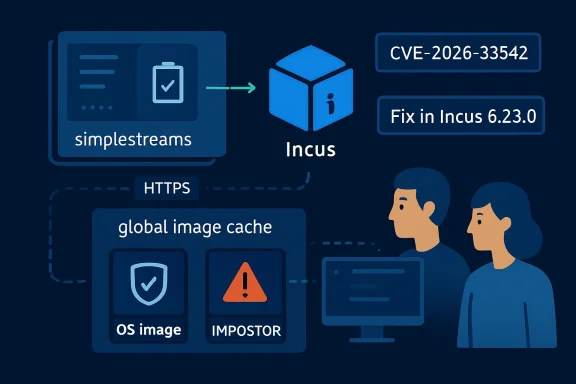
CVE-2026-33542 is a medium-severity Incus vulnerability disclosed in late March 2026 in which Incus versions before 6.23.0 failed to verify the combined image fingerprint when downloading container and virtual-machine images from simplestreams servers, enabling narrowly scoped image cache poisoning in exposed multi-tenant environments. The bug is not the kind of remote-code-execution fire alarm that sends every admin sprinting to a console. It is more interesting than that: a supply-chain trust failure hiding in a workflow that many teams treat as boring plumbing. The patch is straightforward, but the lesson is larger than Incus.
Incus did not simply download arbitrary files and hope for the best. The vulnerable path used HTTPS and validated the SHA-256 hashes of individual image files. That matters, because it explains why this issue can look less serious at first glance than it actually is.
The missing step was the combined fingerprint: the SHA-256 value Incus uses for the concatenated image files that define the image as a whole. In other words, the system checked the parts but did not adequately prove that the assembled object matched the identity advertised in the simplestreams index. That is the sort of mistake that lives in the seam between “file integrity” and “artifact identity.”
This distinction is not academic. Container and VM images are not just blobs; they are bootable trust decisions. If the platform says an image fingerprint corresponds to a known Debian, Ubuntu, or other base image, downstream users tend to behave as though that identity has been settled.
CVE-2026-33542 shows what happens when identity is inferred from adjacent checks instead of verified directly. The attacker does not need to break SHA-256. The attacker needs a workflow that accepts a maliciously constructed image path as if it were the legitimate one.
The plausible attack is a race against legitimate image use. An attacker with access to an Incus environment, and with the ability to point Incus at an attacker-controlled simplestreams image server, can try to get a compromised image cached under a fingerprint associated with a well-known image. Another tenant later asks for the legitimate image and receives the cached impostor instead.
That is why the vulnerability is both limited and uncomfortable. It is limited because the attacker needs access, timing, and an environment that has not restricted image sources. It is uncomfortable because those requirements map neatly onto the places where Incus is most attractive: shared build systems, CI infrastructure, lab clusters, developer platforms, and multi-tenant internal clouds.
In a single-user homelab, the practical risk may be modest. In a shared service where users launch short-lived instances all day, the risk gets sharper. The more predictable the image selection and the more frequent the launches, the easier it becomes to imagine a poisoned image landing before the legitimate one.
The attacker needs some access to the Incus server. The environment must lack project-level image-source restrictions or equivalent controls through firewalls or proxies. The attacker must predict what another user is likely to launch before that image is already cached legitimately. In many well-run environments, those conditions will not line up.
But the operational world is not made entirely of well-run environments. Internal developer platforms often grow by accretion, not by architecture. A cluster starts as a convenience, gains more users, becomes part of build automation, and only later receives the policies it should have had from day one.
That is the security story here. CVE-2026-33542 is less a spectacular exploit than a reminder that shared infrastructure amplifies small validation bugs. A missing check in an image downloader becomes a tenant-to-tenant integrity problem because the cache is shared and the artifact is executable.
Image distribution systems always carry a layered trust model. There is transport security, usually HTTPS. There are file hashes. There are indexes, aliases, publication dates, architectures, and image variants. Finally, there is the thing administrators actually rely on: “this image is the one I asked for.”
CVE-2026-33542 sits at the final layer. Incus validated individual files but did not validate that the concatenated content matched the image fingerprint advertised by the simplestreams index. That is a classic example of a system checking ingredients without checking the recipe.
This also explains why the fix is conceptually simple. Incus 6.23.0 validates not only the individual files but also the full image hash. The product now closes the gap between downloaded components and the image identity that users and caches depend on.
A multi-tenant Incus platform should not allow arbitrary users to make the host fetch images from arbitrary simplestreams servers. That turns the host into a trust broker for every tenant and every cache entry. In a shared system, image sources should be curated, logged, and constrained.
