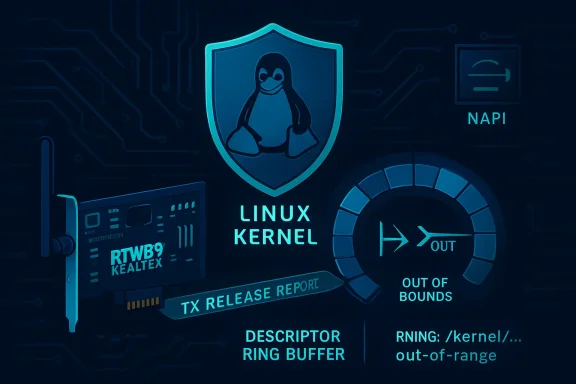
CVE-2026-43213 is a newly published Linux kernel vulnerability, disclosed by kernel.org and listed by Microsoft’s Security Update Guide on May 6, 2026, affecting the Realtek rtw89 PCI Wi-Fi driver when abnormal transmit-release sequence numbers trigger an out-of-bounds kernel access. The immediate symptom is not espionage, ransomware, or remote code execution; it is a crash. But the interesting story is larger than one Realtek driver. This is another reminder that modern operating-system security often fails at the seam where commodity hardware, asynchronous interrupts, and optimistic driver assumptions meet.
The fix for CVE-2026-43213 is almost comically small: before using a sequence number reported by hardware, the rtw89 PCI driver now checks whether that number is within the expected range. If it is not, the driver logs a warning and returns rather than indexing into
That is the sort of patch that looks routine in a kernel tree. It is six lines of defensive programming around a field named
The vulnerability description says the hardware “rarely reports abnormal sequence number” in a TX release report. That adjective matters. Rare hardware behavior is exactly where driver bugs hide, because test matrices tend to validate the normal path, the moderately unhappy path, and the obvious failure path. The strange one-in-a-million report from a Wi-Fi chipset is the path that turns into a CVE when the kernel treats the device’s answer as gospel.
The reported crash trace places the failure in
That makes it easy to dismiss. Availability bugs in a driver do not have the visceral pull of remote code execution. A Wi-Fi crash on a subset of Realtek hardware sounds like the sort of thing Linux laptop users have been working around with kernel updates, module reloads, and forum archaeology for years.
But “boring” driver bugs are often the ones that most clearly reveal the operating system’s real trust model. The kernel is not merely trusting applications, filesystem metadata, or network packets. It is trusting little pieces of silicon attached over PCIe, USB, and platform buses to report sane values while the rest of the machine is busy doing interrupt-driven work.
In this case, the driver parsed a TX release report, extracted a transmit channel and sequence number, and used that sequence number to select an entry in a descriptor ring. The missing check meant an abnormal sequence could point past the intended range. The patch does not introduce a grand redesign. It simply says: before trusting the device’s sequence number, make sure it is less than
That is the essence of defensive kernel engineering. Hardware is not a moral actor. Firmware is not a perfect collaborator. PCIe devices are not always well-behaved. A robust driver assumes that even “impossible” values will eventually arrive.
That ecosystem is improving, but it remains uneven. Realtek adapters are common because they are inexpensive and widely integrated. They also generate a disproportionate amount of support traffic in Linux communities because wireless drivers sit at the intersection of kernel ABI churn, firmware quirks, power management, PCIe behavior, Bluetooth coexistence, suspend/resume, regulatory-domain handling, and vendor-specific device revisions.
CVE-2026-43213 belongs to that world. It is not an indictment of every Realtek chipset, nor proof that the rtw89 driver is uniquely unsafe. It is evidence that Wi-Fi drivers remain some of the most complex and failure-prone code paths in a general-purpose operating system.
The bug’s trigger is particularly revealing: a transmit release report. The driver sends work to the device; the device later tells the driver what has been released or completed; the driver uses that report to free or advance bookkeeping structures. That is a normal ring-buffer dance in high-throughput device drivers. It is also a place where a stale, corrupt, unexpected, or firmware-generated value can desynchronize software’s idea of the world from hardware’s idea of the world.
