Linux administrators received a new kernel CVE on May 6, 2026, when kernel.org published CVE-2026-43116 for a netfilter ctnetlink flaw involving unsafe access to a master conntrack object during expectation handling. The bug is not flashy in the way remote-code-execution headlines are flashy, but it sits in one of Linux’s most security-sensitive neighborhoods: the packet-filtering and connection-tracking machinery that firewalls, routers, containers, and virtualized workloads quietly depend on. Its practical lesson is blunt: the boring concurrency bug in the kernel dataplane is exactly the sort of issue that deserves prompt patch attention.
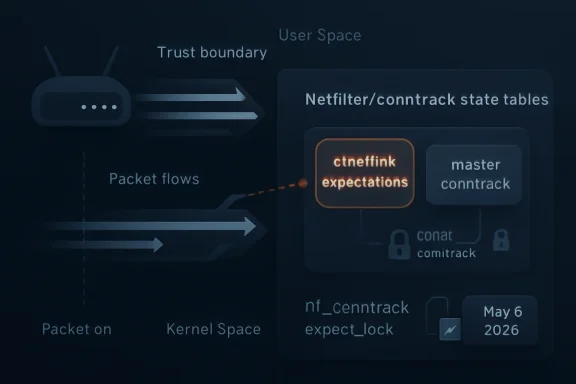
CVE-2026-43116 is, at heart, a lifetime-management problem. The Linux kernel’s netfilter connection tracking code keeps state about network flows, and ctnetlink exposes pieces of that state to user space through the netlink interface. In this case, the vulnerable path involved conntrack “expectations,” a mechanism used when one connection implies that another related connection may soon appear.
The flaw described by the kernel CVE text is subtle but serious: holding a reference to the expectation object was not enough, because the associated master conntrack object could disappear underneath it. That leaves
The patch’s strategy is not a grand redesign. It extends protection under
That makes this the sort of fix that is easy to underestimate. It is “just” a spinlock-section adjustment until you remember what the protected object represents: live kernel memory tied to firewall state, NAT state, helper modules, and user-space visibility into network tracking. When the thing being protected is part of the kernel’s model of the network, a small race can become a large operational concern.
Connection tracking is one of netfilter’s most consequential jobs. Instead of treating every packet as an isolated event, conntrack remembers flows and their state: new, established, related, reply direction, timeout, NAT mapping, helper association, and so on. That is what allows a firewall rule to say, in effect, “permit packets that belong to an already established connection,” rather than manually opening both directions for everything.
Expectations sit one layer deeper. They are used when a protocol helper knows that a control connection may lead to another related data connection. Classic examples historically include protocols such as FTP, where one session can negotiate another connection. The exact helper landscape has evolved, and many administrators now disable or avoid legacy helpers, but the underlying concept remains part of conntrack’s architecture.
CVE-2026-43116 lives in that machinery. It is not a bug in a desktop app, a browser, or a package manager. It is a bug in the kernel code that mediates network state. That placement matters more than any early vulnerability score, because NVD had not yet enriched the record with a CVSS vector at publication time.
But kernel CVEs do not wait politely for enrichment. The absence of a CVSS score says more about the timing of metadata processing than about the technical importance of the fix. Here, the kernel description already tells us the shape of the bug: a master conntrack object can “just go away,” invalidating
That is enough for a first-pass operational judgment. If you run Linux systems that expose netfilter conntrack functionality, especially systems where local users, containers, network namespaces, or management agents can interact with netlink, this belongs on the patch radar. If you run Linux primarily as an appliance platform — firewalls, routers, load balancers, Kubernetes nodes, network sensors — it belongs higher still.
The hardest part of kernel vulnerability management is that many bugs look local until somebody demonstrates a reachable path from a realistic environment. Netlink is one of the interfaces that often complicates that distinction. It is designed for kernel/user-space communication, and access may be shaped by privileges, namespaces, capabilities, and distribution defaults. That makes blanket panic inappropriate, but it also makes blanket dismissal irresponsible.
That is one of the classic traps in concurrent kernel code. A pointer relationship can look stable in the common case, pass ordinary testing, and remain safe for years under normal workloads. Then a cleanup path, event path, or lookup path runs at just the wrong moment, and the implied lifetime guarantee disappears.
