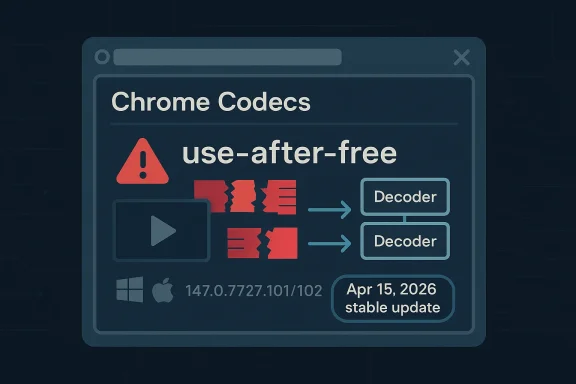
Chromium’s latest security disclosure is a sharp reminder that browser code paths still sit at the center of modern attack surface. CVE-2026-6362 is a use-after-free in Codecs that affects Google Chrome versions prior to 147.0.7727.101, and Google says a remote attacker could potentially trigger out-of-bounds memory access using a crafted video file. The flaw is rated High by Chromium, and Microsoft’s Security Update Guide has already surfaced the same CVE for defenders who track Chromium-origin vulnerabilities downstream. leblog.com]
The significance of this bug is bigger than the terse description suggests. Codecs is not a niche internal subsystem; it is the logic that helps browsers parse, decode, and render media content, which means it frequently processes complex, attacker-controlled input. In browser security, that combination is dangerous because media parsing has historically produced memory corruption, sandbox escape opportunities, and content-driven exploitation chains that begin with something as ordinary as a video file.
Google’s Chrome Releases page shows CVE-2026-6362 landed in the April 15, 2026 stable update cycle, alongside a long list of other security fixes. The release notes state that Chrome 147.0.7727.101/102 for Windows and Mac, and 147.0.7727.101 for Linux, rolled out over the coming days and weeks, with the CVE listed as a High issue in Codecs. That matters because the fix is not just a theoretical upstream patch; it is the concrete version boundary administrators can use to determine whether their fleet has already crossed the safe line.
There is also a broader pattern here that enterprise admins will recognize immediately. Google and Microsoft often publish overlapping records for Chromium CVEs because Microsoft Edge inherits Chromium fixes downstream, and the Microsoft Security Update Guide uses those records to tell customers when the browser family has absorbed upstream patches. Microsoft’s public guidance on the Update Guide and its Chromium-CVE support explains that this is part of a formal ecosystem for tracking industry-assigned vulnerabilities, not an odd duplication or a separate flaw invented by Microsoft.
The timing is notable too. April 2026 has already been a dense month for browser patching, with Chrome 147 moving through stable release channels and multiple security fixes arriving close together. That creates a familiar operational problem: organizations often treat browser updates as routine, but the concentration of memory-safety bugs means “routine” can quietly become urgent if patch verification is delayed by change control or update deferral.
Because the trigger is a crafted video file, the attack surface extends well beyond active browsing. A malicious file can arrive through web pages, embedded players, preview panes, messaging apps, hosted collaboration tools, or any workflow that hands browser-like media handling to Chromium-based components. That is one reason media bugs deserve disproportionate attention: sy to distribute, and user interaction often looks completely ordinary.
That distinction matters for triage. Security teams often prioritize CVSS numbers too literally, but browser CVEs are better judged by a mix of exploitability, ubiquity, and whether the vulnerable component touches routinely exposed input. A media parser that takes untrusted content from many sources can be more operationally urgent than a higher-scored flaw in a less reachable area of the product. Severity labels are useful; attack reality is better.
The Codecs area is especially sensitive because modern browsers do far more than simply “display” media. They negotiate container formats, decode streams, coordinate with GPU or rendering subsystems, and manage object lifetimes across asynchronous execution boundaries. That means a single lifetime bug can become a read-write primitive, a renderer crash, or a potential sandbox escape depending on what the freed object is, when the memory is reused, and how the attack is staged.
Historically, Google has been explicit that many Chrome security bugs are found by tools such as AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL. The company repeats that note in its release posts because it reflects a mature defense pipeline: browser bugs are no longer only discovered through live exploitation; many are surfaced by large-scale automated testing before they become public incidents. CVE-2026-6362 fits that modern pattern of fast identification, fix, and staged rollout.