This is the same pattern Windows admins know from package repositories, driver sources, update rings, and PowerShell galleries. The dangerous part is rarely the download itself. The dangerous part is a trusted automation system downloading something on behalf of users and then making it available to others.
For Incus operators, CVE-2026-33542 should trigger three checks: whether all nodes are at least version 6.23.0, whether image-source restrictions exist per project, and whether the cache should be purged or refreshed after the upgrade. The last point is especially relevant if the environment allowed broad remote image sources before the patch.
That shift matters for WindowsForum readers. Modern Windows estates increasingly include Linux build hosts, WSL-adjacent development workflows, Azure-hosted Linux services, GitHub-driven CI, and container platforms that never show up in the old desktop-server mental model. A flaw in an image-fetching path can therefore matter to a Windows shop even if no Windows endpoint is directly affected.
The Microsoft Knowledge Base disclaimer attached to the entry is boilerplate, but the publication channel is still useful. It places an open-source infrastructure bug into the same operational stream many enterprises already monitor. That helps security teams catch issues that live outside their primary vendor comfort zone.
The risk is that teams misread the context. This is not something to hunt for on every Windows laptop. It is something to look for wherever Incus is used to run containers or virtual machines, especially in shared build and test infrastructure.
That does not mean every LXD deployment is automatically vulnerable in the same way or on the same timeline. It does mean administrators should read their distribution and vendor advisories carefully instead of treating CVE titles as complete inventories. Packaging, backports, snaps, distro builds, and forked implementations can all move at different speeds.
For enterprise IT, this is where asset management earns its keep. Knowing that “we use containers” is not enough. Teams need to know whether they run Incus, LXD, distro-packaged variants, snap packages, or managed services that abstract the whole thing away.
The practical question is not whether the CVE has a frightening name. The practical question is whether any platform in the organization downloads images from simplestreams servers into a shared cache that other users trust.
But patching alone should not be the end of the response. A bug like this exposes whether an organization has been relying on artifact integrity checks as a substitute for source governance. Those are not the same thing.
Source governance says ordinary tenants cannot make the infrastructure pull from arbitrary image servers. Integrity checking says the thing fetched matches the thing described. You need both. One limits who gets to introduce artifacts into the trust domain; the other ensures the artifact has not shifted identity on the way in.
The advisory’s own mitigation logic is therefore unusually useful. Environments already using
The reason is simple: images are supply-chain artifacts. A base image is often the first executable layer in an environment. It may contain shells, package managers, init scripts, cloud-init behavior, certificates, default users, and hooks that later automation assumes are clean.
If a malicious image enters that pipeline under a trusted identity, every layer above it becomes suspect. Secrets mounted into a container, build credentials used during CI, internal network access granted to a test VM, and telemetry collected by agents can all become part of the attacker’s opportunity surface.
That does not mean every vulnerable Incus environment was compromised. The attack conditions are constrained enough that panic would be misplaced. But complacency would be just as misplaced, because this is exactly the kind of low-drama infrastructure bug that can become high-impact in the wrong topology.
CVE-2026-33542 will not be remembered as the vulnerability that broke container security, and that is precisely why it is worth studying. The industry’s most durable failures often arrive as small mismatches between what a platform verifies and what its users believe has been verified. Incus has patched that mismatch, but the next version of this bug will appear wherever shared infrastructure turns downloads into trusted execution; the winning teams will be the ones that treat image sources, caches, and fingerprints as one security boundary rather than three separate chores.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Quiet Failure Was in the Last Hash, Not the First One
The Quiet Failure Was in the Last Hash, Not the First One
Incus did not simply download arbitrary files and hope for the best. The vulnerable path used HTTPS and validated the SHA-256 hashes of individual image files. That matters, because it explains why this issue can look less serious at first glance than it actually is.The missing step was the combined fingerprint: the SHA-256 value Incus uses for the concatenated image files that define the image as a whole. In other words, the system checked the parts but did not adequately prove that the assembled object matched the identity advertised in the simplestreams index. That is the sort of mistake that lives in the seam between “file integrity” and “artifact identity.”
This distinction is not academic. Container and VM images are not just blobs; they are bootable trust decisions. If the platform says an image fingerprint corresponds to a known Debian, Ubuntu, or other base image, downstream users tend to behave as though that identity has been settled.
CVE-2026-33542 shows what happens when identity is inferred from adjacent checks instead of verified directly. The attacker does not need to break SHA-256. The attacker needs a workflow that accepts a maliciously constructed image path as if it were the legitimate one.
Cache Poisoning Turns One User’s Pull Into Another User’s Problem
The most important phrase in the advisory is not “fingerprint” but “global image cache.” Incus, like other virtualization and container platforms, avoids repeatedly fetching the same images by caching them locally or within a cluster. That is good engineering until a poisoned cache becomes a shared trust boundary.The plausible attack is a race against legitimate image use. An attacker with access to an Incus environment, and with the ability to point Incus at an attacker-controlled simplestreams image server, can try to get a compromised image cached under a fingerprint associated with a well-known image. Another tenant later asks for the legitimate image and receives the cached impostor instead.
That is why the vulnerability is both limited and uncomfortable. It is limited because the attacker needs access, timing, and an environment that has not restricted image sources. It is uncomfortable because those requirements map neatly onto the places where Incus is most attractive: shared build systems, CI infrastructure, lab clusters, developer platforms, and multi-tenant internal clouds.
In a single-user homelab, the practical risk may be modest. In a shared service where users launch short-lived instances all day, the risk gets sharper. The more predictable the image selection and the more frequent the launches, the easier it becomes to imagine a poisoned image landing before the legitimate one.
The Exploitability Caveats Are Real, but They Are Not a Free Pass
Security advisories often collapse under their own qualifiers. “Under narrow circumstances” can sound like an invitation to defer patching, especially when the CVSS score lands in the medium range. Here, the caveats are real: this is not a drive-by internet exploit against every Incus daemon.The attacker needs some access to the Incus server. The environment must lack project-level image-source restrictions or equivalent controls through firewalls or proxies. The attacker must predict what another user is likely to launch before that image is already cached legitimately. In many well-run environments, those conditions will not line up.
But the operational world is not made entirely of well-run environments. Internal developer platforms often grow by accretion, not by architecture. A cluster starts as a convenience, gains more users, becomes part of build automation, and only later receives the policies it should have had from day one.
That is the security story here. CVE-2026-33542 is less a spectacular exploit than a reminder that shared infrastructure amplifies small validation bugs. A missing check in an image downloader becomes a tenant-to-tenant integrity problem because the cache is shared and the artifact is executable.
Simplestreams Was the Messenger, Not the Villain
It would be easy to blame simplestreams because it appears in the vulnerability title. That would be too neat. Simplestreams is a metadata and distribution mechanism; the failure was in how Incus consumed that metadata in a specific path.Image distribution systems always carry a layered trust model. There is transport security, usually HTTPS. There are file hashes. There are indexes, aliases, publication dates, architectures, and image variants. Finally, there is the thing administrators actually rely on: “this image is the one I asked for.”
CVE-2026-33542 sits at the final layer. Incus validated individual files but did not validate that the concatenated content matched the image fingerprint advertised by the simplestreams index. That is a classic example of a system checking ingredients without checking the recipe.
This also explains why the fix is conceptually simple. Incus 6.23.0 validates not only the individual files but also the full image hash. The product now closes the gap between downloaded components and the image identity that users and caches depend on.
Multi-Tenant Incus Operators Should Treat This as a Policy Audit
The patch is the headline, but the mitigation language is the story IT teams should read twice. The advisory points torestricted.image.servers and equivalent firewall or HTTP proxy policies as meaningful protections. That is not a workaround in the flimsy sense; it is the right architectural control for shared environments.A multi-tenant Incus platform should not allow arbitrary users to make the host fetch images from arbitrary simplestreams servers. That turns the host into a trust broker for every tenant and every cache entry. In a shared system, image sources should be curated, logged, and constrained.
This is the same pattern Windows admins know from package repositories, driver sources, update rings, and PowerShell galleries. The dangerous part is rarely the download itself. The dangerous part is a trusted automation system downloading something on behalf of users and then making it available to others.
For Incus operators, CVE-2026-33542 should trigger three checks: whether all nodes are at least version 6.23.0, whether image-source restrictions exist per project, and whether the cache should be purged or refreshed after the upgrade. The last point is especially relevant if the environment allowed broad remote image sources before the patch.
Microsoft’s Presence Is a Signal About the New Patch Surface
This vulnerability appears through Microsoft’s Security Update Guide ecosystem, but that does not make it a Windows vulnerability in the traditional Patch Tuesday sense. Incus is a Linux container and VM manager that emerged from the LXD ecosystem. The Microsoft angle is about visibility, dependency awareness, and the reality that enterprise vulnerability management now spans far beyond Microsoft-authored code.That shift matters for WindowsForum readers. Modern Windows estates increasingly include Linux build hosts, WSL-adjacent development workflows, Azure-hosted Linux services, GitHub-driven CI, and container platforms that never show up in the old desktop-server mental model. A flaw in an image-fetching path can therefore matter to a Windows shop even if no Windows endpoint is directly affected.
The Microsoft Knowledge Base disclaimer attached to the entry is boilerplate, but the publication channel is still useful. It places an open-source infrastructure bug into the same operational stream many enterprises already monitor. That helps security teams catch issues that live outside their primary vendor comfort zone.
The risk is that teams misread the context. This is not something to hunt for on every Windows laptop. It is something to look for wherever Incus is used to run containers or virtual machines, especially in shared build and test infrastructure.
The LXD Echo Makes the Bug Harder to Ignore
Incus and LXD have an intertwined history, and the appearance of related release-note language in LXD circles is a reminder that security fixes do not always stay confined to one project name. When a codebase, protocol, or design assumption crosses project boundaries, the vulnerability-management task becomes broader than “patch the product named in the CVE.”That does not mean every LXD deployment is automatically vulnerable in the same way or on the same timeline. It does mean administrators should read their distribution and vendor advisories carefully instead of treating CVE titles as complete inventories. Packaging, backports, snaps, distro builds, and forked implementations can all move at different speeds.
For enterprise IT, this is where asset management earns its keep. Knowing that “we use containers” is not enough. Teams need to know whether they run Incus, LXD, distro-packaged variants, snap packages, or managed services that abstract the whole thing away.
The practical question is not whether the CVE has a frightening name. The practical question is whether any platform in the organization downloads images from simplestreams servers into a shared cache that other users trust.
The Patch Fixes the Bug; the Architecture Decides the Blast Radius
Incus 6.23.0 fixes the validation flaw by checking the full image hash against the expected fingerprint. That is the clean technical answer. If you operate Incus, update to a patched build and verify that every node in a cluster has received the fix.But patching alone should not be the end of the response. A bug like this exposes whether an organization has been relying on artifact integrity checks as a substitute for source governance. Those are not the same thing.
Source governance says ordinary tenants cannot make the infrastructure pull from arbitrary image servers. Integrity checking says the thing fetched matches the thing described. You need both. One limits who gets to introduce artifacts into the trust domain; the other ensures the artifact has not shifted identity on the way in.
The advisory’s own mitigation logic is therefore unusually useful. Environments already using
restricted.image.servers, firewall egress rules, or proxy-based allow lists were positioned far better than those treating public image discovery as an open-ended feature. That is a design win, not just a configuration checkbox.Security Scanners Will See a CVE; Operators Should See a Supply Chain
Vulnerability scanners are good at turning CVEs into tickets. They are less good at explaining whether a bug changes the security model of a platform. CVE-2026-33542 deserves a ticket, but it also deserves a short architecture review.The reason is simple: images are supply-chain artifacts. A base image is often the first executable layer in an environment. It may contain shells, package managers, init scripts, cloud-init behavior, certificates, default users, and hooks that later automation assumes are clean.
If a malicious image enters that pipeline under a trusted identity, every layer above it becomes suspect. Secrets mounted into a container, build credentials used during CI, internal network access granted to a test VM, and telemetry collected by agents can all become part of the attacker’s opportunity surface.
That does not mean every vulnerable Incus environment was compromised. The attack conditions are constrained enough that panic would be misplaced. But complacency would be just as misplaced, because this is exactly the kind of low-drama infrastructure bug that can become high-impact in the wrong topology.
The Admin’s Short List Is Smaller Than the Advisory
The operational response does not need to be theatrical. It needs to be disciplined. Treat the CVE as a prompt to align the software version, the image-source policy, and the cache state.- Upgrade Incus installations to version 6.23.0 or a vendor build that includes the equivalent fix.
- Confirm that multi-tenant projects restrict image sources through
restricted.image.servers, firewall rules, or an HTTP proxy allow list. - Review whether untrusted users could previously add or use arbitrary simplestreams remotes in shared environments.
- Refresh or remove cached images if there is reason to believe untrusted image sources were used before the patch.
- Pay special attention to CI, build farms, training labs, and ephemeral-instance platforms where image names and launch timing are predictable.
- Track related downstream advisories for packaged Incus or LXD-derived components rather than assuming the upstream CVE name tells the whole story.
CVE-2026-33542 will not be remembered as the vulnerability that broke container security, and that is precisely why it is worth studying. The industry’s most durable failures often arrive as small mismatches between what a platform verifies and what its users believe has been verified. Incus has patched that mismatch, but the next version of this bug will appear wherever shared infrastructure turns downloads into trusted execution; the winning teams will be the ones that treat image sources, caches, and fingerprints as one security boundary rather than three separate chores.
Source: MSRC Security Update Guide - Microsoft Security Response Center