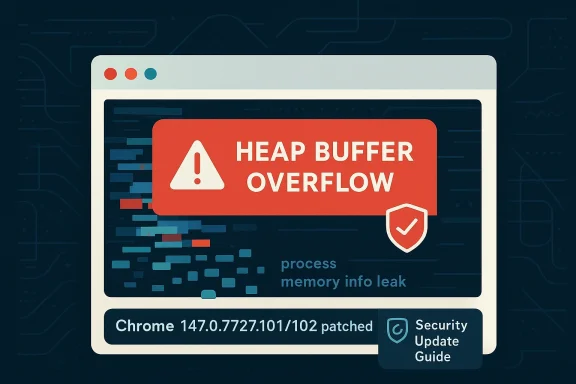
Chromium’s CVE-2026-6298 is a Critical heap buffer overflow in Skia that Google patched in Chrome 147.0.7727.101/102 on April 15, 2026, and Microsoft is now surfacing the same issue in its Security Update Guide for downstream visibility. The public description says a remote attacker could potentially obtain sensitive information from process memory by luring a victim into loading a crafted HTML page, which makes this more than a simple graphics-engine crash. In practice, the case reinforces a familiar browser-security lesson: once a memory-safety flaw lands in a shared subsystem like Skia, the impact can propagate quickly across the Chromium ecosystem. gleblog.com]
Skia sits at the heart of Chromium’s rendering stack, so when a bug appears there, the consequences can spill across text, images, SVG, canvas operations, and layout-driven drawing paths. Google’s release notes identify CVE-2026-6298 as a Critical Skia heap buffer overflow, and the fix was bundled into the April 15 Chrome stable update rather than held back for a later maintenance cycle. That timing matters, because Chrome’s stablribution point that most users and enterprises actually consume.
The vulnerability is particularly interesting because the public impact statement emphasizes information disclosure rather than direct code execution. That does not make it benign; it means the flaw is likely one step earlier in an exploit chain, where an attacker uses a renderer-side leak to reveal memory or other secrets that help defeat mitigations later. In browser exploitation, a leak is often the missing piece that turns a crash into a reliable compromise path.
This is also one of several Chromium issues bundled into the same April 15 release, which included 31 security fixes according to Google. The pattern is telling: browser hardening is increasingly a volume business, where attackers probe a dense attack surface and defenders must close multiple memory-safety defects at once. The update cadence also shows why Chrome and Microsoft Edge users need to pay attention to version numbers rather than just “I already updated recently.”
Microsoft’s Security Update Guide entry is important because it confirms the downstream enterprise view. Microsoft routinely tracks Chromium-origin issues for Edge customers, not because Microsoft authored them, but base inherits Chromium fixes on Google’s schedule. That makes Microsoft’s advisory flow a useful signal for administrators who manage mixed browser fleets and need a single place to verify whether the fix has landed in their environment.
The public advisory also points to CWE-122, the canonical heap-based buffer overflow class. That category is especially troublesome in modern browsers because exploitability often depends less on the overflow itself and more on what the surrounding heap layout looks like at runtime. In other words, the bug class is old, but the engineering work to make it explnt.
The fact that Google rated the issue Critical even though the described impact is information disclosure is not a contradiction. In Chromium security practice, severity is shaped by exploit value in the larger browser threat model, not just the narrow primitive. A reliable memory leak in a browser renderer can be the precondition for sandbox escape or code execution in a chained exploit.
The presence of user interaction also explains whink in terms of exposure windows rather than theoretical severity alone. A flaw that requires a page load may still be highly actionable if it lands in a popular browser engine and remains unpatched across long enterprise update cycles. That is the quiet danger of browser memory bugs: they are often only one social-engineering step away from exploitation.
Google also uses the familiar practice of restricting detailed bug information until a majority of users have updated. That policy is designed to rhich attackers can weaponize technical specifics before most of the installed base is protected. It is a standard browser-security tradeoff: transparency for defenders, but staggered disclosure for safety.
Microsoft’s listing in the Security Update Guide matters because it translates the upstream Chrome fix into downstream Edge governance. For Windows administrators, that often means the question is not “did Google patch it?” but “has my browser channel ingested the Chromium fix yet?” That distinction is practical, not academic.