Microsoft’s involvement is also part of the modern browser-security story. Microsoft does not create the Chromium bug, but it tracks upstream Chrome-assigned CVEs in its Security Update Guide so customers can determine whether Edge has incorporated the relevant fix. That ecosystem exists because Chromium is the shared engine layer for Chrome and Edge, and vulnerability management in 2026 is as much about synchronizing upstream and downstream release trains as it is about understanding the bug itself.
The broader lesson is that browser patching is not a one-and-done event. A product can move from “new stable release” to “secured stable release” within days, and those in-between windows are when many organizations remain exposed because update validation lags behind vendor release cadence. In a browser ecosystem with multiple channels, staggered rollouts, and platform-specific builds, the safest assumption is that release notes are a moving target until the deployment telemetry says otherwise.
In practice, browser vendors have spent years reducing exploitability in media code with sandboxing, pointer hardening, and aggressive fuzzing. But those mitigations do not eliminate the underlying issue: any parser that manages object lifetimes across complex state transitions remains vulnerable to the sort of “free, then touch” mistake that use-after-free bugs embody. CVE-2026-6362 is therefore less an isolated anomaly than a reminder that the problem domain persists.
The language in the release note is also telling. Google notes that bug details may be kept restricted until a majority of users are updated with a fix, a standard defensive practice intended to limit exploitation during the most dangerous window. That tells defenders two things at once: first, the issue was considered worthy of temporary detail suppression; second, the vendor expects the public disclosure window itself to be a risk-management tool.
A second versioning issue is roll-forward timing. Google says the update will roll out over days or weeks, so the fact that a patch exists does not mean every device has it yet. In enterprise environments, this is often where security posture becomes uneven: managed endpoints update quickly, while laptops off-network, kiosks, VDI images, and long-life app stacks lag behind. The patch may be public, but exposure can linger.
That cadence also speaks to a modern reality: browser vendors are not just shipping features, they are shipping a constant stream of memory-safety corrections under compressed timelines. From an operational standpoint, the patch train is now part of the threat model. If your environment cannot absorb browser updates quickly, then media-file parsing bugs become a predictable source of residual risk.
This also clarifies a common misconception. A Chromium CVE appearing in Microsoft’s guide does not necessarily mean Microsoft independently found or changed the bug, and it does not automatically imply a separate Edge-only exploit path. Instead, it is evidence of the shared-source model in action: one vulnerability, multiple distribution channels, and a downstream confirmation step for Microsoft customers.
That means administrators need to think in layers. The browser may be fixed, but WebView-based applications, bundled components, or slower-moving enterprise images can remain on older Chromium-derived builds. In other words, a browser CVE can be “fixed” in one product and still be operationally relevant in a dozen others that share the same engine lineage. That is downstream security in 2026.
For the current bug, that means Microsoft’s entry is best read as a verification aid. It tells the reader to check whether their Edge build includes the Chromium patch and whether any derivative product depends on the vulnerable codebase. That is a small distinction in wording, but a large one in practice because it shifts the focus from the CVE label to the actual deployed build.
A use-after-free in codecs can be attractive to attackers because media parsers often perform complex object allocation and state transitions. If an attacker can influence when an object is freed and what memory is reclaimed in its place, they may be able to shape the bug into a controlled read, crash, or partial overwrite. That does not guarantee reliable exploitation, but it is exactly the kind of vulnerability class defenders should treat as dangerous until proven otherwise.
This makes security awareness campaigns less important than strong automatic patching and content filtering. Users can be trained to avoid suspicious attachments, but the real defense is eliminating the vulnerable build before malicious media reaches the endpoint. In browser security, remediation speed tends to matter more than perfect human judgment.
In the browser world, the question is rarely whether a bug is bad in isolation. The more important question is whether the bug becomes useful when combined with another flaw in the same or adjacent procethinking is why even a single High-severity media bug should be treated as part of the broader security posture, not as an isolated defect to be deferred.
Google’s own release notes show that April’s Chrome stable update also fixed other memory-corruption problems across the browser stack, including issues in ANGLE, Proxy, Cast, V8, and Skia. That does not diminish CVE-2026-6362; instead, it reinforces the point that browser security is a systems problem. The more subsystems a browser integrates, the more memory-safety bugs accumulate along the seams.