When the ring bookkeeping is perfect, the system hums. When it is not, the failure can be abrupt. The crash trace included in the CVE record shows a kernel page fault at address zero, a classic NULL dereference, inside the rtw89 PCI path. In practical terms, the affected machine can fall over because the driver reaches for a descriptor page that is not there.
At the time of publication, NVD enrichment for CVE-2026-43213 is pending, and the NVD record does not provide its own CVSS score. Ubuntu has marked the issue as Medium while still evaluating release impact across kernel packages. Third-party vulnerability feeds may offer preliminary scoring, but the responsible reading is that the official severity picture is still settling.
The known impact is a kernel crash caused by a NULL pointer dereference. That is an availability problem. The public record does not establish a working exploit for code execution, privilege escalation, or data disclosure. It also does not prove that an ordinary remote attacker on the same Wi-Fi network can reliably trigger the abnormal sequence number. The description says the hardware reports the abnormal number, which points toward device or firmware behavior rather than a clean packet-in, crash-out exploit path.
That distinction matters for admins triaging risk. A laptop fleet with affected Realtek hardware deserves attention, especially if machines are already seeing unexplained rtw89 crashes. A headless Linux server with no Realtek rtw89 PCI Wi-Fi device is not suddenly in danger because the kernel has a new CVE. A container workload cannot generally trigger a PCI Wi-Fi driver bug unless the host and hardware path are in play.
Still, availability bugs are not harmless. A kernel crash is a denial of service against the local system. On a developer workstation, that means lost work and corrupted trust in the platform. On a kiosk, medical cart, point-of-sale terminal, factory tablet, or field laptop that depends on Wi-Fi, it can mean operational failure. In a security context, forced reboots can also interfere with monitoring, persistence detection, and forensic continuity.
So the presence of CVE-2026-43213 in MSRC should not be read as “Windows Wi-Fi is vulnerable.” It should be read as “Microsoft’s vulnerability ecosystem tracks this Linux kernel issue because Microsoft customers run Linux in Microsoft-managed and Microsoft-adjacent environments.”
That distinction is important for WindowsForum readers. If you are running Windows 11 on a laptop with a Realtek Wi-Fi card, this CVE is not describing the Windows Realtek driver. It is describing the Linux kernel’s rtw89 PCI path. If you dual-boot Linux, run Linux bare metal on the same hardware, maintain Linux laptops, or operate Linux endpoints with Realtek Wi-Fi, then it becomes relevant.
The more interesting Microsoft angle is strategic. The old boundary between “Windows vulnerabilities” and “Linux vulnerabilities” has eroded. An enterprise Windows admin may now be responsible for WSL developer environments, Linux build agents, Azure Kubernetes nodes, Defender telemetry on Linux, and hybrid identity infrastructure spanning both ecosystems. A Linux kernel Wi-Fi bug can therefore appear in the same dashboard culture as a Windows Kerberos issue or an Exchange advisory.
That is not a bad thing. It is the reality of mixed-platform operations. But it does mean patch teams need to avoid reflexive assumptions. “MSRC listed it” does not automatically mean Windows Update fixes it. “Linux kernel CVE” does not automatically mean it is irrelevant to a Microsoft shop.
This is the kernel’s industrial process in miniature. A driver maintainer sees or receives a crash, produces a small correctness patch, it lands upstream, and stable maintainers propagate it into supported release branches. Later, the CVE machinery assigns an identifier to the resolved vulnerability, and distribution trackers begin mapping the fix against their kernel packages.
That order often surprises people. In the Linux kernel world, the fix may exist before the vulnerability record is fully enriched. The CVE record may lag behind the commit. Distribution status may lag behind both. NVD scoring may appear after admins have already patched through ordinary kernel updates.
For security teams trained on vendor advisories as the beginning of the process, this can feel backwards. In open-source infrastructure, the commit is frequently the primary artifact. The CVE is the tracking wrapper added after the fact, useful for inventory, compliance, and notification, but not always the first sign that something important changed.
