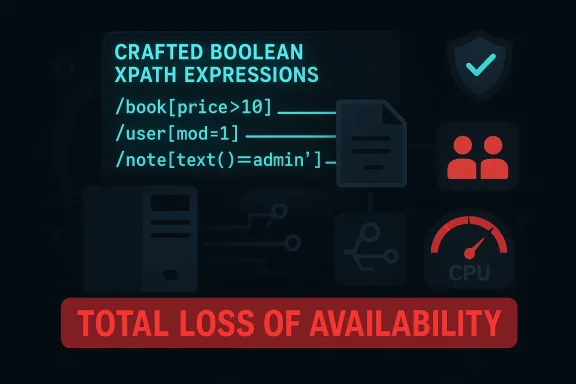
A newly assigned CVE-2026-4645 affects the Go XPath library github.com/antchfx/xpath, and the issue is serious enough to be framed as a denial-of-service risk: specially crafted boolean XPath expressions can drive the component into total loss of availability. The vulnerability description emphasizes that the attacker may be able to fully deny access to resources in the impacted component, either while the malicious input is actively being processed or in a way that leaves the service persistently unavailable afterward. That places this flaw in the same operational category as many recent parser and query-language DoS bugs: small inputs, disproportionate impact, and a patching window that should be treated as urgent.
XPath is one of those quiet dependencies that rarely gets attention until it breaks something important. In the Go ecosystem, antchfx/xpath is widely used for selecting nodes from XML, HTML, and JSON documents, which means it often sits behind web scrapers, integration services, automation tools, document processors, and validation pipelines. The library’s own documentation shows that it supports standard XPath patterns, predicates, comparisons, and boolean expressions, which makes it flexible—but also exposes it to maliciously shaped query logic if those expressions are accepted from users or synthesized from user-controlled data.
The security language attached to CVE-2026-4645 points to a classic availability failure mode rather than a confidentiality or integrity issue. The important clue is the phrase crafted boolean xpath expressions, which suggests that the vulnerable path is not merely “XPath is dangerous” in the abstract, but that specific boolean evaluation behavior can be used to consume excessive resources or trigger a pathological state. That distinction matters because many developers treat XPath as a text-processing helper, when in reality it is an interpreter for a mini query language with recursion, predicate logic, and evaluation semantics that can become expensive very quickly.
This sort of flaw also fits a broader pattern we have seen across parser, template, and expression-evaluation engines: an attacker does not need code execution if they can cheaply monopolize CPU, trigger an infinite loop, or crash a worker process. That can be enough to bring down API endpoints, stall background jobs, interrupt document processing, or exhaust autoscaling capacity. In practice, availability bugs in libraries like this are often underestimated because they do not immediately look like “security” bugs to application teams.
For WindowsForum readers, the operational lesson is straightforward: if your software stack uses Go and processes untrusted XPath input, this is not a theoretical issue. The fact that the affected library is open source and embedded in downstream applications means the blast radius can extend well beyond the direct consumers of
A library can be perfectly safe for ordinary expressions and still be vulnerable to attacker-supplied ones if the evaluation engine does not enforce reasonable limits. That is especially true when the input controls branching, nesting, or repeated evaluation of subexpressions. A small query can be a big hammer when the interpreter’s internal work grows faster than the size of the request.
In practical terms, this means developers should not assume that “it’s just XPath” is a safe mindset. Boolean evaluation in query languages is often where hidden complexity lives, because the engine may need to walk nodes, resolve axes, compare values, and repeatedly backtrack before it can return
That distinction also affects mitigation strategy. If the flaw merely spikes CPU for one request, rate limiting or timeouts might help. If it can crash the process or leave the component in a bad state, then you need version upgrades, isolation boundaries, and potentially circuit breakers or sandboxing. The MSRC-style description makes clear this is not a benign slowdown bug.
In many applications, XPath sits close to user input even when developers do not think of it as such. A web scraper may take a user-defined filter, a document service may accept a template, a rules engine may build queries dynamically, or an internal integration may allow administrators to define matching logic. Once that expression path is reachable from untrusted input, a denial-of-service issue becomes very practical.
