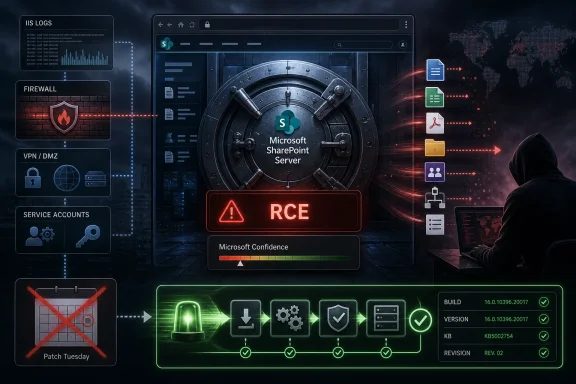
Microsoft’s Security Update Guide entry for CVE-2026-40368 identifies a Microsoft SharePoint Server remote code execution vulnerability, and the most important early signal is not just the RCE label but the confidence Microsoft is attaching to the underlying report. That distinction matters because SharePoint flaws live in the awkward middle of enterprise security: too business-critical to casually take offline, too internet-adjacent to ignore, and too historically attractive to attackers to treat as a paperwork exercise. The lesson for Windows administrators is blunt: when Microsoft publishes a SharePoint Server RCE with confirmed technical confidence, the clock starts before exploit chatter becomes comfortable.
SharePoint Server occupies a peculiar place in Microsoft’s ecosystem. It is no longer the glamorous collaboration story Microsoft tells when it talks about cloud productivity, yet it remains embedded in document workflows, intranets, records systems, legacy integrations, and custom line-of-business applications across government, education, healthcare, manufacturing, and finance.
That is exactly why SharePoint Server vulnerabilities punch above their weight. A compromised SharePoint instance is rarely just a compromised web app. It can be a map of business process, identity assumptions, document permissions, service accounts, workflow engines, and the kind of trusted internal plumbing that defenders often discover only after attackers have already used it.
CVE-2026-40368 arrives in that context. Microsoft’s label — remote code execution in Microsoft SharePoint Server — is the part that will draw the dashboard alerts. But the more subtle signal in the user-supplied metric text is about confidence: how sure the ecosystem is that the vulnerability exists, how credible the known technical details are, and how much an attacker can infer from what has been published.
That is not a bureaucratic footnote. It is the difference between a theoretical weakness that may never leave a spreadsheet and a confirmed bug whose existence can guide exploit development even before a public proof-of-concept appears.
The wording is careful. Sometimes a vulnerability is public only in outline: a product is affected, an impact is undesirable, but the root cause is unknown. Sometimes outside research narrows the field without proving the mechanism. And sometimes the vendor or author confirms the flaw, which changes the operational temperature.
For CVE-2026-40368, the fact that Microsoft has an MSRC entry is itself significant. It does not automatically mean public exploit code exists, and it does not mean every SharePoint Server deployment is equally exposed. It does mean administrators should stop treating the vulnerability as rumor and start treating it as a vendor-recognized risk item in the patch queue.
The metric also points to a second-order problem: attackers do not need a full write-up to make progress. A confirmed product, impact class, and affected component family can be enough to focus reverse engineering, diff patches, build probes, and compare vulnerable and fixed binaries. In the SharePoint world, that kind of narrowing can be especially valuable because the target population is smaller than Windows itself but often richer in organizational value.
The details matter, and responsible defenders should not fill gaps with fantasy. Some SharePoint RCEs require authentication. Some require particular privileges. Some need a crafted request, a malicious file, a chained weakness, or a server configuration that exposes a risky path. The absence of those specifics in early public summaries is exactly why the confidence metric matters: it tells you how far the public record has progressed without pretending every exploit condition is known.
Still, SharePoint’s role makes any RCE especially sensitive. The platform often sits behind load balancers, reverse proxies, federation services, custom web parts, search integrations, and workflow dependencies. It may also hold secrets that are not obvious to a vulnerability scanner: connection strings, cached credentials, integration tokens, legacy service accounts, and sensitive documents whose permissions have accreted over years.
That is why the risk conversation should not stop at “is it internet-facing?” Internal-only SharePoint servers are not harmless. They may be reachable by VPN users, contractors, compromised endpoints, branch networks, legacy application servers, or identity paths that no one has diagrammed since the migration project ended.