That is why blindly waiting for NVD to fill in CVSS details can be a mistake. If your environment contains the affected driver and a fixed kernel is available from your distribution, the absence of an NVD score is not a reason to delay routine patching. Conversely, a high third-party score is not a reason to emergency-patch machines that do not have the hardware or module exposure.
Drivers often behave as though the device is a partner. That is understandable. Device drivers are written to make hardware work, not to litigate every field returned by a chip. Performance pressures also push driver authors toward lean fast paths: avoid branches, avoid logging, avoid unnecessary checks in interrupt-sensitive code.
But hardware reports are input. Firmware is input. DMA-visible state is input. Completion queues, descriptor rings, sequence numbers, and status reports are all untrusted data crossing a boundary into privileged software.
CVE-2026-43213 is modest because the fix is modest. It is also profound because it captures the fundamental rule: if a value controls an array index in kernel space, validate it. The driver already had a special-case guard for an unexpected firmware-command release report channel. The new patch adds the equivalent guard for sequence numbers. That is not glamorous, but it is exactly the kind of small guardrail that keeps a rare device anomaly from becoming a system-wide failure.
This pattern is not unique to Wi-Fi. Storage controllers, GPUs, USB devices, Thunderbolt docks, Ethernet adapters, smart-card readers, webcams, and Bluetooth chipsets all feed complex state back into the kernel. Every one of those paths contains assumptions about what the device can and cannot say. Every wrong assumption is a potential crash, privilege boundary problem, or data corruption event.
The practical question for an affected laptop user is simple: which kernel are you running, and does your distribution include the fix? Rolling distributions may absorb the patch quickly. Enterprise distributions may backport it into older kernel series while keeping their external version numbers stable. Ubuntu’s tracker, as of May 7, 2026, still showed “Needs evaluation” across several supported releases, which means users should watch their normal security and kernel update channels rather than assuming a status from the mainline version alone.
For server admins, the story is usually narrower. Most production servers do not rely on Realtek PCI Wi-Fi. Many do not load rtw89 at all. If the module is absent, blacklisted, or irrelevant to the hardware, the operational risk is low. But edge devices are different. Retail endpoints, industrial PCs, digital signage, conference-room appliances, and small-office Linux boxes often use commodity Wi-Fi parts because they are cheap and available.
That is where the bug deserves more attention. The closer Linux moves to the edge, the more it inherits laptop-class hardware risk. A driver that is irrelevant in a rack can be central in a fleet of tablets, kiosks, or field service devices. Kernel CVE triage based only on “server relevance” can miss those environments.
The right operational move is not panic. It is inventory. Identify machines with Realtek rtw89 PCI devices, check whether the rtw89 PCI module is loaded, map kernel package versions to distributor advisories, and apply the fixed kernel when it arrives through supported channels.
The answer is that CVEs are identifiers, not arguments. They tell us there is a trackable vulnerability record. They do not, by themselves, tell us whether an issue is reachable in your environment, exploitable by your adversary model, or worth disrupting production to patch out of band.
CVE-2026-43213 is a good example of why context is the scarce resource. The affected component is specific: the Realtek rtw89 PCI Wi-Fi driver. The failure mode is specific: abnormal TX release report sequence numbers causing out-of-bounds access into a descriptor-page array and a NULL pointer dereference. The known impact is specific: kernel crash. The remediation is specific: take a kernel containing the sequence-number validation patch.
That specificity is more useful than a naked score. A CVSS number, once NVD or another authority provides one, may help dashboards sort queues. But a score cannot tell you whether your fleet contains the hardware. It cannot tell you whether a crash in a Wi-Fi driver affects your call center laptops more than your cloud nodes. It cannot tell you whether your distribution has already backported the fix without changing the kernel’s apparent major version.
For WindowsForum’s audience, this is the administrative lesson: vulnerability management is becoming less about memorizing vendor silos and more about interpreting component exposure. The patch cadence for Windows, Linux, firmware, drivers, browsers, and cloud agents increasingly overlaps. The winning teams will be the ones that can translate a CVE into an asset question quickly.