The fix chooses serialization over clever lookup. The description notes that holding a reference on the master conntrack via
That is an engineering trade-off. Longer spinlock coverage is rarely something kernel developers do casually, because it can affect contention and latency. Here, the patch text argues that the affected cases only slightly extend an existing lock section. The message is practical: keep the object stable while it is being inspected, and move anything that cannot happen under a spinlock, such as GFP_KERNEL netlink skb allocation, outside that locked region.
This is also why the fix touches multiple paths. The delete expectation command must hold the spinlock before looking up the expectation. The get expectation command must do the same to keep the master conntrack from disappearing. Expectation events also need care because event cache access reaches through
WSL 2 runs a real Linux kernel under the hood. Azure customers deploy Linux at enormous scale. Kubernetes clusters commonly run Linux worker nodes even in Microsoft-heavy shops. Security appliances, SD-WAN boxes, NAS devices, developer workstations, CI runners, container hosts, and edge gateways all depend on Linux networking code. A Windows admin may never type
The Microsoft Security Response Center listing is a reminder of this blended reality. MSRC tracks CVEs that matter to Microsoft customers, and Linux kernel vulnerabilities can matter when they intersect with Microsoft-distributed components, cloud services, container hosts, or platforms that incorporate Linux. The old mental boundary — Windows vulnerabilities over here, Linux vulnerabilities over there — is increasingly useless for defenders.
That does not mean every Windows machine is suddenly exposed. A conventional Windows desktop without Linux components is not affected by a Linux kernel netfilter flaw. But the operational footprint around that desktop may be. The developer laptop running WSL, the build agent running Docker workloads, the Azure VM acting as a NAT gateway, and the Kubernetes node enforcing service traffic are all plausible places where Linux conntrack behavior matters.
The useful question, then, is not “Do we run Linux?” Most organizations do. The useful question is “Where do we run Linux in a way that uses conntrack, netfilter, network namespaces, or containerized networking?” The answer is often broader than the asset inventory suggests.
That said, defenders should not reduce “not trivially remote” to “not urgent.” Kernel-local vulnerabilities matter because local footholds are common. Container escapes, privilege escalation chains, post-exploitation persistence, and denial-of-service attacks all begin with the premise that some code is already running inside the environment. A bug reachable through netlink can become valuable when an attacker has a shell in a container, a compromised service account, or limited access on a multi-tenant box.
The conntrack expectation area is especially interesting because it has a history of subtle bugs. Recent related netfilter CVEs have dealt with validation gaps, helper references, and unsafe memory access around conntrack expectations. That does not prove that CVE-2026-43116 is part of a single exploit family, but it does suggest the subsystem is under active scrutiny.
Security teams should treat that pattern as a signal. Attackers and researchers alike tend to mine fruitful kernel subsystems once a class of bugs becomes visible. When one patch reveals that certain assumptions around object lifetime were too loose, adjacent paths often deserve extra attention. The kernel community has already done that work in the form of the patch; administrators still need to consume it.
Conntrack is also deeply entangled with Kubernetes networking. kube-proxy, service NAT, overlay networks, ingress controllers, and network policy engines may all interact with netfilter or rely on conntrack semantics, depending on the chosen CNI and dataplane. Some modern environments shift more work to eBPF, but netfilter is far from gone. In many clusters, it remains a load-bearing component.
That does not mean a pod can automatically exploit CVE-2026-43116. It means cluster operators should be careful about assuming that only host administrators can reach relevant code. Capabilities such as
There is also the less dramatic denial-of-service dimension. Kernel memory-safety bugs that are difficult to weaponize for privilege escalation may still crash a node. In a clustered environment, a node crash is not merely an inconvenience; it can trigger rescheduling storms, disrupt stateful workloads, break long-lived connections, and obscure forensic evidence. Availability is part of security, and kernel oopses in networking paths are operationally expensive.
That distinction is the difference between data-structure correctness and lifetime correctness. A table lookup can be perfectly valid, and the object found by that lookup can still contain a pointer whose target is racing with destruction. The kernel has many tools for this — reference counts, RCU, spinlocks, per-net namespaces, object caches — but they only work when the code’s assumptions match the object graph.
