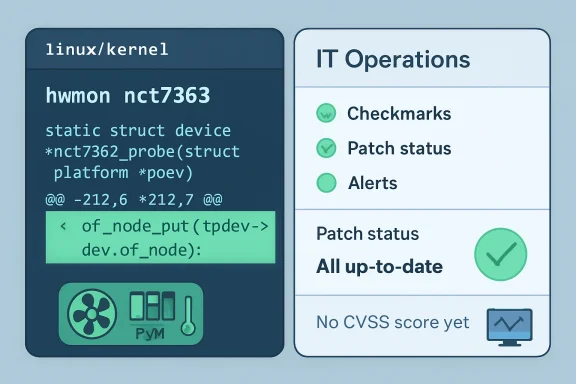
Microsoft listed CVE-2026-43165 on May 6, 2026, after kernel.org assigned the identifier to a Linux kernel hardware-monitoring driver bug in the Nuvoton NCT7363 hwmon code, where a missing device-tree reference release can leak resources during PWM and fan-input parsing. The flaw is not a headline-grabbing remote-code-execution crisis, and NVD has not yet enriched it with severity metrics. But it is a useful specimen of the modern Linux vulnerability machine: small kernel fixes now become CVEs quickly, upstream commits become the security record, and downstream vendors are left to translate that into operational risk.
The temptation is to dismiss CVE-2026-43165 as noise. A one-line fix in a hardware-monitoring driver hardly sounds like the stuff of breach reports, ransomware playbooks, or emergency maintenance windows. Yet that dismissal misses the real story, because Linux kernel security in 2026 is no longer only about the spectacular bug; it is also about whether organizations can absorb a constant stream of precise, low-drama disclosures without either ignoring them or overreacting to them.
CVE-2026-43165 sits in the
The fix is as plain as kernel patches get: add the missing
That does not mean the vulnerability is fake. Kernel reference leaks matter because the kernel is not an ordinary application process that can be casually restarted when it accumulates stale state. A small leak in a rarely used path may be harmless in most deployments, but the kernel’s entire security model depends on thousands of small invariants being upheld consistently.
The more important question is proportionality. CVE-2026-43165 is a real bug, fixed by a real patch, in real kernel code. It is also probably not the next fire drill for most WindowsForum readers running WSL, Linux servers, appliances, or mixed Windows/Linux infrastructure.
This approach has an obvious upside. It anchors the vulnerability record to code that actually changed. Administrators can map the advisory to commits, distributions can backport the fix, and security teams can stop arguing about whether an issue exists in the abstract. The CVE is not a press release; it is a pointer into the maintenance stream.
The downside is equally obvious. The more faithfully the kernel community labels fixed bugs as CVEs, the less useful the mere presence of a CVE becomes as a proxy for urgency. A scanner that treats CVE-2026-43165 like a remotely exploitable authentication bypass is not being cautious; it is being blind.
That is the uncomfortable bargain kernel users now live with. The vulnerability feed is more complete, but it demands more adult supervision. Organizations that built their patching process around CVSS-first dashboards will increasingly struggle with Linux kernel CVEs that are published before scoring, before enrichment, and before downstream advisories have fully converged.
That intimacy is why resource-management bugs in these paths deserve attention even when they do not deserve panic. Device-tree parsing is foundational in many non-PC and embedded Linux environments. A bad reference count does not automatically create a privilege escalation, but it can slowly degrade a running system or complicate hotplug, probe, reprobe, and error paths.
For a general-purpose desktop or server, the specific NCT7363 path may not even be compiled, loaded, or reachable. For a vendor shipping boards that use the affected monitoring chip, the calculation changes. A bug that is irrelevant to a cloud VM can be relevant to a fleet of edge devices expected to run unattended for years.
This is where vulnerability management becomes architecture management. The right answer is not “patch everything immediately” or “ignore low-severity kernel CVEs.” The right answer is to know whether the affected driver exists in your kernel, whether the hardware exists in your fleet, whether the code path is reachable, and how quickly your distribution or vendor backports stable fixes.
Neither reading is defensible. NVD enrichment lag is now a normal part of the vulnerability lifecycle, especially for fast-moving upstream projects. The authoritative initial facts here come from kernel.org’s CVE assignment and the associated stable commits, not from a score that has not yet been written.