The practical upside is that Microsoft gives admins a second view into the same vulnerability lifecycle. The same Guide can help with CVE monitoring, product filtering, and release-date inspection, which is useful when organizations standardize around Microsoft reporting pipelines. That makes the ecosystem a little easier to govern, even if the underlying browser risk remains shared.
But there is also a downside: the existence of multiple update channels can lull teams into thinking one browser family is “covered” when it is only eventually covered. That lag is dangerous when the CVE is a memory-corruption issue with exploitation potential. In a managed Windows estate, the right question is not whether the patch exists, but whether it has reached every browser SKU in use.
The UI requirement also suggests a social-engineering component. An attacker might embed malicious content in a spoofed site, an ad frame, a drive-by landing page, or a phish that encourages the victim to open an HTML page. The exploit surface is therefore partly technical and partly behavioral, whist as important as patching.
It is also notable that Google did not disclose broad technical details immediately. That restraint is normal in browser security, but it means defenders should not interpret the lack of public exploit instructions as evidence of low risk. The browser ecosystem has a long history of weaponizing bugs quickly ozle is visible.
This is why Critical in browser advisories deserves close attention even when the headline says “information disclosure.” Security teams should think beyond the immediate impact category and consider what a leak unlocks in the rest of the chain. In a browser context, what it enables is often more important than what it does alone.
The Chrome team’s repeated reliance on memory-safety mitigation tools also tells its own story. Google notes that many bugs are found using sanitizers, fuzzers, and related tooling, which means a significant portion of the security surface is being caught before it becomes public or weaponized. That is good news, but it is also evidence of how much work remains.
The browser security model is now a constant tug-of-war between exploit chains and memory safety engineering. Each new CVE teaches the same uncomfortable lesson: even if sandboxing prevents direct system compromise, attackers can still use renderer bugs, graphics bugs, and information leaks as stepping stones. CVE-2026-6298 fits that exact pattern.
Users who rely on Chromium-based browsers beyond Chrome itself should be especially careful. Many third-party browsers pick up the same engine lineage, which means the vulnerability class is not limited to Google Chrome in a practical sense. The broader Chromium ecosystem inherits the same risk profile even if the branding differs.
For consumers, the best advice is boring but effective. Update, restart, and avoid interacting with suspicious HTML pages or downloads. In browser security, boring is good.
The broader trend is unmistakable: browser security in 2026 is being driven by memory-safety remediation, update speed, and the ability to detect whether a fix has truly landed. The companies that win here are not the ones with the fewest CVEs on paper, but the ones that shrink the time between patch release and fleet-wide protection. That is where real resilience lives.
Watch these items closely:
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Skia sits at the heart of Chromium’s rendering stack, so when a bug appears there, the consequences can spill across text, images, SVG, canvas operations, and layout-driven drawing paths. Google’s release notes identify CVE-2026-6298 as a Critical Skia heap buffer overflow, and the fix was bundled into the April 15 Chrome stable update rather than held back for a later maintenance cycle. That timing matters, because Chrome’s stablribution point that most users and enterprises actually consume.The vulnerability is particularly interesting because the public impact statement emphasizes information disclosure rather than direct code execution. That does not make it benign; it means the flaw is likely one step earlier in an exploit chain, where an attacker uses a renderer-side leak to reveal memory or other secrets that help defeat mitigations later. In browser exploitation, a leak is often the missing piece that turns a crash into a reliable compromise path.
This is also one of several Chromium issues bundled into the same April 15 release, which included 31 security fixes according to Google. The pattern is telling: browser hardening is increasingly a volume business, where attackers probe a dense attack surface and defenders must close multiple memory-safety defects at once. The update cadence also shows why Chrome and Microsoft Edge users need to pay attention to version numbers rather than just “I already updated recently.”
Microsoft’s Security Update Guide entry is important because it confirms the downstream enterprise view. Microsoft routinely tracks Chromium-origin issues for Edge customers, not because Microsoft authored them, but base inherits Chromium fixes on Google’s schedule. That makes Microsoft’s advisory flow a useful signal for administrators who manage mixed browser fleets and need a single place to verify whether the fix has landed in their environment.