The old code path parsed the release report, filtered an unexpected transmit channel, then indexed into the write-descriptor ring using the reported sequence. The new code inserts a sanity gate before that index. If the sequence is greater than or equal to the maximum transmit descriptor count, the driver warns and returns.
That choice is conservative. It does not attempt to repair the sequence, resynchronize aggressively, or infer what the hardware meant. It refuses to act on an invalid report. In a low-level driver, that is often the safest possible response: preserve kernel integrity first, then let higher-level recovery mechanisms handle the device oddity.
The patch also uses
This is how mature systems become more reliable over time. Not through one sweeping rewrite, but through accumulated humility. Every check like this is a scar from a real failure.
For enterprise admins, the better answer starts with segmentation of relevance. A Linux kernel CVE can be urgent on one hardware class and irrelevant on another. The presence of a CVE in a Microsoft security feed does not remove the need to understand the Linux component underneath it.
This is also a good moment to revisit how endpoint inventories record hardware. Many organizations can tell you the OS version, EDR agent version, browser version, and disk encryption state of every laptop. Fewer can quickly answer which Wi-Fi chipset and kernel module each Linux endpoint uses. For driver CVEs, that missing layer is the difference between targeted remediation and dashboard panic.
The same is true for edge Linux. The devices most likely to use commodity Wi-Fi are often the least loved by central IT: signage boxes, lab systems, scanners, shared-room appliances, training carts, and remote-office devices. Those machines may not sit in the same patch pipeline as servers, yet they can still crash, lose connectivity, and generate operational outages.
The smart move is to fold hardware-linked kernel exposure into ordinary vulnerability management. Not every driver bug should page the CISO. But every driver bug should be mappable to actual machines.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Tiny Bounds Check Becomes a Kernel Security Event
A Tiny Bounds Check Becomes a Kernel Security Event
The fix for CVE-2026-43213 is almost comically small: before using a sequence number reported by hardware, the rtw89 PCI driver now checks whether that number is within the expected range. If it is not, the driver logs a warning and returns rather than indexing into wd_ring->pages and wandering off the valid edge of an array.That is the sort of patch that looks routine in a kernel tree. It is six lines of defensive programming around a field named
rpp_info.seq, guarding a transmit release report path in drivers/net/wireless/realtek/rtw89/pci.c. Yet those six lines are the difference between “hardware behaved weirdly” and “the kernel dereferenced NULL in interrupt context.”The vulnerability description says the hardware “rarely reports abnormal sequence number” in a TX release report. That adjective matters. Rare hardware behavior is exactly where driver bugs hide, because test matrices tend to validate the normal path, the moderately unhappy path, and the obvious failure path. The strange one-in-a-million report from a Wi-Fi chipset is the path that turns into a CVE when the kernel treats the device’s answer as gospel.
The reported crash trace places the failure in
rtw89_pci_release_tx, reached through NAPI polling and softirq handling after an rtw89 PCI interrupt. This is not a userspace program mishandling a bad packet and exiting with a stack trace. This is kernel code processing device-originated state in a context where a bad pointer can take down the whole machine.The Bug Is Boring, Which Is Why It Matters
Security coverage tends to reserve oxygen for vulnerabilities with cinematic attack chains: browser sandboxes, stolen tokens, cloud control planes, speculative execution, nation-state implants. CVE-2026-43213 is not that kind of story, at least based on the currently available record. It is a NULL pointer dereference caused by an unchecked sequence number from a Wi-Fi device.That makes it easy to dismiss. Availability bugs in a driver do not have the visceral pull of remote code execution. A Wi-Fi crash on a subset of Realtek hardware sounds like the sort of thing Linux laptop users have been working around with kernel updates, module reloads, and forum archaeology for years.
But “boring” driver bugs are often the ones that most clearly reveal the operating system’s real trust model. The kernel is not merely trusting applications, filesystem metadata, or network packets. It is trusting little pieces of silicon attached over PCIe, USB, and platform buses to report sane values while the rest of the machine is busy doing interrupt-driven work.