The practical lesson for vendors is clear. Continued investment in memory-safe languages, hardened abstractions, and aggressive sandboxing remains necessary even when release engineering is excellent. For defenders, the lesson is equally clear: browser bugs are not “rare exceptions” anymore; they are a steady operational input that must be managed like patch debt.
That is why stable-channel security notes matter so much: they are the public record of the ongoing cleanup process. Each CVE is less a surprise than a marker of how much work remains in a codebase that must parse the world’s con-2026-6362 belongs squarely in that ongoing cleanup narrative.
For enterprise IT, the problem is more layered. Admins need to verify update deployment, account for offline devices, and make sure browser policy does not pin endpoints to older channels or delay patches beyond a defensible winandard browser, Microsoft’s Security Update Guide should be used alongside Chrome release notes to ensure the downstream build line has the fix as well.
Administrators should therefore separate “feature stability” from “security update velocity.” The former is often negotiable; the latter usually is not. If a patch fixes a High-severity parser bug, then allowing update lag for convenience is a trade-off that deserves explicit approval, not an implicit default.
In other words, CVE-2026-6362 is a browser vulnerability and a supply-chain tracking event at the same time. The first tells you what the bug is; the second tells you how many different software teams may need to react to it. That dual meaning is exactly why Chromium CVEs ripple across the industry so quickly.
Another strength is that the bug is tied to a specific component and trigger class, which helps security teams write practical detection and awareness guidance. Because the issue involves crafted video content, organizations can tailor controls around file handling, web ingestion, and endpoint update compliance. The clearer the trigger, the easier it is to harden the surrounding workflow.
A second concern is patch drift. Chrome and Edge may not update at the same speed across all device classes, and other Chromium-based products may lag even farther behind. That leaves a long tail of exposure after the main browsers have already moved to a fixed build.
Over the medium term, CVE-2026-6362 will probably fade into the larger April 2026 patch narrative, but its significance will remain as part of the evidence that media parsing is still a prime memory-safety battleground. The market lesson is familiar: browsers keep getting safer, but they also keep absorbing enormous amounts of untrusted complexity, and that complexity continues to generate exploitable mistakes. The vendors are improving; the threat surface is improving too, just in the opposite direction.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The significance of this bug is bigger than the terse description suggests. Codecs is not a niche internal subsystem; it is the logic that helps browsers parse, decode, and render media content, which means it frequently processes complex, attacker-controlled input. In browser security, that combination is dangerous because media parsing has historically produced memory corruption, sandbox escape opportunities, and content-driven exploitation chains that begin with something as ordinary as a video file.Google’s Chrome Releases page shows CVE-2026-6362 landed in the April 15, 2026 stable update cycle, alongside a long list of other security fixes. The release notes state that Chrome 147.0.7727.101/102 for Windows and Mac, and 147.0.7727.101 for Linux, rolled out over the coming days and weeks, with the CVE listed as a High issue in Codecs. That matters because the fix is not just a theoretical upstream patch; it is the concrete version boundary administrators can use to determine whether their fleet has already crossed the safe line.
There is also a broader pattern here that enterprise admins will recognize immediately. Google and Microsoft often publish overlapping records for Chromium CVEs because Microsoft Edge inherits Chromium fixes downstream, and the Microsoft Security Update Guide uses those records to tell customers when the browser family has absorbed upstream patches. Microsoft’s public guidance on the Update Guide and its Chromium-CVE support explains that this is part of a formal ecosystem for tracking industry-assigned vulnerabilities, not an odd duplication or a separate flaw invented by Microsoft.
The timing is notable too. April 2026 has already been a dense month for browser patching, with Chrome 147 moving through stable release channels and multiple security fixes arriving close together. That creates a familiar operational problem: organizations often treat browser updates as routine, but the concentration of memory-safety bugs means “routine” can quietly become urgent if patch verification is delayed by change control or update deferral.
What the vulnerability means
At a technical level, use-after-free means code continues to access memory after it has been released, which can lead to crashes, data corruption, or exploitable control-flow manipulation depending on the circumstances. In the case of CVE-2026-6362, Google’s wording points to possible out-of-bounds memory access via crafted media input, which is exactly the kind of primitive attackers use to move from a parser bug to a more meaningful exploit chain. Not every use-after-free is immediately weaponizable, but in browser media code the risk profile is always uncomfortable.Because the trigger is a crafted video file, the attack surface extends well beyond active browsing. A malicious file can arrive through web pages, embedded players, preview panes, messaging apps, hosted collaboration tools, or any workflow that hands browser-like media handling to Chromium-based components. That is one reason media bugs deserve disproportionate attention: sy to distribute, and user interaction often looks completely ordinary.