What CVE-2026-6298 Actually Means
At a technical level, a heap buffer overflow means code wrote past the bounds of a dynamically all In a graphics library like Skia, the bug can sit in a code path that handles parsing, compositing, rasterization, or surface management, any of which may be influenced by attacker-controlled content embedded in a page. The reason this matters is that graphics code is fed by the browser’s rendering pipeline, which accepts a huge variety of inputs.Why Skia bugs are so sensitive
Skia is not a niche helper library. It is the rendering workhorse underneath browser UI and web content, which means a flaw there can affect how the browser draws the page the user thinks is harmless. A malicious page does not need to “look dangerous” if the weakness is buried inside how the engine handles pixels, paths, masks, or intermediate surfaces. That is exactly why memory bugs in Skia show up repeatedly in browser advisories.The public advisory also points to CWE-122, the canonical heap-based buffer overflow class. That category is especially troublesome in modern browsers because exploitability often depends less on the overflow itself and more on what the surrounding heap layout looks like at runtime. In other words, the bug class is old, but the engineering work to make it explnt.
The fact that Google rated the issue Critical even though the described impact is information disclosure is not a contradiction. In Chromium security practice, severity is shaped by exploit value in the larger browser threat model, not just the narrow primitive. A reliable memory leak in a browser renderer can be the precondition for sandbox escape or code execution in a chained exploit.
The user interaction angle
The NVD-enriched description says the vulnerabili crafted HTML page, and the CVSS 3.1 vector includes UI:R, meaning user interaction is required. That usually translates to the victim having to visit or load attacker-supplied content, which lowers the bar enough for phishing, malicious ads, drive-by content, or link-based delivery. It is not “one-click remote compromise,” but it is still a practical web attack surface.The presence of user interaction also explains whink in terms of exposure windows rather than theoretical severity alone. A flaw that requires a page load may still be highly actionable if it lands in a popular browser engine and remains unpatched across long enterprise update cycles. That is the quiet danger of browser memory bugs: they are often only one social-engineering step away from exploitation.
Timeline and Patch Status
Google’s stable-channel notes show the fix landed on Wednesday, April 15, 2026, with Chrome updated to 147.0.7727.101/102 for Windows and Mac and 147.0.7727.101 for Linux. The same release notes identify CVE-2026-6298 among the security fixes in that build. For most users, that means the remediation path is straightforward: update to the patched version or allow the browser to auto-update into it.What changed in the channel release
The release notes say the stable channel rollout would occur over the coming days and weeks, which is an important operational caveat. Chrome updates are fast, but enterprise policy, offline machines, and managed deployment rings can all slow the arrival of a fixed build. That delay is often where real-world risk accumulates.Google also uses the familiar practice of restricting detailed bug information until a majority of users have updated. That policy is designed to rhich attackers can weaponize technical specifics before most of the installed base is protected. It is a standard browser-security tradeoff: transparency for defenders, but staggered disclosure for safety.
Microsoft’s listing in the Security Update Guide matters because it translates the upstream Chrome fix into downstream Edge governance. For Windows administrators, that often means the question is not “did Google patch it?” but “has my browser channel ingested the Chromium fix yet?” That distinction is practical, not academic.
What enterprise admins should verify
Administrators should check three things in order. First, confirm whether Chrome is on 147.0.7727.101/102 or later. Second, confirm Edge’s Chromium base has incorporated the same fix. Third, validate that update policies are not pinning endpoints to an older release ring longer than necessary. Sequentially, that is the difference between a nominal patch and a real mitigation.- Inventory affected browser versions across endpoints.
- Confirm the patch build is present in Chrome and Edge.
- Validate group policy or MDM update deferrals.
- Force update checks on exposed systems.
- Re-test after the browser restarts.
