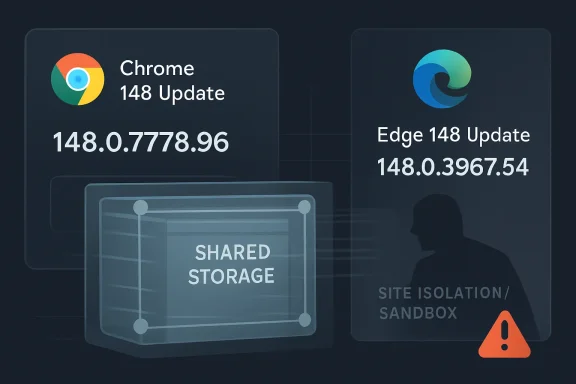
Google and Microsoft addressed CVE-2026-7954 on May 6–7, 2026, by moving Chrome desktop to 148.0.7778.96/97 and Edge Stable to 148.0.3967.54, fixing a Medium-severity Chromium Shared Storage race that could leak cross-origin data after renderer compromise via crafted HTML. That dry sentence is the whole incident in miniature: not a panic-grade remote-code-execution headline, but a reminder that browser privacy boundaries now depend on increasingly intricate ad-tech and storage machinery. The uncomfortable part is that this bug sits exactly where the modern web is trying to reinvent tracking, measurement, and isolation at the same time. For Windows admins, the lesson is less “drop everything” than “stop treating Chromium fixes as somebody else’s browser problem.”
CVE-2026-7954 is not the kind of vulnerability that normally sets off executive war rooms. The published scoring from CISA’s ADP process puts it at a low CVSS 3.1 base score of 3.1, with high attack complexity, required user interaction, no privileges required, and limited confidentiality impact. NVD had not yet assigned its own score at the time the record appeared, but the broad outline is clear enough: this is an information disclosure flaw, not a one-click machine takeover.
That does not make it ignorable. The bug is described as a race condition in Chromium’s Shared Storage implementation, allowing an attacker who had already compromised the renderer process to leak cross-origin data using a crafted HTML page. In plain English, the attack assumes the adversary has already won one round inside the browser’s rendering engine and is then using this flaw to press further against origin separation.
That “already compromised renderer” clause is doing a lot of work. It is the reason the severity is not higher, and it is also the reason defenders should not dismiss the issue too quickly. Modern browser exploitation is often chained: one bug gets execution in a constrained place, another weakens the sandbox or privacy boundary, and a third turns the whole thing into something operationally useful.
Shared Storage itself is part of the browser’s attempt to square a circle. Advertisers, publishers, and web platforms want measurement and personalization; users and regulators want fewer third-party cookies and less cross-site tracking; browser vendors want APIs that promise controlled, privacy-preserving alternatives. When those new APIs malfunction, the failure mode is rarely as simple as “a page crashes.” It is more likely to involve data boundaries that only security engineers, web platform specialists, and ad-tech lawyers can fully diagram.
A vulnerability that requires renderer compromise does not start the fire; it helps the fire spread. That matters because exploit writers do not think in CVSS rows. They think in chains, reliability, primitives, and payoff. If an attacker can use a separate Blink, V8, graphics, media, or IPC flaw to gain a foothold in the renderer, a bug like CVE-2026-7954 may become a way to harvest information that should have remained fenced off.
The race condition angle is also telling. Races are notoriously awkward to reason about because the vulnerable behavior depends on timing, concurrency, and state transitions rather than a single obviously bad input. In a browser, where dozens of subsystems are negotiating storage, permissions, frames, workers, navigations, and site isolation, timing bugs can become especially subtle.
That subtlety is why “Medium” Chromium bugs deserve more respect than they often get. They may not be the exploit chain’s opening act, but they can be the supporting role that turns a browser bug from annoying into useful. A confidentiality leak may expose tokens, identifiers, browsing-state signals, measurement outputs, or other data that helps an attacker understand or personalize the next step.
The web security model is built around the same-origin policy, but the lived reality is a stack of exceptions, special cases, postMessage pathways, embedded content, fenced frames, storage APIs, and privacy mitigations. CVE-2026-7954 appears to live in that messy middle. It is a vulnerability in the machinery that decides what one context can learn about another.
That broader context matters because CVE-2026-7954 is easy to lose in the pile. In a patch bundle with more than 100 fixes, administrators naturally triage toward Critical and High severity items. Yet the bundle is also a map of the browser’s attack surface: rendering, remote desktop plumbing, mobile components, storage, privacy APIs, and the glue between them.
Chrome’s update cadence can make these releases feel ordinary. For consumers, the browser quietly patches itself and offers a relaunch button. For enterprise IT, that normalcy is both a blessing and a trap. The blessing is that most endpoints should receive the fix with little drama. The trap is that “automatic” is not the same as “verified,” especially across virtual desktops, kiosk systems, server-hosted browsers, golden images, offline machines, and tightly managed update rings.