Why the CVSS picture looks softer than the headline
The NVD record is still being enriched, but the advisory data associated through CISA-ADP gives CVE-2026-6362 a CVSS 3.1 base score of 6.3 with AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:L. That vector tells a useful story: exploitation is network-reachable, does not require privileges, but does require user interaction, and its estimated impact is bounded rather than catastrophic. In plain English, that makes it a serious browser flaw without automatically implying “internet-wide worm” conditions.That distinction matters for triage. Security teams often prioritize CVSS numbers too literally, but browser CVEs are better judged by a mix of exploitability, ubiquity, and whether the vulnerable component touches routinely exposed input. A media parser that takes untrusted content from many sources can be more operationally urgent than a higher-scored flaw in a less reachable area of the product. Severity labels are useful; attack reality is better.
Background
Chromium’s architecture makes it both powerful and fragile. On one hand, the project benefits from an enormous engineering ecosystem, broad fuzzing coverage, and rapid patch propagation across Chrome, Edge, and other downstream browsers. On the other hand, the same complexity that enables rich web and media support also creates deep parsing code paths where memory-safety bugs can hide for years before fuzzers, researchers, or red teams surface them.The Codecs area is especially sensitive because modern browsers do far more than simply “display” media. They negotiate container formats, decode streams, coordinate with GPU or rendering subsystems, and manage object lifetimes across asynchronous execution boundaries. That means a single lifetime bug can become a read-write primitive, a renderer crash, or a potential sandbox escape depending on what the freed object is, when the memory is reused, and how the attack is staged.
Historically, Google has been explicit that many Chrome security bugs are found by tools such as AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL. The company repeats that note in its release posts because it reflects a mature defense pipeline: browser bugs are no longer only discovered through live exploitation; many are surfaced by large-scale automated testing before they become public incidents. CVE-2026-6362 fits that modern pattern of fast identification, fix, and staged rollout.
Microsoft’s involvement is also part of the modern browser-security story. Microsoft does not create the Chromium bug, but it tracks upstream Chrome-assigned CVEs in its Security Update Guide so customers can determine whether Edge has incorporated the relevant fix. That ecosystem exists because Chromium is the shared engine layer for Chrome and Edge, and vulnerability management in 2026 is as much about synchronizing upstream and downstream release trains as it is about understanding the bug itself.
How this fits the April 2026 patch cycle
Chrome 147’s stable rollout had already introduced the familiar release rhythm: early stable builds, then broad distribution, then a follow-up stable update with security fixes. CVE-2026-6362 appeared in the later April 15 fix set, which means defenders who only glanced at the first 147 release may have missed the additional security delta that landed a week later. That is exactly why patch managers should track specific build numbers, not just major version families.The broader lesson is that browser patching is not a one-and-done event. A product can move from “new stable release” to “secured stable release” within days, and those in-between windows are when many organizations remain exposed because update validation lags behind vendor release cadence. In a browser ecosystem with multiple channels, staggered rollouts, and platform-specific builds, the safest assumption is that release notes are a moving target until the deployment telemetry says otherwise.
Why video parsing is a recurring target
Media handling has a long history of abuse because it sits at the intersection of complex parsing, large binary data, and user trust. A victim doesn’t need to open a “suspicious executable” to be exposed; they can simply preview content in a browser, open a message, or visit a site with embedded media. That makes codec bugs especially attractive to threat actors who prefer low-friction delivery with plausible deniability.In practice, browser vendors have spent years reducing exploitability in media code with sandboxing, pointer hardening, and aggressive fuzzing. But those mitigations do not eliminate the underlying issue: any parser that manages object lifetimes across complex state transitions remains vulnerable to the sort of “free, then touch” mistake that use-after-free bugs embody. CVE-2026-6362 is therefore less an isolated anomaly than a reminder that the problem domain persists.
