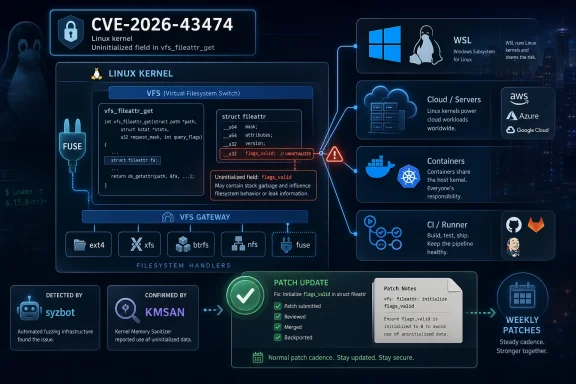
CVE-2026-43474 is a Linux kernel filesystem bug, published in early May 2026 and tracked by Microsoft’s Security Update Guide, that fixes an uninitialized
The core defect is almost comically small: a
That does not automatically make CVE-2026-43474 a dramatic, wormable, internet-facing vulnerability. The available public detail points instead to an uninitialized-value bug found by syzbot and flagged through KMSAN, the Kernel Memory Sanitizer. The patch initializes the field with
But dismissing it as “just a sanitizer bug” would miss the operational lesson. Modern vulnerability management is not only about the spectacular bugs with logos, proofs of concept, and weekend incident bridges. It is also about the quiet defects that move through upstream kernels, stable trees, vendor advisories, cloud images, and enterprise patch queues until someone in IT has to decide whether this matters today, next month, or not at all.
The technical description belongs to the Linux kernel. The affected code is in the filesystem attribute path, not in NTFS, Win32, or the Windows kernel. Microsoft’s role is important because Microsoft now ships, hosts, depends on, or documents Linux in enough places that Linux CVEs routinely appear inside the Microsoft security orbit.
That is the quiet platform shift of the last decade. Windows administrators increasingly patch Linux components without thinking of themselves as Linux administrators. WSL distributions, Azure Linux workloads, Microsoft Defender for Endpoint on Linux, container hosts, appliance images, GitHub-hosted runners, and hybrid developer environments all blur the old boundary.
So the MSRC listing is best read as an ecosystem marker. Microsoft is not saying “this is a Windows kernel flaw.” It is saying, in effect, “this vulnerability may matter to Microsoft customers because Microsoft customers now run a lot of Linux.”
Here, the relevant path involves file attribute retrieval. A user-space request enters a generic VFS layer, which then delegates to filesystem-specific logic. FUSE is especially interesting because it is designed to let user-space filesystems plug into the kernel’s filesystem interface. That flexibility is useful, but it also expands the number of possible code paths and assumptions.
The bug report indicates that
That is why the patch is so deliberately boring. Initialize the structure field before handing it to downstream handlers. Do not rely on caller luck, compiler behavior, stack history, or the kindness of adjacent code. Kernel hardening often looks less like heroic exploit mitigation and more like refusing to let ambiguity survive a function call.
That distinction is useful, but it should not be over-read. Fuzzers regularly uncover bugs that humans later recognize as security-relevant. They also uncover bugs that are hard to exploit, rare in practice, or mostly correctness issues. The existence of a CVE means the ecosystem has decided the defect belongs in vulnerability tracking; it does not, by itself, define urgency.
Syzbot’s value is that it scales boredom. It pounds kernel interfaces with strange combinations, malformed inputs, odd timing, and weird state transitions long after a human tester would have moved on. Filesystem code, ioctl paths, namespace machinery, networking stacks, and driver interfaces all benefit from that relentless abuse.
For IT teams, the practical lesson is not that every syzbot-reported CVE deserves emergency treatment. It is that kernel security increasingly depends on automated discovery pipelines whose output will arrive as a steady stream of small, technically dense advisories. The patch queue is not getting quieter.
