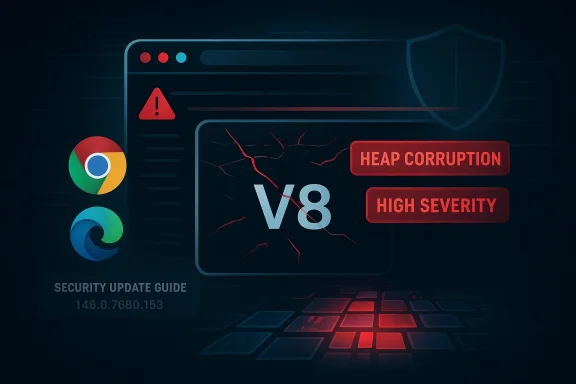
Chromium’s CVE-2026-4457 is another reminder that the browser’s most dangerous flaws are often the ones buried deepest in its engine: V8, the JavaScript and WebAssembly runtime that underpins modern web execution. The public description says the bug is a type confusion issue that could let a remote attacker trigger heap corruption through a crafted HTML page, and the severity assigned by Chromium is High. Microsoft’s Security Update Guide now lists the issue as affecting Chromium-based products, including Microsoft Edge, which is exactly the kind of downstream visibility enterprise administrators need when tracking upstream browser fixes um sits at the center of the modern browser ecosystem because so many products inherit its codebase, release cadence, and security posture. Google Chrome is the most visible shipping product, but Chromium itself is the underlying engine family that also powers Microsoft Edge and several other browsers, web views, and embedded browser shells. That makes every security flaw in Chromium more than a single-vendor problem; it becomes part of a broader platform-risk conversation for enterprises, schools, managed desktops, and consumer devices alike.
The reason V8 matters so much is simple: it is the execution engine for highly dynamic web content. JavaScript has to be fast, flexible, and constantly optimized, which means the engine performs deep type inference and speculative execution under the hood. When those assumptions fail, a type confusion bug can turn a normal-looking page into a memory-safety problem, and memory-safety issues in browser engines are among the most security-significant bugs a vendor can patch.
Google’s March 2026 Chrome security cadence shows how quickly the Chromium team has been closing serious issues in the 146 release line. The Stable channel moved to 146.0.7680.71/72 on March 10, 2026, then to 146.0.7680.75/76 on March 12, 2026, with the later update explicitly calling out a remaining high-severity V8 issue and noting that an exploit existed in the wild for a different V8 flaw in that same release window (chromereleases.googleblog.com)
Microsoft’s role is different but equally important. Rather than reinventing Chromium, Edge consumes it, and Microsoft documents Chromium-origin CVEs in the Security Update Guide so administrators can tell when the downstream Edge build has absorbed the upstream fix. That pattern is visible across multiple Chromium CVEs tracked in Microsoft’s guide, and the same logic applies here: the list entry is not an accusation that Microsoft created the bug, but a signal that Edge customers should verify patch ingestion and update status
For security teams, that distinction matters. A Chromium CVE in Microsoft’s guide is a lifecycle marker as much as a vulnerability record. It tells patch managers where the issue originated, which downstream product line depends on it, and whether the remediation path should be treated as urgent, routine, or already complete. In the case of CVE-2026-4457, the combination of High severity, remote attack surface, and crafted HTML delivery makes it squarely part of the “update fast” class of browser defects.
At the center of CVE-2026-4457 is a classic browser-engine failure mode: the engine treats one object or value as though it were a different type than it actually is. That is what type confusion means in practical terms. Instead of simply crashing the page, the bug can corrupt memory structures in ways that may be exploitable by a sufficiently skilled attacker.
The public wording is brief but important. It says that in Google Chrome prior to 146.0.7680.153, a remote attacker could potentially exploit heap corruption via a crafted HTML page. That phrasing suggests web-delivered exploitation, no local privileges, and no special user capability beyond loading a page or being steered to one. In browser-security terms, that is exactly the sort of setup attackers favor because it scales.
The V8 engine is especially attractive because it sits in a high-performance, highly optimized execution path. Every optimization that makes JavaScript feel instantaneous to users also creates opportunities for the engine to make assumptions about shapes, types, and lifetimes. If an attacker can force the engine into a state where those assumptions break, the resulting memory corruption can be far more valuable than an ordinary DOM bug.
