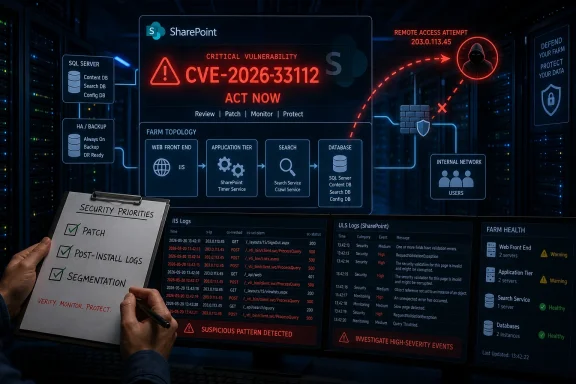
Microsoft published CVE-2026-33112 on May 12, 2026, as a Microsoft SharePoint Server remote code execution vulnerability in its Security Update Guide, marking it as a confirmed server-side flaw for administrators to address in the May Patch Tuesday cycle. The dry wording matters because SharePoint is not just another Microsoft workload; it is often the place where old authentication paths, sensitive documents, workflow glue, and internet-facing collaboration portals meet. In that environment, “remote code execution” is less a category than a warning label. The real story is not simply that Microsoft issued another CVE, but that SharePoint remains one of the most consequential pieces of on-premises software left in the Windows estate.
There are Microsoft vulnerabilities that mostly bother desktop administrators, and then there are Microsoft vulnerabilities that make infrastructure teams stop what they are doing. SharePoint remote code execution falls squarely into the second group. A vulnerable SharePoint farm is rarely isolated, rarely simple, and rarely owned by only one team.
That is why CVE-2026-33112 deserves attention even if Microsoft’s public advisory does not hand attackers a neat exploit recipe. SharePoint farms sit near identity systems, SQL Server back ends, document repositories, intranet portals, line-of-business workflows, and custom web parts that may have survived several generations of IT leadership. The product’s value is precisely what makes it dangerous when code execution enters the discussion.
The modern Microsoft security ecosystem tends to make Patch Tuesday feel mechanized: CVE IDs appear, severity ratings land, scanners update, and dashboards turn red. But a SharePoint RCE does not behave like a routine client patch. It forces administrators to weigh uptime, farm topology, cumulative update dependencies, customizations, and the possibility that the server has already been probed before the maintenance window opens.
Microsoft’s advisory language around report confidence is also important. The metric described in the source material is not decorative metadata. It tells defenders how firmly the vulnerability is believed to exist and how much reliable technical knowledge may be available outside Microsoft. When confidence is high, the risk calculation shifts from “is this real?” to “how quickly can we prove our environment is not exposed?”
A vulnerability with uncertain details can still be dangerous, but uncertainty changes the attacker-defender race. If only the existence of a bug is public, attackers may need time to reproduce it. If credible technical details are known, they can work backward faster. If the vendor confirms the issue, defenders should assume the bug is real, the patch is meaningful, and delay is no longer a research posture.
That is the understated lesson in Microsoft’s explanation of the metric. It is not merely asking whether the vulnerability exists. It is asking how much technical oxygen is already in the room. The more confidence there is in the vulnerability and its details, the easier it becomes for capable attackers to reason about likely affected code paths, patch diffs, and exploit strategy.
For SharePoint, that matters more than usual. Patch diffing a server product with a large exposed web surface is not a theoretical hobby. Once updates are released, attackers can compare old and new binaries, inspect changed components, and search for corresponding behavior in unpatched systems. The advisory may not publish the exploit, but the patch can become a map.
Still, the category justifies urgency because the outcome is severe. Code execution on a SharePoint server can place an attacker inside a trusted application tier, often with access to documents, service accounts, configuration secrets, authentication material, or internal network paths. Even when the initial vulnerability is constrained, the compromised server may become a pivot point.
SharePoint’s architecture adds another layer of concern. The farm model distributes roles across web front ends, application servers, search components, and databases. An attacker who lands on one component may not need immediate domain dominance to do damage. They may only need enough access to read documents, tamper with pages, drop persistence, harvest tokens, or move toward the SQL layer.
This is why server-side RCEs are evaluated differently from many endpoint vulnerabilities. A workstation compromise is bad, but it is often bounded by user context and endpoint controls. A SharePoint compromise can affect every user who trusts the portal, every workflow that depends on it, and every downstream system that treats it as an internal service.
But the existence of SharePoint Online does not make on-premises SharePoint disappear. Government agencies, regulated industries, manufacturers, universities, healthcare systems, and large enterprises still operate local farms for data residency, legacy integration, custom code, air-gapped workflows, or simple institutional inertia. These are exactly the environments where patching is more complex and exposure can persist.
