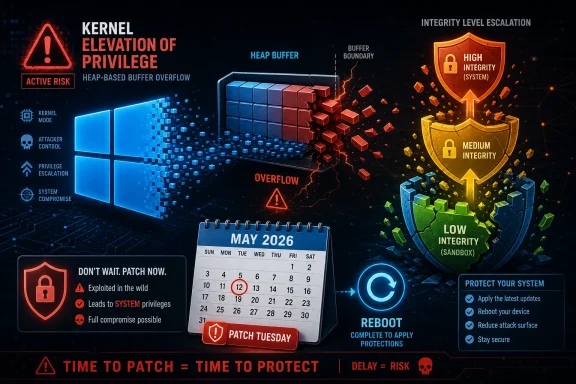
Microsoft published CVE-2026-33841 on May 12, 2026, as an Important Windows Kernel elevation-of-privilege vulnerability caused by a heap-based buffer overflow that lets an authorized local attacker raise privileges on affected Windows client and server systems. The bug is not described as publicly disclosed or exploited in the wild, but Microsoft rates exploitation as “more likely,” which is the detail that should keep administrators from treating it as just another low-drama Patch Tuesday entry. This is not a remote wormable panic story; it is the quieter and often more operationally useful kind of Windows flaw. In modern intrusions, local privilege escalation is the bridge between “we got a foothold” and “we own the box.”
The public description of CVE-2026-33841 is almost aggressively brief: a heap-based buffer overflow in the Windows Kernel allows an authorized attacker to elevate privileges locally. That sentence does not name the exact vulnerable code path, the affected binary, or a reliable trigger condition. It also does not hand defenders a behavioral detection recipe.
But sparse language is not the same thing as weak signal. Microsoft assigns the vulnerability a CVSS 3.1 base score of 7.8, with local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, and high confidentiality, integrity, and availability impact. That combination tells a familiar Windows security story: the attacker must already be able to run code locally, but once there, the flaw may let them break out of the user-level lane.
The more important clue is Microsoft’s exploitability assessment. CVE-2026-33841 is listed as “Exploitation More Likely” for the latest software release, while Microsoft says it has not seen public disclosure or active exploitation at publication time. That is the uncomfortable middle ground for defenders: not a confirmed zero-day, but not a theoretical paper cut either.
For WindowsForum readers, the practical distinction matters. A remote code execution bug can be the initial breach. A kernel elevation-of-privilege bug is what turns that breach into administrative control, credential theft, endpoint tampering, security-tool disablement, or persistence that survives the obvious cleanup steps.
An attacker who lands inside a browser renderer, a sandboxed document viewer, a low-privilege account, or a constrained app environment still has a problem. Windows intentionally surrounds those contexts with boundaries: token privileges, integrity levels, AppContainer restrictions, service isolation, and kernel-enforced access checks. CVE-2026-33841 is notable because Microsoft’s own FAQ says successful exploitation could move an attacker from a Low Integrity Level in a contained, sandboxed execution environment to Medium or High Integrity Level.
That is a sharper impact statement than the generic “could gain SYSTEM” boilerplate seen in many Windows kernel advisories. It suggests the security boundary at issue is not merely standard user-to-admin in the everyday sense, but also sandbox escape or sandbox weakening in environments where low-integrity code is expected to be contained.
This is where the vulnerability becomes strategically interesting. Windows has spent years pushing more application activity into constrained contexts, from UWP and AppContainer-based models to browser sandboxes and newer Win32 isolation efforts. If a kernel bug helps code climb out of that low-integrity box, the risk is less about one obscure kernel memory issue and more about the durability of Windows’ layered containment model.
For enterprises, “Important” kernel EoP bugs can be the vulnerabilities that matter most after initial access. A phishing attachment that gets code running as a user is bad. A phishing attachment plus a reliable kernel privilege escalation is worse, because the attacker can move from user context to stronger local control before endpoint tooling or least-privilege policy has a chance to contain the damage.
The same logic applies to consumer systems. A malicious installer, pirated software package, game mod, browser exploit, or compromised updater does not need administrator rights if it can bring its own path upward. The whole point of user account control, standard-user operation, and sandboxing is to force malware to work harder. Kernel EoP vulnerabilities reduce that friction.