Why This Matters for Microsoft Edge
Microsoft Edge uses Chromiubrowser fix is a downstream operational issue for Microsoft customers. Microsoft’s Security Update Guide exists partly to make that inheritance visible, especially when the vulnerability is not a Microsoft-authored bug but still impacts Edge users. In security terms, Edge is a consumer of Chromium risk and Chromium remediation alike.Edge is not separate from Chromium risk
That is why Microsoft’s tracking of CVE-2026-6298 should be read as more than cataloging. It is effectively a notice that enterprise patch teams cannot treat Edge as an independent security universe. When Google fixes a rendering flaw, organizations using Edge still need to verify whether their Microsoft channel has absorbed the upstream patch.The practical upside is that Microsoft gives admins a second view into the same vulnerability lifecycle. The same Guide can help with CVE monitoring, product filtering, and release-date inspection, which is useful when organizations standardize around Microsoft reporting pipelines. That makes the ecosystem a little easier to govern, even if the underlying browser risk remains shared.
But there is also a downside: the existence of multiple update channels can lull teams into thinking one browser family is “covered” when it is only eventually covered. That lag is dangerous when the CVE is a memory-corruption issue with exploitation potential. In a managed Windows estate, the right question is not whether the patch exists, but whether it has reached every browser SKU in use.
The enterprise patching lesson
For enterprises, browser patching is no longer a low-priority desktop hygiene task. It is a front-line security control, because browsers are now the universal client for email, SaaS, web apps, collaboration tools, and identity flows. A Skia bug in Chrome may begin in rendering, but the business impact lands in thes use to authenticate, approve, and transact.- Browsers are now critical infrastructure.
- Update cadence can be slower than vulnerability disclosure.
- Chromium-based products inherit the same attack surface.
- A memory leak can enable a larger exploit chain.
- Fleet-wide compliance matters more than isolated testing. ([chromereleases.g//chromereleases.googleblog.com/2026/04/stable-channel-update-for-desktop_15.html)
How Attackers Would Think About It
The most important clue in the public description is the phrase obtain potentially sensitive information from process memory. That implies the bug may be most valuable as an information leak rather than a sivery mechanism. In browser exploitation, leaks are used to defeat ASLR, identify object layouts, or expose data that can be chained into follow-on exploits.From leak to chain
A modern browser exploit rarely relies on one bug. More often, the attacker pairs a leak with a separate memory corruption or type-confusion issue, then uses the first bug to make the second more reliable. That is why even a non-executable flaw can be strategically important. It lowers the entropy in the attacker’s problem.The UI requirement also suggests a social-engineering component. An attacker might embed malicious content in a spoofed site, an ad frame, a drive-by landing page, or a phish that encourages the victim to open an HTML page. The exploit surface is therefore partly technical and partly behavioral, whist as important as patching.
It is also notable that Google did not disclose broad technical details immediately. That restraint is normal in browser security, but it means defenders should not interpret the lack of public exploit instructions as evidence of low risk. The browser ecosystem has a long history of weaponizing bugs quickly ozle is visible.
Why memory disclosure matters in 2026
Browser hardening has improved, but exploitation economics still favor attackers who can turn a leak into a predictable primitive. When the browser is the front door to cloud identities and enterprise data, the value of memory contents is amplified. A process-memory leak may reveal tokens, secrets, or internal state that should never have been visible to the page layer.This is why Critical in browser advisories deserves close attention even when the headline says “information disclosure.” Security teams should think beyond the immediate impact category and consider what a leak unlocks in the rest of the chain. In a browser context, what it enables is often more important than what it does alone.
The Broader Chromium Pattern
CVE-2026-6298 is not happening in isolation. Google’s same April 15 stable update bundled a long list of security fixes across different components, and recent Chrome release cycles have repeatedly featured memory-safety issues in Skia and other engine layers. That pattern shows the browser vendor is still fighting a wide attack surface, even with modern mitigation work.Skia keeps resurfacing
Skia appeared in earlier 2026 Chrome security notes as well, including other buffer and bounds issues in the same family. That does not necessarily mean a single underlying code defect persists;cts that a complex graphics engine offers many edge cases where untrusted input meets high-performance C++ code. The lesson is structural: performance-critical rendering code is hard to secure completely.The Chrome team’s repeated reliance on memory-safety mitigation tools also tells its own story. Google notes that many bugs are found using sanitizers, fuzzers, and related tooling, which means a significant portion of the security surface is being caught before it becomes public or weaponized. That is good news, but it is also evidence of how much work remains.