In this case, the driver parsed a TX release report, extracted a transmit channel and sequence number, and used that sequence number to select an entry in a descriptor ring. The missing check meant an abnormal sequence could point past the intended range. The patch does not introduce a grand redesign. It simply says: before trusting the device’s sequence number, make sure it is less than
RTW89_PCI_TXWD_NUM_MAX.That is the essence of defensive kernel engineering. Hardware is not a moral actor. Firmware is not a perfect collaborator. PCIe devices are not always well-behaved. A robust driver assumes that even “impossible” values will eventually arrive.
Realtek’s rtw89 Sits in the Messy Middle of Linux Wi-Fi
The rtw89 driver family supports newer Realtek Wi-Fi chipsets, including hardware found in plenty of consumer laptops, mini PCs, and add-in adapters. For Windows users, Realtek Wi-Fi often arrives as a vendor driver behind an OEM support page. For Linux users, support depends on the upstream kernel, distribution backports, firmware packaging, and sometimes third-party DKMS modules when the in-tree driver lags behind hardware needs.That ecosystem is improving, but it remains uneven. Realtek adapters are common because they are inexpensive and widely integrated. They also generate a disproportionate amount of support traffic in Linux communities because wireless drivers sit at the intersection of kernel ABI churn, firmware quirks, power management, PCIe behavior, Bluetooth coexistence, suspend/resume, regulatory-domain handling, and vendor-specific device revisions.
CVE-2026-43213 belongs to that world. It is not an indictment of every Realtek chipset, nor proof that the rtw89 driver is uniquely unsafe. It is evidence that Wi-Fi drivers remain some of the most complex and failure-prone code paths in a general-purpose operating system.
The bug’s trigger is particularly revealing: a transmit release report. The driver sends work to the device; the device later tells the driver what has been released or completed; the driver uses that report to free or advance bookkeeping structures. That is a normal ring-buffer dance in high-throughput device drivers. It is also a place where a stale, corrupt, unexpected, or firmware-generated value can desynchronize software’s idea of the world from hardware’s idea of the world.
When the ring bookkeeping is perfect, the system hums. When it is not, the failure can be abrupt. The crash trace included in the CVE record shows a kernel page fault at address zero, a classic NULL dereference, inside the rtw89 PCI path. In practical terms, the affected machine can fall over because the driver reaches for a descriptor page that is not there.
The Threat Model Is Narrower Than the CVE Number Suggests
CVE identifiers flatten nuance. A memory-corruption bug in a network-facing daemon, a privilege escalation in a filesystem, and a crash in a Wi-Fi driver all get the same kind of public label. That is useful for tracking, but it can mislead readers who assume every CVE is equally exploitable or equally urgent.At the time of publication, NVD enrichment for CVE-2026-43213 is pending, and the NVD record does not provide its own CVSS score. Ubuntu has marked the issue as Medium while still evaluating release impact across kernel packages. Third-party vulnerability feeds may offer preliminary scoring, but the responsible reading is that the official severity picture is still settling.
The known impact is a kernel crash caused by a NULL pointer dereference. That is an availability problem. The public record does not establish a working exploit for code execution, privilege escalation, or data disclosure. It also does not prove that an ordinary remote attacker on the same Wi-Fi network can reliably trigger the abnormal sequence number. The description says the hardware reports the abnormal number, which points toward device or firmware behavior rather than a clean packet-in, crash-out exploit path.
That distinction matters for admins triaging risk. A laptop fleet with affected Realtek hardware deserves attention, especially if machines are already seeing unexplained rtw89 crashes. A headless Linux server with no Realtek rtw89 PCI Wi-Fi device is not suddenly in danger because the kernel has a new CVE. A container workload cannot generally trigger a PCI Wi-Fi driver bug unless the host and hardware path are in play.
Still, availability bugs are not harmless. A kernel crash is a denial of service against the local system. On a developer workstation, that means lost work and corrupted trust in the platform. On a kiosk, medical cart, point-of-sale terminal, factory tablet, or field laptop that depends on Wi-Fi, it can mean operational failure. In a security context, forced reboots can also interfere with monitoring, persistence detection, and forensic continuity.