Microsoft’s “more likely” exploitability rating is therefore the piece to watch. It does not mean exploitation is happening today. It means Microsoft believes the vulnerability’s characteristics make exploit development plausible enough that customers should not assume obscurity will protect them.
In user-mode software, modern mitigations have made many heap bugs harder to exploit reliably. In kernel-mode code, the stakes are higher because the corrupted memory belongs to the operating system’s most privileged execution environment. A successful exploit may be able to influence kernel objects, tokens, function pointers, or other sensitive structures depending on where the overflow occurs and how deterministic the surrounding memory layout is.
None of that should be read as a claim that CVE-2026-33841 has a public proof of concept or a known exploit technique. Microsoft has not published those details, and that omission is deliberate. The Security Update Guide is designed to help defenders prioritize, not to provide exploit developers with a cookbook.
Still, the combination of heap overflow, local privilege escalation, low attack complexity, and low privileges required is enough to warrant attention. Memory-safety bugs in kernel code are difficult to eliminate completely, and attackers have a long history of turning them into reliable post-compromise tools when the affected interface is reachable from unprivileged code.
Mandatory Integrity Control is one of Windows’ mechanisms for limiting what lower-trust processes can do, even when discretionary access control might otherwise allow access. Low-integrity processes are restricted from writing to medium-integrity objects, and AppContainer-style isolation adds another layer by limiting which resources an app can touch at all. In ordinary terms, low-integrity code is supposed to be boxed in.
A vulnerability that helps low-integrity code rise to medium or high integrity is not merely “local admin by another route.” It weakens the defensive assumption behind sandboxes: that risky code can execute, parse hostile inputs, or handle untrusted content without being able to alter the rest of the user’s environment.
That matters for browsers, packaged apps, document handling, and any enterprise workflow that relies on containment rather than perfect prevention. Security architects do not assume all code is benign. They assume some code will be compromised and then try to keep the blast radius small. CVE-2026-33841 is the kind of bug that challenges the blast-radius calculation.
The distinction between Medium and High Integrity also matters. Medium integrity is the normal standard-user desktop context. High integrity is associated with elevated administrator operations. A path from Low to Medium may be enough to escape a sandbox and access user data. A path to High raises the possibility of broader system modification, depending on the account, policy, and exploit chain.
That breadth tells administrators two things. First, this is not a niche Windows 11 regression confined to a new branch. Second, mixed estates will need coordinated patching across client and server generations, including machines that are already in the awkward Windows 10 transition zone.
The KB mapping is also scattered in the way Windows patch teams know too well. Windows 11 23H2 receives KB5087420. Windows 11 24H2 and 25H2 receive KB5089549, with hotpatch KB5089466 also listed for eligible systems. Windows 11 26H1 receives KB5089548. Windows Server 2022 receives KB5087545, with hotpatch KB5087424 listed. Windows Server 2025 receives KB5087539, with hotpatch KB5087423 listed. Windows Server 2022 23H2 Server Core receives KB5087541. Windows 10 21H2 and 22H2 receive KB5087544.
The common operational point is simpler than the KB matrix: Microsoft marks customer action as required and reboot required across the listed updates. This is not a Defender signature update or a policy tweak. It is kernel-level patching, and that means restart planning.
For home users, the answer is easy: let Windows Update install the May 2026 security update and reboot. For administrators, the answer is less glamorous: test against business-critical software, deploy through rings, watch known-issue notes for the relevant KB, and do not let “not exploited yet” become the excuse that leaves privilege escalation sitting open on every endpoint.
But CVE-2026-33841 also illustrates the limits of that story. Microsoft still lists reboot required in the affected-product entries, including the hotpatch rows returned by the advisory data. Administrators should therefore treat hotpatch availability as environment-specific relief, not as a universal escape from maintenance windows.
That distinction matters because reboot avoidance is one of the biggest sources of patch lag in the real world. Servers host workloads. Laptops are sleeping, traveling, or waiting on VPN. Kiosks and point-of-sale systems sit behind operational rules written by people who do not think in CVSS vectors. Security teams can approve an update on Tuesday and still be living with vulnerable machines weeks later.
A kernel EoP bug marked “more likely” is precisely the sort of issue that punishes that lag. Attackers do not need every machine vulnerable forever. They need enough unpatched systems to make privilege escalation a reusable step in their playbook.