A few practical implications follow from that:
That version pin is especially meaningful for administrators using Chrome Enterprise, because browser update lag is one of the easiest places for an attacker to find leverage. If the fix exists but the fleet still lags a few builds behind, the practical risk remains alive even after the vendor has already shipped a patch.
The broader lesson is uncomfortable but familiar. Browser security does not end when a vendor publishes a CVE. It ends only when the last exposed endpoint in an organization has updated and restarted. Anything short of that is paper security, not actual security.
That matters because browser security is cumulative. Attackers do not care whether a flaw is “the one on the bulletin” or one of several patches in the same month. They care whether the browser’s attack surface has been reduced faster than they can weaponize it. A steady run of high-severity releases usually indicates one of two things: either the browser is under active pressure from offensive research, or the codebase remains large and complex enough that memory-safety defects keep surfacing despite strong defensive tooling.
The important point is not simply that V8 has bugs. All complex engines do. The point is that V8 bugs are disproportionately dangerous because they sit on the boundary between ordinary webpage content and the browser’s most privileged execution machinery. A flaw in that layer can turn a simple page visit into a memory-corruption event, and memory corruption remains the dominant substrate for modern browser exploitation.
This is why browser teams increasingly rely on layered defenses:
That matters because Edge is not a fork in the old sense; it is a consumer of Chromium release artifacts. In operational terms, this creates a very specific responsibility split. Google discloses and patches the underlying engine issue, while Microsoft documents the exposure window for Edge customers through its security guidance. The result is a cleaner enterprise workflow, but only if administrators actually use the guide as intended.
This is one of the hidden strengths of the Chromium model: fixes propagate across many products at once. It is also one of its weaknesses, because a flaw in Chromium becomes an ecosystem event. A delay in patching can echo through Chrome, Edge, WebView-based apps, kiosks, and embedded browser controls.
The result is a familiar enterprise decision tree:
That makes the bug especially useful for initial access. Web-delivered exploits are scalable, easy to host, and easy to rotate. If the first exploit attempt fails, the attacker can revise the page structure, tweak the triggering object graph, or alter JavaScript timing until the engine misbehaves the way they want.
This is why modern browser exploitation often looks like ordinary web content rather than obviously malicious code. The page may present as a benign article, login screen, invoice, or support portal. Beneath that surface, the attacker can carefully trigger engine edge cases, then use the corruption primitive to transition into more advanced payload stages.
A likely exploitation progression looks like this:
The Chrome release history around March 2026 shows how quickly the channel can move. Google pushed a Stable release on March 10, then a follow-up Stable update on March 12. That speed is good for security, but it also means administrators need visibility into which build is currently deployed and which build was only partially rolled out
That creates a gap between vendor patch availability and real-world safety. In the browser world, that gap is often where exploitation happens. Attackers do not need every endpoint to be vulnerable; they only need one exposed user on one unmanaged device.
Enterprise teams should focus on:
Consumers are also more likely to underestimate browser risk because modern browsers feel like stable utilities rather than high-value attack surfaces. But the browser is effectively the front door to identity, email, cloud storage, banking, and personal messages. If an attacker can corrupt memory in the browser engine, they may be able to move from a simple web page to account compromise or device intrusion.
This is also why automatic updates are only half the story. The update still has to be installed, and the updated browser still has to restart. Without that final step, the user remains exposed. For many real-world incidents, the decisive factor is not whether the patch exists but whether the user has actually relaunch the browser.
Consumers should remember a few basics:
Chromium’s own release history has repeatedly featured V8-related defects, and Google’s security notes frequently call out engine issues alongside graphics, UI, and sandbox bugs. The larger story is that browser engines sit at the limit of what software can safely do while still remaining fast enough for users to tolerate. Security engineers are constantly tightening one side of the triangle while performance engineers are stretching the other.
But no amount of defensive tooling can eliminate the underlying tension. A browser engine is a high-performance interpreter for hostile input. It processes content from every corner of the internet, much of it under attacker control, and must do so at speed. That makes the browser one of the most heavily attacked pieces of software in computing.
The historical pattern is clear:
That dynamic puts pressure on competitors that rely on Chromium. It also keeps non-Chromium browsers honest, because users increasingly compare patch velocity as a proxy for operational maturity. In a market where browser choice is often shaped by enterprise manageability and security posture rather than raw feature count, fast vulnerability response can become a competitive differentiator.