Microsoft’s Listing Is a Signal, Not a Windows Panic Button
The user-visible source here is Microsoft’s Security Update Guide, which can be confusing because the vulnerability itself is in the Linux kernel. Microsoft now has perfectly good reasons to track Linux CVEs. Azure runs Linux at vast scale. Windows Subsystem for Linux has become a mainstream developer surface. Microsoft ships and supports Linux images, Linux agents, Linux container hosts, Azure Linux, and security tooling that needs to understand open-source exposure.So the presence of CVE-2026-43213 in MSRC should not be read as “Windows Wi-Fi is vulnerable.” It should be read as “Microsoft’s vulnerability ecosystem tracks this Linux kernel issue because Microsoft customers run Linux in Microsoft-managed and Microsoft-adjacent environments.”
That distinction is important for WindowsForum readers. If you are running Windows 11 on a laptop with a Realtek Wi-Fi card, this CVE is not describing the Windows Realtek driver. It is describing the Linux kernel’s rtw89 PCI path. If you dual-boot Linux, run Linux bare metal on the same hardware, maintain Linux laptops, or operate Linux endpoints with Realtek Wi-Fi, then it becomes relevant.
The more interesting Microsoft angle is strategic. The old boundary between “Windows vulnerabilities” and “Linux vulnerabilities” has eroded. An enterprise Windows admin may now be responsible for WSL developer environments, Linux build agents, Azure Kubernetes nodes, Defender telemetry on Linux, and hybrid identity infrastructure spanning both ecosystems. A Linux kernel Wi-Fi bug can therefore appear in the same dashboard culture as a Windows Kerberos issue or an Exchange advisory.
That is not a bad thing. It is the reality of mixed-platform operations. But it does mean patch teams need to avoid reflexive assumptions. “MSRC listed it” does not automatically mean Windows Update fixes it. “Linux kernel CVE” does not automatically mean it is irrelevant to a Microsoft shop.
The Patch Shows How Kernel Stable Really Works
The patch associated with CVE-2026-43213 was authored by Ping-Ke Shih and carried through stable channels by Sasha Levin. The upstream commit identified in public records is957eda596c7665f2966970fd1dcc35fe299b38e8, and the same fix is referenced across stable commit lines. Ubuntu’s tracker notes that the issue was introduced by an earlier commit and fixed by that upstream change, with Linux 7.0-rc1 identified as containing the fix in the mainline path.This is the kernel’s industrial process in miniature. A driver maintainer sees or receives a crash, produces a small correctness patch, it lands upstream, and stable maintainers propagate it into supported release branches. Later, the CVE machinery assigns an identifier to the resolved vulnerability, and distribution trackers begin mapping the fix against their kernel packages.
That order often surprises people. In the Linux kernel world, the fix may exist before the vulnerability record is fully enriched. The CVE record may lag behind the commit. Distribution status may lag behind both. NVD scoring may appear after admins have already patched through ordinary kernel updates.
For security teams trained on vendor advisories as the beginning of the process, this can feel backwards. In open-source infrastructure, the commit is frequently the primary artifact. The CVE is the tracking wrapper added after the fact, useful for inventory, compliance, and notification, but not always the first sign that something important changed.
That is why blindly waiting for NVD to fill in CVSS details can be a mistake. If your environment contains the affected driver and a fixed kernel is available from your distribution, the absence of an NVD score is not a reason to delay routine patching. Conversely, a high third-party score is not a reason to emergency-patch machines that do not have the hardware or module exposure.
The Abnormal Device Is the Oldest Problem in Modern Security
Operating systems have spent decades learning not to trust input from the network. They have spent nearly as long learning not to trust files, fonts, images, archives, USB descriptors, and browser content. Hardware-originated metadata still sits in a more ambiguous mental category.Drivers often behave as though the device is a partner. That is understandable. Device drivers are written to make hardware work, not to litigate every field returned by a chip. Performance pressures also push driver authors toward lean fast paths: avoid branches, avoid logging, avoid unnecessary checks in interrupt-sensitive code.
