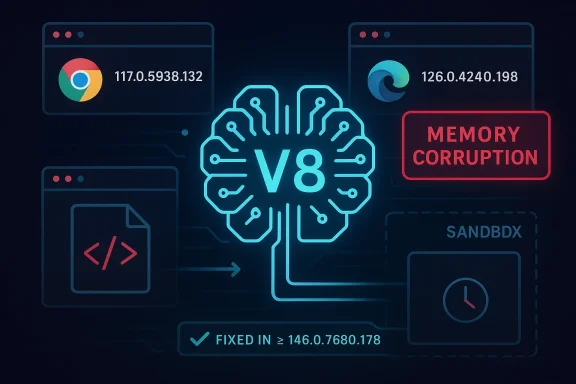
CVE-2026-5279 is another reminder that V8 remains one of Chrome’s most valuable and most dangerous attack surfaces: a memory-corruption bug in the JavaScript engine, reachable through a crafted HTML page, can be turned into code execution inside the browser sandbox if users are not patched quickly. Microsoft’s Security Update Guide records the flaw as affecting Chrome prior to 146.0.7680.178, which is the practical boundary enterprises should use when checking fleet exposure. The vulnerability is rated High in Chromium’s own severity language, while third-party tracking has converged on a network-reachable, user-interaction-dependent exploit profile that still warrants urgent attention.
Chrome security alerts in 2026 have followed a familiar but increasingly urgent pattern: one Chromium release cycle can contain multiple high-severity memory-safety fixes, and downstream browsers such as Microsoft Edge inherit those fixes on their own cadence. That means patch management is no longer just about the browser brand a user sees on screen. It is about understanding which Chromium build has actually landed in the downstream product, and whether that buif.
The V8 engine sits at the center of that story because it executes the JavaScript that powers modern websites, web apps, and large portions of browser-driven enterprise workflows. When V8 experiences object corruption, the bug can become a stepping stone to arbitrary code execution, especially if the attacker can shepherd the browser into the right state with a malicious page. The browser sandbox still matters, but sandboxed code execution is not the same thing as harmless code execution; it is usually the first stage of a broader compromise chain.
Google’s Chrome release notes for March 2026 show a steady progression of security updates from 146.0.7680.71 to 146.0.7680.153, reinforcing that Chrome 146 has been a dense patch train rather than a single-point correction. That context matters because CVE-2026-5279 appears in the same general release window as several other high-risk memory issues, which increases the odds that administrators may need to validate more than one build number across desktop, mobile, and enterprise-managed channels.
Microsoft’s inclusion of the issue in its Security Update Guide is equally important. For Windows admins, the MSRC listing acts as a downstream confirmation layer: it tells them the Chromium vulnerability matters to Edge-adjacent envi upstream in Google’s codebase. In practice, that is how an open-source browser flaw becomes an enterprise patch ticket.
The published description says a remote attacker could execute arbitrary code inside a sandbox via a crafted HTML page. That phrasing is telling. It implies the attack can begin with ordinary web content, without requiring a plugin, local file access, or user-installed helper application. The user interaction requirement still raises the bar a bit, but only a bit: one convincing lure page is enough to make this a practical browser-delivery risk.
There is also an architectural reason V8 flaws are so prized. JavaScript engines are optimized to the edge of what memory safety permits, and modern browser exploit chains often depend on bypassing layers of type confusion, bounds checks, or object layout assumptions. The details of this specific CVE are limited in the public record, but the category alone is enough to justify heightened scrutiny.
Google’s March 2026 release cadence shows that Chrome 146 has already received repeated maintenance updates. That matters because it creates a patching ladder rather than a single jump: some machines may land on 146.0.7680.71, then move to 146.0.7680.153, and then eventually to 146.0.7680.178. Administrators should therefore verify not merely that Chrome is “recent,” but that it has crossed the exact security floor linked to the CVE in question.
For organizations using Chromium-based browsers beyond Google Chrome, the issue becomes even more layered. Microsoft’s Security Update Guide mirrors Chromium CVEs so that Edge administrators can verify whether Microsoft’s downstream channel has incorporated the upstream fix. That is not just documentation overhead; it is the mechanism by which enterprise patch owners avoid false confidence.