That makes it tempting to file CVE-2026-43474 under “routine kernel maintenance.” In many environments, that is probably the right operational category. A desktop user running Windows with no WSL usage and no Linux workloads is unlikely to have a direct action item because of this CVE alone.
But “routine” still means “patch it through the normal channel.” If you maintain Linux hosts, container base images, WSL kernels, developer workstations, CI runners, NAS appliances, hypervisor-side Linux components, or Azure Linux VMs, you should let vendor kernel updates do their job. The point is not to panic over this specific flaw. The point is to avoid building a habit of treating low-drama kernel CVEs as optional forever.
The bug class also deserves respect. Uninitialized reads can be boring correctness problems, information leaks, control-flow oddities, or ingredients in more complex exploit chains depending on context. The public evidence here does not justify melodrama, but kernel history argues against complacency.
WSL 2 runs a real Linux kernel inside a lightweight virtual machine. That architecture is one of the reasons WSL 2 is so capable, but it also means kernel CVEs cannot be dismissed merely because the host OS is Windows. If the WSL kernel contains the affected code, the fix has to arrive through the WSL kernel update mechanism or the relevant Microsoft Store / Windows Update channel.
For most users, the right response is simple: keep WSL current. Developers who use FUSE-heavy workflows, custom filesystems, container tooling, or bleeding-edge distributions inside WSL should be more attentive than someone who occasionally opens Ubuntu to run
The more interesting enterprise issue is inventory. Many organizations have excellent Windows patch compliance dashboards and much weaker visibility into WSL usage on developer endpoints. A Linux kernel flaw inside WSL can therefore exist in the gap between “we patch Windows” and “we patch Linux,” with neither team fully owning it.
CVE-2026-43474 is not the sort of vulnerability that should send every Kubernetes administrator into emergency node rotation. But it is exactly the kind of defect that should be absorbed into the normal cadence of node image refreshes, host kernel updates, and managed cluster maintenance. If your environment depends on FUSE-based storage layers, user-space filesystems, developer containers, or unusual file attribute behavior, the case for prompt testing strengthens.
The same logic applies to CI/CD infrastructure. Build agents and test runners tend to accumulate strange filesystem interactions: bind mounts, overlay filesystems, FUSE mounts, cache directories, artifact stores, and sandboxing tools. These systems are not always treated as production assets, but they frequently handle secrets, source code, signing material, and deployment credentials.
That is why kernel hygiene in build infrastructure deserves more attention than it gets. A low-severity kernel bug on a throwaway runner can still matter if the runner is where your release pipeline lives.
Security teams that grew up triaging vendor advisories by CVSS score and exploitability labels can struggle with kernel CVEs that arrive before scoring is complete, without a polished vendor narrative, or with terse upstream commit messages. The result is a mismatch: the vulnerability database says “security,” while the patch reads like ordinary engineering maintenance.
The answer is not to ignore the CVE stream. The answer is to build a triage model that understands kernel reality. Was the bug introduced only in recent kernels? Does it affect a subsystem you use? Is it reachable by unprivileged local users? Does it require unusual hardware, a specific filesystem, or a configuration you do not deploy? Has your distribution backported the fix under a different version string?
Those questions are more useful than asking whether the advisory sounds scary. Kernel security is contextual. A flaw in a filesystem path you never expose may be background noise; the same flaw in a developer platform with untrusted workloads may deserve faster movement.
That does not mean the patch should be hand-applied casually across production systems. Kernel patching is still kernel patching. Most administrators should consume the fix through their distribution, cloud image provider, appliance vendor, or Microsoft’s relevant update mechanism if WSL or Microsoft-managed Linux components are involved.
But the narrowness of the patch helps frame the risk conversation. If a vendor ships the update, there is little reason to avoid it out of fear that this particular fix will destabilize the filesystem stack. The broader regression risk comes from the full kernel update bundle, not from this initializer alone.