A key takeaway is that the risk is not limited to public-facing applications. Internal tooling can be just as exposed if it processes data from suppliers, partners, log feeds, or upload pipelines. Trust boundaries are often weaker than teams assume, especially in automation-heavy environments where expression strings are passed around without strong validation.
The fact that the vulnerability is in a package used for data extraction rather than networking or cryptography can make it even easier to miss in audits. Teams typically look for TLS bugs, auth bypasses, and deserialization problems first, while expression engines and query builders get less scrutiny. CVE-2026-4645 is another reminder that low-level parsing logic deserves first-class security review.
The exact implementation details are not fully exposed in the publicly visible summary, so caution is appropriate when speculating. Still, bugs like this often arise where evaluators recursively traverse nodes, re-evaluate predicates, or mix type coercion with complex comparison rules. In expression engines, the shape of the input can matter more than its length, which is why a short string can be more dangerous than a long one.
The danger is even worse when the application exposes query construction indirectly. For example, a developer might concatenate user-provided fragments into a larger XPath expression, or let users select from a menu of filters that eventually become boolean clauses. In those designs, security testing often focuses on injection and correctness, while denial-of-service behavior gets little attention until production traffic reveals the problem.
A useful mental model is this: XPath is not just text search. It is a mini interpreter with control flow. Whenever you expose interpreter input to an attacker, you should think about execution cost, depth limits, and failure containment, not only whether the expression is syntactically valid.
If you control the application layer, log the exact XPath expressions being evaluated, at least in sanitized form and with access controls. That can help identify whether the same crafted pattern is being replayed, whether one tenant is responsible for repeated failures, and whether the issue is confined to a particular code path. Visibility matters because availability bugs tend to look like generic instability until you correlate them with input shape.
Availability issues in enterprise environments are especially costly because they tend to cascade. A crashed document worker can delay approvals; a wedged filter service can block customer onboarding; a failing internal API can create retries and duplicate traffic. When the failure is triggered by malformed input, the operational overhead gets even worse because teams must decide whether to block traffic, throttle a tenant, or roll back a release.
That said, patch hygiene is still the first line of defense. Because the package is open source and likely transitive in some environments, it may not be obvious where the vulnerable version sits. Software composition analysis, dependency pinning, and rebuild verification should be standard practice here, not optional extras.
If your organization uses policy engines or content filters built on XPath, the exposure can be broader than it first appears. Those systems are often treated as infrastructure, which means they sit on the path of many other applications. A denial-of-service bug in a shared evaluation engine can therefore become a platform outage, not just an application bug.
For developers, the lesson is more immediate: do not treat query-language input as low-risk text. If your product accepts XPath from users, partners, or upstream systems, you should assume the expression engine is part of the attack surface. The presence of a CVE like this should also prompt a review of whether the feature needs to accept raw XPath at all, or whether a constrained selector model would be safer.
Where XPath must remain, precompiling queries, validating allowed tokens, and placing strict execution limits around evaluation can all reduce risk. None of those steps is a substitute for a patch, but they can soften the impact of a future bug or a maliciously expensive input. Defense in depth is the right phrase here, because no single control is likely to be enough.
The broader developer takeaway is that availability bugs deserve the same respect as code execution bugs in services that process attacker-controlled content. The operational difference between “the service is slow” and “the service is down” is often only a small amount of additional pressure. CVE-2026-4645 is a reminder that parsing layers can be as critical as authentication layers when the wrong input lands at the wrong time.
That is why security teams should treat expression engines as part of the same risk family as XML parsers, regex engines, template interpreters, and archive extractors. Each of those subsystems can be weaponized for resource exhaustion even when they do not expose memory corruption or arbitrary code execution. In an outage-sensitive environment, that is enough to justify urgent patching.
The third lesson is that fallback plans matter. Even if the vulnerable package is patched quickly, your service might still need request timeouts, worker isolation, queue limits, and circuit breakers to survive the next issue. Availability is a system property, not a library property.