That does not mean every technical detail is public. In fact, the public advisory leaves out the most exploitable details by design. But vendor confirmation changes the decision-making calculus. Defenders do not need a GitHub proof of concept to justify patching when the affected vendor has shipped fixes, assigned a concrete weakness category, and marked exploitation more likely.
There is a double edge here. The same confirmation that helps defenders prioritize also helps attackers triage. A newly patched kernel EoP with a clear CVSS vector, CWE classification, affected build list, and patch availability becomes a target for patch diffing. Researchers and adversaries alike can compare pre-patch and post-patch binaries to infer the vulnerable code path.
That is why the first days after Patch Tuesday matter. The public may not have exploit details at release time, but the patch itself begins to reveal them to anyone with the skill and motivation to reverse engineer the change. When Microsoft says exploitation is more likely, it is partly acknowledging the reality that exploitability is not frozen at the moment of publication.
Kernel updates deserve testing because the kernel is shared by everything. Endpoint detection agents, VPN clients, disk encryption, virtualization stacks, anti-cheat drivers, storage filters, and legacy business software can all make kernel patching feel higher-risk than application updates. That reality is why many administrators flinch when a kernel CVE appears in the monthly bundle.
But the alternative is not stability. It is unpatched kernel attack surface. In an environment where phishing, token theft, exposed remote access, and software supply-chain compromises are all plausible initial-access routes, local privilege escalation turns into a multiplier. The machine that might have been contained as a standard user becomes a foothold with teeth.
The right response is not panic-patching production domain controllers at random. It is disciplined acceleration. Validate the update on representative hardware and workload profiles, track failures quickly, and move the patch through the estate before exploit code matures.
For virtual desktop infrastructure, shared workstations, developer machines, jump boxes, and administrative endpoints, the urgency is higher. Those systems either host many user contexts or touch privileged workflows. If a low-privilege foothold on one of them can climb integrity levels, the downstream damage can be disproportionate.
The relevant question is not “Can a stranger across the Internet exploit this directly?” The relevant question is “If something untrusted runs on my machine, can it become more powerful than it should be?” CVE-2026-33841 is a yes-shaped advisory.
The fix path for consumers is straightforward. Install the May 2026 cumulative update for the Windows version you run, restart when prompted, and resist the temptation to pause updates indefinitely because the machine is “working fine.” Security updates are not feature updates in disguise, even if they sometimes arrive in the same monthly package with quality fixes and occasional annoyances.
Windows 10 users face an additional strategic issue. With Windows 10 now moving through its extended support and Extended Security Updates reality, the cost of staying put is becoming more visible. CVE-2026-33841 receiving Windows 10 fixes is good news for covered systems, but the long-term direction is clear: the older platform is becoming a managed exception rather than the default Windows future.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Wording Is Sparse, but the Risk Signal Is Not
Microsoft’s Wording Is Sparse, but the Risk Signal Is Not
The public description of CVE-2026-33841 is almost aggressively brief: a heap-based buffer overflow in the Windows Kernel allows an authorized attacker to elevate privileges locally. That sentence does not name the exact vulnerable code path, the affected binary, or a reliable trigger condition. It also does not hand defenders a behavioral detection recipe.But sparse language is not the same thing as weak signal. Microsoft assigns the vulnerability a CVSS 3.1 base score of 7.8, with local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, and high confidentiality, integrity, and availability impact. That combination tells a familiar Windows security story: the attacker must already be able to run code locally, but once there, the flaw may let them break out of the user-level lane.
The more important clue is Microsoft’s exploitability assessment. CVE-2026-33841 is listed as “Exploitation More Likely” for the latest software release, while Microsoft says it has not seen public disclosure or active exploitation at publication time. That is the uncomfortable middle ground for defenders: not a confirmed zero-day, but not a theoretical paper cut either.
For WindowsForum readers, the practical distinction matters. A remote code execution bug can be the initial breach. A kernel elevation-of-privilege bug is what turns that breach into administrative control, credential theft, endpoint tampering, security-tool disablement, or persistence that survives the obvious cleanup steps.