CVSS is useful when it captures exploitability, impact, privileges required, attack complexity, and environmental assumptions. It is much less useful as a substitute for knowing whether a bug applies to your systems. CVE-2026-43165 is almost a textbook example of that distinction: the interesting part is not the future number but the operational context.
For Windows administrators managing Linux through WSL, Hyper-V guests, Azure images, containers, or appliance-like distributions, this matters. A kernel CVE may be irrelevant to WSL if the affected driver is absent. It may be irrelevant to a container if the host kernel is already patched. It may be highly relevant to a storage appliance, router, lab board, or monitoring-heavy industrial controller.
This is not Microsoft claiming ownership of the flaw. It is Microsoft acknowledging that customer exposure increasingly crosses product boundaries. In 2026, the Windows estate is not just Windows clients and Windows Server. It is Windows endpoints running developer Linux environments, Azure workloads built on Linux images, Defender-protected mixed fleets, Kubernetes clusters, and vendor appliances plugged into Microsoft-centric management planes.
That does not mean every Linux kernel CVE in MSRC guidance should trigger a Windows patching ritual. It means administrators need to stop treating “Microsoft advisory” and “Windows vulnerability” as synonyms. The advisory surface has widened because the operational surface has widened.
The irony is that Microsoft’s involvement may make low-level Linux CVEs more visible to Windows-heavy shops than they would otherwise be. That visibility is useful, but only if it leads to triage rather than reflex. Security teams need to ask whether the affected Linux kernel code is present in Microsoft-supplied images, third-party images, WSL kernels, or vendor-managed appliances before assigning urgency.
That translation layer is where vulnerability management either works or fails. A distribution may backport the fix without changing the apparent upstream version. A vendor may mark the CVE not affected because the driver is not enabled. An appliance maker may silently absorb the patch in a firmware update months later. A scanner may flag the system anyway because it sees a version string rather than a patched source tree.
CVE-2026-43165 is unlikely to cause emergency outages by itself, but it will expose weak process. If your tooling cannot distinguish between a vulnerable upstream version and a downstream backport, it will create false pressure. If your asset inventory cannot tell you where the NCT7363 driver is present, it will create false uncertainty.
For sysadmins, the practical path is refreshingly boring. Track your vendor’s kernel advisories, confirm whether your running kernel includes the stable fix, and schedule the update according to the system’s role. If this is an internet-facing production server with no affected hardware, it belongs in normal kernel maintenance. If this is a board or appliance using NCT7363 monitoring and designed for long uptime, it deserves closer review.
That is why treating CVE-2026-43165 as “just a leak” is too glib. Kernel memory and resource leaks can contribute to denial-of-service conditions, instability, and hard-to-debug failures. In constrained systems, long-running devices, or repeated probe paths, even boring leaks have operational consequences.
At the same time, treating every kernel CVE as an immediate breach precursor is equally wrong. The point of mature vulnerability management is not to flatten all risk into the same red alert. It is to preserve enough context to move quickly when speed matters and calmly when it does not.
This is where many enterprises still lag behind the kernel community. Upstream maintainers have become more systematic about labeling fixes. Security operations teams must now become more systematic about interpreting them. The bottleneck is no longer only disclosure; it is comprehension.
The affected code path is tied to device-tree parsing in a hardware-monitoring driver. That narrows the practical exposure substantially compared with a core networking, filesystem, memory-management, or privilege-boundary flaw. It also suggests that exploitability, if any, depends heavily on platform configuration and reachable device descriptions.
A mature assessment starts there. Is the driver built into the kernel or available as a module? Is the relevant hardware present? Can an unprivileged user influence the device-tree data or trigger repeated parsing? Is this a general-purpose system, an appliance, or an embedded board? Does the vendor already include the one-line fix?
Those questions are less satisfying than a severity label, but they are more useful. A CVSS score is a compressed opinion. A patch is evidence.
The subtle risk is not that CVE-2026-43165 will suddenly become the next major exploit wave. The subtler risk is that organizations will continue to accumulate Linux dependencies without a Linux-grade patching process. Windows shops have spent decades learning Patch Tuesday muscle memory; Linux kernel maintenance is a different rhythm, with stable releases, distribution backports, live patching options, and hardware-specific relevance.