There is also a broader test for defenders: whether organizations respond by only updating the package, or whether they take the chance to harden the surrounding application design. The latter matters more in the long run because a second denial-of-service flaw in another expression engine would otherwise produce the same outage pattern. Security work that stops at version numbers is necessary but incomplete.
Finally, it will be worth watching whether additional advisories emerge for adjacent query or parsing components in Go and related ecosystems. The more we see these bugs cluster around interpreter-like libraries, the clearer it becomes that modern application risk is increasingly about resource abuse, not just memory corruption.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
XPath is one of those quiet dependencies that rarely gets attention until it breaks something important. In the Go ecosystem, antchfx/xpath is widely used for selecting nodes from XML, HTML, and JSON documents, which means it often sits behind web scrapers, integration services, automation tools, document processors, and validation pipelines. The library’s own documentation shows that it supports standard XPath patterns, predicates, comparisons, and boolean expressions, which makes it flexible—but also exposes it to maliciously shaped query logic if those expressions are accepted from users or synthesized from user-controlled data.The security language attached to CVE-2026-4645 points to a classic availability failure mode rather than a confidentiality or integrity issue. The important clue is the phrase crafted boolean xpath expressions, which suggests that the vulnerable path is not merely “XPath is dangerous” in the abstract, but that specific boolean evaluation behavior can be used to consume excessive resources or trigger a pathological state. That distinction matters because many developers treat XPath as a text-processing helper, when in reality it is an interpreter for a mini query language with recursion, predicate logic, and evaluation semantics that can become expensive very quickly.
This sort of flaw also fits a broader pattern we have seen across parser, template, and expression-evaluation engines: an attacker does not need code execution if they can cheaply monopolize CPU, trigger an infinite loop, or crash a worker process. That can be enough to bring down API endpoints, stall background jobs, interrupt document processing, or exhaust autoscaling capacity. In practice, availability bugs in libraries like this are often underestimated because they do not immediately look like “security” bugs to application teams.
For WindowsForum readers, the operational lesson is straightforward: if your software stack uses Go and processes untrusted XPath input, this is not a theoretical issue. The fact that the affected library is open source and embedded in downstream applications means the blast radius can extend well beyond the direct consumers of
antchfx/xpath. A vulnerability at the expression engine layer tends to travel quietly through CI systems, document pipelines, ETL jobs, and web services until a bad input causes a queue to stall or a node to disappear from service.What CVE-2026-4645 Means
At a high level, CVE-2026-4645 says an attacker can supply a boolean XPath expression that makes the library misbehave badly enough to deny service. The official wording is unusually strong in describing the outcome: it speaks of total loss of availability, not just a slow request or one failed evaluation. That is the sort of language used when a bug can completely take a component offline, or when repeated exploitation can reliably turn a running service into a dead one.Why boolean expressions matter
Boolean XPath expressions are used constantly in real code. They power filters such as “does this node exist,” “does this attribute equal a value,” or “is any element in this subtree present.” Because they look innocuous, they are often allowed into systems with less scrutiny than full-blown executable code. The danger is that boolean logic can still produce expensive evaluation paths when combined with recursion, predicates, axis traversal, or complex comparisons.A library can be perfectly safe for ordinary expressions and still be vulnerable to attacker-supplied ones if the evaluation engine does not enforce reasonable limits. That is especially true when the input controls branching, nesting, or repeated evaluation of subexpressions. A small query can be a big hammer when the interpreter’s internal work grows faster than the size of the request.