The patch’s lockdep additions are also worth noting. Lockdep is the kernel’s runtime lock dependency validator, used to catch incorrect locking patterns and potential deadlocks. Adding lockdep annotations is not just a belt-and-suspenders move; it is a statement that future code should be able to verify whether it is following the required locking discipline.
That matters because this class of bug tends to return when future maintenance changes reintroduce a shortcut. A developer sees an object pointer that “obviously” exists because the parent object exists. A fast path avoids a lock because the common case seems safe. A netlink event path grows one more field. Over time, the original lifetime rule becomes folklore unless the code documents and enforces it.
Security fixes that encode the rule are stronger than fixes that merely patch the symptom. CVE-2026-43116 appears to do both: it moves vulnerable access under the lock and adds annotations to help identify code paths that must follow the same rule. That is the sort of boring correctness work that keeps kernel subsystems survivable.
That lag is where risk lives. A fix can exist upstream while production systems remain exposed because the relevant stable update has not landed, has not been packaged, has not passed internal testing, or has not been rebooted into service. Kernel vulnerabilities are particularly unforgiving because installing the package is often not enough; the machine must actually boot the patched kernel.
For server fleets, the reboot requirement is the real patch-management tax. Live patching may help in some environments, but not every kernel fix is covered by every livepatch provider, and not every organization has livepatch infrastructure. In appliance and embedded contexts, administrators may be completely dependent on vendor firmware.
The practical move is to track three states, not one. First, determine whether your vendor has shipped a kernel containing the relevant netfilter fix. Second, confirm that your systems have installed that kernel package. Third, verify that they are actually running it. Vulnerability scanners frequently catch the first two poorly and the third too late.
Administrators should also watch for backports rather than only version numbers. Enterprise distributions often apply security patches to older kernel branches without changing to an upstream version that obviously contains the fix. A system can be patched while still reporting an old-looking kernel, and a system can be vulnerable while reporting a newer-looking custom build. Vendor advisory status matters.
CVE-2026-43116 is exactly the kind of issue that exposes those gaps. It is too technical to make a board-level dashboard by itself, but it affects a subsystem that can sit at key choke points in the environment. A forgotten Linux NAT instance, a self-managed Kubernetes cluster, or a WSL-heavy developer fleet can quietly become the place where “we patch everything” stops being true.
For WSL specifically, the situation should be handled with precision rather than alarm. WSL 2 uses a Microsoft-provided Linux kernel, and users generally receive kernel updates through Microsoft’s update mechanisms or the Microsoft Store distribution path depending on installation mode. The netfilter exposure in WSL is not the same as a public-facing Linux firewall, but developer machines are high-value targets and often run untrusted build scripts, containers, and package-install commands.
Azure environments need the same nuance. Managed services may abstract the kernel away from customers, while customer-managed VMs and self-managed AKS nodes place more responsibility on the tenant. Azure Linux, Ubuntu images, custom images, marketplace appliances, and third-party network virtual appliances will not all move in lockstep. The cloud removes some hardware headaches; it does not remove kernel patch governance.
The WindowsForum audience should read this CVE as another reminder that “Windows admin” now includes a working understanding of Linux kernel exposure. The platform boundary has moved. Attackers noticed years ago.
Each of those expectations is shaky. Object lifetime in kernel code must be explicit, not implied. CVSS is useful but late and incomplete. Local bugs become chain links. Linux ownership in hybrid shops is often shared until something breaks, at which point it becomes nobody’s fault and everybody’s outage.
CVE-2026-43116 also illustrates why vulnerability triage should read the patch, not just the headline. The headline says “netfilter: ctnetlink: ensure safe access to master conntrack.” The patch narrative says more: several expectation operations needed tighter lock coverage; event delivery touched the master through a cache; allocation had to be moved outside the spinlock; lockdep annotations were added to prevent future mistakes. That is a real engineering story.
The lesson for defenders is to map the engineering story onto their environment. Do they allow untrusted local users? Do containers get network administration capabilities? Do monitoring or orchestration agents interact with conntrack? Do appliances expose netfilter-heavy paths? Do distributions have updates available, and have systems rebooted into them?
That is better triage than waiting for a severity label to arrive.
The first tier is obvious: routers, firewalls, NAT gateways, load balancers, VPN concentrators, container hosts, Kubernetes nodes, and network security sensors. These systems are both network-critical and likely to exercise netfilter paths under churn. If they crash, the blast radius is larger than the box.