This is where mature patch operations separate themselves from reactive ones. They do not debate each minor CVE as if it were a courtroom drama. They maintain rings, snapshots, rollback plans, and maintenance windows so routine kernel fixes can flow without becoming bespoke emergencies.
That machine is useful, but it is not gentle. It can hand a Windows admin a Linux kernel CVE with a Microsoft-branded source line and expect the organization to know what to do next. In smaller IT shops, that context-switching is painful. In larger enterprises, it becomes a workflow problem across endpoint, server, cloud, and developer platform teams.
The danger is not that CVE-2026-43474 will be misunderstood as the next great Windows crisis. The danger is that it will be misunderstood in both directions: over-escalated by teams that see “Microsoft” and “CVE,” or under-triaged by teams that see “Linux” and assume it belongs to someone else.
Good vulnerability management lives between those mistakes. It asks where the affected code actually runs, who owns that runtime, how updates arrive, and what compensating controls exist until patching completes.
For Windows developer workstations with WSL 2 enabled, it belongs in the “keep the platform current” bucket. Developers should update WSL, distributions, and container tooling as part of normal hygiene. Organizations should know whether WSL is allowed, monitored, and patched rather than discovering it during an audit.
For Azure and hybrid shops, the answer depends on asset inventory. Linux VMs, managed images, AKS nodes, self-hosted runners, and appliances may need attention through their normal vendor channels. The Microsoft branding around the advisory should prompt checking Microsoft-hosted or Microsoft-managed Linux surfaces, not blind assumptions.
For security teams, the CVE is a useful test of process maturity. If your scanners can identify the flaw but your ownership model cannot say who patches the affected kernel, the problem is not this CVE. The problem is the boundary map.
The concrete lessons are straightforward:
Source: MSRC Security Update Guide - Microsoft Security Response Center
flags_valid field before vfs_fileattr_get() calls into filesystem-specific file attribute handlers such as FUSE on affected modern kernels. The fix is tiny, but the story is larger than a one-line initializer. This is another case where the Windows ecosystem has to care about Linux kernel hygiene because WSL, Azure images, containers, appliances, and cross-platform development have made “not a Windows bug” an increasingly thin comfort blanket.
 A One-Line Patch With a Much Bigger Address Book
A One-Line Patch With a Much Bigger Address Book
The core defect is almost comically small: a struct file_kattr variable was being placed on the stack without the flags_valid member being initialized before it was passed into vfs_fileattr_get(). In the FUSE path, that field could be read before being written, which is exactly the sort of thing kernel memory sanitizers are designed to catch.That does not automatically make CVE-2026-43474 a dramatic, wormable, internet-facing vulnerability. The available public detail points instead to an uninitialized-value bug found by syzbot and flagged through KMSAN, the Kernel Memory Sanitizer. The patch initializes the field with
.flags_valid = true, mirroring an existing kernel pattern.But dismissing it as “just a sanitizer bug” would miss the operational lesson. Modern vulnerability management is not only about the spectacular bugs with logos, proofs of concept, and weekend incident bridges. It is also about the quiet defects that move through upstream kernels, stable trees, vendor advisories, cloud images, and enterprise patch queues until someone in IT has to decide whether this matters today, next month, or not at all.
Microsoft’s Presence Here Is the Signal, Not the Root Cause
The user-facing breadcrumb for many WindowsForum readers is Microsoft’s Security Update Guide entry, complete with the familiar Knowledge Base disclaimer language. That framing can make the vulnerability look, at first glance, like a Microsoft-originated Windows defect. It is not.The technical description belongs to the Linux kernel. The affected code is in the filesystem attribute path, not in NTFS, Win32, or the Windows kernel. Microsoft’s role is important because Microsoft now ships, hosts, depends on, or documents Linux in enough places that Linux CVEs routinely appear inside the Microsoft security orbit.
That is the quiet platform shift of the last decade. Windows administrators increasingly patch Linux components without thinking of themselves as Linux administrators. WSL distributions, Azure Linux workloads, Microsoft Defender for Endpoint on Linux, container hosts, appliance images, GitHub-hosted runners, and hybrid developer environments all blur the old boundary.