But hardware reports are input. Firmware is input. DMA-visible state is input. Completion queues, descriptor rings, sequence numbers, and status reports are all untrusted data crossing a boundary into privileged software.
CVE-2026-43213 is modest because the fix is modest. It is also profound because it captures the fundamental rule: if a value controls an array index in kernel space, validate it. The driver already had a special-case guard for an unexpected firmware-command release report channel. The new patch adds the equivalent guard for sequence numbers. That is not glamorous, but it is exactly the kind of small guardrail that keeps a rare device anomaly from becoming a system-wide failure.
This pattern is not unique to Wi-Fi. Storage controllers, GPUs, USB devices, Thunderbolt docks, Ethernet adapters, smart-card readers, webcams, and Bluetooth chipsets all feed complex state back into the kernel. Every one of those paths contains assumptions about what the device can and cannot say. Every wrong assumption is a potential crash, privilege boundary problem, or data corruption event.
Linux Desktop Users Will Feel This Differently Than Server Admins
For Linux desktop users, the likely experience of this class of issue is maddeningly familiar: the system freezes, the network disappears, the journal contains rtw89 noise, and the advice online ranges from “try the LTS kernel” to “disable PCIe power saving” to “install this out-of-tree driver.” CVE-2026-43213 gives one specific failure mode a name, but it lives in a broader ecosystem of Wi-Fi stability complaints.The practical question for an affected laptop user is simple: which kernel are you running, and does your distribution include the fix? Rolling distributions may absorb the patch quickly. Enterprise distributions may backport it into older kernel series while keeping their external version numbers stable. Ubuntu’s tracker, as of May 7, 2026, still showed “Needs evaluation” across several supported releases, which means users should watch their normal security and kernel update channels rather than assuming a status from the mainline version alone.
For server admins, the story is usually narrower. Most production servers do not rely on Realtek PCI Wi-Fi. Many do not load rtw89 at all. If the module is absent, blacklisted, or irrelevant to the hardware, the operational risk is low. But edge devices are different. Retail endpoints, industrial PCs, digital signage, conference-room appliances, and small-office Linux boxes often use commodity Wi-Fi parts because they are cheap and available.
That is where the bug deserves more attention. The closer Linux moves to the edge, the more it inherits laptop-class hardware risk. A driver that is irrelevant in a rack can be central in a fleet of tablets, kiosks, or field service devices. Kernel CVE triage based only on “server relevance” can miss those environments.
The right operational move is not panic. It is inventory. Identify machines with Realtek rtw89 PCI devices, check whether the rtw89 PCI module is loaded, map kernel package versions to distributor advisories, and apply the fixed kernel when it arrives through supported channels.
CVE Inflation Makes Context More Valuable, Not Less
The Linux kernel’s CVE pipeline has changed the tone of vulnerability tracking. More kernel fixes are receiving CVE identifiers, including many that look like ordinary robustness patches. That can produce fatigue. If every NULL dereference is a CVE, admins may reasonably ask whether the label still communicates urgency.The answer is that CVEs are identifiers, not arguments. They tell us there is a trackable vulnerability record. They do not, by themselves, tell us whether an issue is reachable in your environment, exploitable by your adversary model, or worth disrupting production to patch out of band.
CVE-2026-43213 is a good example of why context is the scarce resource. The affected component is specific: the Realtek rtw89 PCI Wi-Fi driver. The failure mode is specific: abnormal TX release report sequence numbers causing out-of-bounds access into a descriptor-page array and a NULL pointer dereference. The known impact is specific: kernel crash. The remediation is specific: take a kernel containing the sequence-number validation patch.
That specificity is more useful than a naked score. A CVSS number, once NVD or another authority provides one, may help dashboards sort queues. But a score cannot tell you whether your fleet contains the hardware. It cannot tell you whether a crash in a Wi-Fi driver affects your call center laptops more than your cloud nodes. It cannot tell you whether your distribution has already backported the fix without changing the kernel’s apparent major version.
