CVE-2026-31563 is a reminder that some of the most consequential kernel security fixes are not dramatic memory-corruption rewrites, but small context-correctness changes in code paths that run under heavy pressure. The flaw sits in the Linux kernel’s Cadence MACB/GEM Ethernet driver, where transmitted socket buffers could be freed with the wrong helper after a locking change caused the operation to occur with interrupts disabled. For most Windows users, this is not a direct Windows vulnerability; for administrators running Linux appliances, embedded systems, Azure-hosted Linux workloads, WSL-adjacent development environments, or mixed Windows/Linux infrastructure, it is exactly the kind of networking bug that deserves careful triage.
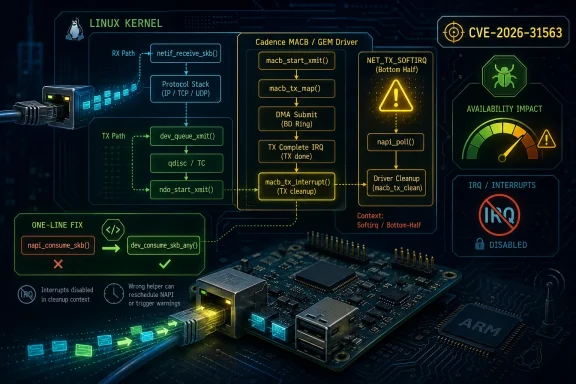
CVE-2026-31563 concerns the Linux kernel networking driver known as macb, used for Cadence MACB and GEM Ethernet controllers found across embedded and system-on-chip platforms. The reported fix changes the transmit cleanup path so that TX socket buffers are released with
That sounds deceptively small, but the kernel call context matters enormously.
The Common Vulnerability Scoring System entry from the kernel CNA assigns this issue a CVSS 3.1 score of 7.5 High, using a vector that emphasizes network attackability and availability impact rather than confidentiality or integrity loss. NVD enrichment was still incomplete at the time of the record shown in the advisory data, but affected CPE entries had already begun appearing for several mainline and stable kernel ranges.
Historically, Linux kernel CVEs have often been difficult for enterprise vulnerability teams to interpret because a given flaw may be exploitable only with specific hardware, kernel configuration, driver enablement, and traffic conditions. CVE-2026-31563 fits that pattern. It is serious enough to patch, but it is not the same kind of universal emergency as a remotely exploitable bug in a default Internet-facing service.
The visible symptom in the report was a warning from
Key points:
This is a subtle category of bug because the driver was not obviously dereferencing a bad pointer or copying past the end of a buffer. Instead, the code violated a kernel API contract. When networking traffic exercised the path, the kernel emitted a warning through the softirq machinery.
SKBs, or socket buffers, are the kernel’s core network packet containers. They carry packet data and metadata through the stack, from drivers to protocols and back again. Freeing them at the wrong time or in the wrong context can create warnings, stalls, or worse.
The important distinction is this:
Administrators should treat these CPE entries as a starting point rather than the final word. Distribution kernels often carry backports, vendor patches, and downstream version strings that do not map cleanly to upstream kernel numbers. An enterprise appliance running a vendor-maintained 6.1-based kernel may already contain the patch even if the visible kernel version appears older.
The reported trace mentions a ZynqMP ZCU102 class platform, which reinforces the embedded and board-level character of the issue. That does not mean only that board is affected, but it gives defenders a strong clue about where to look first.
Practical exposure checks should include:
A high availability score still matters. Kernel warnings in networking paths can indicate deeper stability concerns, especially if they appear under production traffic. In embedded systems, even a repeated warning or softirq disruption can become a service reliability problem.
That is why administrators should avoid two common mistakes. The first is dismissing the CVE because it is “only Linux” or “only a driver.” The second is treating it like a universal remote exploit against every Linux server.
A measured reading looks like this:
This distinction matters for patch planning. Seeing a CVE in a Microsoft security portal should not automatically lead administrators to search for a Windows cumulative update. The remediation path may involve Linux distribution packages, appliance firmware, Azure image updates, or vendor-specific kernel builds.
That does not mean WSL users should assume exposure. WSL kernels are managed differently from physical embedded Linux kernels and do not typically expose arbitrary MACB hardware paths. The more likely concern is infrastructure adjacent to Windows estates.
Windows-centric teams should check:
However, applying the fix in production still depends on distribution and vendor packaging. Embedded vendors may take longer to publish firmware images than mainstream distributions take to ship kernel updates. In some environments, the kernel is part of a read-only appliance image rather than a package that administrators can update directly.