So the MSRC listing is best read as an ecosystem marker. Microsoft is not saying “this is a Windows kernel flaw.” It is saying, in effect, “this vulnerability may matter to Microsoft customers because Microsoft customers now run a lot of Linux.”
The Filesystem Layer Is Where Abstractions Go to Leak
Filesystem code is a poor place to be casual about initialization. It sits at the border between user requests, kernel metadata, filesystem-specific implementations, compatibility behaviors, and sometimes untrusted or semi-trusted backends. A field that looks like a hint in one layer can become a branch selector in another.Here, the relevant path involves file attribute retrieval. A user-space request enters a generic VFS layer, which then delegates to filesystem-specific logic. FUSE is especially interesting because it is designed to let user-space filesystems plug into the kernel’s filesystem interface. That flexibility is useful, but it also expands the number of possible code paths and assumptions.
The bug report indicates that
fuse_fileattr_get() could read flags_valid from a structure that had not been properly initialized in the file_getattr syscall path. If stack garbage happened to look like one value, the code could take one path; if it looked like another, it could take a different one. In a kernel, “undefined but probably harmless” is not a policy. It is a bet.That is why the patch is so deliberately boring. Initialize the structure field before handing it to downstream handlers. Do not rely on caller luck, compiler behavior, stack history, or the kindness of adjacent code. Kernel hardening often looks less like heroic exploit mitigation and more like refusing to let ambiguity survive a function call.
Syzbot Has Become the Kernel’s Most Relentless Junior Engineer
The discovery path matters. CVE-2026-43474 appears to have been reported by syzbot, the automated bug-finding system built around syzkaller fuzzing. That detail tells administrators two things at once: the bug was real enough for sanitizer instrumentation to complain, and it may not have emerged from a known attacker campaign.That distinction is useful, but it should not be over-read. Fuzzers regularly uncover bugs that humans later recognize as security-relevant. They also uncover bugs that are hard to exploit, rare in practice, or mostly correctness issues. The existence of a CVE means the ecosystem has decided the defect belongs in vulnerability tracking; it does not, by itself, define urgency.
Syzbot’s value is that it scales boredom. It pounds kernel interfaces with strange combinations, malformed inputs, odd timing, and weird state transitions long after a human tester would have moved on. Filesystem code, ioctl paths, namespace machinery, networking stacks, and driver interfaces all benefit from that relentless abuse.
For IT teams, the practical lesson is not that every syzbot-reported CVE deserves emergency treatment. It is that kernel security increasingly depends on automated discovery pipelines whose output will arrive as a steady stream of small, technically dense advisories. The patch queue is not getting quieter.
The Risk Looks Low, but “Low” Is Not the Same as “Ignore”
Based on the public patch trail, this looks like a contained fix for an uninitialized read in a relatively specific syscall and filesystem interaction. There is no public indication in the material at hand of broad remote exploitation, active attacks, or a simple privilege-escalation recipe. The fix itself is a one-line initialization.That makes it tempting to file CVE-2026-43474 under “routine kernel maintenance.” In many environments, that is probably the right operational category. A desktop user running Windows with no WSL usage and no Linux workloads is unlikely to have a direct action item because of this CVE alone.
But “routine” still means “patch it through the normal channel.” If you maintain Linux hosts, container base images, WSL kernels, developer workstations, CI runners, NAS appliances, hypervisor-side Linux components, or Azure Linux VMs, you should let vendor kernel updates do their job. The point is not to panic over this specific flaw. The point is to avoid building a habit of treating low-drama kernel CVEs as optional forever.
The bug class also deserves respect. Uninitialized reads can be boring correctness problems, information leaks, control-flow oddities, or ingredients in more complex exploit chains depending on context. The public evidence here does not justify melodrama, but kernel history argues against complacency.