The browser security model is now a constant tug-of-war between exploit chains and memory safety engineering. Each new CVE teaches the same uncomfortable lesson: even if sandboxing prevents direct system compromise, attackers can still use renderer bugs, graphics bugs, and information leaks as stepping stones. CVE-2026-6298 fits that exact pattern.
What this says about the modern browser stack
The browser is no longer just a document viewer. It is a distributed runtime, a graphics engine, a media processor, a networking client, and a security boundary all at once. an unavoidable tension: the more capability the browser absorbs, the more code paths an attacker can target.- Rendering code remains a high-value target.
- Shared libraries amplify the impact of a single bug.
- Sandboxing helps, but leaks still matter.
- Fuzzing finds bugs, but it cannot eliminate them all.
- Patch velocitsecurity architecture.
Consumer Impact
For ordinary users, the immediate guidance is simple: make sure Chrome has updated past 147.0.7727.101/102 and restart the browser if needed. Because the attack is triggered by a crafted HTML page, the practical risk is highest when users browse untrusted sites, click suspicious links, or load content from compromised ad ecosystems. A browser update is the decisive control here.What users should notice
The troubling part is that users may not notice anything at all. Memory-disclosure bugs can be silent, especially if the page simply appears to load normally while leaking process memory behind the scenes. That makes patching more important than behavior-based detection for most consumer scenarios.Users who rely on Chromium-based browsers beyond Chrome itself should be especially careful. Many third-party browsers pick up the same engine lineage, which means the vulnerability class is not limited to Google Chrome in a practical sense. The broader Chromium ecosystem inherits the same risk profile even if the branding differs.
For consumers, the best advice is boring but effective. Update, restart, and avoid interacting with suspicious HTML pages or downloads. In browser security, boring is good.
Strengths and Opportunities
The good news is that the response chain looks healthy: Google patched quickly, Microsoft mirrored the issue for visibility, and the version guidance is clear enough for admins to act. That makes CVE-2026-6298 a case study in how the Chromium ecosystem is supposed to work when the process is functioning properly. It is not a comforting story, but it is a workable one.- Google fixed the issue in a stable-channel release.
- Microsoft surfaced the vulnerability for downstream enterprise tracking.
- The version floor is explicit and easy to verify.
- The bug class is known, so defenses can be targeted.
- The issue reinforces better update discipline across fleets.
- Security teams can use the CVE to audit browser-version drift.
- The patch cadence demonstrates good upstream/downstream coordination.
Risks and Concerns
The concern is not the patch itself; it is the delay between disclosure and universal deployment. Browser updates still have to traverse enterprise rings, offline endpoints, managed policies, and user restarts, and that creates a window where an attacker may have more freedom than defenders would like. In the browser world, a few days can be meaningful.- User interaction is still required, which invites phishing-style delivery.
- Information disclosure can enable chained exploitation.
- Shared Chromium code means many products may be affected.
- Enterprise update lag can extend exposure.
- Users may not realize a restart is still needed.
- Security teams may underestimate a “leak” compared with code execution.
- Patch visibility does not guarantee patch adoption.
Looking Ahead
What happens next is less about the bug itself and more about how quickly organizations translate the advisory into endpoint compliance. If Google and Microsoft continue to keep their Chromium advisories tightly aligned, defenders will have a clearer view of risk across Chrome and Edge. If not, the lag between upstream patching and downstream validation will remain a persistent blind spot.The broader trend is unmistakable: browser security in 2026 is being driven by memory-safety remediation, update speed, and the ability to detect whether a fix has truly landed. The companies that win here are not the ones with the fewest CVEs on paper, but the ones that shrink the time between patch release and fleet-wide protection. That is where real resilience lives.
Watch these items closely:
- Chrome fleet versions reaching 147.0.7727.101/102 or later.
- Edge release notes confirming ingestion of the Chromium fix.
- Any sign of exploit chaining involving Skia or related renderer bugs.
- Enterprise policy settings that delay browser updates.
- Follow-on advisories that clarify the bug’s exploitability.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
Last edited: