CVE-2026-31662 is a reminder that some of the most disruptive kernel bugs are not dramatic memory-corruption exploits but quiet state-machine failures that can strand production workloads. The flaw sits in the Linux kernel’s Transparent Inter-Process Communication implementation, where duplicate group acknowledgment messages could underflow a broadcast counter and leave later group broadcasts permanently blocked on the affected socket. Although public scoring was still awaiting NVD enrichment at publication time, the fix has already moved through upstream and stable-kernel channels, making this a patch-management issue for administrators who rely on TIPC in clustered Linux environments.
TIPC, short for Transparent Inter-Process Communication, is a Linux networking protocol designed for reliable messaging between processes in clustered systems. It has long appealed to telecom, carrier-grade, embedded, and high-availability deployments because it gives applications a cluster-aware messaging fabric without forcing developers to build every discovery and routing primitive themselves.
The protocol is not a mainstream desktop feature, and most WindowsForum readers will never knowingly enable it on a laptop or gaming PC. Its importance lies elsewhere: in appliances, network functions, private clouds, industrial gateways, and Linux-based infrastructure where distributed services need low-latency group communication. That is why bugs in TIPC tend to matter most to operators of specialized systems rather than casual Linux users.
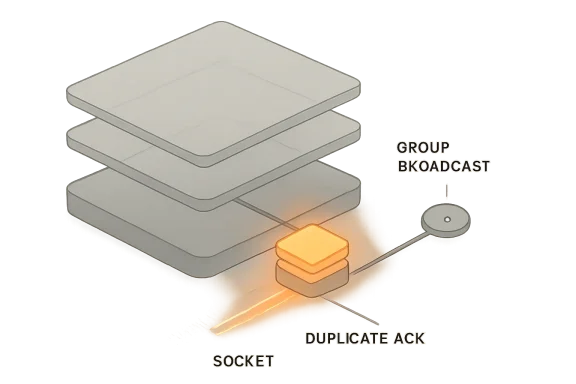
CVE-2026-31662 concerns the group broadcast acknowledgment path. In simplified terms, a sender tracks how many group members still need to acknowledge a broadcast round. The vulnerable logic allowed a duplicate or stale acknowledgment to decrement that count again, even if the same member had already acknowledged the relevant broadcast.
The technical impact is an unsigned 16-bit underflow. When a counter expected to reach zero is decremented one more time, it wraps to 65535, causing the congestion logic to believe a huge number of acknowledgments are still outstanding. The result is not a classic shell-spawning exploit but a stubborn availability failure: later group broadcasts on that socket can remain blocked until the group is recreated.
The problem was not that acknowledgments existed; it was that they were trusted too eagerly. If a member sent or caused the system to receive a duplicate acknowledgment for the same broadcast round, the kernel path could treat it as fresh progress. After the last legitimate acknowledgment brought the counter to zero, one more duplicate acknowledgment could push the unsigned counter through zero and wrap it to 65535.
That wraparound changes the meaning of the state. A value of zero says the group broadcast round is complete; a value of 65535 says the opposite, and says it loudly. Once that happens, tipc_group_bc_cong() continues to report congestion, which blocks subsequent group broadcasts on the affected socket.
That design makes GRP_ACK_MSG handling idempotent. Idempotency is a crucial property in distributed protocols: receiving the same message twice should not cause the system to make progress twice. In networking code, where duplication and reordering are normal, idempotency is not a luxury but a defensive requirement.
The patch reportedly adds only a handful of lines, but those lines restore the intended relationship between per-member acknowledgment state and the group-wide remaining-acknowledger count. It also uses sequence-aware comparison rather than a naïve integer check, which matters for protocols that must reason about sequence number wraparound.
That is the right kind of stable-kernel fix: minimal, reviewable, and targeted at the violated invariant. For enterprise maintainers, this matters because small fixes are easier to backport, easier to audit, and less likely to introduce regressions than broad rewrites.
That does not make it harmless. Availability flaws can be severe in clustered systems because they interrupt coordination. If TIPC group broadcasts carry service membership, routing state, failover signals, or application control messages, a stuck broadcast path can degrade the cluster in ways that look like partial failure rather than a clean crash.