That rhythm matters more as Windows and Linux estates converge. Developers run Linux tooling on Windows laptops. Enterprises run Linux workloads in Microsoft clouds. Security products inspect both. The old boundary between “our Windows patch process” and “some Linux thing engineering handles” is increasingly fictional.
CVE-2026-43165 is therefore a small advisory with a large lesson. It asks whether your organization can process a low-severity, upstream-driven, hardware-specific Linux kernel CVE without confusion. If the answer is no, the problem is bigger than this driver.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
The temptation is to dismiss CVE-2026-43165 as noise. A one-line fix in a hardware-monitoring driver hardly sounds like the stuff of breach reports, ransomware playbooks, or emergency maintenance windows. Yet that dismissal misses the real story, because Linux kernel security in 2026 is no longer only about the spectacular bug; it is also about whether organizations can absorb a constant stream of precise, low-drama disclosures without either ignoring them or overreacting to them.
 A One-Line Kernel Fix Becomes a Public Security Event
A One-Line Kernel Fix Becomes a Public Security Event
CVE-2026-43165 sits in the hwmon subsystem, specifically the nct7363 driver for Nuvoton hardware-monitoring functionality. The affected function, nct7363_present_pwm_fanin, calls of_parse_phandle_with_args(), which obtains a reference to a device-tree node. Kernel convention requires the caller to release that reference with of_node_put() when it is finished.The fix is as plain as kernel patches get: add the missing
of_node_put(args.np);. That is the kind of change that, in another era, might have passed through the stable tree as an unremarkable resource-management cleanup. In the current era, it arrives with a CVE number, a vendor advisory entry, and a spot in vulnerability scanners before NVD has even assigned a score.That does not mean the vulnerability is fake. Kernel reference leaks matter because the kernel is not an ordinary application process that can be casually restarted when it accumulates stale state. A small leak in a rarely used path may be harmless in most deployments, but the kernel’s entire security model depends on thousands of small invariants being upheld consistently.
The more important question is proportionality. CVE-2026-43165 is a real bug, fixed by a real patch, in real kernel code. It is also probably not the next fire drill for most WindowsForum readers running WSL, Linux servers, appliances, or mixed Windows/Linux infrastructure.
The Kernel CNA Era Rewards Precision and Punishes Triage Laziness
The Linux kernel project’s move to handle its own CVE assignments changed the texture of vulnerability management. Instead of waiting for outside researchers, vendors, or downstream distributions to classify only the most dramatic issues, the kernel process now tends to assign CVEs once fixes land in stable trees and are judged plausibly security-relevant. That is why a missing reference release in anhwmon driver can receive an identifier before NVD has enriched the record.This approach has an obvious upside. It anchors the vulnerability record to code that actually changed. Administrators can map the advisory to commits, distributions can backport the fix, and security teams can stop arguing about whether an issue exists in the abstract. The CVE is not a press release; it is a pointer into the maintenance stream.
The downside is equally obvious. The more faithfully the kernel community labels fixed bugs as CVEs, the less useful the mere presence of a CVE becomes as a proxy for urgency. A scanner that treats CVE-2026-43165 like a remotely exploitable authentication bypass is not being cautious; it is being blind.
That is the uncomfortable bargain kernel users now live with. The vulnerability feed is more complete, but it demands more adult supervision. Organizations that built their patching process around CVSS-first dashboards will increasingly struggle with Linux kernel CVEs that are published before scoring, before enrichment, and before downstream advisories have fully converged.
Hardware-Monitoring Bugs Live in the Long Tail of Risk
Thehwmon subsystem is not glamorous, but it is everywhere in the kinds of systems IT pros actually maintain. Servers, embedded boards, appliances, industrial systems, and enthusiast rigs all rely on hardware-monitoring code to expose temperatures, fan speeds, voltages, and board-specific control paths. Much of this code is necessarily intimate with platform firmware descriptions and device-tree data.That intimacy is why resource-management bugs in these paths deserve attention even when they do not deserve panic. Device-tree parsing is foundational in many non-PC and embedded Linux environments. A bad reference count does not automatically create a privilege escalation, but it can slowly degrade a running system or complicate hotplug, probe, reprobe, and error paths.
For a general-purpose desktop or server, the specific NCT7363 path may not even be compiled, loaded, or reachable. For a vendor shipping boards that use the affected monitoring chip, the calculation changes. A bug that is irrelevant to a cloud VM can be relevant to a fleet of edge devices expected to run unattended for years.