For Microsoft, the Edge Security Update Guide is part of that trust relationship. It gives administrators a structured way to map upstream Chromium fixes into downstream Edge operations. For Google, the Chrome releases blog remains the public canonical source for the immediate patch narrative. Together, they shape the cadence of browser defense across the Windows ecosystem.
The competitive implications are straightforward:
It will also be worth watching whether additional Chromium disclosures in the 146 line continue to cluster around engine internals, especially V8. If they do, that would reinforce the view that the browser engine remains one of the most valuable targets in modern software exploitation. If the pace slows, that may indicate the current hardening work is paying off, though security teams should never assume that means the risk has disappeared.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
The reason V8 matters so much is simple: it is the execution engine for highly dynamic web content. JavaScript has to be fast, flexible, and constantly optimized, which means the engine performs deep type inference and speculative execution under the hood. When those assumptions fail, a type confusion bug can turn a normal-looking page into a memory-safety problem, and memory-safety issues in browser engines are among the most security-significant bugs a vendor can patch.
Google’s March 2026 Chrome security cadence shows how quickly the Chromium team has been closing serious issues in the 146 release line. The Stable channel moved to 146.0.7680.71/72 on March 10, 2026, then to 146.0.7680.75/76 on March 12, 2026, with the later update explicitly calling out a remaining high-severity V8 issue and noting that an exploit existed in the wild for a different V8 flaw in that same release window (chromereleases.googleblog.com)
Microsoft’s role is different but equally important. Rather than reinventing Chromium, Edge consumes it, and Microsoft documents Chromium-origin CVEs in the Security Update Guide so administrators can tell when the downstream Edge build has absorbed the upstream fix. That pattern is visible across multiple Chromium CVEs tracked in Microsoft’s guide, and the same logic applies here: the list entry is not an accusation that Microsoft created the bug, but a signal that Edge customers should verify patch ingestion and update status
For security teams, that distinction matters. A Chromium CVE in Microsoft’s guide is a lifecycle marker as much as a vulnerability record. It tells patch managers where the issue originated, which downstream product line depends on it, and whether the remediation path should be treated as urgent, routine, or already complete. In the case of CVE-2026-4457, the combination of High severity, remote attack surface, and crafted HTML delivery makes it squarely part of the “update fast” class of browser defects.
 What CVE-2026-4457 Actually Is
What CVE-2026-4457 Actually Is
At the center of CVE-2026-4457 is a classic browser-engine failure mode: the engine treats one object or value as though it were a different type than it actually is. That is what type confusion means in practical terms. Instead of simply crashing the page, the bug can corrupt memory structures in ways that may be exploitable by a sufficiently skilled attacker.The public wording is brief but important. It says that in Google Chrome prior to 146.0.7680.153, a remote attacker could potentially exploit heap corruption via a crafted HTML page. That phrasing suggests web-delivered exploitation, no local privileges, and no special user capability beyond loading a page or being steered to one. In browser-security terms, that is exactly the sort of setup attackers favor because it scales.
Why Type Confusion Is So Dangerous
Type confusion is a memory-safety bug, but it is not just a generic memory-safety bug. It is often a gateway to controlled memory corruption, pointer manipulation, and eventually code execution or sandbox escape chains. Attackers prize these flaws because they can be paired with additional primitives, such as information leaks or JIT spraying, to turn a browser crash into a reliable exploit.The V8 engine is especially attractive because it sits in a high-performance, highly optimized execution path. Every optimization that makes JavaScript feel instantaneous to users also creates opportunities for the engine to make assumptions about shapes, types, and lifetimes. If an attacker can force the engine into a state where those assumptions break, the resulting memory corruption can be far more valuable than an ordinary DOM bug.
A few practical implications follow from that:
- Remote delivery means the attack can be hosted anywhere.
- HTML-triggered exploitation lowers the bar for phishing and watering-hole attacks.
- Heap corruption is often a precursor to full exploitation chains.
- High severity suggests the bug is not merely theoretical.
- Browser ubiquity magnifies the exposure window.
Why the Version Number Matters
The specific fixed version, 146.0.7680.153, is the practical dividing line. Chrome releases are not just feature milestones; they are security boundaries. Once a patched build is available, the real question for defenders becomes whether every managed endpoint, unmanaged workstation, kiosk, and VDI image has actually moved to the fixed version.That version pin is especially meaningful for administrators using Chrome Enterprise, because browser update lag is one of the easiest places for an attacker to find leverage. If the fix exists but the fleet still lags a few builds behind, the practical risk remains alive even after the vendor has already shipped a patch.