The second tier includes multi-user servers, CI runners, developer workstations with containers, and WSL-heavy engineering machines. These systems may not be network appliances, but they are more likely to run untrusted or semi-trusted code. In 2026, “developer box” often means local admin exceptions, package scripts, containers, credentials, and access to production-adjacent systems.
The third tier includes ordinary single-purpose Linux servers where local execution is tightly controlled and conntrack use is minimal. These should still be patched, but they may not justify emergency maintenance windows ahead of more exposed systems.
This prioritization is not an excuse to defer indefinitely. Kernel memory-safety fixes accumulate, and the cost of falling behind grows with every reboot skipped. It is simply a way to spend the first maintenance window where it matters most.
Administrators should identify affected kernel packages through their distribution or vendor advisories, install the relevant updates, and reboot into the patched kernel where required. They should also verify any network appliances or embedded Linux devices that rely on vendor firmware. If a product uses Linux netfilter internally, the fix may arrive as a firmware update rather than a normal package update.
Security teams should review whether untrusted users or workloads can access netlink paths related to conntrack expectations. In container environments, this means auditing privileged workloads, host networking,
Monitoring should focus on kernel oopses, unexpected reboots, conntrack-related errors, and unusual use of netlink interfaces where telemetry exists. Detection will not replace patching, but it can help spot instability during the window before updates are fully deployed.
Above all, teams should avoid turning the absence of a public exploit into a reason for complacency. Kernel bugs often become more actionable after patch publication, when researchers and attackers can compare before-and-after code.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 The Kernel Bug Is Small; the Trust Boundary Around It Is Not
The Kernel Bug Is Small; the Trust Boundary Around It Is Not
CVE-2026-43116 is, at heart, a lifetime-management problem. The Linux kernel’s netfilter connection tracking code keeps state about network flows, and ctnetlink exposes pieces of that state to user space through the netlink interface. In this case, the vulnerable path involved conntrack “expectations,” a mechanism used when one connection implies that another related connection may soon appear.The flaw described by the kernel CVE text is subtle but serious: holding a reference to the expectation object was not enough, because the associated master conntrack object could disappear underneath it. That leaves
exp->master pointing at an object that may no longer be valid. In kernel security language, that is the terrain of use-after-free behavior, stale pointers, crashes, and potentially worse outcomes depending on reachability, timing, and surrounding allocator state.The patch’s strategy is not a grand redesign. It extends protection under
nf_conntrack_expect_lock, serializing access with cleanup paths that run when the master conntrack is going away. It also adjusts the lock coverage around add, delete, get, and event-delivery paths so that code touching the master object does so while the relevant lock discipline is in force.That makes this the sort of fix that is easy to underestimate. It is “just” a spinlock-section adjustment until you remember what the protected object represents: live kernel memory tied to firewall state, NAT state, helper modules, and user-space visibility into network tracking. When the thing being protected is part of the kernel’s model of the network, a small race can become a large operational concern.
Netfilter Is Where Linux Turns Packets Into Policy
For Windows-centric readers, netfilter is not merely “the Linux firewall.” It is the in-kernel framework behind packet filtering, NAT, connection tracking, and much of the plumbing that makes Linux viable as a router, firewall, container host, Kubernetes node, VPN gateway, or cloud edge appliance. The user-facing tools have changed over the years — iptables, nftables, firewalld, UFW, conntrack-tools — but the kernel machinery remains a core enforcement point.Connection tracking is one of netfilter’s most consequential jobs. Instead of treating every packet as an isolated event, conntrack remembers flows and their state: new, established, related, reply direction, timeout, NAT mapping, helper association, and so on. That is what allows a firewall rule to say, in effect, “permit packets that belong to an already established connection,” rather than manually opening both directions for everything.
Expectations sit one layer deeper. They are used when a protocol helper knows that a control connection may lead to another related data connection. Classic examples historically include protocols such as FTP, where one session can negotiate another connection. The exact helper landscape has evolved, and many administrators now disable or avoid legacy helpers, but the underlying concept remains part of conntrack’s architecture.
CVE-2026-43116 lives in that machinery. It is not a bug in a desktop app, a browser, or a package manager. It is a bug in the kernel code that mediates network state. That placement matters more than any early vulnerability score, because NVD had not yet enriched the record with a CVSS vector at publication time.