In practical terms, this means developers should not assume that “it’s just XPath” is a safe mindset. Boolean evaluation in query languages is often where hidden complexity lives, because the engine may need to walk nodes, resolve axes, compare values, and repeatedly backtrack before it can return
true or false. If those mechanics are exploitable, the result is a reliability bug with security consequences.The availability impact
The vulnerability description’s emphasis on sustained or persistent denial of service is important. Sustained DoS means the attacker can keep the service down while continuing to send input, while persistent DoS means the condition can survive after the triggering request ends, such as a crashed process, wedged worker, or poisoned state requiring intervention. Either outcome is operationally painful, but persistent failures are especially disruptive because they can force restarts, scaling events, or manual cleanup.That distinction also affects mitigation strategy. If the flaw merely spikes CPU for one request, rate limiting or timeouts might help. If it can crash the process or leave the component in a bad state, then you need version upgrades, isolation boundaries, and potentially circuit breakers or sandboxing. The MSRC-style description makes clear this is not a benign slowdown bug.
Where antchfx/xpath Fits in the Stack
antchfx/xpath is a Go library for selecting nodes from XML, HTML, and JSON documents. Its repository describes support for the common XPath model—node selection, attribute matching, predicates, axes, and expression evaluation—which is exactly why it shows up in so many utilities and services. That versatility is also what makes the vulnerability interesting: the same features that make the package useful also make it a tempting target for maliciously complex queries.In many applications, XPath sits close to user input even when developers do not think of it as such. A web scraper may take a user-defined filter, a document service may accept a template, a rules engine may build queries dynamically, or an internal integration may allow administrators to define matching logic. Once that expression path is reachable from untrusted input, a denial-of-service issue becomes very practical.
Common downstream patterns
The most common downstream patterns are not glamorous, but they are everywhere:- XML or HTML extraction services.
- Test automation and UI inspection tools.
- Data transformation and validation pipelines.
- Search, filtering, or policy-matching engines.
- Internal admin dashboards that evaluate document queries.
These uses are easy to overlook because they are often framed as “helper functionality,” but helper libraries are still part of the attack surface.
following-sibling::* and preceding::*, and standard comparison operators inside expressions. Those features are normal and expected, but they also multiply the number of paths an evaluator may need to consider before it can resolve a boolean result.A key takeaway is that the risk is not limited to public-facing applications. Internal tooling can be just as exposed if it processes data from suppliers, partners, log feeds, or upload pipelines. Trust boundaries are often weaker than teams assume, especially in automation-heavy environments where expression strings are passed around without strong validation.
Why this matters to Go developers
Go has a strong reputation for shipping predictable, simple binaries, and that often leads teams to underestimate the security risk of third-party packages. But a language runtime is only as safe as the libraries it embeds. If the XPath evaluator can be forced into a pathological path, then an otherwise robust Go service can still grind to a halt.The fact that the vulnerability is in a package used for data extraction rather than networking or cryptography can make it even easier to miss in audits. Teams typically look for TLS bugs, auth bypasses, and deserialization problems first, while expression engines and query builders get less scrutiny. CVE-2026-4645 is another reminder that low-level parsing logic deserves first-class security review.
Technical Risk Profile
The strongest clue in the public description is the phrase crafted boolean xpath expressions. That implies the vulnerable behavior is tied to expression evaluation rather than document parsing alone, and likely to a code path where boolean logic can trigger excessive work, recursion, or an unbounded loop. Whether the issue manifests as CPU exhaustion, stack growth, repeated backtracking, or a crash, the security impact remains squarely in the availability category.The exact implementation details are not fully exposed in the publicly visible summary, so caution is appropriate when speculating. Still, bugs like this often arise where evaluators recursively traverse nodes, re-evaluate predicates, or mix type coercion with complex comparison rules. In expression engines, the shape of the input can matter more than its length, which is why a short string can be more dangerous than a long one.
How boolean XPath can go wrong
Boolean XPath expressions can become expensive when they force repeated traversal of large node sets. A query that looks simple to a human may require the engine to walk the tree, resolve relationships, compare values, and short-circuit only after exploring a lot of state. If the evaluator lacks guardrails, the cost can balloon in ways that are disproportionate to the attacker’s effort.The danger is even worse when the application exposes query construction indirectly. For example, a developer might concatenate user-provided fragments into a larger XPath expression, or let users select from a menu of filters that eventually become boolean clauses. In those designs, security testing often focuses on injection and correctness, while denial-of-service behavior gets little attention until production traffic reveals the problem.