The absence of an NVD score at the time of disclosure also deserves careful interpretation. “Awaiting enrichment” is not the same thing as “not vulnerable” or “low severity.” It simply means the public scoring and metadata process has not yet assigned a final vector.
Administrators should avoid both extremes: panic and dismissal. This is not another universal worm-class Linux panic button, but it is also not a cosmetic cleanup. In the environments that use TIPC, stalled group broadcast behavior can be operationally painful.
The more interesting systems are those that intentionally use TIPC for cluster messaging. Telecom platforms, embedded appliances, lab clusters, and specialized high-availability systems may rely on it because it was built for distributed message passing. In those cases, group broadcast reliability can be central to the application’s behavior.
For Windows users, the relevance is indirect but real. WindowsForum readers increasingly run Linux through WSL, Hyper-V guests, containers, appliances, NAS devices, routers, and lab clusters. CVE-2026-31662 is unlikely to be a Windows desktop vulnerability, but it may affect Linux kernels running alongside or underneath Windows-centered infrastructure.
For enterprises, the calculus is different. Asset owners need to identify whether TIPC is used in production and whether untrusted or semi-trusted peers can send relevant group protocol messages. If TIPC underpins service coordination, the issue deserves a place in availability-risk reviews even without a high CVSS score.
The patch has appeared in stable review material for branches including 5.15, 6.6, 6.12, and 6.18, with the upstream fix identified in the stable notes. Those branches matter because they map closely to real-world enterprise and embedded deployments. Administrators should still rely on their distribution’s advisory and package versioning rather than assuming a mainline commit hash equals local remediation.
Kernel patching is often indirect. A vendor may backport the fix without changing the visible major kernel version, so “still on 5.15” does not necessarily mean “still vulnerable.” The only reliable answer comes from vendor changelogs, package advisory metadata, or direct source-package inspection.
A practical verification process should combine package data, configuration state, and runtime exposure. The best remediation story is not just “we updated,” but “we confirmed the vulnerable path is not present or not reachable.”
Operators should look for patterns rather than a single signature. If a TIPC-based application stops broadcasting after a period of normal operation and recovers only when the group or service is recreated, this vulnerability becomes a plausible suspect. Duplicate or stale ACK traffic in packet traces would further strengthen the case, though capturing and interpreting that traffic requires TIPC familiarity.
Because the NVD record was still awaiting enrichment, many automated tools may lag in precision. Some scanners will not know affected package ranges immediately; others may overreport based on kernel family. Human review is still necessary for environments where TIPC matters.
A simple operational triage flow looks like this:
CVE-2026-31662 is less sensational than a heap overflow, but it belongs to the same broader category of risk: complex protocol code operating in privileged kernel context. Protocol implementations must handle malformed, duplicated, reordered, and adversarial traffic without corrupting internal state. That is a demanding standard.
The lesson is not that TIPC is uniquely bad. The lesson is that distributed protocol state machines are hard, especially when old code paths evolve over years and must remain compatible across stable branches. A small counter, a stale ACK, and a missing comparison can combine into a real outage condition.
This is why sequence comparisons and idempotent handlers matter. The protocol must ask not just “Is this message well-formed?” but also “Is this message new, relevant, and safe to apply now?” That second question is where many availability bugs hide.
The key distinction is that a Linux kernel CVE appearing in a Microsoft security guide does not automatically mean the Windows kernel is affected. Microsoft ships and supports Linux in several contexts, including cloud images, container hosts, Azure-oriented distributions, and developer tooling. A Linux kernel issue may therefore matter to Microsoft customers without being a Windows flaw.
This distinction is important for communication. Security teams should not tell end users that “Windows is vulnerable to TIPC” based on this CVE. They should instead identify which Linux-based Microsoft-supported or Microsoft-adjacent environments receive the advisory and patch those components according to the relevant servicing channel.
That hybrid reality changes patch management. Administrators can no longer treat Windows and Linux advisories as separate planets. A vulnerability may not touch Windows itself but still affect workloads that Windows users deploy, manage, monitor, or depend on.
For Microsoft, Red Hat, Canonical, SUSE, Debian, appliance makers, and cloud providers, the competitive differentiator is not merely whether a bug exists. Bugs exist everywhere. The differentiator is how quickly vendors identify affected products, backport fixes, publish clear guidance, and reduce customer uncertainty.