WSL Makes This a Windows Story by Proximity
For WindowsForum readers, the obvious question is whether this touches Windows Subsystem for Linux. The answer depends on which kernel line and update path a given WSL installation is using, and that is precisely why the Windows angle matters. WSL turned Linux kernel patching into a Windows-adjacent maintenance task.WSL 2 runs a real Linux kernel inside a lightweight virtual machine. That architecture is one of the reasons WSL 2 is so capable, but it also means kernel CVEs cannot be dismissed merely because the host OS is Windows. If the WSL kernel contains the affected code, the fix has to arrive through the WSL kernel update mechanism or the relevant Microsoft Store / Windows Update channel.
For most users, the right response is simple: keep WSL current. Developers who use FUSE-heavy workflows, custom filesystems, container tooling, or bleeding-edge distributions inside WSL should be more attentive than someone who occasionally opens Ubuntu to run
grep. The risk differential comes from exposure, not from the CVE name itself.The more interesting enterprise issue is inventory. Many organizations have excellent Windows patch compliance dashboards and much weaker visibility into WSL usage on developer endpoints. A Linux kernel flaw inside WSL can therefore exist in the gap between “we patch Windows” and “we patch Linux,” with neither team fully owning it.
Cloud and Container Teams Should Read This as Kernel Debt
Containers do not carry their own kernel. That familiar sentence is still the shortest explanation for why kernel CVEs matter in container-heavy environments. A vulnerable userspace image may be rebuilt by an application team, but a vulnerable host kernel has to be handled by the platform team.CVE-2026-43474 is not the sort of vulnerability that should send every Kubernetes administrator into emergency node rotation. But it is exactly the kind of defect that should be absorbed into the normal cadence of node image refreshes, host kernel updates, and managed cluster maintenance. If your environment depends on FUSE-based storage layers, user-space filesystems, developer containers, or unusual file attribute behavior, the case for prompt testing strengthens.
The same logic applies to CI/CD infrastructure. Build agents and test runners tend to accumulate strange filesystem interactions: bind mounts, overlay filesystems, FUSE mounts, cache directories, artifact stores, and sandboxing tools. These systems are not always treated as production assets, but they frequently handle secrets, source code, signing material, and deployment credentials.
That is why kernel hygiene in build infrastructure deserves more attention than it gets. A low-severity kernel bug on a throwaway runner can still matter if the runner is where your release pipeline lives.
The CVE Firehose Is Now Part of the Linux Kernel Deal
There is also a broader policy story behind CVE-2026-43474. The Linux kernel project’s CVE assignment practices have made many more kernel fixes visible as CVEs than administrators were used to seeing in earlier eras. That has improved transparency, but it has also increased noise.Security teams that grew up triaging vendor advisories by CVSS score and exploitability labels can struggle with kernel CVEs that arrive before scoring is complete, without a polished vendor narrative, or with terse upstream commit messages. The result is a mismatch: the vulnerability database says “security,” while the patch reads like ordinary engineering maintenance.
The answer is not to ignore the CVE stream. The answer is to build a triage model that understands kernel reality. Was the bug introduced only in recent kernels? Does it affect a subsystem you use? Is it reachable by unprivileged local users? Does it require unusual hardware, a specific filesystem, or a configuration you do not deploy? Has your distribution backported the fix under a different version string?
Those questions are more useful than asking whether the advisory sounds scary. Kernel security is contextual. A flaw in a filesystem path you never expose may be background noise; the same flaw in a developer platform with untrusted workloads may deserve faster movement.
The Patch Tells Admins More Than the Advisory Does
The most useful fact about CVE-2026-43474 is the shape of the fix. A single field is initialized before a VFS helper calls into filesystem-specific code. That is a narrow change, and narrow changes are generally easier to test, easier to backport, and less likely to produce disruptive regressions than invasive rewrites.That does not mean the patch should be hand-applied casually across production systems. Kernel patching is still kernel patching. Most administrators should consume the fix through their distribution, cloud image provider, appliance vendor, or Microsoft’s relevant update mechanism if WSL or Microsoft-managed Linux components are involved.