“Awaiting Enrichment” Is Not a Synonym for “Low Risk”
The NVD entry for CVE-2026-43116 was marked as awaiting enrichment, with no NIST CVSS 4.0, 3.x, or 2.0 score provided at the time reflected in the advisory text. That can create a dangerous pause in enterprise patch triage. Many vulnerability management workflows still lean heavily on numeric severity, and unscored CVEs often sit in an awkward queue until the scanners, dashboards, and compliance tools catch up.But kernel CVEs do not wait politely for enrichment. The absence of a CVSS score says more about the timing of metadata processing than about the technical importance of the fix. Here, the kernel description already tells us the shape of the bug: a master conntrack object can “just go away,” invalidating
exp->master, and the patch exists to ensure safe access through locking.That is enough for a first-pass operational judgment. If you run Linux systems that expose netfilter conntrack functionality, especially systems where local users, containers, network namespaces, or management agents can interact with netlink, this belongs on the patch radar. If you run Linux primarily as an appliance platform — firewalls, routers, load balancers, Kubernetes nodes, network sensors — it belongs higher still.
The hardest part of kernel vulnerability management is that many bugs look local until somebody demonstrates a reachable path from a realistic environment. Netlink is one of the interfaces that often complicates that distinction. It is designed for kernel/user-space communication, and access may be shaped by privileges, namespaces, capabilities, and distribution defaults. That makes blanket panic inappropriate, but it also makes blanket dismissal irresponsible.
The Patch Tells a Story About the Bug
The CVE description is unusually useful because it explains why the obvious reference was insufficient. The expectation object could be referenced, but the master conntrack object attached to it had its own lifetime. In other words, one object being alive did not guarantee that another object it pointed to was still safe to dereference.That is one of the classic traps in concurrent kernel code. A pointer relationship can look stable in the common case, pass ordinary testing, and remain safe for years under normal workloads. Then a cleanup path, event path, or lookup path runs at just the wrong moment, and the implied lifetime guarantee disappears.
The fix chooses serialization over clever lookup. The description notes that holding a reference on the master conntrack via
nf_conntrack_find_get() would be one safe approach, but the master tuple needed for lookup is not available in the problematic paths. Rather than reconstructing the world, the patch extends the critical section guarded by nf_conntrack_expect_lock.That is an engineering trade-off. Longer spinlock coverage is rarely something kernel developers do casually, because it can affect contention and latency. Here, the patch text argues that the affected cases only slightly extend an existing lock section. The message is practical: keep the object stable while it is being inspected, and move anything that cannot happen under a spinlock, such as GFP_KERNEL netlink skb allocation, outside that locked region.
This is also why the fix touches multiple paths. The delete expectation command must hold the spinlock before looking up the expectation. The get expectation command must do the same to keep the master conntrack from disappearing. Expectation events also need care because event cache access reaches through
exp->master. The bug is not a single bad line so much as a violated assumption that appeared in several related routes through the same subsystem.The Real Audience Is Not Just Linux Desktop Users
It is tempting to file this under “Linux kernel issue” and move on, especially on a site whose community has deep Windows roots. That would be a mistake. Modern Windows and Microsoft environments are full of Linux, even when nobody calls them Linux estates.WSL 2 runs a real Linux kernel under the hood. Azure customers deploy Linux at enormous scale. Kubernetes clusters commonly run Linux worker nodes even in Microsoft-heavy shops. Security appliances, SD-WAN boxes, NAS devices, developer workstations, CI runners, container hosts, and edge gateways all depend on Linux networking code. A Windows admin may never type
nft list ruleset and still be responsible for systems whose uptime and security depend on netfilter.The Microsoft Security Response Center listing is a reminder of this blended reality. MSRC tracks CVEs that matter to Microsoft customers, and Linux kernel vulnerabilities can matter when they intersect with Microsoft-distributed components, cloud services, container hosts, or platforms that incorporate Linux. The old mental boundary — Windows vulnerabilities over here, Linux vulnerabilities over there — is increasingly useless for defenders.