This kind of CVE also highlights the value of secure-by-default configurations. If TIPC is not loaded, not configured, and not reachable in common deployments, the blast radius is naturally smaller. Vendors that minimize enabled kernel attack surface gain a quiet security advantage.
For open source, the stable-kernel process remains one of its strongest defenses. The public review trail, small patch size, and rapid backporting demonstrate a mature remediation pipeline. The challenge is getting that fix from upstream repositories into every appliance, image, and long-lived production kernel.
Do not wait for NVD scoring if your environment relies on TIPC. CVSS is helpful for comparison, but it is not a substitute for local context. A medium-scored availability bug can be critical for a system whose business function depends on the affected communication path.
If you run vendor appliances, ask the vendor whether TIPC is enabled and whether the kernel includes the fix. Appliance owners often cannot inspect or patch kernels directly, which makes vendor transparency essential. In those cases, mitigation may involve isolation and monitoring until firmware is available.
Security teams should also watch for any enrichment that clarifies CVSS scoring, affected versions, or exploitability assumptions. A final score will help standard reporting, but local exposure should remain the deciding factor. If your systems do not use TIPC, this may stay routine; if they do, it belongs in the next maintenance cycle.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
TIPC, short for Transparent Inter-Process Communication, is a Linux networking protocol designed for reliable messaging between processes in clustered systems. It has long appealed to telecom, carrier-grade, embedded, and high-availability deployments because it gives applications a cluster-aware messaging fabric without forcing developers to build every discovery and routing primitive themselves.The protocol is not a mainstream desktop feature, and most WindowsForum readers will never knowingly enable it on a laptop or gaming PC. Its importance lies elsewhere: in appliances, network functions, private clouds, industrial gateways, and Linux-based infrastructure where distributed services need low-latency group communication. That is why bugs in TIPC tend to matter most to operators of specialized systems rather than casual Linux users.
CVE-2026-31662 concerns the group broadcast acknowledgment path. In simplified terms, a sender tracks how many group members still need to acknowledge a broadcast round. The vulnerable logic allowed a duplicate or stale acknowledgment to decrement that count again, even if the same member had already acknowledged the relevant broadcast.
The technical impact is an unsigned 16-bit underflow. When a counter expected to reach zero is decremented one more time, it wraps to 65535, causing the congestion logic to believe a huge number of acknowledgments are still outstanding. The result is not a classic shell-spawning exploit but a stubborn availability failure: later group broadcasts on that socket can remain blocked until the group is recreated.
Why this matters beyond one protocol
Kernel reliability depends on small invariants staying true under messy real-world traffic. Duplicate packets, retransmissions, stale messages, and reordered acknowledgments are not exotic conditions in distributed systems. The flaw matters because it shows how a single missing idempotency check can turn normal network weirdness into a persistent application-level outage.The Bug: A Counter That Could Fall Through Zero
The vulnerable path is in tipc_group_proto_rcv(), the group protocol receive handler. When the handler processed a GRP_ACK_MSG, it updated the member’s broadcast acknowledgment state and decremented bc_ackers, the counter representing remaining acknowledgers for the broadcast round.The problem was not that acknowledgments existed; it was that they were trusted too eagerly. If a member sent or caused the system to receive a duplicate acknowledgment for the same broadcast round, the kernel path could treat it as fresh progress. After the last legitimate acknowledgment brought the counter to zero, one more duplicate acknowledgment could push the unsigned counter through zero and wrap it to 65535.
That wraparound changes the meaning of the state. A value of zero says the group broadcast round is complete; a value of 65535 says the opposite, and says it loudly. Once that happens, tipc_group_bc_cong() continues to report congestion, which blocks subsequent group broadcasts on the affected socket.
The vulnerable sequence
The failure can be understood as a short sequence rather than a sprawling exploit chain:- A TIPC group broadcast waits for acknowledgments from participating members.
- Legitimate acknowledgments arrive and decrement bc_ackers toward zero.
- A duplicate or stale GRP_ACK_MSG arrives after the sender already counted that member.
- The handler decrements the unsigned counter again.
- The counter wraps from zero to 65535, making the socket appear congested indefinitely.
- Root cause: duplicate acknowledgments were not ignored early enough.
- Faulty assumption: each inbound group ACK represented unique progress.
- Broken invariant: bc_ackers should never decrement below zero.
- Visible symptom: group broadcasts remain blocked.
- Practical recovery: recreate the affected group or deploy the fixed kernel.
The Fix: Make ACK Handling Idempotent
The upstream fix is small but important. The corrected logic extracts the acknowledged sequence value into a local variable, compares it with the member’s existing bc_acked value, and returns early if the incoming acknowledgment is duplicate or stale. Only a genuinely newer acknowledgment is allowed to update state and decrement bc_ackers.That design makes GRP_ACK_MSG handling idempotent. Idempotency is a crucial property in distributed protocols: receiving the same message twice should not cause the system to make progress twice. In networking code, where duplication and reordering are normal, idempotency is not a luxury but a defensive requirement.
The patch reportedly adds only a handful of lines, but those lines restore the intended relationship between per-member acknowledgment state and the group-wide remaining-acknowledger count. It also uses sequence-aware comparison rather than a naïve integer check, which matters for protocols that must reason about sequence number wraparound.
Why a tiny patch can be a major fix
The most reassuring part of this correction is that it narrows the behavior instead of redesigning the subsystem. It does not add a new queueing model, change the group API, or alter the broader congestion system. It simply refuses to let old information mutate current accounting.That is the right kind of stable-kernel fix: minimal, reviewable, and targeted at the violated invariant. For enterprise maintainers, this matters because small fixes are easier to backport, easier to audit, and less likely to introduce regressions than broad rewrites.
- Before: every inbound group ACK could decrement the counter.
- After: only a newer ACK can update bc_acked and decrement bc_ackers.
- Before: duplicate ACKs could cause underflow.
- After: duplicate and stale ACKs return without changing state.
- Before: congestion could become permanent for the socket.
- After: broadcast completion accounting remains bounded and consistent.
Severity: Availability Over Data Theft
CVE-2026-31662 should be read primarily as an availability vulnerability. The disclosed behavior blocks later group broadcasts on the affected socket, potentially disrupting applications that depend on group messaging. There is no public indication from the record that this flaw enables arbitrary code execution, privilege escalation, or direct data disclosure.That does not make it harmless. Availability flaws can be severe in clustered systems because they interrupt coordination. If TIPC group broadcasts carry service membership, routing state, failover signals, or application control messages, a stuck broadcast path can degrade the cluster in ways that look like partial failure rather than a clean crash.
The absence of an NVD score at the time of disclosure also deserves careful interpretation. “Awaiting enrichment” is not the same thing as “not vulnerable” or “low severity.” It simply means the public scoring and metadata process has not yet assigned a final vector.
How defenders should think about impact
The right triage question is not “Is this remotely exploitable on every Linux server?” The better question is, “Do we run kernels with TIPC enabled and exposed to peers that can influence group protocol traffic?” For most general-purpose systems, the answer may be no; for specialized clusters, the answer may be yes.Administrators should avoid both extremes: panic and dismissal. This is not another universal worm-class Linux panic button, but it is also not a cosmetic cleanup. In the environments that use TIPC, stalled group broadcast behavior can be operationally painful.
- Confidentiality impact: no direct public evidence of data exposure.
- Integrity impact: no direct public evidence of unauthorized data modification.
- Availability impact: potentially meaningful for TIPC group users.
- Exploit shape: likely protocol-state manipulation, not memory corruption.
- Operational symptom: blocked group broadcasts until group recreation.
Who Is Actually Exposed?
Exposure depends on whether TIPC is present, enabled, and reachable in a meaningful deployment. Many Linux distributions ship kernel support for a wide range of protocols that are not active by default. A compiled-in or loadable feature is not automatically an exposed service.The more interesting systems are those that intentionally use TIPC for cluster messaging. Telecom platforms, embedded appliances, lab clusters, and specialized high-availability systems may rely on it because it was built for distributed message passing. In those cases, group broadcast reliability can be central to the application’s behavior.
For Windows users, the relevance is indirect but real. WindowsForum readers increasingly run Linux through WSL, Hyper-V guests, containers, appliances, NAS devices, routers, and lab clusters. CVE-2026-31662 is unlikely to be a Windows desktop vulnerability, but it may affect Linux kernels running alongside or underneath Windows-centered infrastructure.
Consumer versus enterprise exposure
For consumers, the likely action is simple: keep Linux distributions, appliances, and firmware updated. If you never configured TIPC, never joined a TIPC cluster, and never exposed a TIPC bearer, your practical risk is probably limited. Still, the fix will arrive through normal kernel updates, so there is little reason to avoid it.For enterprises, the calculus is different. Asset owners need to identify whether TIPC is used in production and whether untrusted or semi-trusted peers can send relevant group protocol messages. If TIPC underpins service coordination, the issue deserves a place in availability-risk reviews even without a high CVSS score.
- Higher concern: systems with intentional TIPC group communication.
- Moderate concern: appliances or vendor platforms where TIPC use is hidden.
- Lower concern: ordinary desktops with no TIPC configuration.
- Windows-adjacent concern: Linux guests, WSL kernels, containers, and appliances.
- Audit priority: externally reachable or multi-tenant clustered Linux systems.
Stable Kernel Backports and Patch Flow
The fix was accepted upstream and then propagated into multiple stable-kernel review streams. That is important because many production systems do not run the latest mainline kernel. They run long-term support branches maintained by distribution vendors or appliance suppliers.The patch has appeared in stable review material for branches including 5.15, 6.6, 6.12, and 6.18, with the upstream fix identified in the stable notes. Those branches matter because they map closely to real-world enterprise and embedded deployments. Administrators should still rely on their distribution’s advisory and package versioning rather than assuming a mainline commit hash equals local remediation.
Kernel patching is often indirect. A vendor may backport the fix without changing the visible major kernel version, so “still on 5.15” does not necessarily mean “still vulnerable.” The only reliable answer comes from vendor changelogs, package advisory metadata, or direct source-package inspection.
What patch managers should verify
This is where vulnerability management teams need discipline. A scanner may see a kernel version and flag broadly, while a distribution may have already backported the fix. Conversely, a custom kernel may report a newer base version but lack the specific patch.A practical verification process should combine package data, configuration state, and runtime exposure. The best remediation story is not just “we updated,” but “we confirmed the vulnerable path is not present or not reachable.”
- Check vendor advisories for the distribution or appliance.
- Confirm installed kernel packages include the TIPC fix.
- Review custom kernel trees if your organization builds its own kernels.
- Validate runtime configuration to see whether TIPC is loaded or enabled.
- Document exceptions where reboot timing delays kernel activation.
Detection, Triage, and Operational Clues
CVE-2026-31662 may not announce itself with a dramatic kernel panic. The disclosed failure mode is blocked group broadcast traffic on the affected socket. That means symptoms may appear as application hangs, stalled cluster membership updates, delayed failover behavior, or unexplained congestion in TIPC-dependent services.Operators should look for patterns rather than a single signature. If a TIPC-based application stops broadcasting after a period of normal operation and recovers only when the group or service is recreated, this vulnerability becomes a plausible suspect. Duplicate or stale ACK traffic in packet traces would further strengthen the case, though capturing and interpreting that traffic requires TIPC familiarity.
Because the NVD record was still awaiting enrichment, many automated tools may lag in precision. Some scanners will not know affected package ranges immediately; others may overreport based on kernel family. Human review is still necessary for environments where TIPC matters.
A practical triage checklist
The fastest path is to separate theoretical exposure from real exposure. Teams should first identify whether TIPC is active, then determine whether group broadcast is used, and finally compare the running kernel against fixed vendor packages. That narrows the response from a broad kernel scare to a targeted infrastructure task.A simple operational triage flow looks like this:
- Inventory Linux systems that run clustered or appliance workloads.
- Identify hosts where TIPC modules or built-in support are active.
- Determine whether those hosts use group broadcast features.
- Match running kernels to vendor-fixed package versions.
- Schedule reboot or live-patching actions where required.
- Monitor affected services for stuck broadcast or congestion symptoms.
- Look for: repeated service stalls in TIPC-backed clusters.
- Correlate with: kernel versions and recent traffic anomalies.
- Do not rely only on: CVSS availability or scanner output.
- Prioritize: systems where untrusted peers can influence TIPC traffic.
- Retest after patching: confirm group communication resumes normally.
Why TIPC Bugs Keep Getting Attention
TIPC has a history of security attention because it sits in the kernel networking stack and serves specialized clustered environments. Past TIPC vulnerabilities have included more severe memory-safety issues, including remotely reachable bugs under certain configurations. That history makes each new TIPC CVE worth reading carefully, even when the immediate impact differs.CVE-2026-31662 is less sensational than a heap overflow, but it belongs to the same broader category of risk: complex protocol code operating in privileged kernel context. Protocol implementations must handle malformed, duplicated, reordered, and adversarial traffic without corrupting internal state. That is a demanding standard.
The lesson is not that TIPC is uniquely bad. The lesson is that distributed protocol state machines are hard, especially when old code paths evolve over years and must remain compatible across stable branches. A small counter, a stale ACK, and a missing comparison can combine into a real outage condition.
The state-machine problem
Networking code often fails at boundaries between “message received” and “state advanced.” A packet parser may be correct, and the data structure may be valid, yet the system still misbehaves because the transition should not have occurred. CVE-2026-31662 fits that pattern almost perfectly.This is why sequence comparisons and idempotent handlers matter. The protocol must ask not just “Is this message well-formed?” but also “Is this message new, relevant, and safe to apply now?” That second question is where many availability bugs hide.
- Parsing safety prevents malformed input from corrupting memory.
- State safety prevents valid-looking input from corrupting logic.
- Idempotency prevents duplicates from causing repeated effects.
- Sequence validation prevents stale messages from rewriting current state.
- Congestion sanity checks prevent transient accounting errors from becoming permanent stalls.
Microsoft Angle: Why This Appears in a Microsoft Context
The user-facing source for many readers may be the Microsoft Security Response Center vulnerability guide, which tracks a wide range of vulnerabilities relevant to Microsoft products, services, and ecosystems. Seeing a Linux kernel CVE in that context can be confusing, especially for Windows administrators who associate MSRC primarily with Patch Tuesday.The key distinction is that a Linux kernel CVE appearing in a Microsoft security guide does not automatically mean the Windows kernel is affected. Microsoft ships and supports Linux in several contexts, including cloud images, container hosts, Azure-oriented distributions, and developer tooling. A Linux kernel issue may therefore matter to Microsoft customers without being a Windows flaw.
This distinction is important for communication. Security teams should not tell end users that “Windows is vulnerable to TIPC” based on this CVE. They should instead identify which Linux-based Microsoft-supported or Microsoft-adjacent environments receive the advisory and patch those components according to the relevant servicing channel.
WindowsForum relevance
For WindowsForum readers, the takeaway is practical. Modern Windows environments often include Linux in the stack, even when Windows remains the administrative center. Hyper-V labs, Azure workloads, Kubernetes nodes, WSL development environments, and network appliances can all introduce Linux kernel exposure.That hybrid reality changes patch management. Administrators can no longer treat Windows and Linux advisories as separate planets. A vulnerability may not touch Windows itself but still affect workloads that Windows users deploy, manage, monitor, or depend on.
- Not the same as: a native Windows kernel vulnerability.
- Potentially relevant to: Azure Linux, Linux guests, containers, appliances, and WSL-adjacent workflows.
- Best response: patch the Linux kernel through the owning distribution channel.
- Communication goal: avoid misleading “Windows affected” headlines.
- Operational reality: mixed Windows-Linux estates need unified asset visibility.
Competitive and Ecosystem Implications
Linux remains dominant across cloud infrastructure, embedded devices, network appliances, and container platforms. That dominance makes Linux kernel CVEs broadly significant even when a specific subsystem has niche deployment. Vendors that ship managed Linux platforms must absorb the complexity of kernel backports, customer communication, and exposure triage.For Microsoft, Red Hat, Canonical, SUSE, Debian, appliance makers, and cloud providers, the competitive differentiator is not merely whether a bug exists. Bugs exist everywhere. The differentiator is how quickly vendors identify affected products, backport fixes, publish clear guidance, and reduce customer uncertainty.
This kind of CVE also highlights the value of secure-by-default configurations. If TIPC is not loaded, not configured, and not reachable in common deployments, the blast radius is naturally smaller. Vendors that minimize enabled kernel attack surface gain a quiet security advantage.
The patching reputation economy
Enterprise buyers increasingly judge platforms by response quality. A low-drama advisory with clear fixed versions, sane defaults, and rapid backports builds trust. A vague advisory with uncertain exposure and delayed packages does the opposite.For open source, the stable-kernel process remains one of its strongest defenses. The public review trail, small patch size, and rapid backporting demonstrate a mature remediation pipeline. The challenge is getting that fix from upstream repositories into every appliance, image, and long-lived production kernel.
- Cloud providers must refresh images and host kernels.
- Distribution vendors must map backports to supported releases.
- Appliance makers must ship firmware updates, not just acknowledge upstream fixes.
- Security vendors must avoid overbroad scanner noise.
- Customers must reboot or otherwise activate fixed kernels.
Practical Guidance for Administrators
Administrators should start by identifying whether they operate systems that use TIPC group communication. If the answer is no, the urgency is lower, though normal kernel updates still apply. If the answer is yes, this CVE deserves prompt attention because the failure mode can interrupt service coordination.Do not wait for NVD scoring if your environment relies on TIPC. CVSS is helpful for comparison, but it is not a substitute for local context. A medium-scored availability bug can be critical for a system whose business function depends on the affected communication path.
If you run vendor appliances, ask the vendor whether TIPC is enabled and whether the kernel includes the fix. Appliance owners often cannot inspect or patch kernels directly, which makes vendor transparency essential. In those cases, mitigation may involve isolation and monitoring until firmware is available.
Recommended action plan
The sensible response is targeted and evidence-driven. Patch systems where the feature is present, reduce unnecessary exposure where it is not required, and monitor clustered services for symptoms. Avoid speculative claims about exploitation unless credible evidence emerges.- Update kernels through trusted distribution or vendor channels.
- Reboot systems where required so the fixed kernel is actually running.
- Disable TIPC where it is not needed.
- Restrict TIPC traffic to trusted cluster networks.
- Review logs and traces for stalled group communication.
- Track vendor advisories for appliances and cloud images.
- Document residual risk where patching must wait for maintenance windows.
Strengths and Opportunities
The handling of CVE-2026-31662 shows several strengths in the Linux ecosystem, particularly around upstream review and stable backporting. The fix is narrow, understandable, and rooted in a clear invariant: duplicate or stale acknowledgments must not alter broadcast accounting.Where defenders can benefit
- Small patch footprint reduces regression risk and simplifies review.
- Stable-branch backports help long-term-support deployments receive the correction.
- Clear technical root cause makes internal risk explanations easier.
- Availability-focused impact allows measured prioritization instead of panic.
- Configuration-dependent exposure gives defenders room to reduce attack surface.
- Hybrid-estate visibility can improve as teams map Linux components under Windows-centered operations.
- Protocol hardening lessons can be reused in other distributed messaging systems.
Risks and Concerns
The biggest risk is not mass exploitation on ordinary desktops; it is silent operational disruption in environments that actually depend on TIPC. A stuck group broadcast path may look like an application bug, cluster split, or transient network condition, delaying proper diagnosis.Where caution is warranted
- No final NVD score may cause some tools or teams to under-prioritize the issue.
- Custom kernels may miss the patch even when upstream branches are fixed.
- Appliances may hide TIPC use from administrators.
- Delayed reboots can leave systems vulnerable after packages are installed.
- Scanner ambiguity may create both false positives and false negatives.
- Duplicate traffic conditions may be hard to reproduce in staging.
- Availability failures may cause cascading service disruption in clustered systems.
What to Watch Next
The next important development is vendor-specific guidance. Distribution maintainers and appliance vendors will determine how quickly this fix becomes meaningful for real deployments. Watch for advisories that identify fixed package versions, required reboots, and whether TIPC is enabled by default in supported configurations.Security teams should also watch for any enrichment that clarifies CVSS scoring, affected versions, or exploitability assumptions. A final score will help standard reporting, but local exposure should remain the deciding factor. If your systems do not use TIPC, this may stay routine; if they do, it belongs in the next maintenance cycle.
Key follow-up items
- Distribution advisories for fixed kernel packages.
- Appliance firmware updates from vendors that embed Linux.
- Cloud image refreshes for Linux-based workloads.
- Scanner updates that correctly identify backported fixes.
- Any evidence of exploitation or public proof-of-concept activity.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center