A useful mental model is this: XPath is not just text search. It is a mini interpreter with control flow. Whenever you expose interpreter input to an attacker, you should think about execution cost, depth limits, and failure containment, not only whether the expression is syntactically valid.
Indicators of exploitation
Operators looking for signs of abuse should watch for repeated spikes in CPU, a sudden buildup of stuck requests, or worker processes that fail while handling query-heavy endpoints. If the vulnerable library is used in batch jobs, queue backlogs and timeouts may be the first symptom. In persistent DoS scenarios, you may also see the service recover only partially after restart, especially if the triggering input keeps reappearing in a queue or retry loop.If you control the application layer, log the exact XPath expressions being evaluated, at least in sanitized form and with access controls. That can help identify whether the same crafted pattern is being replayed, whether one tenant is responsible for repeated failures, and whether the issue is confined to a particular code path. Visibility matters because availability bugs tend to look like generic instability until you correlate them with input shape.
Practical triage checklist
- Identify every service that imports
github.com/antchfx/xpath. - Determine whether any XPath expression can be influenced by a user, customer, partner, or external feed.
- Review whether the vulnerable code path handles boolean expressions or predicates.
- Check for process crashes, infinite evaluation, or request timeouts tied to XPath input.
- Upgrade or isolate affected components as soon as a patched release is available.
That sort of triage is boring work, but boring work is usually what prevents a short exploit string from becoming a wide outage.
Enterprise Impact
For enterprises, the main concern is not only the vulnerable library itself but the business logic wrapped around it. XPath often appears in integration layers, content management workflows, identity systems, and document processing pipelines. If any of those components becomes unavailable, the impact can spread quickly into user-facing services, helpdesk volume, or failed automation jobs.Availability issues in enterprise environments are especially costly because they tend to cascade. A crashed document worker can delay approvals; a wedged filter service can block customer onboarding; a failing internal API can create retries and duplicate traffic. When the failure is triggered by malformed input, the operational overhead gets even worse because teams must decide whether to block traffic, throttle a tenant, or roll back a release.
Enterprise control points
Enterprises do have leverage, though. They can often enforce centralized dependency scanning, restrict where expression language input is accepted, and add proxy-level protections around document-processing services. They can also require that high-risk parsers run in isolated worker pools rather than in the same process as critical business logic.That said, patch hygiene is still the first line of defense. Because the package is open source and likely transitive in some environments, it may not be obvious where the vulnerable version sits. Software composition analysis, dependency pinning, and rebuild verification should be standard practice here, not optional extras.
If your organization uses policy engines or content filters built on XPath, the exposure can be broader than it first appears. Those systems are often treated as infrastructure, which means they sit on the path of many other applications. A denial-of-service bug in a shared evaluation engine can therefore become a platform outage, not just an application bug.
Consumer and Developer Impact
For consumers, the impact is indirect but still real. End users may never know they are interacting with a service that relies onantchfx/xpath, but they will feel the consequences if that service stops responding. That can show up as a broken search feature, stalled sync, failed import, or a web page that spins indefinitely while the server chokes on malicious input.For developers, the lesson is more immediate: do not treat query-language input as low-risk text. If your product accepts XPath from users, partners, or upstream systems, you should assume the expression engine is part of the attack surface. The presence of a CVE like this should also prompt a review of whether the feature needs to accept raw XPath at all, or whether a constrained selector model would be safer.
Safer design choices
The safest design is often to avoid arbitrary XPath entirely. If the use case only needs a few known filters, define those as explicit options rather than as a free-form expression language. A constrained feature set is easier to test, easier to rate-limit, and less likely to produce interpreter-level edge cases.Where XPath must remain, precompiling queries, validating allowed tokens, and placing strict execution limits around evaluation can all reduce risk. None of those steps is a substitute for a patch, but they can soften the impact of a future bug or a maliciously expensive input. Defense in depth is the right phrase here, because no single control is likely to be enough.
The broader developer takeaway is that availability bugs deserve the same respect as code execution bugs in services that process attacker-controlled content. The operational difference between “the service is slow” and “the service is down” is often only a small amount of additional pressure. CVE-2026-4645 is a reminder that parsing layers can be as critical as authentication layers when the wrong input lands at the wrong time.
Comparison With Similar Parser and Expression Bugs
CVE-2026-4645 is not unique in concept. We have seen many cases where a small, structured input can provoke a disproportionate amount of work from a parser, query engine, or transformation library. The common thread is not the language or framework; it is the combination of attacker-controlled syntax and an evaluator that lacks sufficient guardrails.That is why security teams should treat expression engines as part of the same risk family as XML parsers, regex engines, template interpreters, and archive extractors. Each of those subsystems can be weaponized for resource exhaustion even when they do not expose memory corruption or arbitrary code execution. In an outage-sensitive environment, that is enough to justify urgent patching.
What this teaches defenders
The first lesson is to inventory dependencies by behavior, not just by package name. If a library evaluates expressions, parses complex syntax, or walks recursive data structures, it deserves extra scrutiny. The second lesson is to test worst-case behavior, not just correctness, because successful attacks often look like valid input that happens to be pathological.The third lesson is that fallback plans matter. Even if the vulnerable package is patched quickly, your service might still need request timeouts, worker isolation, queue limits, and circuit breakers to survive the next issue. Availability is a system property, not a library property.
Strengths and Opportunities
The positive side of this incident is that it creates a clean opportunity for teams to harden a frequently overlooked layer of their stack. A CVE tied to XPath evaluation is a useful forcing function because it nudges organizations to inspect dependency paths, query validation, and operational safeguards at the same time.- It highlights a real-world attack surface that many teams under-monitor.
- It encourages dependency inventory discipline across Go services.
- It creates pressure to add timeout and isolation controls around evaluators.
- It pushes teams to reconsider whether they need free-form XPath at all.
- It rewards codebases that already use precompiled or constrained queries.
- It gives security teams a reason to test for resource-exhaustion regressions.
- It improves awareness of how small inputs can cause large outages.
Risks and Concerns
The biggest concern is that availability flaws are often patched slowly because they do not look as urgent as remote code execution. That is a mistake. A denial-of-service condition that can fully take a service offline is still a high-impact security problem, especially when it affects shared infrastructure or customer-facing workloads.- Transitive dependencies may hide the vulnerable package.
- Some services may expose XPath indirectly through plugins or admin tools.
- Attackers may need very little traffic to trigger repeated crashes.
- Operators may misclassify the issue as a generic performance bug.
- Persistent failures can survive restarts if the triggering input is reprocessed.
- Legacy or embedded services may be slow to receive updates.
- Without good logging, the root cause may be difficult to identify quickly.
What to Watch Next
The most important near-term development is whether a patched release or vendor guidance appears for downstream consumers. Once a fix lands, the practical question becomes how quickly package maintainers and application teams can roll it out without breaking their own XPath-heavy workflows. That rollout pace will tell us a lot about how exposed the ecosystem really is.There is also a broader test for defenders: whether organizations respond by only updating the package, or whether they take the chance to harden the surrounding application design. The latter matters more in the long run because a second denial-of-service flaw in another expression engine would otherwise produce the same outage pattern. Security work that stops at version numbers is necessary but incomplete.
Finally, it will be worth watching whether additional advisories emerge for adjacent query or parsing components in Go and related ecosystems. The more we see these bugs cluster around interpreter-like libraries, the clearer it becomes that modern application risk is increasingly about resource abuse, not just memory corruption.
- Confirm the fixed version and upgrade path for affected consumers.
- Audit whether any public or partner-facing endpoint accepts XPath input.
- Add request limits, worker isolation, and timeout controls.
- Review logging for repeated malformed or pathological expressions.
- Re-test services under worst-case query loads after patching.
Source: MSRC Security Update Guide - Microsoft Security Response Center