints, test rigs, or wireless-capable servers are on affected kernels, patch them through the normal kernel update process. If the machine has no Wi-Fi hardware, no untrusted local users, and no realistic path to
NL80211_TDLS_ENABLE_LINK, the operational risk is materially lower.The Affected Kernel Ranges Tell a Messier Story Than One Version Number
The NVD configuration data currently identifies affected Linux kernel ranges from 3.2 up to, but excluding, 6.12.81; from 6.13 up to, but excluding, 6.18.22; from 6.19 up to, but excluding, 6.19.12; and 7.0 release candidates rc1 through rc4. That spread is a classic Linux kernel maintenance pattern: the vulnerable logic has existed across multiple maintained and historical branches, and fixes are landing as stable backports rather than as one neat “upgrade to version X” instruction.This is where Windows administrators entering Linux patch management often get tripped up. The upstream version number is not the same as the distro package state. Ubuntu, Debian, Red Hat, SUSE, Amazon Linux, Azure Linux, and appliance vendors routinely backport security fixes into kernel builds whose version strings do not look “new enough” if judged only against upstream kernel.org tags.
That means a vulnerability scanner may report an affected upstream range while a vendor advisory says a specific distribution kernel has already received the fix. Both can be true. The scanner is describing source lineage; the vendor is describing the patched package actually shipped to customers. In Linux kernel security, version comparison without vendor context is often worse than no version comparison at all.
The kernel.org references attached to the CVE are patch commits in stable trees. For hands-on Linux users, those commits are useful because they show the exact logic change: validate the TDLS flag before the enable-link path performs operations with side effects. For enterprise teams, the commits are less important than whether the distribution’s kernel package has absorbed the fix.
WindowsForum readers who manage mixed fleets should resist the urge to chase kernel.org versions directly unless they build their own kernels. The safer operational question is: has the vendor channel for this system shipped a kernel update that includes the CVE-2026-43052 fix? If yes, install it. If no, decide whether the machine’s exposure justifies a temporary mitigation.
Microsoft’s Presence in the Story Is About Ecosystem Gravity
The user-submitted source points to Microsoft’s Security Update Guide, even though the CVE itself is a Linux kernel issue sourced from kernel.org. That may feel odd if you still think of Microsoft security bulletins as mostly Windows, Office, Exchange, SQL Server, and Edge. In 2026, that mental model is obsolete.Microsoft now ships, hosts, or supports enough Linux-connected infrastructure that Linux CVEs can appear in Microsoft-facing security workflows. Azure Linux, Azure host components, Microsoft container images, Linux workloads on Azure, WSL-backed developer environments, and third-party marketplace images all blur the old boundary between “Microsoft patching” and “Linux patching.” The point is not that CVE-2026-43052 is a Windows kernel flaw. It is not. The point is that Microsoft customers can encounter it inside Microsoft-managed or Microsoft-adjacent operational surfaces.
That distinction is worth preserving. A Linux kernel CVE in a Microsoft guide should not be misread as “Windows is vulnerable to a Linux Wi-Fi bug.” Windows’ native Wi-Fi stack is a different codebase. A standard Windows 11 client is not affected merely because NVD lists Linux kernel CPEs or because Microsoft’s security ecosystem indexes the CVE.
But many Windows-first organizations now run Linux as a dependency rather than as a separate estate. Developers use WSL. Security teams deploy Linux-based sensors. Cloud teams build on Linux containers. Edge devices and appliances ship Linux kernels under vendor branding. A vulnerability like this may surface in Microsoft Defender, cloud security posture management, container inventory, or third-party asset tools even if nobody in the Windows desktop team has ever touched
mac80211.That is the real lesson: Microsoft’s security universe has become a catalog of dependencies, not just a catalog of Microsoft-authored code. CVE-2026-43052 is a small example of the larger administrative burden. The Windows admin now needs enough Linux literacy to know when a scary-looking kernel CVE is urgent, when it is irrelevant, and when it is a vendor-patching question.
The Bug Is Small Because the Contract Was Small
Kernel vulnerabilities often look mysterious until you reduce them to a broken contract. Here, the contract was supposed to be simple: the TDLS enable-link operation should apply only to TDLS peers. The code checked for the existence of a station object, but existence is not eligibility.That is a surprisingly common class of systems bug. A data structure can be valid but semantically wrong for the operation. A handle can point to a real object that is in the wrong state. An account can exist but lack the right role. A device can be present but not configured for the requested transition. The dangerous part is when code performs state-changing work before completing those semantic checks.
The public description says the operation could modify channel context and HT protection before failing. HT, or high throughput, refers to 802.11n-era wireless behavior, and channel context is central to how the kernel tracks radio operating state. Those are not cosmetic fields. They are part of the machinery that keeps wireless networking consistent across stations, channels, capabilities, and driver expectations.
The fix is therefore not glamorous, but it is exactly what secure kernel code should do: fail early, before side effects. In security engineering, that pattern is more valuable than it sounds. Validation should happen before mutation, especially in subsystems where state is shared across drivers, firmware, userspace tools, and hardware behavior.
This also explains why a local, non-confidentiality bug can still earn a High rating. The kernel is a state machine with privileges. If a low-privileged local actor can push that state machine through an invalid transition, the resulting integrity and availability consequences can be significant even without reading secrets or executing arbitrary code.
Wi-Fi Bugs Are Rarely Just About Wi-Fi
Wi-Fi vulnerabilities tend to get described in consumer terms: laptops dropping connections, routers misbehaving, drivers crashing after suspend. That framing misses the role wireless subsystems play in modern endpoint trust. A wireless stack is a privileged, hardware-facing, protocol-heavy attack surface that touches authentication, roaming, power management, firmware, and userspace policy.The Linux wireless stack is also layered.
cfg80211 provides configuration APIs, nl80211 is the netlink interface used by userspace, mac80211 implements common 802.11 logic for soft-MAC drivers, and hardware drivers plug into that framework. A bug in mac80211 can therefore have broad relevance across devices that rely on the common stack, even if exploitability depends on local permissions and hardware availability.TDLS adds another wrinkle because it is designed to optimize station-to-station traffic inside a Wi-Fi network. In ordinary infrastructure mode, two clients often communicate through the access point. With TDLS, they can establish a direct link while remaining associated with the same AP. That requires careful coordination because the kernel must track which peer relationships have which capabilities and state.
CVE-2026-43052 is not a dramatic failure of cryptography or a rogue access point attack. It is a bookkeeping failure in a privileged state transition. But bookkeeping failures are exactly how stable systems become unstable under adversarial input. The phrase “unintended side effects” in a kernel CVE should always make administrators pay attention, because kernel side effects rarely stay politely confined to the line of code that caused them.
The practical risk will vary sharply. A headless Linux server in a rack with no wireless hardware is unlikely to care. A fleet of Linux laptops used by engineers, penetration testers, or field staff deserves faster attention. A lab full of custom kernels and wireless experimentation deserves the fastest attention of all.
CPEs Are Helpful Until They Pretend to Be Asset Management
The NVD entry’s CPE configuration is useful because it gives scanners something to map against. It is also imperfect because CPEs compress a messy ecosystem into formal product strings. The prompt itself asks whether a CPE is missing, and that is the right instinct: kernel vulnerabilities often affect more products than the obvious upstreamlinux_kernel entry suggests.The trouble is that “Linux kernel” is both a product and an ingredient. It appears in distributions, appliances, Android-derived systems, routers, security tools, industrial devices, NAS boxes, and cloud images. NVD can list upstream kernel versions, but it cannot fully enumerate every downstream product that includes affected code, applies backports, disables features, or ships kernels with vendor patches.
That leaves vulnerability management teams in an awkward middle. If they rely only on NVD CPEs, they may miss embedded or vendor-branded devices using affected kernel code. If they rely only on product advisories, they may wait days or weeks for vendors to translate upstream CVEs into their own bulletins. If they rely only on scanner version checks, they may drown in false positives against backported distro kernels.
The better model is layered. Use NVD for the initial technical scope. Use distribution and vendor advisories for package status. Use endpoint inventory to identify systems with wireless hardware and Linux kernels in the affected families. Use compensating context to decide urgency: local users, privilege boundaries, exposed netlink capabilities, and operational importance.
For Windows-centric teams, this may require new inventory habits. It is no longer enough to know that an endpoint is “a developer laptop” or that a VM is “Ubuntu.” You need kernel package status, hardware class, whether wireless interfaces exist, whether untrusted local users can log in, and whether the system is managed by a vendor patch channel. The CPE is the beginning of the conversation, not the answer.
WSL Is Probably Not the Main Blast Radius, but It Changes the Conversation
Whenever a Linux kernel CVE appears in a Windows community, WSL naturally comes up. Windows Subsystem for Linux 2 runs a real Linux kernel inside a lightweight virtualized environment, and Microsoft services that kernel through its own update mechanism. That makes WSL relevant to Linux kernel security in general.For this specific CVE, however, WSL is unlikely to be the most interesting exposure path for most users. WSL environments typically do not present a normal physical Wi-Fi stack through
mac80211 in the way a native Linux laptop does. Windows owns the physical wireless adapter, and Linux userspace inside WSL sees virtualized networking rather than direct control of the 802.11 mac80211 layer.That does not mean WSL users should ignore Linux kernel updates. It means the exploit path described for CVE-2026-43052 does not map cleanly onto the usual WSL networking model. If a scanner flags WSL because it sees a Linux kernel version, administrators should verify whether the vulnerable subsystem and operation are reachable, not simply assume equivalence with a native Linux laptop.
This is a broader WSL security lesson. WSL makes Linux real enough that kernel CVEs matter, but virtualized enough that hardware-specific CVEs may not have the same blast radius. Treating every Linux kernel CVE as fully applicable to WSL creates noise. Treating none of them as applicable creates blind spots. The right answer is boring and contextual: check the component, the configuration, and the update channel.
Developers should still update WSL kernels as part of normal hygiene. Organizations should still monitor Microsoft’s guidance for WSL-related servicing. But CVE-2026-43052 is more likely to matter on native Linux systems with wireless stack exposure than inside a default WSL environment on a Windows laptop.
The Patch Is Easy; the Confidence Is Hard
The engineering fix for CVE-2026-43052 is straightforward: add an early TDLS flag check in the enable-link case. That does not mean remediation is equally straightforward across fleets. Kernel patching remains one of the most operationally expensive parts of Linux administration because it often requires rebooting systems, coordinating maintenance windows, and validating driver compatibility.Wireless fixes can be especially annoying on endpoints. A kernel update that resolves a security issue can also expose out-of-tree driver problems, DKMS build failures, firmware mismatches, or regressions in power management. Anyone who has managed Linux laptops at scale knows that “just update the kernel” can turn into “why did half the Realtek adapters disappear after reboot?”
That operational friction is why prioritization matters. Systems with active wireless use, local multi-user exposure, or sensitive operational roles should move first. Systems without Wi-Fi hardware or without untrusted local users can follow the normal maintenance cadence unless a vendor advisory says otherwise. The goal is to patch intelligently, not theatrically.
There are also temporary mitigations, though they are less elegant than a fixed kernel. Removing or disabling unused wireless interfaces, limiting local shell access, tightening capabilities around network configuration, and avoiding unnecessary TDLS tooling can reduce exposure. Those controls are not substitutes for the patch, but they can buy time where reboot windows are constrained.
The key is to avoid two bad extremes. Do not dismiss the CVE because it sounds obscure. Do not escalate it as if it were a remote unauthenticated Windows worm. It is a local Linux kernel Wi-Fi state-validation flaw with meaningful integrity and availability implications. That sentence should drive the response.
The Windows Admin’s Linux Problem Is Now Permanent
CVE-2026-43052 is the kind of vulnerability that exposes a quiet organizational gap. Many Windows-first teams have accumulated Linux dependencies without building Linux patch fluency. They know Patch Tuesday. They know cumulative updates. They know Defender alerts and Intune rings. But Linux kernel advisories arrive through a different culture: upstream commits, stable trees, distro backports, vendor errata, and CVE records that may lag behind the code.That mismatch leads to avoidable confusion. A security dashboard may show “Linux kernel before 6.12.81” and a sysadmin may see a distro kernel labeled 6.8 or 5.15 and assume it is vulnerable forever. In reality, the distro may have backported the exact fix into that older-looking kernel. Conversely, a product may use a custom kernel that does not track the distribution’s advisory cadence at all.
Windows admins do not need to become kernel maintainers. They do need to know enough to ask better questions. Is this upstream version check valid for our distribution? Has the vendor shipped a fixed package? Is the affected subsystem built and reachable? Does the system have the relevant hardware? Are there untrusted local users? Does our scanner understand backports?
Those questions are especially important in hybrid Microsoft environments. A vulnerability may enter the workflow through Microsoft tooling while the fix comes from a Linux distribution. A Linux issue may affect a Windows developer’s workstation only through WSL or a container image. A cloud workload may be “owned” by an application team but patched through a platform image maintained elsewhere.
The administrative boundary has shifted from operating system brand to dependency ownership. CVE-2026-43052 is not a Windows bug, but it is absolutely a Windows admin’s problem if that admin owns the developer fleet, the Azure estate, or the security tooling that reports it.
The Concrete Moves Behind This Particular Kernel Fix
The practical response to CVE-2026-43052 should be calm, specific, and inventory-driven. Treat the NVD score as a reason to investigate quickly, not as a reason to reboot everything before lunch. The systems that matter most are Linux machines with wireless stack exposure and local users who can reach the affected operation.- Identify Linux endpoints and images running kernels in the affected upstream ranges, then confirm status against the relevant distribution or vendor advisory rather than relying on upstream version numbers alone.
- Prioritize native Linux laptops, field devices, lab machines, and wireless-capable systems before headless servers with no Wi-Fi hardware.
- Update to vendor kernels that include the CVE-2026-43052 fix, and remember that a backported distro kernel may be fixed even when its version string appears older than the upstream cutoff.
- Treat WSL findings with context, because the default WSL networking model does not usually expose the physical mac80211 Wi-Fi stack in the same way as native Linux.
- Use temporary exposure reduction only as a bridge to patching, especially by disabling unused wireless interfaces and limiting local access where maintenance windows are delayed.
- Tune vulnerability management rules to distinguish upstream kernel CPE matches from confirmed vulnerable downstream packages, or this CVE will become another source of dashboard noise.
The Real Risk Is Letting “Linux Kernel” Become Background Noise
Kernel.org’s CVE pipeline has made Linux kernel vulnerabilities more visible, but visibility has a cost. Security teams now see a steady stream of kernel CVEs, many of them narrow, subsystem-specific, and difficult to map cleanly to business risk. The danger is alert fatigue: after enough obscure driver flaws, teams stop reading the details and start sorting only by score.CVE-2026-43052 is a useful antidote to that habit. The details matter. The attack vector is local. The affected subsystem is Wi-Fi. The vulnerable operation is TDLS enable-link handling through nl80211. The impact is integrity and availability, not confidentiality. The fix is an early semantic check. The affected version ranges are broad, but real exposure depends on hardware, configuration, package status, and local access.
That is exactly the level of specificity modern vulnerability management needs. A generic “Linux kernel High” alert is almost useless. A statement that “native Linux laptops with affected mac80211 kernels should receive the vendor update promptly, while WSL and non-wireless servers require contextual validation” is actionable.
This is also where WindowsForum’s audience has an advantage. Windows administrators already understand the difference between a vulnerability that is technically present and one that is operationally exploitable. They do this every month with optional components, mitigations, role-based exposure, and cumulative update timing. The same discipline now has to extend into Linux dependencies.
The future Windows estate will keep absorbing Linux at the edges: in developer tooling, cloud images, security products, AI infrastructure, network appliances, and embedded systems. CVE-2026-43052 will not be remembered as a landmark vulnerability, but it is a clean example of the new normal. The patch is a small kernel check; the larger fix is teaching our inventories, scanners, and teams to understand the systems they already depend on.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center