The broader lesson is uncomfortable but familiar. Browser security does not end when a vendor publishes a CVE. It ends only when the last exposed endpoint in an organization has updated and restarted. Anything short of that is paper security, not actual security.
The March 2026 Chrome Security Context
CVE-2026-4457 does not exist in isolation. It arrives in a release cycle that already featured multiple serious Chromium fixes, including a March 12 Stable update where Google said it was aware that an exploit for CVE-2026-3910 existed in the wild, and a March 10 Stable release that contained 29 security fixes across the Chrome codebase (chromereleases.googleblog.com)That matters because browser security is cumulative. Attackers do not care whether a flaw is “the one on the bulletin” or one of several patches in the same month. They care whether the browser’s attack surface has been reduced faster than they can weaponize it. A steady run of high-severity releases usually indicates one of two things: either the browser is under active pressure from offensive research, or the codebase remains large and complex enough that memory-safety defects keep surfacing despite strong defensive tooling.
V8 as a Recurrent Target
V8 has long been one of Chromium’s highest-value targets because the JavaScript engine sits at the intersection of performance and trust. When Google’s release notes call out V8-specific issues, defenders should read that as a sign that the engine remains a rich source of exploitable state-machine errors, optimization bugs, and object-lifetime mistakes.The important point is not simply that V8 has bugs. All complex engines do. The point is that V8 bugs are disproportionately dangerous because they sit on the boundary between ordinary webpage content and the browser’s most privileged execution machinery. A flaw in that layer can turn a simple page visit into a memory-corruption event, and memory corruption remains the dominant substrate for modern browser exploitation.
This is why browser teams increasingly rely on layered defenses:
- Sandboxing to contain compromise.
- ASLR and CFI to complicate control-flow hijacking.
- Sanitizers during development to catch regressions early.
- Fuzzer coverage to shake out edge cases before release.
- Rapid stable-channel turnarounds to shorten exposure windows.
What Microsoft’s Listing Means for Edge
Microsoft’s Security Update Guide now includes CVE-2026-4457 as a Chromium-origin issue, which means Edge administrators should treat it as a downstream patch-verification item rather than a separate Microsoft-authored flaw. Microsoft’s broader practice is to catalog Chromium CVEs so customers can confirm when Edge has ingested the upstream Chromium fix and is therefore no longer vulnerableThat matters because Edge is not a fork in the old sense; it is a consumer of Chromium release artifacts. In operational terms, this creates a very specific responsibility split. Google discloses and patches the underlying engine issue, while Microsoft documents the exposure window for Edge customers through its security guidance. The result is a cleaner enterprise workflow, but only if administrators actually use the guide as intended.
Why Downstream Tracking Matters
Enterprise security teams often run mixed browser estates. Some desktops are Chrome-managed, some are Edge-managed, and some are locked into application compatibility settings or OS-level defaults. A Chromium CVE listed in MSRC is a reminder that the vulnerability may affect multiple browser channels even if the disclosure originated upstream in Google’s ecosystem.This is one of the hidden strengths of the Chromium model: fixes propagate across many products at once. It is also one of its weaknesses, because a flaw in Chromium becomes an ecosystem event. A delay in patching can echo through Chrome, Edge, WebView-based apps, kiosks, and embedded browser controls.
The result is a familiar enterprise decision tree:
- Identify the fixed upstream Chromium version.
- Verify whether Edge or another Chromium-based product has ingested that fix.
- Confirm deployment across the fleet.
- Force restarts where necessary.
- Audit laggards and exceptions.
The Exploitation Story Behind Crafted HTML
The phrase crafted HTML page is a clue to the likely attack chain. It implies that the adversary does not need a native payload, installer, or device access. Instead, they need a malicious page, a poisoned ad slot, a compromised site, or an email/social-engineering lure that directs the victim into the browser’s content-processing path.That makes the bug especially useful for initial access. Web-delivered exploits are scalable, easy to host, and easy to rotate. If the first exploit attempt fails, the attacker can revise the page structure, tweak the triggering object graph, or alter JavaScript timing until the engine misbehaves the way they want.