But the narrowness of the patch helps frame the risk conversation. If a vendor ships the update, there is little reason to avoid it out of fear that this particular fix will destabilize the filesystem stack. The broader regression risk comes from the full kernel update bundle, not from this initializer alone.
This is where mature patch operations separate themselves from reactive ones. They do not debate each minor CVE as if it were a courtroom drama. They maintain rings, snapshots, rollback plans, and maintenance windows so routine kernel fixes can flow without becoming bespoke emergencies.
The Microsoft Disclaimer Is a Reminder of the Advisory Machine
The Knowledge Base disclaimer attached to the MSRC entry is boilerplate, but it is revealing boilerplate. Security advisories are not warranties, exploit analyses, or deployment plans. They are structured signals in a much larger machine that includes upstream maintainers, vendors, package builders, cloud operators, vulnerability databases, scanners, and customers.That machine is useful, but it is not gentle. It can hand a Windows admin a Linux kernel CVE with a Microsoft-branded source line and expect the organization to know what to do next. In smaller IT shops, that context-switching is painful. In larger enterprises, it becomes a workflow problem across endpoint, server, cloud, and developer platform teams.
The danger is not that CVE-2026-43474 will be misunderstood as the next great Windows crisis. The danger is that it will be misunderstood in both directions: over-escalated by teams that see “Microsoft” and “CVE,” or under-triaged by teams that see “Linux” and assume it belongs to someone else.
Good vulnerability management lives between those mistakes. It asks where the affected code actually runs, who owns that runtime, how updates arrive, and what compensating controls exist until patching completes.
Where Windows Administrators Should Draw the Line
For traditional Windows desktops and servers with no Linux runtime, no WSL, and no Linux-based appliance dependency, CVE-2026-43474 is mostly informational. It may appear in scanners or advisory feeds, but it should not be treated as a Windows OS emergency.For Windows developer workstations with WSL 2 enabled, it belongs in the “keep the platform current” bucket. Developers should update WSL, distributions, and container tooling as part of normal hygiene. Organizations should know whether WSL is allowed, monitored, and patched rather than discovering it during an audit.
For Azure and hybrid shops, the answer depends on asset inventory. Linux VMs, managed images, AKS nodes, self-hosted runners, and appliances may need attention through their normal vendor channels. The Microsoft branding around the advisory should prompt checking Microsoft-hosted or Microsoft-managed Linux surfaces, not blind assumptions.
For security teams, the CVE is a useful test of process maturity. If your scanners can identify the flaw but your ownership model cannot say who patches the affected kernel, the problem is not this CVE. The problem is the boundary map.
The Small Initializer That Should Change the Patch Conversation
CVE-2026-43474 will not be remembered as a landmark vulnerability, and that is precisely why it is useful. It shows how modern platform risk often arrives: a small upstream Linux fix, an automated bug report, a Microsoft-tracked advisory, and a mixed audience of Windows admins, cloud operators, developers, and security teams trying to decide whether the item is theirs.The concrete lessons are straightforward:
- CVE-2026-43474 is a Linux kernel filesystem issue involving an uninitialized
flags_validfield beforevfs_fileattr_get()invokes filesystem-specific attribute handling. - The public patch trail points to a syzbot and KMSAN-discovered uninitialized-value bug, not to confirmed active exploitation.
- The fix is small, but affected systems should still receive it through normal kernel update channels rather than through ad hoc source edits.
- Windows users mainly need to care if they run WSL 2, Linux virtual machines, containers, developer tooling, or Microsoft-managed Linux workloads.
- Enterprise teams should use this CVE to verify ownership of Linux kernels hiding inside Windows-adjacent workflows, cloud infrastructure, and CI/CD systems.
Source: MSRC Security Update Guide - Microsoft Security Response Center