The user-interaction element slightly reduces mass-worm potential, but it does not make the bug low risk. Most real-world browser compromises still begin with a click, a page load, or a social-engineering chain that appears mundane to the victim. That is why the practical security value of a browser patch is measured not only by exploit elegance, but by how easily a target can be tricked into activating it.
Chrome’s own history in March 2026 underscores why this matters. Google has already issued urgent fixes for multiple high-severity browser bugs during the same release cycle, including flaws where exploitability was treated as a live concern. CVE-2026-5279 fits that broader pattern of browser security where the difference between a manageable issue and a major incident is often the speed of deployment. ([chromereleases.googleblog.com](https://chromereleases.googleblog.com/2026/03/stable-channel-update-for-desktop_12ass** can come from a single malicious page.
Microsoft’s Security Update Guide entry is especially valuable for Windows environments because it signals when downstream Edge builds have incorporated upstream Chromium fixes. That matters in mixed environments where employees use Chrome, Edge, or both, and where group policy or enterprise management tools can leave one browser patched while another lags behind. The result is a patch gap that looks small on paper but enormous in practice.
This is also a good moment to review web filtering and exploit mitigation layers. While those controls are not substitutes for patching, they can narrow exposure if an attacker tries to deliver a malicious page before the update reaches every machine. Defense in depth matters more when a vulnerability is internet-facing by design.
The most important behavioral risk is not technical curiosity; it is routine browsing. A user does not need to visit an obviously shady site to be exposed if a legitimate service is compromised or a link is routed through a malicious advertising chain. That is why Chrome patch alerts deserve the same urgency as operating-system security updates, even if they arrive with less ceremony.
Consumers who use multiple Chromium browsers should not assume a patch in one app covers the others. Edge, Brave, Vivaldi, and similar browsers may track the same Chromium fix, but each product has its own release schedule. That distinction matters far more than most people realize.
The presence of multiple V8-related bugs in the same general period should also concern defenders. Even when each issue is unique, repeated attention on the JavaScript engine suggests ongoing pressure on the same class of code pn assumed browser memory safety had somehow become a solved problem.
There is a competitive implication too. Browser vendors that ship Chromium-based products must absorb these upstream fixes quickly or risk inheriting the same exposure window. Microsoft’s decision to surfacdat reality: the update ecosystem is now as important as the browser engine itself.
That bridge is useful, but it can also create false comfort if organizations assume an MSRC entry means Edge is patched everywhere immediately. In reality, the guide is a visibility mechanism, not an automatic enforcement mechanism. The update has to be installed, tested, and restarted before the risk is gone.
The practical upshot is simple. If your environment standardizes on more than one Chromium-based browser, your vulnerability management program must treat them as related but separate patch targets. Shared code does not mean shared remediation timing.
A second concern is operational lag. Enterprises may know about the fix long before every endpoint has restarted into the patched build, especially where update deferrals are common. That lag is where real risk lives, because published CVEs quickly become a race between patch deployment and opportunistic exploitation.
It will also be worth watching downstream release timing for Microsoft Edge and other Chromium browsers. The true risk window for most organizations is not the date Google shipped the fix, but the date every managed browser in the fleet actually crossed the vulnerable build boundary. That is the difference between theoretical patch coverage and real reduction in attack surface.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Chrome security alerts in 2026 have followed a familiar but increasingly urgent pattern: one Chromium release cycle can contain multiple high-severity memory-safety fixes, and downstream browsers such as Microsoft Edge inherit those fixes on their own cadence. That means patch management is no longer just about the browser brand a user sees on screen. It is about understanding which Chromium build has actually landed in the downstream product, and whether that buif.The V8 engine sits at the center of that story because it executes the JavaScript that powers modern websites, web apps, and large portions of browser-driven enterprise workflows. When V8 experiences object corruption, the bug can become a stepping stone to arbitrary code execution, especially if the attacker can shepherd the browser into the right state with a malicious page. The browser sandbox still matters, but sandboxed code execution is not the same thing as harmless code execution; it is usually the first stage of a broader compromise chain.
Google’s Chrome release notes for March 2026 show a steady progression of security updates from 146.0.7680.71 to 146.0.7680.153, reinforcing that Chrome 146 has been a dense patch train rather than a single-point correction. That context matters because CVE-2026-5279 appears in the same general release window as several other high-risk memory issues, which increases the odds that administrators may need to validate more than one build number across desktop, mobile, and enterprise-managed channels.