Why HTML-Delivered Exploits Scale So Well
HTML and JavaScript are universal delivery formats. They cross OS boundaries, language barriers, and most user trust assumptions. A page can be embedded in a phishing campaign, delivered through a compromised CMS, or hidden behind a legitimate-looking link shortener, and the victim may never realize the browser itself is the target.This is why modern browser exploitation often looks like ordinary web content rather than obviously malicious code. The page may present as a benign article, login screen, invoice, or support portal. Beneath that surface, the attacker can carefully trigger engine edge cases, then use the corruption primitive to transition into more advanced payload stages.
A likely exploitation progression looks like this:
- Deliver a malicious page.
- Trigger type confusion in V8.
- Convert confusion into heap corruption.
- Use corruption to gain arbitrary memory access.
- Pair with a leak or sandbox escape if needed.
- Deploy a follow-on payload or session theft logic.
Enterprise Exposure and Patch Operations
For enterprises, the real question is not whether the bug is technically interesting. It is whether the exposure can be contained before users encounter malicious content in the wild. Because browsers are updated frequently and often automatically, many organizations assume the problem will self-resolve. That assumption is dangerous when update rings, reboot policies, and holdback channels are involved.The Chrome release history around March 2026 shows how quickly the channel can move. Google pushed a Stable release on March 10, then a follow-up Stable update on March 12. That speed is good for security, but it also means administrators need visibility into which build is currently deployed and which build was only partially rolled out
Where Exposure Usually Hides
The most common failure modes are operational rather than technical. Devices may download the update but fail to restart. Management policies may defer browser restarts to preserve application uptime. Remote workers may remain offline long enough to miss the update window entirely.That creates a gap between vendor patch availability and real-world safety. In the browser world, that gap is often where exploitation happens. Attackers do not need every endpoint to be vulnerable; they only need one exposed user on one unmanaged device.
Enterprise teams should focus on:
- Build verification across all managed browsers.
- Restart enforcement after critical browser updates.
- Exception inventory for legacy apps and kiosk systems.
- Telemetry review for old browser versions.
- User communication so forced restarts do not become support incidents.
Consumer Impact and Everyday Risk
For consumers, the takeaway is simpler: update the browser as soon as the patched build is offered, and restart it. A V8 type confusion bug does not require advanced technical skill from the victim. A malicious link, a drive-by ad, or a compromised site is enough to expose a user who is still on an older version.Consumers are also more likely to underestimate browser risk because modern browsers feel like stable utilities rather than high-value attack surfaces. But the browser is effectively the front door to identity, email, cloud storage, banking, and personal messages. If an attacker can corrupt memory in the browser engine, they may be able to move from a simple web page to account compromise or device intrusion.
Why “Just a Browser Update” Is Misleading
Many users treat browser updates as routine maintenance, similar to icon changes or minor UI tweaks. That mindset is understandable, but it misses the fact that browser updates often carry some of the most important security fixes on the entire system. A single V8 issue can be more dangerous than a month’s worth of cosmetic feature changes.This is also why automatic updates are only half the story. The update still has to be installed, and the updated browser still has to restart. Without that final step, the user remains exposed. For many real-world incidents, the decisive factor is not whether the patch exists but whether the user has actually relaunch the browser.
Consumers should remember a few basics:
- Keep automatic updates enabled.
- Restart the browser after patching.
- Avoid unknown links, especially those sent unexpectedly.
- Be cautious with lookalike sites and short links.
- Assume browser-engine bugs can be weaponized quickly.
Historical Context: Why This Class of Bug Keeps Coming Back
Type confusion in browser engines is not new, and it is not unique to Chrome. It is a recurring pattern across modern JIT compilers and script runtimes because these systems are built to speculate, optimize, and then de-optimize in real time. That performance model is powerful, but it also creates an unusually large surface for logic mistakes.Chromium’s own release history has repeatedly featured V8-related defects, and Google’s security notes frequently call out engine issues alongside graphics, UI, and sandbox bugs. The larger story is that browser engines sit at the limit of what software can safely do while still remaining fast enough for users to tolerate. Security engineers are constantly tightening one side of the triangle while performance engineers are stretching the other.
Why Defenses Help but Do Not End the Problem
Google does an enormous amount of defensive work to keep these bugs from reaching stable releases. The company explicitly credits sanitizers, fuzzers, and control-flow defenses in its release notes, which shows how much of Chrome security depends on catching flaws before they ship (chromereleases.googleblog.com)But no amount of defensive tooling can eliminate the underlying tension. A browser engine is a high-performance interpreter for hostile input. It processes content from every corner of the internet, much of it under attacker control, and must do so at speed. That makes the browser one of the most heavily attacked pieces of software in computing.