That does not mean every Windows machine is suddenly exposed. A conventional Windows desktop without Linux components is not affected by a Linux kernel netfilter flaw. But the operational footprint around that desktop may be. The developer laptop running WSL, the build agent running Docker workloads, the Azure VM acting as a NAT gateway, and the Kubernetes node enforcing service traffic are all plausible places where Linux conntrack behavior matters.
The useful question, then, is not “Do we run Linux?” Most organizations do. The useful question is “Where do we run Linux in a way that uses conntrack, netfilter, network namespaces, or containerized networking?” The answer is often broader than the asset inventory suggests.
Exploitability Will Depend on Reachability, But Reachability Is Messy
No responsible reading of CVE-2026-43116 should claim a universal remote exploit from the public description alone. The described issue is in ctnetlink expectation handling, which points toward local or privileged interaction with netlink rather than a magic packet from the internet. Attack viability will depend on kernel version, configuration, enabled modules, namespaces, capabilities, distribution hardening, and what user-space paths can trigger expectation operations.That said, defenders should not reduce “not trivially remote” to “not urgent.” Kernel-local vulnerabilities matter because local footholds are common. Container escapes, privilege escalation chains, post-exploitation persistence, and denial-of-service attacks all begin with the premise that some code is already running inside the environment. A bug reachable through netlink can become valuable when an attacker has a shell in a container, a compromised service account, or limited access on a multi-tenant box.
The conntrack expectation area is especially interesting because it has a history of subtle bugs. Recent related netfilter CVEs have dealt with validation gaps, helper references, and unsafe memory access around conntrack expectations. That does not prove that CVE-2026-43116 is part of a single exploit family, but it does suggest the subsystem is under active scrutiny.
Security teams should treat that pattern as a signal. Attackers and researchers alike tend to mine fruitful kernel subsystems once a class of bugs becomes visible. When one patch reveals that certain assumptions around object lifetime were too loose, adjacent paths often deserve extra attention. The kernel community has already done that work in the form of the patch; administrators still need to consume it.
The Container Angle Is Where This Gets Uncomfortable
Containers make netfilter bugs harder to reason about because they blur the line between “local” and “tenant-controlled.” A containerized workload may be heavily restricted, or it may have enough network namespace and capability access to interact with pieces of the kernel networking stack in ways that surprise the platform team. The difference between those two states is often a YAML file, a Helm chart, or a well-meaning exception granted months ago.Conntrack is also deeply entangled with Kubernetes networking. kube-proxy, service NAT, overlay networks, ingress controllers, and network policy engines may all interact with netfilter or rely on conntrack semantics, depending on the chosen CNI and dataplane. Some modern environments shift more work to eBPF, but netfilter is far from gone. In many clusters, it remains a load-bearing component.
That does not mean a pod can automatically exploit CVE-2026-43116. It means cluster operators should be careful about assuming that only host administrators can reach relevant code. Capabilities such as
CAP_NET_ADMIN, privileged containers, host networking, custom firewall controllers, service meshes, and node-level agents can expand the attack surface. The more a cluster delegates networking control to workloads or third-party agents, the more attention this CVE deserves.There is also the less dramatic denial-of-service dimension. Kernel memory-safety bugs that are difficult to weaponize for privilege escalation may still crash a node. In a clustered environment, a node crash is not merely an inconvenience; it can trigger rescheduling storms, disrupt stateful workloads, break long-lived connections, and obscure forensic evidence. Availability is part of security, and kernel oopses in networking paths are operationally expensive.
The Fix Is a Locking Lesson With a Security Label
The interesting part of this CVE is not that the kernel needed a lock. The interesting part is that the right lock had to cover the right conceptual operation. The vulnerable code did not merely need to protect the expectation table as a data structure; it needed to protect the relationship between the expectation and its master conntrack object while user-space-visible data was being produced or modified.That distinction is the difference between data-structure correctness and lifetime correctness. A table lookup can be perfectly valid, and the object found by that lookup can still contain a pointer whose target is racing with destruction. The kernel has many tools for this — reference counts, RCU, spinlocks, per-net namespaces, object caches — but they only work when the code’s assumptions match the object graph.
The patch’s lockdep additions are also worth noting. Lockdep is the kernel’s runtime lock dependency validator, used to catch incorrect locking patterns and potential deadlocks. Adding lockdep annotations is not just a belt-and-suspenders move; it is a statement that future code should be able to verify whether it is following the required locking discipline.