Microsoft’s inclusion of the issue in its Security Update Guide is equally important. For Windows admins, the MSRC listing acts as a downstream confirmation layer: it tells them the Chromium vulnerability matters to Edge-adjacent envi upstream in Google’s codebase. In practice, that is how an open-source browser flaw becomes an enterprise patch ticket.
What CVE-2026-5279 Means
At the technical level, object corruption in V8 usually means the engine lost track of the real layout or type of an object in memory. Once an attacker can influence that state, the next move is often to turn a logic error into a memory-primitive chain: read, write, pivot, and eventually execute. That is why “object corruption” should never be read as a vague stability issue; in browser security, it is a red flag for potential exploitation.The published description says a remote attacker could execute arbitrary code inside a sandbox via a crafted HTML page. That phrasing is telling. It implies the attack can begin with ordinary web content, without requiring a plugin, local file access, or user-installed helper application. The user interaction requirement still raises the bar a bit, but only a bit: one convincing lure page is enough to make this a practical browser-delivery risk.
Why V8 Bugs Matter So Much
V8 is not an edge-case component. It is the engine that makes modern web applications fast enough to feel native, and that same complexity is what makes it arnd a flaw here, they are aiming at the most universal runtime in the browser. That is why V8 fixes often appear in urgent Chrome advisories and why they ripple quickly into the rest of the Chromium ecosystem.There is also an architectural reason V8 flaws are so prized. JavaScript engines are optimized to the edge of what memory safety permits, and modern browser exploit chains often depend on bypassing layers of type confusion, bounds checks, or object layout assumptions. The details of this specific CVE are limited in the public record, but the category alone is enough to justify heightened scrutiny.
- Object corruption often serves as the first reliable memory primitive in a browser exploit chain.
- Crafted HTML means the attacker can deliver the trigger through ordinary web traffic.
- Sandbox escape is not required for serious impact if code execution occurs inside the browser process.
- V8 bugs are especially sensitive because they sit in the most widely exercised execution path on the web.
Patch Timing and Version Boundaries
The version cutoff is the simplest part of the story: Chrome builds prior to 146.0.7680.178 are affected. That gives security teams a concrete compliance test, but only if they are checking the actual installed build and not relying on policy baselines or stale inventory reports. In browser security, the difference between “should be patched” and “is patched” can be a matter of hours or days in managed environments.Google’s March 2026 release cadence shows that Chrome 146 has already received repeated maintenance updates. That matters because it creates a patching ladder rather than a single jump: some machines may land on 146.0.7680.71, then move to 146.0.7680.153, and then eventually to 146.0.7680.178. Administrators should therefore verify not merely that Chrome is “recent,” but that it has crossed the exact security floor linked to the CVE in question.
How to Read the Build Number
The build number is the cleanest operational signal because it is binary: either the vulnerable version is present or it is not. That said, enterprises often complicate the picture with staged rollouts, update deferrals, and application control policies that delay browser restarts. In other words, patch availability and patch adoption are not the samattps://chromereleases.googleblog.com/2026/03/stable-channel-update-for-desktop_18.html)For organizations using Chromium-based browsers beyond Google Chrome, the issue becomes even more layered. Microsoft’s Security Update Guide mirrors Chromium CVEs so that Edge administrators can verify whether Microsoft’s downstream channel has incorporated the upstream fix. That is not just documentation overhead; it is the mechanism by which enterprise patch owners avoid false confidence.
- Confirm the browser family in use, not just the user-facing brand.
- Check the installed Chromium build number on each platform.
- Verify that the version is at or beyond the fixed release.
- Recheck after any policy-driven browser restart or delayed reboot.
- Treat managed and unmanaged endpoints differently in your reporting.
Threat Model and Exploitability
The threat model here is straightforward but serious: a remote attacker lures a target to a malicious page, the page triggers the V8 corruption, and the attacker gains code execution within the browser sandbox. That is not full system compromise by default, but it is a dangerous foothold, especially if paired with a second vulnerability for sandbox escape or privilege elevation.The user-interaction element slightly reduces mass-worm potential, but it does not make the bug low risk. Most real-world browser compromises still begin with a click, a page load, or a social-engineering chain that appears mundane to the victim. That is why the practical security value of a browser patch is measured not only by exploit elegance, but by how easily a target can be tricked into activating it.