This is where vulnerability management becomes architecture management. The right answer is not “patch everything immediately” or “ignore low-severity kernel CVEs.” The right answer is to know whether the affected driver exists in your kernel, whether the hardware exists in your fleet, whether the code path is reachable, and how quickly your distribution or vendor backports stable fixes.
NVD’s Silence Is Not a Safety Signal
At publication time, the NVD record for CVE-2026-43165 is still awaiting enrichment, with no NIST-provided CVSS score or vector. That absence will be misread in two opposite ways. Some dashboards will inflate uncertainty into urgency, while some teams will mistake “not yet scored” for “not important.”Neither reading is defensible. NVD enrichment lag is now a normal part of the vulnerability lifecycle, especially for fast-moving upstream projects. The authoritative initial facts here come from kernel.org’s CVE assignment and the associated stable commits, not from a score that has not yet been written.
CVSS is useful when it captures exploitability, impact, privileges required, attack complexity, and environmental assumptions. It is much less useful as a substitute for knowing whether a bug applies to your systems. CVE-2026-43165 is almost a textbook example of that distinction: the interesting part is not the future number but the operational context.
For Windows administrators managing Linux through WSL, Hyper-V guests, Azure images, containers, or appliance-like distributions, this matters. A kernel CVE may be irrelevant to WSL if the affected driver is absent. It may be irrelevant to a container if the host kernel is already patched. It may be highly relevant to a storage appliance, router, lab board, or monitoring-heavy industrial controller.
Microsoft’s Listing Is a Reminder That Linux Is Now Part of the Windows Estate
The MSRC appearance of CVE-2026-43165 may surprise readers who still think of Microsoft security guidance as a Windows-only universe. That world is gone. Microsoft ships, hosts, integrates, and supports Linux across Azure, WSL, container tooling, security products, IoT scenarios, and enterprise hybrid environments. A Linux kernel CVE can therefore become a Microsoft-tracked issue even when the bug itself is upstream Linux code.This is not Microsoft claiming ownership of the flaw. It is Microsoft acknowledging that customer exposure increasingly crosses product boundaries. In 2026, the Windows estate is not just Windows clients and Windows Server. It is Windows endpoints running developer Linux environments, Azure workloads built on Linux images, Defender-protected mixed fleets, Kubernetes clusters, and vendor appliances plugged into Microsoft-centric management planes.
That does not mean every Linux kernel CVE in MSRC guidance should trigger a Windows patching ritual. It means administrators need to stop treating “Microsoft advisory” and “Windows vulnerability” as synonyms. The advisory surface has widened because the operational surface has widened.
The irony is that Microsoft’s involvement may make low-level Linux CVEs more visible to Windows-heavy shops than they would otherwise be. That visibility is useful, but only if it leads to triage rather than reflex. Security teams need to ask whether the affected Linux kernel code is present in Microsoft-supplied images, third-party images, WSL kernels, or vendor-managed appliances before assigning urgency.
The Fix Is Simple; the Distribution Story Is Not
Upstream kernel fixes are clean in theory and messy in practice. The patch for CVE-2026-43165 is tiny, and the stable references indicate it has been carried into maintained kernel branches. But most organizations do not run upstream stable kernels directly. They run Ubuntu, Debian, Red Hat, SUSE, Oracle, Amazon Linux, Azure-tuned kernels, vendor appliance kernels, or heavily customized embedded builds.That translation layer is where vulnerability management either works or fails. A distribution may backport the fix without changing the apparent upstream version. A vendor may mark the CVE not affected because the driver is not enabled. An appliance maker may silently absorb the patch in a firmware update months later. A scanner may flag the system anyway because it sees a version string rather than a patched source tree.
CVE-2026-43165 is unlikely to cause emergency outages by itself, but it will expose weak process. If your tooling cannot distinguish between a vulnerable upstream version and a downstream backport, it will create false pressure. If your asset inventory cannot tell you where the NCT7363 driver is present, it will create false uncertainty.
For sysadmins, the practical path is refreshingly boring. Track your vendor’s kernel advisories, confirm whether your running kernel includes the stable fix, and schedule the update according to the system’s role. If this is an internet-facing production server with no affected hardware, it belongs in normal kernel maintenance. If this is a board or appliance using NCT7363 monitoring and designed for long uptime, it deserves closer review.
The Security Industry Still Struggles With Small Truths
The vulnerability economy is built to reward drama. A named exploit, a logo, a proof-of-concept video, and an active-exploitation claim will travel faster than a careful explanation of a missing reference release. But most real security work is not dramatic. It is the patient removal of small defects before they combine with other defects into something worse.That is why treating CVE-2026-43165 as “just a leak” is too glib. Kernel memory and resource leaks can contribute to denial-of-service conditions, instability, and hard-to-debug failures. In constrained systems, long-running devices, or repeated probe paths, even boring leaks have operational consequences.
At the same time, treating every kernel CVE as an immediate breach precursor is equally wrong. The point of mature vulnerability management is not to flatten all risk into the same red alert. It is to preserve enough context to move quickly when speed matters and calmly when it does not.
This is where many enterprises still lag behind the kernel community. Upstream maintainers have become more systematic about labeling fixes. Security operations teams must now become more systematic about interpreting them. The bottleneck is no longer only disclosure; it is comprehension.
The Patch Tells Us More Than the Score Will
When NVD eventually enriches CVE-2026-43165, the score may help procurement systems, compliance reports, and vulnerability dashboards settle into a familiar shape. But the score will not tell the whole story. The patch already tells us the class of bug, the subsystem, the likely reach, and the operational assumptions.The affected code path is tied to device-tree parsing in a hardware-monitoring driver. That narrows the practical exposure substantially compared with a core networking, filesystem, memory-management, or privilege-boundary flaw. It also suggests that exploitability, if any, depends heavily on platform configuration and reachable device descriptions.
A mature assessment starts there. Is the driver built into the kernel or available as a module? Is the relevant hardware present? Can an unprivileged user influence the device-tree data or trigger repeated parsing? Is this a general-purpose system, an appliance, or an embedded board? Does the vendor already include the one-line fix?
Those questions are less satisfying than a severity label, but they are more useful. A CVSS score is a compressed opinion. A patch is evidence.
WindowsForum Readers Should Watch the Plumbing, Not the Panic
For Windows enthusiasts and IT pros, the practical relevance of a Linuxhwmon CVE depends on how Linux enters the environment. WSL users should watch for Microsoft-provided kernel updates rather than trying to apply upstream patches manually. Hyper-V and Azure operators should track the distributions and images they actually deploy. Container administrators should remember that containers share the host kernel, which makes host patching the decisive control.The subtle risk is not that CVE-2026-43165 will suddenly become the next major exploit wave. The subtler risk is that organizations will continue to accumulate Linux dependencies without a Linux-grade patching process. Windows shops have spent decades learning Patch Tuesday muscle memory; Linux kernel maintenance is a different rhythm, with stable releases, distribution backports, live patching options, and hardware-specific relevance.
That rhythm matters more as Windows and Linux estates converge. Developers run Linux tooling on Windows laptops. Enterprises run Linux workloads in Microsoft clouds. Security products inspect both. The old boundary between “our Windows patch process” and “some Linux thing engineering handles” is increasingly fictional.
CVE-2026-43165 is therefore a small advisory with a large lesson. It asks whether your organization can process a low-severity, upstream-driven, hardware-specific Linux kernel CVE without confusion. If the answer is no, the problem is bigger than this driver.
This Tiny hwmon CVE Is a Test of Patch Discipline, Not Nerve
The correct response to CVE-2026-43165 is measured, but not dismissive. It is a reminder that kernel CVEs now include small, well-scoped fixes, and that security teams need enough technical inventory to separate applicable risk from background noise.- CVE-2026-43165 affects the Linux kernel’s NCT7363 hardware-monitoring driver, not Windows itself.
- The underlying fix adds a missing
of_node_put()call after device-tree parsing, addressing a resource leak. - NVD had not yet provided CVSS enrichment when the record appeared, so absence of a score should not be treated as absence of risk.
- Most general-purpose systems are likely to face low practical exposure unless the affected driver and hardware path are present.
- Organizations should rely on their kernel or distribution vendor’s patched packages rather than manually editing kernel source.
- The advisory is most useful as a prompt to verify Linux kernel inventory, backport visibility, and scanner accuracy.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center