That matters because this class of bug tends to return when future maintenance changes reintroduce a shortcut. A developer sees an object pointer that “obviously” exists because the parent object exists. A fast path avoids a lock because the common case seems safe. A netlink event path grows one more field. Over time, the original lifetime rule becomes folklore unless the code documents and enforces it.
Security fixes that encode the rule are stronger than fixes that merely patch the symptom. CVE-2026-43116 appears to do both: it moves vulnerable access under the lock and adds annotations to help identify code paths that must follow the same rule. That is the sort of boring correctness work that keeps kernel subsystems survivable.
The Distribution Lag Is the Window That Matters
Kernel.org CVE publication is only the start of the patching story. Most administrators do not run kernels directly from upstream stable Git. They run distribution kernels from Ubuntu, Debian, Red Hat, SUSE, Oracle, Amazon, Arch, Alpine, Proxmox, OpenWrt, or vendor appliance firmware. Each has its own backporting, testing, advisory, and release cadence.That lag is where risk lives. A fix can exist upstream while production systems remain exposed because the relevant stable update has not landed, has not been packaged, has not passed internal testing, or has not been rebooted into service. Kernel vulnerabilities are particularly unforgiving because installing the package is often not enough; the machine must actually boot the patched kernel.
For server fleets, the reboot requirement is the real patch-management tax. Live patching may help in some environments, but not every kernel fix is covered by every livepatch provider, and not every organization has livepatch infrastructure. In appliance and embedded contexts, administrators may be completely dependent on vendor firmware.
The practical move is to track three states, not one. First, determine whether your vendor has shipped a kernel containing the relevant netfilter fix. Second, confirm that your systems have installed that kernel package. Third, verify that they are actually running it. Vulnerability scanners frequently catch the first two poorly and the third too late.
Administrators should also watch for backports rather than only version numbers. Enterprise distributions often apply security patches to older kernel branches without changing to an upstream version that obviously contains the fix. A system can be patched while still reporting an old-looking kernel, and a system can be vulnerable while reporting a newer-looking custom build. Vendor advisory status matters.
Microsoft Shops Should Audit the Linux They Forgot They Owned
The most awkward inventory problems live in hybrid environments. A Microsoft-first company may have meticulous coverage for Windows Server, Defender, Intune, SCCM, and Entra-connected endpoints, while Linux nodes exist as project infrastructure, developer tooling, or cloud service dependencies. Those machines often fall between teams: not quite endpoint, not quite server, not quite network appliance.CVE-2026-43116 is exactly the kind of issue that exposes those gaps. It is too technical to make a board-level dashboard by itself, but it affects a subsystem that can sit at key choke points in the environment. A forgotten Linux NAT instance, a self-managed Kubernetes cluster, or a WSL-heavy developer fleet can quietly become the place where “we patch everything” stops being true.
For WSL specifically, the situation should be handled with precision rather than alarm. WSL 2 uses a Microsoft-provided Linux kernel, and users generally receive kernel updates through Microsoft’s update mechanisms or the Microsoft Store distribution path depending on installation mode. The netfilter exposure in WSL is not the same as a public-facing Linux firewall, but developer machines are high-value targets and often run untrusted build scripts, containers, and package-install commands.
Azure environments need the same nuance. Managed services may abstract the kernel away from customers, while customer-managed VMs and self-managed AKS nodes place more responsibility on the tenant. Azure Linux, Ubuntu images, custom images, marketplace appliances, and third-party network virtual appliances will not all move in lockstep. The cloud removes some hardware headaches; it does not remove kernel patch governance.
The WindowsForum audience should read this CVE as another reminder that “Windows admin” now includes a working understanding of Linux kernel exposure. The platform boundary has moved. Attackers noticed years ago.
A CVE About Expectations Also Tests Our Expectations
There is a neat irony in a vulnerability about conntrack expectations: the bug challenges the expectations of the people managing it. We expect a referenced object to keep its neighbors safe. We expect unscored CVEs to be less urgent than scored ones. We expect local kernel bugs to stay local. We expect Linux systems in Microsoft environments to be someone else’s problem.Each of those expectations is shaky. Object lifetime in kernel code must be explicit, not implied. CVSS is useful but late and incomplete. Local bugs become chain links. Linux ownership in hybrid shops is often shared until something breaks, at which point it becomes nobody’s fault and everybody’s outage.