The Kernel Bug That Starts After the First Mistake
Elevation-of-privilege vulnerabilities are sometimes underrated because they do not usually provide the first click, phish, exploit, or exposed service compromise. That framing misunderstands how Windows intrusions actually unfold. Attack chains are built out of components, and local privilege escalation is one of the components attackers prize most.An attacker who lands inside a browser renderer, a sandboxed document viewer, a low-privilege account, or a constrained app environment still has a problem. Windows intentionally surrounds those contexts with boundaries: token privileges, integrity levels, AppContainer restrictions, service isolation, and kernel-enforced access checks. CVE-2026-33841 is notable because Microsoft’s own FAQ says successful exploitation could move an attacker from a Low Integrity Level in a contained, sandboxed execution environment to Medium or High Integrity Level.
That is a sharper impact statement than the generic “could gain SYSTEM” boilerplate seen in many Windows kernel advisories. It suggests the security boundary at issue is not merely standard user-to-admin in the everyday sense, but also sandbox escape or sandbox weakening in environments where low-integrity code is expected to be contained.
This is where the vulnerability becomes strategically interesting. Windows has spent years pushing more application activity into constrained contexts, from UWP and AppContainer-based models to browser sandboxes and newer Win32 isolation efforts. If a kernel bug helps code climb out of that low-integrity box, the risk is less about one obscure kernel memory issue and more about the durability of Windows’ layered containment model.
“Important” Is Not a Synonym for “Later”
Microsoft rates CVE-2026-33841 as Important, not Critical. That is technically consistent with the CVSS vector: the flaw requires local access and low privileges, and it does not cross security scope in the CVSS sense. But severity labels often compress too much operational nuance into a single word.For enterprises, “Important” kernel EoP bugs can be the vulnerabilities that matter most after initial access. A phishing attachment that gets code running as a user is bad. A phishing attachment plus a reliable kernel privilege escalation is worse, because the attacker can move from user context to stronger local control before endpoint tooling or least-privilege policy has a chance to contain the damage.
The same logic applies to consumer systems. A malicious installer, pirated software package, game mod, browser exploit, or compromised updater does not need administrator rights if it can bring its own path upward. The whole point of user account control, standard-user operation, and sandboxing is to force malware to work harder. Kernel EoP vulnerabilities reduce that friction.
Microsoft’s “more likely” exploitability rating is therefore the piece to watch. It does not mean exploitation is happening today. It means Microsoft believes the vulnerability’s characteristics make exploit development plausible enough that customers should not assume obscurity will protect them.
Heap Corruption Still Has Teeth in a Hardened Windows World
CVE-2026-33841 is classified as CWE-122, a heap-based buffer overflow. That phrase is old enough to feel almost retro, but it remains one of the classic routes from memory corruption to privilege escalation. A heap overflow occurs when software writes more data than a heap-allocated buffer is meant to hold, corrupting adjacent memory structures.In user-mode software, modern mitigations have made many heap bugs harder to exploit reliably. In kernel-mode code, the stakes are higher because the corrupted memory belongs to the operating system’s most privileged execution environment. A successful exploit may be able to influence kernel objects, tokens, function pointers, or other sensitive structures depending on where the overflow occurs and how deterministic the surrounding memory layout is.
None of that should be read as a claim that CVE-2026-33841 has a public proof of concept or a known exploit technique. Microsoft has not published those details, and that omission is deliberate. The Security Update Guide is designed to help defenders prioritize, not to provide exploit developers with a cookbook.
Still, the combination of heap overflow, local privilege escalation, low attack complexity, and low privileges required is enough to warrant attention. Memory-safety bugs in kernel code are difficult to eliminate completely, and attackers have a long history of turning them into reliable post-compromise tools when the affected interface is reachable from unprivileged code.
The Sandbox Detail Changes the Story
The most revealing part of Microsoft’s advisory is not the headline. It is the FAQ language about moving from Low Integrity Level in a contained execution environment to Medium or High Integrity Level. That places CVE-2026-33841 squarely in the Windows integrity model.Mandatory Integrity Control is one of Windows’ mechanisms for limiting what lower-trust processes can do, even when discretionary access control might otherwise allow access. Low-integrity processes are restricted from writing to medium-integrity objects, and AppContainer-style isolation adds another layer by limiting which resources an app can touch at all. In ordinary terms, low-integrity code is supposed to be boxed in.