That distinction is easy to understate. Many organizations say they are “on SharePoint” when they mean a hybrid tangle of SharePoint Online sites, legacy SharePoint Server farms, archived portals, custom workflows, and departmental systems that nobody wants to own. Attackers do not care which part the roadmap says should have been retired.
CVE-2026-40368 therefore lands as another reminder that on-premises collaboration infrastructure is not simply old software; it is old software with current business trust. If it still authenticates users, serves documents, runs workflows, or connects to internal data, it belongs in the same risk conversation as VPN appliances, identity servers, and externally reachable management consoles.
The uncomfortable truth is that many SharePoint Server farms are hard to patch precisely because they matter. They host workflows that break when cumulative updates shift behavior. They depend on third-party components that have not been tested against the latest build. They serve departments that have executive visibility and little tolerance for downtime. That friction is why confirmed RCEs in SharePoint should not wait for the next leisurely maintenance cycle.
This is where enterprise reality intrudes. SharePoint patching is not the same as updating a single desktop application. Farms can include multiple web front ends, application servers, search roles, distributed cache dependencies, and database relationships. A half-patched farm is not a comforting middle state; it is often a new troubleshooting ticket waiting to happen.
Administrators should also assume that public disclosure compresses timelines. Once a vendor advisory exists, defenders are not the only people reading it. Attackers can monitor update releases, compare files, and build targeting logic around organizations that historically lag on patching. The exploitability of CVE-2026-40368 may depend on technical specifics not visible in the prompt, but the strategic pattern is familiar enough: patch gaps become attacker inventory.
The right operational posture is therefore staged urgency. Test quickly, deploy deliberately, and verify aggressively. A failed patch is not security. A delayed patch is not stability. The art is in reducing both forms of risk without pretending one of them does not exist.
Those systems are where CVE entries become incidents. Modern security programs often have decent visibility into Windows endpoints and cloud identities, but older application servers sit in a gray zone between infrastructure, collaboration, and business ownership. Nobody argues that they are unimportant; everyone argues that someone else owns the upgrade plan.
SharePoint compounds the problem because it is both platform and application. A vulnerability in the server product may affect a farm whose business value comes from custom code, document libraries, workflows, and integrations that are not described anywhere in a CMDB. Patching is then treated as an application change, not an infrastructure hygiene task, and the delay expands.
CVE-2026-40368 should push organizations to revisit that ownership model. If a SharePoint Server can execute code, access sensitive documents, authenticate users, and connect to internal services, then it is security-critical infrastructure. The business can own the content and workflows, but IT and security must own the exposure, update cadence, and retirement path.
That is the point of vendor acknowledgement. Microsoft’s recognition of a CVE does not hand defenders every exploit detail, but it confirms that the issue belongs in a real remediation process. For SharePoint Server, that means inventory, exposure review, patch validation, log review, and executive communication if the farm supports critical business functions.
It also means being careful with public exploit assumptions. If there is no confirmed in-the-wild exploitation for a given CVE, say that plainly. If there is no public proof-of-concept, do not invent one. But do not confuse the absence of public exploit code with the absence of attacker interest. SharePoint Server has already proven it can attract serious attention when a usable path appears.
The best security teams communicate that nuance well. They do not cry apocalypse over every advisory, and they do not wait for ransomware screenshots before acting. They explain that confidence in the vulnerability raises urgency because it reduces ambiguity, not because every possible exploit condition is already known.
Those questions sound basic because they are. They are also where many incident responses discover the real weakness was not the CVE but the inventory. A vulnerability cannot be remediated cleanly if the organization cannot say where the affected product runs.
The second step is prioritization by exposure and business blast radius. An externally reachable SharePoint farm with sensitive content deserves a different patch window from an isolated lab instance. A farm integrated with identity, workflow automation, or document management for regulated records deserves more attention than a stale archive with no active users. But “internal” should not be a magic word that downgrades urgency by default.
The third step is validation after action. SharePoint updates can require follow-up configuration steps, service checks, and farm health review. Security teams should ask not only whether the update was installed, but whether the farm is actually at the expected build level and functioning in the expected security state.
Detection should start with SharePoint and IIS logs, authentication patterns, unusual process creation, unexpected web-accessible files, suspicious changes to application directories, and anomalies in service account behavior. The exact indicators for CVE-2026-40368 depend on technical details Microsoft may publish or update over time, but the defensive habit is consistent: look for evidence of exploitation paths, not just evidence of missing patches.
Security teams should also review segmentation. A SharePoint server should not have casual reach into every internal subnet simply because it has been around for years. If compromise of the farm would provide a convenient bridge to databases, file shares, domain services, or management networks, the vulnerability is more than a SharePoint issue.
The better long-term answer is to reduce the privileges and network reach of these systems before the next CVE arrives. Least privilege, service account hygiene, egress restrictions, and monitored administrative access are not glamorous. They are what turn a server compromise from a domain-wide disaster into a contained incident.
SharePoint Server is a good example of why. The number of affected systems may be small, but each one can be strategically important. Waiting for the same cycle used for commodity endpoint updates can leave a disproportionate amount of risk sitting in a handful of servers.
This does not mean reckless patching. It means creating a separate lane for exposed, high-value server applications. That lane needs predefined owners, emergency test criteria, rollback plans, communication templates, and authority to move faster when Microsoft confirms a serious vulnerability. If those pieces are invented during the incident, the organization has already lost time.
CVE-2026-40368 should be treated as a test of that lane. If the organization cannot quickly identify its SharePoint Server estate, assess exposure, test the update, deploy safely, and verify completion, then the problem is bigger than one CVE. It is a process gap waiting for the next confirmed RCE.
But migration is not a magic eraser. Many SharePoint Server deployments exist because of custom workflows, data residency requirements, integrations, latency concerns, governance constraints, or plain institutional inertia. Moving that complexity to the cloud requires architecture, identity cleanup, permissions review, content rationalization, and political capital.
The right conclusion is not “everyone must migrate tomorrow.” It is that every remaining SharePoint Server should have a reason to exist. If the reason is strong, it deserves proper funding, patch engineering, monitoring, and lifecycle planning. If the reason is merely that nobody has had time to retire it, CVE-2026-40368 is another argument that the hidden cost of delay is rising.
A server kept for convenience can become a breach path. That is the brutal arithmetic of legacy collaboration infrastructure.
CVE-2026-40368 may ultimately prove to be a routine Microsoft server vulnerability, or it may become one of those SharePoint bugs administrators remember because attackers moved faster than change-control boards. The prudent position is to act before that distinction is settled in public. Microsoft’s confidence signal narrows the room for denial, and for anyone still running SharePoint Server, the next responsible move is to turn that signal into verified remediation rather than another item aging quietly in the vulnerability queue.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 SharePoint Is Still Where Old Enterprise Risk Meets New Attacker Speed
SharePoint Is Still Where Old Enterprise Risk Meets New Attacker Speed
SharePoint Server occupies a peculiar place in Microsoft’s ecosystem. It is no longer the glamorous collaboration story Microsoft tells when it talks about cloud productivity, yet it remains embedded in document workflows, intranets, records systems, legacy integrations, and custom line-of-business applications across government, education, healthcare, manufacturing, and finance.That is exactly why SharePoint Server vulnerabilities punch above their weight. A compromised SharePoint instance is rarely just a compromised web app. It can be a map of business process, identity assumptions, document permissions, service accounts, workflow engines, and the kind of trusted internal plumbing that defenders often discover only after attackers have already used it.
CVE-2026-40368 arrives in that context. Microsoft’s label — remote code execution in Microsoft SharePoint Server — is the part that will draw the dashboard alerts. But the more subtle signal in the user-supplied metric text is about confidence: how sure the ecosystem is that the vulnerability exists, how credible the known technical details are, and how much an attacker can infer from what has been published.
That is not a bureaucratic footnote. It is the difference between a theoretical weakness that may never leave a spreadsheet and a confirmed bug whose existence can guide exploit development even before a public proof-of-concept appears.
The Confidence Metric Is a Warning About Attacker Knowledge
The metric described in the prompt is the kind of scoring language security teams often skim past while hunting for the base score. That is a mistake. Base severity tells you what the vulnerability could do under the model’s assumptions; confidence tells you how solid the public case is and, by implication, how much useful information is already available to both defenders and attackers.The wording is careful. Sometimes a vulnerability is public only in outline: a product is affected, an impact is undesirable, but the root cause is unknown. Sometimes outside research narrows the field without proving the mechanism. And sometimes the vendor or author confirms the flaw, which changes the operational temperature.
For CVE-2026-40368, the fact that Microsoft has an MSRC entry is itself significant. It does not automatically mean public exploit code exists, and it does not mean every SharePoint Server deployment is equally exposed. It does mean administrators should stop treating the vulnerability as rumor and start treating it as a vendor-recognized risk item in the patch queue.
The metric also points to a second-order problem: attackers do not need a full write-up to make progress. A confirmed product, impact class, and affected component family can be enough to focus reverse engineering, diff patches, build probes, and compare vulnerable and fixed binaries. In the SharePoint world, that kind of narrowing can be especially valuable because the target population is smaller than Windows itself but often richer in organizational value.
Remote Code Execution Is the Label That Changes the Meeting
Remote code execution has become a phrase so familiar that it risks losing its force. In a SharePoint Server context, it should still change the meeting. RCE means the vulnerability is not merely about viewing data that should have been hidden or causing a service interruption; it means successful exploitation can cross into attacker-controlled execution on the server side.The details matter, and responsible defenders should not fill gaps with fantasy. Some SharePoint RCEs require authentication. Some require particular privileges. Some need a crafted request, a malicious file, a chained weakness, or a server configuration that exposes a risky path. The absence of those specifics in early public summaries is exactly why the confidence metric matters: it tells you how far the public record has progressed without pretending every exploit condition is known.
Still, SharePoint’s role makes any RCE especially sensitive. The platform often sits behind load balancers, reverse proxies, federation services, custom web parts, search integrations, and workflow dependencies. It may also hold secrets that are not obvious to a vulnerability scanner: connection strings, cached credentials, integration tokens, legacy service accounts, and sensitive documents whose permissions have accreted over years.
That is why the risk conversation should not stop at “is it internet-facing?” Internal-only SharePoint servers are not harmless. They may be reachable by VPN users, contractors, compromised endpoints, branch networks, legacy application servers, or identity paths that no one has diagrammed since the migration project ended.
Microsoft’s Cloud Escape Hatch Does Not Help the Server You Still Run
One of the recurring themes in modern Microsoft security is the divide between Microsoft 365 services and on-premises server products. SharePoint Online can be patched, monitored, and instrumented by Microsoft at cloud speed. SharePoint Server, by contrast, remains the customer’s operational problem: patch windows, farm topology, customizations, compatibility testing, backup discipline, and the uncomfortable question of who still understands the farm.That distinction is easy to understate. Many organizations say they are “on SharePoint” when they mean a hybrid tangle of SharePoint Online sites, legacy SharePoint Server farms, archived portals, custom workflows, and departmental systems that nobody wants to own. Attackers do not care which part the roadmap says should have been retired.
CVE-2026-40368 therefore lands as another reminder that on-premises collaboration infrastructure is not simply old software; it is old software with current business trust. If it still authenticates users, serves documents, runs workflows, or connects to internal data, it belongs in the same risk conversation as VPN appliances, identity servers, and externally reachable management consoles.
The uncomfortable truth is that many SharePoint Server farms are hard to patch precisely because they matter. They host workflows that break when cumulative updates shift behavior. They depend on third-party components that have not been tested against the latest build. They serve departments that have executive visibility and little tolerance for downtime. That friction is why confirmed RCEs in SharePoint should not wait for the next leisurely maintenance cycle.
Patch Management Is Only the First Defensive Act
The obvious answer to a Microsoft RCE is to apply the relevant security update. That answer is correct but incomplete. SharePoint has repeatedly shown that patching must be paired with operational verification: knowing which servers are in the farm, which build each one is running, whether the configuration wizard has completed successfully, and whether mitigations recommended by Microsoft actually took effect.This is where enterprise reality intrudes. SharePoint patching is not the same as updating a single desktop application. Farms can include multiple web front ends, application servers, search roles, distributed cache dependencies, and database relationships. A half-patched farm is not a comforting middle state; it is often a new troubleshooting ticket waiting to happen.
Administrators should also assume that public disclosure compresses timelines. Once a vendor advisory exists, defenders are not the only people reading it. Attackers can monitor update releases, compare files, and build targeting logic around organizations that historically lag on patching. The exploitability of CVE-2026-40368 may depend on technical specifics not visible in the prompt, but the strategic pattern is familiar enough: patch gaps become attacker inventory.
The right operational posture is therefore staged urgency. Test quickly, deploy deliberately, and verify aggressively. A failed patch is not security. A delayed patch is not stability. The art is in reducing both forms of risk without pretending one of them does not exist.
The Real Risk Is the Farm Nobody Wants to Own
The most vulnerable SharePoint Server in an organization is often not the most visible one. It is the old project portal kept alive for archived contracts. It is the departmental farm that predates central IT governance. It is the extranet instance whose owner left three reorganizations ago. It is the “temporary” server that became permanent because a business process quietly depended on it.Those systems are where CVE entries become incidents. Modern security programs often have decent visibility into Windows endpoints and cloud identities, but older application servers sit in a gray zone between infrastructure, collaboration, and business ownership. Nobody argues that they are unimportant; everyone argues that someone else owns the upgrade plan.
SharePoint compounds the problem because it is both platform and application. A vulnerability in the server product may affect a farm whose business value comes from custom code, document libraries, workflows, and integrations that are not described anywhere in a CMDB. Patching is then treated as an application change, not an infrastructure hygiene task, and the delay expands.
CVE-2026-40368 should push organizations to revisit that ownership model. If a SharePoint Server can execute code, access sensitive documents, authenticate users, and connect to internal services, then it is security-critical infrastructure. The business can own the content and workflows, but IT and security must own the exposure, update cadence, and retirement path.
Confidence Does Not Mean Complacency; It Means Less Room for Denial
The metric language in the prompt is useful because it captures a reality defenders sometimes resist. Early vulnerability information is uncertain, but uncertainty is not the same as safety. When confidence increases, the organization loses the ability to dismiss the issue as speculative.That is the point of vendor acknowledgement. Microsoft’s recognition of a CVE does not hand defenders every exploit detail, but it confirms that the issue belongs in a real remediation process. For SharePoint Server, that means inventory, exposure review, patch validation, log review, and executive communication if the farm supports critical business functions.
It also means being careful with public exploit assumptions. If there is no confirmed in-the-wild exploitation for a given CVE, say that plainly. If there is no public proof-of-concept, do not invent one. But do not confuse the absence of public exploit code with the absence of attacker interest. SharePoint Server has already proven it can attract serious attention when a usable path appears.
The best security teams communicate that nuance well. They do not cry apocalypse over every advisory, and they do not wait for ransomware screenshots before acting. They explain that confidence in the vulnerability raises urgency because it reduces ambiguity, not because every possible exploit condition is already known.
The Practical Playbook Starts With Boring Questions
For administrators, the first response to CVE-2026-40368 should not be a heroic all-nighter fueled by guesswork. It should be a short list of boring questions answered with evidence. Which SharePoint Server versions are still running? Which farms are internet-facing or reachable through partner access? Which servers have custom components? Which update level is installed? Which farms have current backups and tested restoration procedures?Those questions sound basic because they are. They are also where many incident responses discover the real weakness was not the CVE but the inventory. A vulnerability cannot be remediated cleanly if the organization cannot say where the affected product runs.
The second step is prioritization by exposure and business blast radius. An externally reachable SharePoint farm with sensitive content deserves a different patch window from an isolated lab instance. A farm integrated with identity, workflow automation, or document management for regulated records deserves more attention than a stale archive with no active users. But “internal” should not be a magic word that downgrades urgency by default.
The third step is validation after action. SharePoint updates can require follow-up configuration steps, service checks, and farm health review. Security teams should ask not only whether the update was installed, but whether the farm is actually at the expected build level and functioning in the expected security state.
Detection Has to Look Beyond the Advisory Page
Patching closes the known door, but defenders also need to ask whether anyone walked through before it closed. That is especially true when public confidence is high enough to create attacker interest and when the product involved is a server-side collaboration platform with access to sensitive content.Detection should start with SharePoint and IIS logs, authentication patterns, unusual process creation, unexpected web-accessible files, suspicious changes to application directories, and anomalies in service account behavior. The exact indicators for CVE-2026-40368 depend on technical details Microsoft may publish or update over time, but the defensive habit is consistent: look for evidence of exploitation paths, not just evidence of missing patches.
Security teams should also review segmentation. A SharePoint server should not have casual reach into every internal subnet simply because it has been around for years. If compromise of the farm would provide a convenient bridge to databases, file shares, domain services, or management networks, the vulnerability is more than a SharePoint issue.
The better long-term answer is to reduce the privileges and network reach of these systems before the next CVE arrives. Least privilege, service account hygiene, egress restrictions, and monitored administrative access are not glamorous. They are what turn a server compromise from a domain-wide disaster into a contained incident.
The Patch Tuesday Ritual Is Too Slow for Server-Side RCEs
Many organizations still process Microsoft security updates through a monthly ritual built around predictability. That model works tolerably well for broad fleets of user endpoints where staged rings, rollback planning, and compatibility checks are essential. It works less well when a server-side RCE affects a high-value application reachable over the network.SharePoint Server is a good example of why. The number of affected systems may be small, but each one can be strategically important. Waiting for the same cycle used for commodity endpoint updates can leave a disproportionate amount of risk sitting in a handful of servers.
This does not mean reckless patching. It means creating a separate lane for exposed, high-value server applications. That lane needs predefined owners, emergency test criteria, rollback plans, communication templates, and authority to move faster when Microsoft confirms a serious vulnerability. If those pieces are invented during the incident, the organization has already lost time.
CVE-2026-40368 should be treated as a test of that lane. If the organization cannot quickly identify its SharePoint Server estate, assess exposure, test the update, deploy safely, and verify completion, then the problem is bigger than one CVE. It is a process gap waiting for the next confirmed RCE.
The Cloud Migration Argument Gets Stronger, But Not Simpler
Every serious SharePoint Server vulnerability strengthens the case for reducing on-premises exposure. Microsoft would prefer customers to be in Microsoft 365, and from a patch-responsibility standpoint the cloud argument is compelling. Fewer customer-managed servers means fewer emergency farm updates, fewer forgotten portals, and fewer public-facing legacy systems waiting for the next exploit chain.But migration is not a magic eraser. Many SharePoint Server deployments exist because of custom workflows, data residency requirements, integrations, latency concerns, governance constraints, or plain institutional inertia. Moving that complexity to the cloud requires architecture, identity cleanup, permissions review, content rationalization, and political capital.
The right conclusion is not “everyone must migrate tomorrow.” It is that every remaining SharePoint Server should have a reason to exist. If the reason is strong, it deserves proper funding, patch engineering, monitoring, and lifecycle planning. If the reason is merely that nobody has had time to retire it, CVE-2026-40368 is another argument that the hidden cost of delay is rising.
A server kept for convenience can become a breach path. That is the brutal arithmetic of legacy collaboration infrastructure.
CVE-2026-40368 Turns SharePoint Hygiene Into a Board-Level Chore
The concrete lessons from this advisory are not exotic, but they are easy to postpone. That is precisely why they matter.- Organizations should confirm whether they run Microsoft SharePoint Server, not merely whether they use SharePoint Online or Microsoft 365.
- Administrators should treat Microsoft’s acknowledgement of CVE-2026-40368 as enough reason to begin remediation planning, even if exploit details remain limited.
- Externally reachable SharePoint farms should move to the front of the patch and validation queue.
- Internal SharePoint farms should still be assessed for lateral-movement value, sensitive content, and service account reach.
- Patch installation should be followed by build verification, farm health checks, and review of logs for suspicious pre-patch activity.
- Any SharePoint Server that cannot be patched quickly should trigger an explicit risk decision, compensating controls, and a retirement or modernization plan.
CVE-2026-40368 may ultimately prove to be a routine Microsoft server vulnerability, or it may become one of those SharePoint bugs administrators remember because attackers moved faster than change-control boards. The prudent position is to act before that distinction is settled in public. Microsoft’s confidence signal narrows the room for denial, and for anyone still running SharePoint Server, the next responsible move is to turn that signal into verified remediation rather than another item aging quietly in the vulnerability queue.
Source: MSRC Security Update Guide - Microsoft Security Response Center