The historical pattern is clear:
- Performance optimization introduces speculative logic.
- Speculative logic creates type and state assumptions.
- Attacker-controlled input breaks those assumptions.
- Memory corruption follows.
- Security teams patch, harden, and repeat.
Competitive and Market Implications
Browser vulnerabilities are not just a security issue; they are also a product-trust issue. When Google fixes a high-severity Chromium flaw, it implicitly raises expectations for every downstream browser that consumes the same engine. Microsoft Edge benefits from the shared codebase, but it also inherits the obligation to move quickly and communicate clearly through its update guidanceThat dynamic puts pressure on competitors that rely on Chromium. It also keeps non-Chromium browsers honest, because users increasingly compare patch velocity as a proxy for operational maturity. In a market where browser choice is often shaped by enterprise manageability and security posture rather than raw feature count, fast vulnerability response can become a competitive differentiator.
The Real Business Value of Fast Patching
A vendor that can consistently deliver rapid browser updates earns more than security goodwill. It earns administrative trust. Enterprises care about patch predictability because browser updates can break web apps, shift UI behavior, or disrupt logon flows. If a vendor can close a major memory-safety issue without causing a maintenance nightmare, that is a meaningful product advantage.For Microsoft, the Edge Security Update Guide is part of that trust relationship. It gives administrators a structured way to map upstream Chromium fixes into downstream Edge operations. For Google, the Chrome releases blog remains the public canonical source for the immediate patch narrative. Together, they shape the cadence of browser defense across the Windows ecosystem.
The competitive implications are straightforward:
- Faster fixes reduce headline risk.
- Clearer documentation reduces admin confusion.
- Better patch telemetry reduces exposure.
- Shared engine code spreads both risk and remediation.
- Security maturity influences browser selection in enterprise environments.
Strengths and Opportunities
The good news is that the Chromium ecosystem has built a mature, repeatable response process around high-severity browser bugs. Google has a well-established rapid-patching model, Microsoft provides downstream visibility for Edge, and the versioned release process makes it possible for administrators to verify exposure with precision. That creates a solid foundation for reducing the lifetime of CVE-2026-4457 in real deployments.- Rapid upstream patching shortens the time attackers have to weaponize the bug.
- Version pinning makes remediation clear and auditable.
- Microsoft’s downstream tracking helps Edge administrators confirm fix ingestion.
- Automatic update systems can eliminate much of the manual effort.
- Enterprise management tools can enforce restart and compliance policies.
- Cross-vendor transparency improves operational confidence.
- Shared security language around CVEs makes reporting easier for defenders.
Risks and Concerns
The main concern with a bug like CVE-2026-4457 is not that it exists; it is that a meaningful number of systems may remain exposed after the fix is public. Browser updates are usually automatic, but they are not instantaneous, and many users do not restart quickly enough to finish the remediation cycle. In a high-severity V8 issue, even a short lag can matter if attackers are actively probing for unpatched systems.- Delayed restarts can leave patched browsers functionally vulnerable.
- Mixed browser fleets create inconsistent exposure across endpoints.
- Legacy enterprise applications may delay upgrade adoption.
- Unmanaged devices can miss the update entirely.
- Phishing and malvertising can deliver malicious HTML at scale.
- Exploit chaining can turn memory corruption into broader compromise.
- User complacency remains one of the hardest problems to solve.
Looking Ahead
The next thing to watch is how quickly fixed versions move through Chrome’s stable channel and into any downstream Chromium consumers, including Edge. The March 2026 release pattern suggests that Google is moving aggressively on security issues, but the real measure of success is how fast that patch reaches the last exposed endpoint. Microsoft’s Security Update Guide will remain an important checkpoint for Edge administrators confirming downstream coverageIt will also be worth watching whether additional Chromium disclosures in the 146 line continue to cluster around engine internals, especially V8. If they do, that would reinforce the view that the browser engine remains one of the most valuable targets in modern software exploitation. If the pace slows, that may indicate the current hardening work is paying off, though security teams should never assume that means the risk has disappeared.
- Chrome and Edge build adoption
- Any follow-on disclosures in V8
- Whether exploit activity appears publicly
- Enterprise update compliance rates
- Future Chrome release notes for the 146 branch
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center