Google’s Fix and Release Channel Response
Google’s stable-channel post is the primary source of truth for the fix. It identifies 147.0.7727.101/102 as the version line that contains the remediation and marks CVE-2026-6362 as a High severity issue in Codecs. The practical implication is straightforward: systems at or above that build should no longer be exposed to this specific Chromium bug, assuming they are on an updated branch and have not been held back by enterprise policies or offline maintenance cycles.The language in the release note is also telling. Google notes that bug details may be kept restricted until a majority of users are updated with a fix, a standard defensive practice intended to limit exploitation during the most dangerous window. That tells defenders two things at once: first, the issue was considered worthy of temporary detail suppression; second, the vendor expects the public disclosure window itself to be a risk-management tool.
Versioning matters more than headlines
Administrators should not stop at “Chrome 147.” The release note makes clear that Windows/Mac and Linux have distinct build identifiers, and Chrome stable updates can show slightly different numbering even when they sharge. That means inventory tools should confirm the exact browser build rather than assuming parity across operating systems.A second versioning issue is roll-forward timing. Google says the update will roll out over days or weeks, so the fact that a patch exists does not mean every device has it yet. In enterprise environments, this is often where security posture becomes uneven: managed endpoints update quickly, while laptops off-network, kiosks, VDI images, and long-life app stacks lag behind. The patch may be public, but exposure can linger.
What the update cadence suggests
The presence of 31 security fixes in the same stable update underscores how browsers now ship as continuously hardened platforms rather than static applications. For security teams, that means a single browser patch may close multiple unrelated defects, and delaying one update to “reduce change” can inadvertently preserve several distinct attack paths. CVE-2026-6362 is one patch among many, but it belongs in the same urgent bucket as the rest of the April fix set.That cadence also speaks to a modern reality: browser vendors are not just shipping features, they are shipping a constant stream of memory-safety corrections under compressed timelines. From an operational standpoint, the patch train is now part of the threat model. If your environment cannot absorb browser updates quickly, then media-file parsing bugs become a predictable source of residual risk.
Microsoft Edge and the Downstream Security Impact
Microsoft’s Security Update Guide entry matters because Edge inherits Chromium’s core engine. When Google fixes a browser vulnerability upstream, Microsoft uses its downw whether Edge has absorbed the same fix, which is crucial for organizations that standardize on Edge even when Chrome is not their primary browser. The Microsoft record for CVE-2026-6362 is therefore not redundant; it is an operational signal.This also clarifies a common misconception. A Chromium CVE appearing in Microsoft’s guide does not necessarily mean Microsoft independently found or changed the bug, and it does not automatically imply a separate Edge-only exploit path. Instead, it is evidence of the shared-source model in action: one vulnerability, multiple distribution channels, and a downstream confirmation step for Microsoft customers.
Why enterprises care more than consumers often do
For consumers, the issue is usually simple: update the browser and move on. For enterprises, the question is whether every managed instance has actually reached the safe build, whether update rings are aligned, and whether embedded Chromium components in other products are also affected. Because Chromium is reused widely, the edge case is no longer just the browser window itself.That means administrators need to think in layers. The browser may be fixed, but WebView-based applications, bundled components, or slower-moving enterprise images can remain on older Chromium-derived builds. In other words, a browser CVE can be “fixed” in one product and still be operationally relevant in a dozen others that share the same engine lineage. That is downstream security in 2026.
What Microsoft’s notation really provides
Microsoft’s Security Update Guide is designed to be a unified source of truth for Microsoft customers, and the company has explicitly said it supports industry-assigned CVEs through that channel. That framework gives defenders a way to map upstream Chrome fixes to their own Microsoft-managed fleet, which is especially useful when patch windows are staggered or when policy blocks automatic update adoption.For the current bug, that means Microsoft’s entry is best read as a verification aid. It tells the reader to check whether their Edge build includes the Chromium patch and whether any derivative product depends on the vulnerable codebase. That is a small distinction in wording, but a large one in practice because it shifts the focus from the CVE label to the actual deployed build.
Exploitation Potential and Attack Surface
The obvious attack surface is malicious video delivery, but that is only the starting point. Modern attack chains often rely on content that is embedded, previewed, cached, re-transcoded, or served through a seemingly safe application layer that ultimately reaches the browser’s media decoder. The more places Chromium handles media-like content, the more opportunities exist for the bug to be exercised.A use-after-free in codecs can be attractive to attackers because media parsers often perform complex object allocation and state transitions. If an attacker can influence when an object is freed and what memory is reclaimed in its place, they may be able to shape the bug into a controlled read, crash, or partial overwrite. That does not guarantee reliable exploitation, but it is exactly the kind of vulnerability class defenders should treat as dangerous until proven otherwise.