That tension has defined SharePoint security for years. Microsoft can harden the cloud service continuously, but customers running SharePoint Server carry the operational burden themselves. They must test cumulative updates, verify custom solutions, coordinate downtime, back up farms, monitor health, and remediate failures. The patch is only the beginning of the work.
CVE-2026-33112 therefore lands in a familiar but uncomfortable place. It is a Microsoft vulnerability, but the risk is distributed across customer architecture. Redmond can ship the fix; administrators must make it real.
A SharePoint security update may require careful sequencing across farm members. It may need the SharePoint Products Configuration Wizard or equivalent PowerShell steps after binaries are installed. It may expose stale customizations that no one has touched in years. It may require coordination with SQL backups, load balancers, search indexing, and application owners who still treat the intranet as a business-critical system.
That operational friction is why SharePoint vulnerabilities can remain dangerous after patches exist. The issue is not that administrators do not care. It is that the cost of a failed SharePoint patch can be immediate and visible, while the cost of delayed security work remains probabilistic until it becomes catastrophic.
Attackers understand that asymmetry. They do not need every organization to delay. They need enough organizations to postpone updates because the portal is fragile, the maintenance window is next weekend, the farm documentation is stale, or the person who understands the custom web parts left three years ago.
The first step is asset clarity. Teams should know which SharePoint versions and editions are deployed, which farms are internet-facing, which sit behind VPN or reverse proxy infrastructure, and which are unsupported or nearly unsupported. If that inventory is incomplete, CVE-2026-33112 is a reminder that “we think we have two farms” is not a security posture.
The second step is exposure review. SharePoint portals that were once internal sometimes become externally reachable through application delivery controllers, hybrid publishing, legacy extranet projects, or emergency remote-work changes that were never unwound. The difference between an internal-only farm and a public-facing one is decisive when triaging an RCE.
The third step is log and integrity review. Administrators should examine IIS logs, SharePoint ULS logs, Windows event logs, unexpected file changes, suspicious web-access patterns, new or modified application files, anomalous service account behavior, and outbound connections from SharePoint servers. The goal is not to panic, but to avoid the common mistake of assuming patching and incident assessment are the same task.
Those orphaned farms are where server vulnerabilities become breach narratives. They may still host policy documents, HR forms, project files, or departmental workflows. They may be excluded from modern monitoring. They may rely on service accounts with excessive permissions because that was the quickest way to keep a legacy integration alive.
Security teams should be especially suspicious of SharePoint farms that have survived migrations to Microsoft 365. In many organizations, the cloud move did not retire the old farm; it merely reduced its visibility. A half-abandoned SharePoint server can be more dangerous than a central production farm because fewer people notice when it behaves strangely.
This is also where unsupported or out-of-support components create compounding risk. Even when the SharePoint version itself can receive updates, the surrounding ecosystem may include old Windows Server builds, outdated SQL Server instances, forgotten third-party add-ons, weak TLS configurations, or custom code compiled for a previous era of .NET assumptions.
The missing half is environmental context. A SharePoint RCE in a tightly segmented internal farm with rapid patching and strong monitoring is one kind of problem. The same CVE on an internet-facing extranet with legacy authentication and weak logging is another. The advisory cannot know which one you run.
This is where sysadmins and security teams need to resist dashboard flattening. Vulnerability management platforms often rank issues by severity score and asset count, but SharePoint deserves a higher-fidelity view. The question is not merely “how many vulnerable servers exist?” It is “what business process, identity path, and data set does each vulnerable server touch?”
That context should influence patch order. Internet-facing farms should move first. Farms with sensitive document repositories should move early. Farms with custom code should be tested quickly but not allowed to drift indefinitely. Farms that nobody claims should trigger a harder conversation: patch them, isolate them, or retire them.
Some actors watch advisories. Others diff patches. Others scan the internet. Others sell access. Others wait for working proof-of-concept code to circulate privately before it appears publicly. By the time a vulnerability becomes widely commoditized, the earliest compromise windows may already be closed for well-run organizations and wide open for laggards.
That is why the confidence metric in the user-provided description is so relevant. The more certain the vulnerability is, and the more credible the known details are, the less defenders should rely on obscurity. Even if Microsoft does not say exploitation is observed, administrators should assume serious researchers and serious attackers are paying attention.
The defender’s advantage is boring but real: inventory, patching, segmentation, least privilege, logging, backups, and rehearsed incident response. None of those are glamorous. All of them matter more than guessing whether a CVE will become the next headline.
SharePoint should break through that fatigue. It is a collaboration platform, a document store, an application platform, and in many environments a legacy dependency hub. A remote code execution vulnerability in that stack deserves a different kind of attention than yet another local privilege escalation on a lightly used endpoint.
The broader pattern is also worth noticing. Microsoft has spent years pushing customers toward cloud-managed services where patching responsibility shifts upward. Yet the Windows ecosystem still contains enormous on-premises gravity. Every SharePoint Server RCE is a reminder that hybrid IT is not a transitional phase for many organizations; it is the long-term operating model.
That means defenders cannot simply adopt cloud assumptions while leaving server-era systems behind. The organizations most at risk are often those that believe they have modernized because Microsoft 365 is widely deployed, while older SharePoint farms continue to run in the background.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 SharePoint Keeps Turning Routine Patch Tuesday Into a Server-Room Fire Drill
SharePoint Keeps Turning Routine Patch Tuesday Into a Server-Room Fire Drill
There are Microsoft vulnerabilities that mostly bother desktop administrators, and then there are Microsoft vulnerabilities that make infrastructure teams stop what they are doing. SharePoint remote code execution falls squarely into the second group. A vulnerable SharePoint farm is rarely isolated, rarely simple, and rarely owned by only one team.That is why CVE-2026-33112 deserves attention even if Microsoft’s public advisory does not hand attackers a neat exploit recipe. SharePoint farms sit near identity systems, SQL Server back ends, document repositories, intranet portals, line-of-business workflows, and custom web parts that may have survived several generations of IT leadership. The product’s value is precisely what makes it dangerous when code execution enters the discussion.
The modern Microsoft security ecosystem tends to make Patch Tuesday feel mechanized: CVE IDs appear, severity ratings land, scanners update, and dashboards turn red. But a SharePoint RCE does not behave like a routine client patch. It forces administrators to weigh uptime, farm topology, cumulative update dependencies, customizations, and the possibility that the server has already been probed before the maintenance window opens.
Microsoft’s advisory language around report confidence is also important. The metric described in the source material is not decorative metadata. It tells defenders how firmly the vulnerability is believed to exist and how much reliable technical knowledge may be available outside Microsoft. When confidence is high, the risk calculation shifts from “is this real?” to “how quickly can we prove our environment is not exposed?”
The Confidence Metric Is a Quiet Signal With Loud Operational Consequences
Security advisories are full of fields that many administrators skim past because they appear abstract. CVSS vectors, exploitability assessments, report confidence, attack complexity, privileges required, user interaction, scope: all of them can blur into the same dashboard noise when a team is triaging dozens of updates. But the confidence metric attached to a vulnerability is one of the more useful signals when deciding how aggressively to move.A vulnerability with uncertain details can still be dangerous, but uncertainty changes the attacker-defender race. If only the existence of a bug is public, attackers may need time to reproduce it. If credible technical details are known, they can work backward faster. If the vendor confirms the issue, defenders should assume the bug is real, the patch is meaningful, and delay is no longer a research posture.
That is the understated lesson in Microsoft’s explanation of the metric. It is not merely asking whether the vulnerability exists. It is asking how much technical oxygen is already in the room. The more confidence there is in the vulnerability and its details, the easier it becomes for capable attackers to reason about likely affected code paths, patch diffs, and exploit strategy.
For SharePoint, that matters more than usual. Patch diffing a server product with a large exposed web surface is not a theoretical hobby. Once updates are released, attackers can compare old and new binaries, inspect changed components, and search for corresponding behavior in unpatched systems. The advisory may not publish the exploit, but the patch can become a map.
Remote Code Execution Is Not One Risk, but a Chain Waiting for Context
The phrase remote code execution can be misleadingly compact. In practical terms, it can mean anything from a difficult authenticated attack requiring a peculiar configuration to a pre-authentication bug that can be triggered over the network with a crafted request. The difference is enormous, and administrators should read Microsoft’s advisory fields closely rather than reacting to the acronym alone.Still, the category justifies urgency because the outcome is severe. Code execution on a SharePoint server can place an attacker inside a trusted application tier, often with access to documents, service accounts, configuration secrets, authentication material, or internal network paths. Even when the initial vulnerability is constrained, the compromised server may become a pivot point.
SharePoint’s architecture adds another layer of concern. The farm model distributes roles across web front ends, application servers, search components, and databases. An attacker who lands on one component may not need immediate domain dominance to do damage. They may only need enough access to read documents, tamper with pages, drop persistence, harvest tokens, or move toward the SQL layer.
This is why server-side RCEs are evaluated differently from many endpoint vulnerabilities. A workstation compromise is bad, but it is often bounded by user context and endpoint controls. A SharePoint compromise can affect every user who trusts the portal, every workflow that depends on it, and every downstream system that treats it as an internal service.
The Cloud Escape Hatch Does Not Help the On-Premises Fleet
Microsoft’s strategic answer to many SharePoint security headaches is, implicitly, SharePoint Online. The cloud service gives Microsoft more control over patch cadence, telemetry, isolation, and emergency response. For many organizations, the safest SharePoint server is the one they no longer run.But the existence of SharePoint Online does not make on-premises SharePoint disappear. Government agencies, regulated industries, manufacturers, universities, healthcare systems, and large enterprises still operate local farms for data residency, legacy integration, custom code, air-gapped workflows, or simple institutional inertia. These are exactly the environments where patching is more complex and exposure can persist.
That tension has defined SharePoint security for years. Microsoft can harden the cloud service continuously, but customers running SharePoint Server carry the operational burden themselves. They must test cumulative updates, verify custom solutions, coordinate downtime, back up farms, monitor health, and remediate failures. The patch is only the beginning of the work.
CVE-2026-33112 therefore lands in a familiar but uncomfortable place. It is a Microsoft vulnerability, but the risk is distributed across customer architecture. Redmond can ship the fix; administrators must make it real.
Patch Management Is the Easy Part Until SharePoint Is Involved
For ordinary Windows endpoints, patch management has become increasingly automated. Windows Update for Business, Intune, WSUS, Autopatch-style servicing, and third-party tools can move large fleets with predictable rings and rollback planning. SharePoint Server does not fit neatly into that mental model.A SharePoint security update may require careful sequencing across farm members. It may need the SharePoint Products Configuration Wizard or equivalent PowerShell steps after binaries are installed. It may expose stale customizations that no one has touched in years. It may require coordination with SQL backups, load balancers, search indexing, and application owners who still treat the intranet as a business-critical system.
That operational friction is why SharePoint vulnerabilities can remain dangerous after patches exist. The issue is not that administrators do not care. It is that the cost of a failed SharePoint patch can be immediate and visible, while the cost of delayed security work remains probabilistic until it becomes catastrophic.
Attackers understand that asymmetry. They do not need every organization to delay. They need enough organizations to postpone updates because the portal is fragile, the maintenance window is next weekend, the farm documentation is stale, or the person who understands the custom web parts left three years ago.
The Post-Patch Checklist Is Where Many Defenses Actually Begin
Installing Microsoft’s update should be the first priority, but it should not be the last action. SharePoint administrators should treat a server-side RCE advisory as an opportunity to verify the entire defensive posture around the farm. The patch closes the known bug; it does not automatically prove that the server was never touched.The first step is asset clarity. Teams should know which SharePoint versions and editions are deployed, which farms are internet-facing, which sit behind VPN or reverse proxy infrastructure, and which are unsupported or nearly unsupported. If that inventory is incomplete, CVE-2026-33112 is a reminder that “we think we have two farms” is not a security posture.
The second step is exposure review. SharePoint portals that were once internal sometimes become externally reachable through application delivery controllers, hybrid publishing, legacy extranet projects, or emergency remote-work changes that were never unwound. The difference between an internal-only farm and a public-facing one is decisive when triaging an RCE.
The third step is log and integrity review. Administrators should examine IIS logs, SharePoint ULS logs, Windows event logs, unexpected file changes, suspicious web-access patterns, new or modified application files, anomalous service account behavior, and outbound connections from SharePoint servers. The goal is not to panic, but to avoid the common mistake of assuming patching and incident assessment are the same task.
Older Farms Are the Real Blast Radius
The most exposed SharePoint environments are often not the ones with the largest budgets, but the ones with the oldest assumptions. A mature enterprise may have a well-run SharePoint Subscription Edition farm with documented patch rings and dedicated ownership. A smaller or fragmented organization may have an older SharePoint deployment that is technically “important” but operationally orphaned.Those orphaned farms are where server vulnerabilities become breach narratives. They may still host policy documents, HR forms, project files, or departmental workflows. They may be excluded from modern monitoring. They may rely on service accounts with excessive permissions because that was the quickest way to keep a legacy integration alive.
Security teams should be especially suspicious of SharePoint farms that have survived migrations to Microsoft 365. In many organizations, the cloud move did not retire the old farm; it merely reduced its visibility. A half-abandoned SharePoint server can be more dangerous than a central production farm because fewer people notice when it behaves strangely.
This is also where unsupported or out-of-support components create compounding risk. Even when the SharePoint version itself can receive updates, the surrounding ecosystem may include old Windows Server builds, outdated SQL Server instances, forgotten third-party add-ons, weak TLS configurations, or custom code compiled for a previous era of .NET assumptions.
Microsoft’s Security Guide Tells Only Half the Story
Microsoft’s Security Update Guide is built for precision, not narrative. It tells administrators what CVE exists, what products are affected, what updates apply, and how Microsoft evaluates severity and exploitability. That is necessary, but it is not sufficient for real-world risk management.The missing half is environmental context. A SharePoint RCE in a tightly segmented internal farm with rapid patching and strong monitoring is one kind of problem. The same CVE on an internet-facing extranet with legacy authentication and weak logging is another. The advisory cannot know which one you run.
This is where sysadmins and security teams need to resist dashboard flattening. Vulnerability management platforms often rank issues by severity score and asset count, but SharePoint deserves a higher-fidelity view. The question is not merely “how many vulnerable servers exist?” It is “what business process, identity path, and data set does each vulnerable server touch?”
That context should influence patch order. Internet-facing farms should move first. Farms with sensitive document repositories should move early. Farms with custom code should be tested quickly but not allowed to drift indefinitely. Farms that nobody claims should trigger a harder conversation: patch them, isolate them, or retire them.
The Attacker’s Advantage Is Time, Not Magic
There is a tendency to treat high-profile Microsoft server vulnerabilities as if exploitation requires nation-state genius. Sometimes it does. Often it does not, at least not for long. Once a patch ships, the research problem changes, and the attacker community can divide the labor.Some actors watch advisories. Others diff patches. Others scan the internet. Others sell access. Others wait for working proof-of-concept code to circulate privately before it appears publicly. By the time a vulnerability becomes widely commoditized, the earliest compromise windows may already be closed for well-run organizations and wide open for laggards.
That is why the confidence metric in the user-provided description is so relevant. The more certain the vulnerability is, and the more credible the known details are, the less defenders should rely on obscurity. Even if Microsoft does not say exploitation is observed, administrators should assume serious researchers and serious attackers are paying attention.
The defender’s advantage is boring but real: inventory, patching, segmentation, least privilege, logging, backups, and rehearsed incident response. None of those are glamorous. All of them matter more than guessing whether a CVE will become the next headline.
The May Patch Tuesday Signal Is Bigger Than One CVE
CVE-2026-33112 arrives as part of a broader monthly security rhythm that has become both indispensable and exhausting. Microsoft’s monthly releases routinely touch Windows, Office, Edge, Azure components, developer tools, identity services, and server products. For administrators, the flood of CVEs can make individual issues feel interchangeable.SharePoint should break through that fatigue. It is a collaboration platform, a document store, an application platform, and in many environments a legacy dependency hub. A remote code execution vulnerability in that stack deserves a different kind of attention than yet another local privilege escalation on a lightly used endpoint.
The broader pattern is also worth noticing. Microsoft has spent years pushing customers toward cloud-managed services where patching responsibility shifts upward. Yet the Windows ecosystem still contains enormous on-premises gravity. Every SharePoint Server RCE is a reminder that hybrid IT is not a transitional phase for many organizations; it is the long-term operating model.
That means defenders cannot simply adopt cloud assumptions while leaving server-era systems behind. The organizations most at risk are often those that believe they have modernized because Microsoft 365 is widely deployed, while older SharePoint farms continue to run in the background.
The SharePoint Patch Window Is Really a Governance Test
The concrete response to CVE-2026-33112 is straightforward: identify affected SharePoint Server deployments, apply Microsoft’s security updates, complete required post-installation configuration steps, and review the environment for signs of suspicious activity. The harder response is organizational. SharePoint security is where ownership gaps become technical exposure.- Organizations should treat CVE-2026-33112 as a server-risk event, not merely another item in the monthly Microsoft patch bundle.
- Administrators should prioritize internet-facing SharePoint farms, sensitive document repositories, and deployments with weak monitoring or unclear ownership.
- Patch installation should be paired with SharePoint configuration completion, farm health validation, and log review rather than treated as a one-click endpoint update.
- Security teams should verify whether old SharePoint farms remain reachable after Microsoft 365 migrations or legacy extranet projects.
- Unsupported add-ons, stale custom code, overprivileged service accounts, and poor segmentation can turn a patched CVE into a broader compromise problem.
- The confidence signal in Microsoft’s advisory metadata should push teams toward action because confirmed vulnerabilities give attackers more reliable ground to study.
Source: MSRC Security Update Guide - Microsoft Security Response Center