For WindowsForum’s audience, this is the administrative lesson: vulnerability management is becoming less about memorizing vendor silos and more about interpreting component exposure. The patch cadence for Windows, Linux, firmware, drivers, browsers, and cloud agents increasingly overlaps. The winning teams will be the ones that can translate a CVE into an asset question quickly.
The Fix Is Small Because the Assumption Was Large
There is a temptation to look at the diff and ask why the check was not there from the beginning. That temptation is understandable, but not always fair. Drivers evolve under pressure: new chips, new firmware, new bus behaviors, new power-management states, new recovery paths, new report formats. A field that seemed naturally bounded when a feature was added can later become risky as surrounding assumptions change.The old code path parsed the release report, filtered an unexpected transmit channel, then indexed into the write-descriptor ring using the reported sequence. The new code inserts a sanity gate before that index. If the sequence is greater than or equal to the maximum transmit descriptor count, the driver warns and returns.
That choice is conservative. It does not attempt to repair the sequence, resynchronize aggressively, or infer what the hardware meant. It refuses to act on an invalid report. In a low-level driver, that is often the safest possible response: preserve kernel integrity first, then let higher-level recovery mechanisms handle the device oddity.
The patch also uses
unlikely, a kernel hint that the branch is not expected on the hot path. That tiny detail captures the compromise at the heart of driver hardening. The common case remains fast. The rare case is no longer fatal. The code acknowledges that abnormal values should not happen often while still accepting that they do happen.This is how mature systems become more reliable over time. Not through one sweeping rewrite, but through accumulated humility. Every check like this is a scar from a real failure.
Fleet Owners Should Patch, But They Should Also Learn
For individual users, the recommendation is straightforward: install your distribution’s kernel updates when they include the fix. Avoid random driver forks unless you have a clear reason and understand the maintenance cost. If you are affected by rtw89 crashes today, keep logs, note kernel versions, and test a fixed kernel from your distribution or a trusted mainline build path.For enterprise admins, the better answer starts with segmentation of relevance. A Linux kernel CVE can be urgent on one hardware class and irrelevant on another. The presence of a CVE in a Microsoft security feed does not remove the need to understand the Linux component underneath it.
This is also a good moment to revisit how endpoint inventories record hardware. Many organizations can tell you the OS version, EDR agent version, browser version, and disk encryption state of every laptop. Fewer can quickly answer which Wi-Fi chipset and kernel module each Linux endpoint uses. For driver CVEs, that missing layer is the difference between targeted remediation and dashboard panic.
The same is true for edge Linux. The devices most likely to use commodity Wi-Fi are often the least loved by central IT: signage boxes, lab systems, scanners, shared-room appliances, training carts, and remote-office devices. Those machines may not sit in the same patch pipeline as servers, yet they can still crash, lose connectivity, and generate operational outages.
The smart move is to fold hardware-linked kernel exposure into ordinary vulnerability management. Not every driver bug should page the CISO. But every driver bug should be mappable to actual machines.
The Realtek Crash Leaves a Short Checklist Behind
CVE-2026-43213 is not a five-alarm fire, but it is a useful test of whether your patching process understands hardware-specific Linux risk. Treat it as a targeted kernel maintenance issue, not a generic Internet-wide crisis.- Systems without the Realtek rtw89 PCI Wi-Fi driver in use are unlikely to be meaningfully exposed to this specific flaw.
- Systems using affected Realtek rtw89 PCI Wi-Fi hardware should receive a kernel update that includes the sequence-number validation fix.
- The known failure mode is a kernel crash from a NULL pointer dereference, not a publicly demonstrated remote code-execution chain.
- Distribution status matters more than mainline version numbers because vendors often backport kernel fixes into older supported branches.
- Microsoft’s listing of the CVE is best understood as cross-platform vulnerability tracking, not evidence of a Windows Realtek driver flaw.
- Repeated rtw89 instability on Linux laptops or edge devices should be treated as an operational signal to review kernel, firmware, and driver provenance.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center