User interaction still matters
The CVSS vector indicates UI:R, which means user interaction is required. That is good news in the abstract, but it should not encourage complacency. Browser and media exploits frequently rely on one click, one preview, or one automatic media load in a workflow the user perceives as low risk. Once a crafted file is in circulation, the difference between “needs interaction” and “easy to trigger” can be very small.This makes security awareness campaigns less important than strong automatic patching and content filtering. Users can be trained to avoid suspicious attachments, but the real defense is eliminating the vulnerable build before malicious media reaches the endpoint. In browser security, remediation speed tends to matter more than perfect human judgment.
Why out-of-bounds access is such a red flag
Google’s description explicitly mentions potential out-of-bounds memory access. That wording raises the stakes because out-of-bounds reads and writes can reveal memory contents, destabilize the process, or help attackers defeat exploit mitigations by learning object layouts. Even when the initial condition is “only” a crash, memory disclosure can often be the bridge to more serious compromise.In the browser world, the question is rarely whether a bug is bad in isolation. The more important question is whether the bug becomes useful when combined with another flaw in the same or adjacent procethinking is why even a single High-severity media bug should be treated as part of the broader security posture, not as an isolated defect to be deferred.
Memory-Safety Trends in Chromium
CVE-2026-6362 is part of a long line of Chromium memory-safety issues, many of them use-after-free bugs across different components. The pattern is not accidental: browsers are among the most heavily fuzzed applications in the world, but they are also among the most complicated, and complexity still beats diligence when lifetime management and asynchronous execution intersect.Google’s own release notes show that April’s Chrome stable update also fixed other memory-corruption problems across the browser stack, including issues in ANGLE, Proxy, Cast, V8, and Skia. That does not diminish CVE-2026-6362; instead, it reinforces the point that browser security is a systems problem. The more subsystems a browser integrates, the more memory-safety bugs accumulate along the seams.
The codec class remains especially stubborn
Codec bugs are stubborn because they combine format complexity with performance pressure. Developers want fast, low-latency parsing for popular formats, but every shortcut or state transition can introduce edge cases that fuzzing later uncovers. This is why media parsers appear so often in browser advisories: they are high-value, high-complexity, and constantly exercised by real-world traffic.The practical lesson for vendors is clear. Continued investment in memory-safe languages, hardened abstractions, and aggressive sandboxing remains necessary even when release engineering is excellent. For defenders, the lesson is equally clear: browser bugs are not “rare exceptions” anymore; they are a steady operational input that must be managed like patch debt.
Why fuzzing helps but cannot finish the job
Google’s mention of fuzzing and sanitizers is a reminder that modern browser teams are finding bugs before attackers do, but also that the bug class is still abundant enough to keep the pipeline busy. Sanitizers improve detection, yet they do not eliminate the fundamental risk that a complex parser can still mishandle object ownership in real code. The security win is real, but it is not absolute.That is why stable-channel security notes matter so much: they are the public record of the ongoing cleanup process. Each CVE is less a surprise than a marker of how much work remains in a codebase that must parse the world’s con-2026-6362 belongs squarely in that ongoing cleanup narrative.
Enterprise and Consumer Implications
For consumers, the action is simple: ensure Chrome is updated past 147.0.7727.101 and let auto-update do its job. Most users will never know why the browser relaunched, only that it did. That quiet remediation model is one of Chrome’s biggest strengths, because it reduces the chance that a user will knowingly sit on a vulnerable build for long.For enterprise IT, the problem is more layered. Admins need to verify update deployment, account for offline devices, and make sure browser policy does not pin endpoints to older channels or delay patches beyond a defensible winandard browser, Microsoft’s Security Update Guide should be used alongside Chrome release notes to ensure the downstream build line has the fix as well.