Sandbox Context
The sandbox is an important containment boundary, but it is not a magic shield. If an attacker can execute code inside the browser renderer, they may still be able to steal session data, manipulate pages, scrape content, or prepare a follow-on exploit. In many incident-response cases, the sandbox is the first wall, not the last one.Chrome’s own history in March 2026 underscores why this matters. Google has already issued urgent fixes for multiple high-severity browser bugs during the same release cycle, including flaws where exploitability was treated as a live concern. CVE-2026-5279 fits that broader pattern of browser security where the difference between a manageable issue and a major incident is often the speed of deployment. ([chromereleases.googleblog.com](https://chromereleases.googleblog.com/2026/03/stable-channel-update-for-desktop_12ass** can come from a single malicious page.
- Renderer compromise may be enough for data theft or session abuse.
- Sandbox limits reduce but do not eliminate operational risk.
- Follow-on exploitation is what turns a browser bug into an endpoint event.
Enterprise Impact
For enterprises, the real question is not whether Chrome is affected. It is how many endpoints are still below the fixed version, how many are controlled by are stranded on custom release cadences. In large fleets, browsers are often the last application to update because they are considered “just a browser,” and that assumption is precisely what attackers exploit.Microsoft’s Security Update Guide entry is especially valuable for Windows environments because it signals when downstream Edge builds have incorporated upstream Chromium fixes. That matters in mixed environments where employees use Chrome, Edge, or both, and where group policy or enterprise management tools can leave one browser patched while another lags behind. The result is a patch gap that looks small on paper but enormous in practice.
Operational Priorities
Security teams should treat CVE-2026-5279 as part of a broader browser hardening program rather than an isolated event. The best response is not only installing the fixed build, but also verifying restart compliance, reconciling endpoint inventory, and ensuring that browser auto-update policies are not being overridden by legacy software standards.This is also a good moment to review web filtering and exploit mitigation layers. While those controls are not substitutes for patching, they can narrow exposure if an attacker tries to deliver a malicious page before the update reaches every machine. Defense in depth matters more when a vulnerability is internet-facing by design.
- Verify Chrome, Edge, and other Chromium-based browser versions separately.
- Confirm update channels on managed and unmanaged devices.
- Force browser restarts where policy allows.
- Audit exceptions for kiosks, VDI pools, and shared devices.
- Cross-check endpoint telemetry for late patch adoption.
Consumer Impact
For individual users, the story is simpler: update immediately and restart the browser. The combination of remote delivery and a crafted HTML page means there is no meaningful reason to delay if the patch is available on the device. Consumers often assume browser vulnerabilities are abstract or enterprise-only, but this kind of bug sits directly on the path between the user and the modern web.The most important behavioral risk is not technical curiosity; it is routine browsing. A user does not need to visit an obviously shady site to be exposed if a legitimate service is compromised or a link is routed through a malicious advertising chain. That is why Chrome patch alerts deserve the same urgency as operating-system security updates, even if they arrive with less ceremony.
Practical Advice for Home Users
Home users should make sure automatic updates are not paused, disabled, or blocked by an extension, security product, or stale installer. If Chrome or another Chromium-based browser asks for a relaunch, the safest answer is to relaunch. The risk window is usually short, but only if users let the update complete.Consumers who use multiple Chromium browsers should not assume a patch in one app covers the others. Edge, Brave, Vivaldi, and similar browsers may track the same Chromium fix, but each product has its own release schedule. That distinction matters far more than most people realize.
- Restart the browser after updating.
- Check the installed version, not just the update prompt.
- Update every Chromium-based browser on the device.
- Avoid postponing security relaunches.
- Be skeptical of unexpected links, even from familiar senders.
How This Fits the 2026 Chrome Security Pattern
CVE-2026-5279 is not an isolated anomaly. March 2026 has already shown how quickly Chrome releases can stack multiple serious memory-safety fixes into the same channel, spanning V8, Skia, WebMCP, WebAudio, Extensions, and other core subsystems. That density tells us two things: Google’s security engineering is catching serious bugs, and attackers are still finding fertile ground in browser internals.The presence of multiple V8-related bugs in the same general period should also concern defenders. Even when each issue is unique, repeated attention on the JavaScript engine suggests ongoing pressure on the same class of code pn assumed browser memory safety had somehow become a solved problem.
What the Release Cadence Suggests
The release cadence suggests an ecosystem where patch velocity is now a core security control. Chrome’s rapid march from one stable update to the next is a feature, not a bug, because it compresses the time between disclosure and remediation. But it also places a premium on endpoint compliance, because any device that misses a cycle can remain exposed longer than administratorsattps://chromereleases.googleblog.com/2026/03/stable-channel-update-for-desktop_18.html)There is a competitive implication too. Browser vendors that ship Chromium-based products must absorb these upstream fixes quickly or risk inheriting the same exposure window. Microsoft’s decision to surfacdat reality: the update ecosystem is now as important as the browser engine itself.
- Rapid Chrome releases reduce exposure time.
- Downstream browsers still need their own update cadence.
- Repeated V8 issues increase attacker interest.
- Admins should expect layered fixes, not one-off patch events.
Microsoft Edge and Downstream Chromium Consumers
Microsoft Edge matters here because it illustrates how Chromium vulnerabilities propagate. Edge does not create the upstream bug, but it inherits the code and therefore the risk profile. Microsoft’s Security Update Guide acts as the bridge between Google’s upstream adviaworkflow that many enterprises rely on.That bridge is useful, but it can also create false comfort if organizations assume an MSRC entry means Edge is patched everywhere immediately. In reality, the guide is a visibility mechanism, not an automatic enforcement mechanism. The update has to be installed, tested, and restarted before the risk is gone.
Why This Matters Beyond Edge
Any Chromium consumer inherits the same core lesson: upstream browser security is only as good as downstream adoption. If a product ships Chromium at a slower pace, it can remain vulnerable after Chrome itself is fixed. That is one reason browser choice in enterprises has become a policy decision as much as a user-preference decision.The practical upshot is simple. If your environment standardizes on more than one Chromium-based browser, your vulnerability management program must treat them as related but separate patch targets. Shared code does not mean shared remediation timing.
- Edge tracks upstream Chromium fixes through MSRC visibility.
- Other Chromium browsers may lag behind Chrome by days or weeks.
- Patch confirmation should be version-based, not advisory-based.
- Enterprise inventories must distinguish browser families.
Strengths and Opportunities
The good news is that this is a well-defined vulnerability with a clear fixed version, which gives administrators a straightforward way to measure success. The broader Chrome release cadence also shows that Google and downstream vendors are actively pushing security updates through the ecosystem, making it easier to align patching with known build numbers.- Clear affected-verin: update to the fixed build.
- Existing enterprise patch tools can validate version status.
- Browser update channels already exist for rapid distribution.
- Microsoft’s downstream guide improves visibility for Windows admins.
- The issue reinforces good patch hygiene across all Chromium browsers.
- Security teams can fold this into ongoing browser-hardening work.
Risks and Concerns
The main concern is that browser bugs like this are routinely reachable from ordinary web content, which makes them inherently scalable for attackers. Even with sandboxing, successful code execution in the browser process can expose session data, user activity, and a foothold for further exploitation.A second concern is operational lag. Enterprises may know about the fix long before every endpoint has restarted into the patched build, especially where update deferrals are common. That lag is where real risk lives, because published CVEs quickly become a race between patch deployment and opportunistic exploitation.
- A malicious page is enough to trigger the bug.
- Sandbox compromise can still have meaningful impact.
- Delayed n Mixed-browser fleets increase the chance of partial patching.
- Users may assume the issue is fixed when an update is only pending restart.
- Downstream Chromium consumers can lag behind Chrome.
- Memory-corruption bugs often attract exploit-chaining attempts.
Looking Ahead
The next thing to watch is whether Google or the wider ecosystem discloses more detail about the root cause and whether the issue becomes part of a broader cluster of V8 memory-safety findings. When multiple engine bugs surface in the same release window, defenders should assume attackers are already studying the pattern, even if public exploit reports have not appeared yet.It will also be worth watching downstream release timing for Microsoft Edge and other Chromium browsers. The true risk window for most organizations is not the date Google shipped the fix, but the date every managed browser in the fleet actually crossed the vulnerable build boundary. That is the difference between theoretical patch coverage and real reduction in attack surface.
- Confirm whether Edge and other Chromium browsers have reached the fixed build.
- Watch for any new exploit reporting or active exploitation claims.
- Reconcile endpoint telemetry with browser restart status.
- Review whether browser auto-update policies are functioning as intended.
- Keep an eye on whether related V8 issues appear in the same release train.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center