Use this workflow:
This is especially painful for long-term support distributions. A system can appear vulnerable by version number while already containing the relevant patch. Conversely, a custom embedded kernel can report a harmless-looking downstream version while missing the upstream fix.
The risk of false positives is particularly high when:
On the positive side, the issue is documented, scored, linked to patches, and mapped into vulnerability databases quickly. On the difficult side, operations teams receive another high-severity CVE that may apply only to a subset of hardware-specific deployments.
That fragmentation creates a perception gap. A Windows flaw may have a clear KB package, while a Linux kernel CVE may require interpreting upstream commits, distribution advisories, vendor firmware notes, and scanner logic.
The broader market consequences include:
The most exposed environments are likely those with embedded Linux boards connected to operational networks. Industrial gateways, lab benches, and custom networked devices may not follow the same patch cadence as servers in a data center. That gap can turn a narrow kernel bug into a long-lived operational risk.
Priority environments include:
For enthusiasts, the more relevant audience is Raspberry Pi-style hobbyists, FPGA developers, ARM board users, and home lab operators experimenting with embedded platforms. If a board uses a Cadence-derived Ethernet MAC and runs a kernel in the affected range, this CVE is worth checking.
Enthusiasts should:
Security teams should also watch how vulnerability scanners refine detection. If scanners continue to flag every kernel in a broad range without checking driver exposure or backport status, CVE-2026-31563 will become another example of the CPE accuracy problem that frustrates Linux administrators.
Watch for:
CVE-2026-31563 is not a Windows crisis, nor is it a vulnerability to dismiss. It is a focused Linux kernel networking flaw with a clean fix, meaningful availability implications, and a hardware-dependent exposure profile. The right response is to patch where applicable, verify rather than assume, and use this case to strengthen the inventory discipline that modern mixed-platform security now requires.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-31563 concerns the Linux kernel networking driver known as macb, used for Cadence MACB and GEM Ethernet controllers found across embedded and system-on-chip platforms. The reported fix changes the transmit cleanup path so that TX socket buffers are released with dev_consume_skb_any() rather than napi_consume_skb().That sounds deceptively small, but the kernel call context matters enormously.
napi_consume_skb() is designed for NAPI processing expectations, while the affected code path began freeing TX SKBs with IRQs disabled after an earlier locking fix. The result was a kernel warning in the softirq path, with the trace pointing through skb_attempt_defer_free(), napi_consume_skb(), and macb_tx_poll().The Common Vulnerability Scoring System entry from the kernel CNA assigns this issue a CVSS 3.1 score of 7.5 High, using a vector that emphasizes network attackability and availability impact rather than confidentiality or integrity loss. NVD enrichment was still incomplete at the time of the record shown in the advisory data, but affected CPE entries had already begun appearing for several mainline and stable kernel ranges.
Historically, Linux kernel CVEs have often been difficult for enterprise vulnerability teams to interpret because a given flaw may be exploitable only with specific hardware, kernel configuration, driver enablement, and traffic conditions. CVE-2026-31563 fits that pattern. It is serious enough to patch, but it is not the same kind of universal emergency as a remotely exploitable bug in a default Internet-facing service.
Why This Kernel Bug Matters
The immediate issue is that the MACB transmit cleanup path was calling a helper that assumes a different execution context. In the Linux networking stack, freeing a socket buffer is not just a memory-management detail; it can interact with deferred freeing, softirq state, and per-CPU networking behavior.The visible symptom in the report was a warning from
__local_bh_enable_ip(), indicating that the kernel was unhappy with bottom-half handling while processing softirqs. The call trace showed the path through ksoftirqd, making this a classic Linux networking timing and context problem rather than an obvious user-space crash.The One-Line Fix With Outsized Meaning
The patch replaces one SKB release helper with another. That may look like a cosmetic API cleanup, but in kernel networking, choosing the wrong helper can create unstable behavior under interrupt or softirq constraints.Key points:
- The vulnerable path is in the TX cleanup side, not the receive fast path.
- The affected driver is hardware-specific, narrowing exposure to systems using compatible MACB/GEM devices.
- The failure mode is availability-focused, reflected in the CNA score’s high availability impact.
- The fix is intentionally narrow, reducing regression risk compared with larger driver rewrites.
- The trigger depends on runtime context, traffic, locking, and driver activity.
The Technical Root Cause
The vulnerability description points to an earlier change identified by the title “net: macb: Fix tx_ptr_lock locking.” After that change, freeing TX SKBs occurred while IRQs were disabled. The driver still callednapi_consume_skb(), which was not intended for that context.This is a subtle category of bug because the driver was not obviously dereferencing a bad pointer or copying past the end of a buffer. Instead, the code violated a kernel API contract. When networking traffic exercised the path, the kernel emitted a warning through the softirq machinery.
NAPI, SKBs, and Context Rules
NAPI is the Linux networking mechanism that reduces interrupt overhead by shifting packet processing into scheduled polling. It is central to modern Linux network performance because it prevents a device from interrupting the CPU for every packet during heavy traffic.SKBs, or socket buffers, are the kernel’s core network packet containers. They carry packet data and metadata through the stack, from drivers to protocols and back again. Freeing them at the wrong time or in the wrong context can create warnings, stalls, or worse.
The important distinction is this:
- A network device completes packet transmission.
- The driver’s TX cleanup code releases resources tied to that packet.
- The SKB must be consumed or freed using a helper appropriate to the current execution context.
- If interrupts are disabled, the helper must not assume it can safely perform operations that rely on a different bottom-half state.
- The corrected helper,
dev_consume_skb_any(), is designed to be safe across more contexts.
Affected Systems and Kernel Ranges
The advisory data lists multiple Linux kernel versions and ranges as affected, including entries around 6.1, 6.6, 6.12, 6.16, 6.17, 6.18, 6.19, and 7.0 release candidates. The listed fixed thresholds include versions such as 6.1.168, 6.6.131, 6.12.80, 6.18.21, and 6.19.11, with 7.0 release candidates also appearing in the configuration data.Administrators should treat these CPE entries as a starting point rather than the final word. Distribution kernels often carry backports, vendor patches, and downstream version strings that do not map cleanly to upstream kernel numbers. An enterprise appliance running a vendor-maintained 6.1-based kernel may already contain the patch even if the visible kernel version appears older.
Hardware Scope Is the Critical Filter
This is not a flaw that affects every Linux machine equally. The driver is associated with Cadence MACB/GEM Ethernet hardware, which is common in embedded and SoC environments, including platforms tied to ARM development boards and industrial systems.The reported trace mentions a ZynqMP ZCU102 class platform, which reinforces the embedded and board-level character of the issue. That does not mean only that board is affected, but it gives defenders a strong clue about where to look first.
Practical exposure checks should include:
- Whether the kernel includes the MACB driver
- Whether the driver is built in or loaded as a module
- Whether the system actually uses compatible Ethernet hardware
- Whether the vulnerable upstream commit range maps to the deployed vendor kernel
- Whether the vendor has backported the one-line fix
- Whether network load can exercise the TX cleanup path
Security Impact: Availability, Not Data Theft
The kernel CNA scoring emphasizes availability impact while listing no confidentiality or integrity impact. That is a meaningful distinction. CVE-2026-31563 is not described as a data-exfiltration bug, credential leak, or privilege-escalation path in the official vulnerability text provided.A high availability score still matters. Kernel warnings in networking paths can indicate deeper stability concerns, especially if they appear under production traffic. In embedded systems, even a repeated warning or softirq disruption can become a service reliability problem.
Remote Does Not Always Mean Universal
The vector lists network attack vector, low attack complexity, no privileges required, and no user interaction. That combination naturally attracts attention because it sounds broadly remote. The narrowing factor is that the vulnerable driver and hardware path must be present.That is why administrators should avoid two common mistakes. The first is dismissing the CVE because it is “only Linux” or “only a driver.” The second is treating it like a universal remote exploit against every Linux server.
A measured reading looks like this:
- High priority for embedded systems using MACB/GEM Ethernet.
- Medium operational priority for Linux fleets where hardware exposure is unknown.
- Low direct relevance for ordinary Windows endpoints.
- Scanner noise risk where version-only detection ignores driver and hardware context.
- Patch validation required for appliances with vendor-customized kernels.
Why Microsoft Users Are Seeing This CVE
The advisory material points to Microsoft’s Security Update Guide, which can surprise readers because the vulnerability is in the Linux kernel, not Windows. Microsoft’s ecosystem increasingly spans Windows, Linux, cloud infrastructure, containers, development tooling, and managed services. As a result, Linux CVEs can surface in Microsoft-facing channels even when they are not Windows OS bugs.This distinction matters for patch planning. Seeing a CVE in a Microsoft security portal should not automatically lead administrators to search for a Windows cumulative update. The remediation path may involve Linux distribution packages, appliance firmware, Azure image updates, or vendor-specific kernel builds.
Windows, WSL, Azure, and Appliances
The relationship between Windows and Linux is now operational rather than theoretical. Developers run Linux tooling through WSL, enterprises deploy Linux virtual machines in Azure, security appliances often run embedded Linux, and CI/CD systems routinely mix Windows and Linux build agents.That does not mean WSL users should assume exposure. WSL kernels are managed differently from physical embedded Linux kernels and do not typically expose arbitrary MACB hardware paths. The more likely concern is infrastructure adjacent to Windows estates.
Windows-centric teams should check:
- Linux VMs running network-facing workloads
- Embedded Linux devices monitored by Windows management tools
- Azure images based on affected Linux kernels
- Vendor appliances with Cadence MACB/GEM Ethernet controllers
- Build farms that include ARM development boards
- Security scanners mapping Linux CPEs without hardware awareness
Patch Path and Operational Response
The upstream patch is narrow: usedev_consume_skb_any() to free TX SKBs in the MACB driver. Stable backports are referenced across multiple kernel branches. That is good news because the remediation should be low-risk compared with invasive networking subsystem changes.However, applying the fix in production still depends on distribution and vendor packaging. Embedded vendors may take longer to publish firmware images than mainstream distributions take to ship kernel updates. In some environments, the kernel is part of a read-only appliance image rather than a package that administrators can update directly.
Recommended Triage Workflow
A disciplined response should separate presence, reachability, and fix status. Many teams skip straight from CVE alert to emergency change ticket, which creates unnecessary churn.Use this workflow:
- Identify whether any Linux assets use kernels listed in the affected ranges.
- Determine whether the MACB driver is present, loaded, or built into the kernel.
- Confirm whether compatible Cadence MACB/GEM Ethernet hardware is active.
- Check vendor or distribution advisories for backported fixes.
- Prioritize systems exposed to untrusted network traffic or high packet rates.
- Patch or update kernels where available.
- Monitor logs for recurring softirq, NAPI, or
macb_tx_poll()warnings after remediation.
Scanner Noise and CPE Pitfalls
The NVD change record shown in the advisory data includes CPE configurations for multiple Linux kernel ranges. CPE enrichment is useful for scanners, but Linux kernel versioning makes it tricky. A vendor kernel may report a base version while carrying hundreds of backported fixes.This is especially painful for long-term support distributions. A system can appear vulnerable by version number while already containing the relevant patch. Conversely, a custom embedded kernel can report a harmless-looking downstream version while missing the upstream fix.
Why Version Strings Are Not Enough
Security teams should treat automated findings as signals, not verdicts. For CVE-2026-31563, the ideal detection would verify the code change in the MACB driver or confirm a vendor advisory, not merely compare a kernel version to an upstream range.The risk of false positives is particularly high when:
- The scanner relies only on upstream CPE ranges
- The distribution backports fixes without changing major kernel version
- The affected driver is not enabled
- The hardware is absent
- The system is an appliance with a vendor-maintained kernel
- The scanner cannot inspect kernel configuration
Competitive and Ecosystem Implications
Linux’s vulnerability process has changed significantly since kernel.org became a CVE Numbering Authority. More kernel fixes now receive CVE identifiers, which improves traceability but also increases alert volume. CVE-2026-31563 illustrates both sides of that shift.On the positive side, the issue is documented, scored, linked to patches, and mapped into vulnerability databases quickly. On the difficult side, operations teams receive another high-severity CVE that may apply only to a subset of hardware-specific deployments.
Linux, Windows, and the Patch Perception Gap
Windows administrators are accustomed to monthly cumulative updates where applicability is often handled through Windows Update, WSUS, Intune, or enterprise patch tools. Linux kernel patching is more fragmented because distributions, hardware vendors, cloud images, and embedded BSPs all participate in the delivery chain.That fragmentation creates a perception gap. A Windows flaw may have a clear KB package, while a Linux kernel CVE may require interpreting upstream commits, distribution advisories, vendor firmware notes, and scanner logic.
The broader market consequences include:
- More pressure on vendors to publish clear kernel provenance
- More demand for SBOM-style visibility into appliance kernels
- More scrutiny of embedded Linux networking drivers
- More operational overlap between Windows and Linux security teams
- More need for patch tools that understand backports
- More confusion when high CVSS scores lack hardware context
Enterprise Impact
For enterprises, CVE-2026-31563 is primarily an asset intelligence problem. The patch itself is simple; finding every potentially affected system may be harder. Large organizations often have Linux kernels hidden inside network appliances, lab hardware, manufacturing systems, storage controllers, and ARM-based edge deployments.The most exposed environments are likely those with embedded Linux boards connected to operational networks. Industrial gateways, lab benches, and custom networked devices may not follow the same patch cadence as servers in a data center. That gap can turn a narrow kernel bug into a long-lived operational risk.
Where IT Teams Should Focus
Enterprise teams should first ask whether they own or depend on Cadence MACB/GEM Ethernet hardware. If the answer is unknown, that uncertainty is itself a governance issue.Priority environments include:
- Industrial and embedded Linux systems
- ARM development boards used in production testing
- Custom appliances built on vendor BSP kernels
- Network-connected lab equipment
- Linux-based gateways managed by Windows-heavy IT teams
- Cloud or edge workloads using vendor-provided kernel images
- Long-lived LTS kernels with delayed firmware refresh cycles
Consumer and Enthusiast Impact
For ordinary desktop Linux users, the practical risk is likely limited unless their machine uses affected MACB/GEM hardware. Most consumer PCs use Ethernet controllers from other vendors. The same is true for typical Windows laptops and desktops.For enthusiasts, the more relevant audience is Raspberry Pi-style hobbyists, FPGA developers, ARM board users, and home lab operators experimenting with embedded platforms. If a board uses a Cadence-derived Ethernet MAC and runs a kernel in the affected range, this CVE is worth checking.
Home Labs Are Not Immune
Home labs increasingly resemble small enterprises. They run Proxmox, Linux routers, NAS devices, ARM boards, Kubernetes clusters, and remote-access tooling. A vulnerability that sounds exotic can still apply if the hardware stack matches.Enthusiasts should:
- Update board vendor kernels when available
- Check whether the MACB driver is active
- Avoid exposing experimental boards directly to untrusted networks
- Watch kernel logs for softirq or MACB-related warnings
- Prefer maintained kernels over stale board-support packages
Strengths and Opportunities
CVE-2026-31563 also shows the Linux ecosystem working as intended in several respects. A precise bug was identified, a minimal fix was produced, stable branches received attention, and vulnerability databases began tracking affected ranges. The opportunity now is to turn that transparency into better operational practice rather than more indiscriminate alert fatigue.- The fix is small and reviewable, reducing the chance of broad regressions.
- The affected subsystem is identifiable, allowing hardware-aware triage.
- The vulnerability record includes patch references, helping vendors backport quickly.
- The CVSS vector clarifies the main concern as availability, not data theft.
- The issue reinforces the value of kernel API discipline, especially around IRQ and softirq context.
- The case can improve asset inventory practices for embedded Linux systems.
- The alert gives Windows-centric teams another reason to map Linux dependencies across their estates.
Risks and Concerns
The biggest risk is not that every Linux machine is suddenly vulnerable. The bigger concern is that organizations may either overreact to the high score or underreact because the bug is hardware-specific. Both responses are flawed. Context is the difference between useful vulnerability management and noisy compliance theater.- Version-only scanners may produce false positives against backported vendor kernels.
- Embedded devices may remain unpatched long after mainstream distributions ship fixes.
- Administrators may misread the Microsoft listing as a Windows OS vulnerability.
- Hardware inventory gaps may hide real exposure in industrial or lab environments.
- High availability impact may be underestimated if teams focus only on data theft.
- Custom kernels may lack clear provenance, making fix verification difficult.
- Release-candidate kernels in test labs may be overlooked because they are not considered production assets.
What to Watch Next
The next phase is distribution and vendor response. Upstream fixes are only part of the story; production safety depends on whether Debian, Ubuntu, Red Hat-family distributions, SUSE, Yocto-based vendors, appliance makers, and board-support package maintainers carry the change into deployable kernels.Security teams should also watch how vulnerability scanners refine detection. If scanners continue to flag every kernel in a broad range without checking driver exposure or backport status, CVE-2026-31563 will become another example of the CPE accuracy problem that frustrates Linux administrators.
Watch for:
- Distribution advisories confirming fixed package versions
- Embedded vendor firmware updates for MACB/GEM-based platforms
- Cloud image refreshes for Linux kernels in affected ranges
- Scanner plugin updates that account for backports
- Follow-on MACB driver fixes if testing uncovers related context bugs
CVE-2026-31563 is not a Windows crisis, nor is it a vulnerability to dismiss. It is a focused Linux kernel networking flaw with a clean fix, meaningful availability implications, and a hardware-dependent exposure profile. The right response is to patch where applicable, verify rather than assume, and use this case to strengthen the inventory discipline that modern mixed-platform security now requires.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center