CVE-2026-43116 also illustrates why vulnerability triage should read the patch, not just the headline. The headline says “netfilter: ctnetlink: ensure safe access to master conntrack.” The patch narrative says more: several expectation operations needed tighter lock coverage; event delivery touched the master through a cache; allocation had to be moved outside the spinlock; lockdep annotations were added to prevent future mistakes. That is a real engineering story.
The lesson for defenders is to map the engineering story onto their environment. Do they allow untrusted local users? Do containers get network administration capabilities? Do monitoring or orchestration agents interact with conntrack? Do appliances expose netfilter-heavy paths? Do distributions have updates available, and have systems rebooted into them?
That is better triage than waiting for a severity label to arrive.
The Patch Queue Should Start With Network Choke Points
Not every Linux host deserves the same urgency. A lab VM with no untrusted users and no meaningful network role is not the same as a border firewall or Kubernetes node. CVE-2026-43116 should push administrators to rank systems by how heavily they rely on conntrack and how exposed their local execution surface is.The first tier is obvious: routers, firewalls, NAT gateways, load balancers, VPN concentrators, container hosts, Kubernetes nodes, and network security sensors. These systems are both network-critical and likely to exercise netfilter paths under churn. If they crash, the blast radius is larger than the box.
The second tier includes multi-user servers, CI runners, developer workstations with containers, and WSL-heavy engineering machines. These systems may not be network appliances, but they are more likely to run untrusted or semi-trusted code. In 2026, “developer box” often means local admin exceptions, package scripts, containers, credentials, and access to production-adjacent systems.
The third tier includes ordinary single-purpose Linux servers where local execution is tightly controlled and conntrack use is minimal. These should still be patched, but they may not justify emergency maintenance windows ahead of more exposed systems.
This prioritization is not an excuse to defer indefinitely. Kernel memory-safety fixes accumulate, and the cost of falling behind grows with every reboot skipped. It is simply a way to spend the first maintenance window where it matters most.
The Concrete Work Starts After the Advisory
The immediate checklist for CVE-2026-43116 is mercifully familiar, but it must be done carefully. The risk is less about misunderstanding the bug than about assuming the fleet is already covered. Kernel patching is one of the places where assumptions routinely fail.Administrators should identify affected kernel packages through their distribution or vendor advisories, install the relevant updates, and reboot into the patched kernel where required. They should also verify any network appliances or embedded Linux devices that rely on vendor firmware. If a product uses Linux netfilter internally, the fix may arrive as a firmware update rather than a normal package update.
Security teams should review whether untrusted users or workloads can access netlink paths related to conntrack expectations. In container environments, this means auditing privileged workloads, host networking,
CAP_NET_ADMIN, and node-level agents. In developer environments, it means acknowledging that local code execution is not hypothetical; it is the default state of modern software development.Monitoring should focus on kernel oopses, unexpected reboots, conntrack-related errors, and unusual use of netlink interfaces where telemetry exists. Detection will not replace patching, but it can help spot instability during the window before updates are fully deployed.
Above all, teams should avoid turning the absence of a public exploit into a reason for complacency. Kernel bugs often become more actionable after patch publication, when researchers and attackers can compare before-and-after code.
The Few Facts That Should Drive the Maintenance Window
The story around CVE-2026-43116 is technical, but the operational message is compact. This is a kernel networking fix, not a cosmetic advisory, and it touches a subsystem many organizations use more widely than they realize.- CVE-2026-43116 was published on May 6, 2026, for a Linux kernel netfilter ctnetlink issue involving unsafe access to a master conntrack object.
- The bug concerns conntrack expectation handling, where a referenced expectation did not guarantee that
exp->masterremained valid. - The upstream fix expands locking around expectation lookup, deletion, retrieval, and event paths so the master conntrack object cannot disappear during unsafe access.
- The lack of an NVD CVSS score at publication time should not be treated as evidence that the issue is low severity.
- The highest-priority systems are Linux hosts that act as firewalls, routers, NAT gateways, container nodes, Kubernetes workers, VPN systems, or other network choke points.
- Windows-heavy organizations should include WSL, Azure Linux workloads, container hosts, and Linux-based appliances in their exposure review.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center