The role of managed policies
Managed browsers can be both a blessing and a trap. Policies make standardized deployment easier, but they can also delay automatic updates if the environment is configured too conservatively or if maintenance windows are too narrow. That creates a paradox: the very controls meant to improve stability can lengthen exposure to a known memory-safety flaw.Administrators should therefore separate “feature stability” from “security update velocity.” The former is often negotiable; the latter usually is not. If a patch fixes a High-severity parser bug, then allowing update lag for convenience is a trade-off that deserves explicit approval, not an implicit default.
Third-party and embedded Chromium consumers
One of the most underappreciated aspects of Chromium CVEs is how many products depend on the engine without branding themselves as browsers. Applications that embed Chromium, use WebView, or ship web-rendering functions can inherit the same exposure path. That means vulnerability management cannot stop at Chrome and Edge inventory; it must extend to every product that quietly bundles the same stack.In other words, CVE-2026-6362 is a browser vulnerability and a supply-chain tracking event at the same time. The first tells you what the bug is; the second tells you how many different software teams may need to react to it. That dual meaning is exactly why Chromium CVEs ripple across the industry so quickly.
Strengths and Opportunities
The good news is that Google and Microsoft’s combined disclosure model gives defenders a clear remediation path. The Chrome release note identifies the fixed build, and Microsoft’s Security Update Guide helps downstream customers verify whether the same upstream patch has reached Edge. That makes this a relatively tractable issue compared with vulnerabilities that lack a clean version boundary or public tracking.Another strength is that the bug is tied to a specific component and trigger class, which helps security teams write practical detection and awareness guidance. Because the issue involves crafted video content, organizations can tailor controls around file handling, web ingestion, and endpoint update compliance. The clearer the trigger, the easier it is to harden the surrounding workflow.
- Clear fixed version: Chrome 147.0.7727.101/102 provides a concrete remediation target.
- Downstream visibility: Microsoft’s tracking helps Edge administrators verify ingestion of the fix.
- Defined attack class: The bug is tied to crafted video files, making threat modeling more focused.
- Established patch channel: Auto-update and managed deployment can close the gap quickly when configured well.
- Mature vendor response: Google’s security tooling and staged disclosure process reduce long-term exposure.
- Useful operational signal: The CVSS vector helps teams judge urgency without overreacting to a single number.
- Broader visibility into Chromium reuse: The advisory reminds IT teams to inventory embedded Chromium consumers.
Risks and Concerns
The biggest concern is that the word “High” can still be underestimated in practice when the vulnerability requires user interaction. Many organizations assume UI-based flaws are inherently slow to exploit, but crafted media files are among the easiest payloads to distribute through normal user workflows. The attack may need a click, but that is not the same as needing a skilled insider.A second concern is patch drift. Chrome and Edge may not update at the same speed across all device classes, and other Chromium-based products may lag even farther behind. That leaves a long tail of exposure after the main browsers have already moved to a fixed build.
- User interaction reduces, but does not eliminate, exploitability.
- Delayed rollout windows can keep endpoints vulnerable after the fix is public.
- Embedded Chromium consumers may remain exposed even when browsers are patched.
- Policy-based update deferral can turn a short-lived bug into a lasting enterprise risk.
- Media handling is ubiquitous, so the trigger path is broader than many teams expect.
- Memory-safety flaws often compose with other bugs, raising the real-world impact.
- Version confusion is easy if teams track only major versions and not build numbers.
Looking Ahead
The immediate next step is simple: verify that Chrome is at or above 147.0.7727.101 and that Edge has ingested the corresponding Chromium fix. After that, the more important job is continuous inventory hygiene, because the same engine may be hiding in other software categories that do not advertise themselves as browsers. Security teams that only check the visible browser window are likely to miss embedded exposure elsewhere.Over the medium term, CVE-2026-6362 will probably fade into the larger April 2026 patch narrative, but its significance will remain as part of the evidence that media parsing is still a prime memory-safety battleground. The market lesson is familiar: browsers keep getting safer, but they also keep absorbing enormous amounts of untrusted complexity, and that complexity continues to generate exploitable mistakes. The vendors are improving; the threat surface is improving too, just in the opposite direction.
- Confirm Chrome versioning across desktop fleets and update any lagging endpoints.
- Check Edge build status in Microsoft’s Security Update Guide.
- Audit embedded Chromium usage in line-of-business apps and WebView consumers.
- Review file-ingestion controls for video, preview, and media-processing workflows.
- Watch for follow-on advisories that may reference related media or parser bugs in the same release cycle.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center