A vulnerability that helps low-integrity code rise to medium or high integrity is not merely “local admin by another route.” It weakens the defensive assumption behind sandboxes: that risky code can execute, parse hostile inputs, or handle untrusted content without being able to alter the rest of the user’s environment.
That matters for browsers, packaged apps, document handling, and any enterprise workflow that relies on containment rather than perfect prevention. Security architects do not assume all code is benign. They assume some code will be compromised and then try to keep the blast radius small. CVE-2026-33841 is the kind of bug that challenges the blast-radius calculation.
The distinction between Medium and High Integrity also matters. Medium integrity is the normal standard-user desktop context. High integrity is associated with elevated administrator operations. A path from Low to Medium may be enough to escape a sandbox and access user data. A path to High raises the possibility of broader system modification, depending on the account, policy, and exploit chain.
Windows 10’s Extended Life Complicates the Patch Picture
The affected-product list is broad. Microsoft lists Windows 11 versions 23H2, 24H2, 25H2, and 26H1, along with Windows Server 2022, Windows Server 2022 23H2 Server Core, and Windows Server 2025. Windows 10 versions 21H2 and 22H2 also appear, with Windows 10 22H2 entries marked under the Extended Security Updates family.That breadth tells administrators two things. First, this is not a niche Windows 11 regression confined to a new branch. Second, mixed estates will need coordinated patching across client and server generations, including machines that are already in the awkward Windows 10 transition zone.
The KB mapping is also scattered in the way Windows patch teams know too well. Windows 11 23H2 receives KB5087420. Windows 11 24H2 and 25H2 receive KB5089549, with hotpatch KB5089466 also listed for eligible systems. Windows 11 26H1 receives KB5089548. Windows Server 2022 receives KB5087545, with hotpatch KB5087424 listed. Windows Server 2025 receives KB5087539, with hotpatch KB5087423 listed. Windows Server 2022 23H2 Server Core receives KB5087541. Windows 10 21H2 and 22H2 receive KB5087544.
The common operational point is simpler than the KB matrix: Microsoft marks customer action as required and reboot required across the listed updates. This is not a Defender signature update or a policy tweak. It is kernel-level patching, and that means restart planning.
For home users, the answer is easy: let Windows Update install the May 2026 security update and reboot. For administrators, the answer is less glamorous: test against business-critical software, deploy through rings, watch known-issue notes for the relevant KB, and do not let “not exploited yet” become the excuse that leaves privilege escalation sitting open on every endpoint.
Hotpatching Helps, but It Does Not Erase the Calendar
The presence of hotpatch updates for some Windows 11 and Windows Server builds is worth noting. Microsoft has been pushing hotpatching as a way to reduce restart pressure, particularly for modern server scenarios and eligible Windows editions. In theory, that is exactly the kind of mechanism that should make kernel-security maintenance less painful.But CVE-2026-33841 also illustrates the limits of that story. Microsoft still lists reboot required in the affected-product entries, including the hotpatch rows returned by the advisory data. Administrators should therefore treat hotpatch availability as environment-specific relief, not as a universal escape from maintenance windows.
That distinction matters because reboot avoidance is one of the biggest sources of patch lag in the real world. Servers host workloads. Laptops are sleeping, traveling, or waiting on VPN. Kiosks and point-of-sale systems sit behind operational rules written by people who do not think in CVSS vectors. Security teams can approve an update on Tuesday and still be living with vulnerable machines weeks later.
A kernel EoP bug marked “more likely” is precisely the sort of issue that punishes that lag. Attackers do not need every machine vulnerable forever. They need enough unpatched systems to make privilege escalation a reusable step in their playbook.
The Advisory’s Confidence Metric Is a Warning About What Attackers Know
The user-submitted context around this CVE points to a key scoring idea: confidence in the existence of the vulnerability and credibility of known technical details. Microsoft’s CVSS vector ends with RC:C, meaning report confidence is complete. In plain English, this is not a rumor, a disputed researcher claim, or a vague undesirable behavior. The vendor confirms the issue.That does not mean every technical detail is public. In fact, the public advisory leaves out the most exploitable details by design. But vendor confirmation changes the decision-making calculus. Defenders do not need a GitHub proof of concept to justify patching when the affected vendor has shipped fixes, assigned a concrete weakness category, and marked exploitation more likely.
There is a double edge here. The same confirmation that helps defenders prioritize also helps attackers triage. A newly patched kernel EoP with a clear CVSS vector, CWE classification, affected build list, and patch availability becomes a target for patch diffing. Researchers and adversaries alike can compare pre-patch and post-patch binaries to infer the vulnerable code path.
That is why the first days after Patch Tuesday matter. The public may not have exploit details at release time, but the patch itself begins to reveal them to anyone with the skill and motivation to reverse engineer the change. When Microsoft says exploitation is more likely, it is partly acknowledging the reality that exploitability is not frozen at the moment of publication.
Enterprise Risk Lives in the Gaps Between Rings
The best-run Windows shops already have patch rings: canaries, pilot groups, broad deployment, and exceptions. CVE-2026-33841 does not require abandoning that discipline. It does require making sure the rings are measured in days, not months.Kernel updates deserve testing because the kernel is shared by everything. Endpoint detection agents, VPN clients, disk encryption, virtualization stacks, anti-cheat drivers, storage filters, and legacy business software can all make kernel patching feel higher-risk than application updates. That reality is why many administrators flinch when a kernel CVE appears in the monthly bundle.
But the alternative is not stability. It is unpatched kernel attack surface. In an environment where phishing, token theft, exposed remote access, and software supply-chain compromises are all plausible initial-access routes, local privilege escalation turns into a multiplier. The machine that might have been contained as a standard user becomes a foothold with teeth.
The right response is not panic-patching production domain controllers at random. It is disciplined acceleration. Validate the update on representative hardware and workload profiles, track failures quickly, and move the patch through the estate before exploit code matures.
For virtual desktop infrastructure, shared workstations, developer machines, jump boxes, and administrative endpoints, the urgency is higher. Those systems either host many user contexts or touch privileged workflows. If a low-privilege foothold on one of them can climb integrity levels, the downstream damage can be disproportionate.
Consumers Should Not Wait for Exploit Headlines
Home users often hear “local attacker” and assume the issue does not apply to them unless someone has physical access to the PC. That is the wrong mental model. Local exploitation can happen after malware, a malicious script, a compromised app, or a browser-delivered payload gains execution as the current user.The relevant question is not “Can a stranger across the Internet exploit this directly?” The relevant question is “If something untrusted runs on my machine, can it become more powerful than it should be?” CVE-2026-33841 is a yes-shaped advisory.
The fix path for consumers is straightforward. Install the May 2026 cumulative update for the Windows version you run, restart when prompted, and resist the temptation to pause updates indefinitely because the machine is “working fine.” Security updates are not feature updates in disguise, even if they sometimes arrive in the same monthly package with quality fixes and occasional annoyances.
Windows 10 users face an additional strategic issue. With Windows 10 now moving through its extended support and Extended Security Updates reality, the cost of staying put is becoming more visible. CVE-2026-33841 receiving Windows 10 fixes is good news for covered systems, but the long-term direction is clear: the older platform is becoming a managed exception rather than the default Windows future.
The May Kernel Patch Deserves a Shorter Fuse
CVE-2026-33841 is not the loudest kind of vulnerability, but it is the kind defenders regret ignoring. It is confirmed by Microsoft, patched in the May 2026 security release, classified as a heap-based Windows Kernel flaw, and assessed as more likely to be exploited despite no known public exploitation at release.- Organizations should prioritize deployment of the relevant May 2026 Windows security update because Microsoft marks customer action as required and exploitation as more likely.
- Administrators should treat the bug as a post-compromise accelerator, especially on endpoints where users, browsers, document tools, and sandboxed applications handle untrusted content.
- Security teams should pay particular attention to systems where low-integrity or AppContainer isolation is part of the defense model, because Microsoft describes potential movement from Low Integrity Level to Medium or High Integrity Level.
- Patch planning should include reboots or hotpatch eligibility checks rather than assuming the update can be absorbed silently.
- Windows 10 systems should be reviewed carefully for support and ESU coverage, because the affected list includes Windows 10 21H2 and 22H2 entries but the platform’s lifecycle is no longer business as usual.
- Detection teams should watch for suspicious local privilege-escalation behavior after initial access, but they should not treat monitoring as a substitute for removing the vulnerable kernel path.
Source: MSRC Security Update Guide - Microsoft Security Response Center