The version numbers are the operational fact that matters. Chrome prior to 148.0.7778.96 is the vulnerable line identified for CVE-2026-7954, with Windows and macOS seeing 148.0.7778.96/97 in the stable release stream. Edge, because it rides Chromium but ships on Microsoft’s cadence and versioning, fixed the relevant Chromium batch in Edge Stable 148.0.3967.54 on May 7.
That one-day gap between Google’s stable release and Microsoft’s Edge note is not scandalous. It is the normal reality of a shared engine moving through multiple vendors’ build, validation, and distribution systems. But it is exactly why Windows shops need to track both Chrome and Edge as first-class patch targets instead of assuming “Chromium” is a single monolithic product.
A Windows 11 endpoint can easily have Edge as the default managed browser, Chrome installed for compatibility, WebView2 powering desktop apps, Electron-based applications embedding Chromium-derived code, and third-party browsers with their own update logic. CVE-2026-7954 is formally about Google Chrome before a specific version, but the surrounding ecosystem is bigger than the product name in the CVE entry.
Edge’s release also contained Microsoft Edge-specific fixes, which is a useful reminder that Microsoft is not merely copying Google’s bits and changing the icon. The browser has its own update channel, enterprise policy surface, account integrations, sync behavior, security features, and platform hooks. Chromium vulnerabilities may arrive through the shared engine, while Edge-specific issues travel alongside them.
The admin problem is that users experience all of this as “the browser,” while defenders have to inventory the pieces. A user may open a phishing link in Chrome, authenticate through Edge, launch an app that embeds WebView2, and preview content inside Teams or Outlook flows that rely on web components. From the attacker’s point of view, any renderable web surface is interesting.
This is why browser patch management has quietly become endpoint security work, not desktop convenience work. It belongs in the same operational rhythm as Defender updates, Windows cumulative updates, Office servicing, and third-party application patching. If the browser is the primary place where untrusted code enters the enterprise, then browser version drift is not cosmetic debt. It is exposure.
That is the noble version of the story. The engineering version is harder: browsers are adding new primitives that deliberately allow limited cross-context computation while trying to prevent uncontrolled cross-origin leakage. Every new primitive has state, timing, permissions, lifecycle behavior, and edge cases. Every edge case is a place where a race condition can hide.
CVE-2026-7954 should therefore be read as part of a larger pattern. The web platform is not getting simpler as it becomes more privacy-conscious. It is getting more elaborate. Instead of a blunt third-party cookie jar, browsers now ship an expanding suite of privacy-preserving APIs, anti-fingerprinting defenses, storage partitioning schemes, attribution tools, fenced contexts, and isolated execution models.
Security teams should not hear that as an argument against privacy engineering. The old tracking model was indefensible from a user trust perspective. But the replacement model asks browser vendors to become not just software companies, but governors of extremely delicate information flows. When those flows are controlled by complex asynchronous browser internals, race bugs become governance failures as much as code defects.
There is a broader irony here. The Privacy Sandbox era was supposed to reduce cross-origin leakage by design. A Shared Storage race that can leak cross-origin data after renderer compromise does not invalidate that project, but it does reveal the cost of moving privacy guarantees deeper into browser implementation details. The promise becomes only as strong as the synchronization logic enforcing it.
But CVSS is a measurement framework, not a patching strategy. It is especially awkward for browser-chain vulnerabilities, where individual bugs often look modest in isolation and dangerous in combination. A renderer-only leak may be low severity until paired with an actively exploited renderer bug, a sandbox escape, a phishing campaign, or a target with valuable authenticated web sessions.
The exploitability language also deserves careful reading. There is no public indication in the available advisory language that CVE-2026-7954 is being exploited in the wild. That distinction matters. This is not one of those Chrome advisories where the browser vendor explicitly says an exploit exists in the wild and everyone should assume active attack pressure.
Still, the absence of known exploitation is not a permission slip to wait indefinitely. Browser vulnerabilities age poorly after patches ship. Attackers can diff open-source code, study bug references as they become available, and look for users who lag behind automatic updates. The window between patch availability and broad fleet adoption is where “Medium” bugs become useful tools for selective exploitation.
The right response is proportionate urgency. Home users should relaunch Chrome and Edge and verify they are current. Enterprise teams should check telemetry, update rings, and any frozen channels. Security teams should prioritize systems that process untrusted web content, handle sensitive SaaS sessions, or sit in high-value user groups such as finance, engineering, legal, identity administration, and executive staff.
CPEs are the plumbing behind a lot of automated vulnerability management. If the product mapping is incomplete, too broad, too narrow, or slow to update, scanners may miss affected assets or flag systems incorrectly. In browser land, that problem is amplified by forks, embedded runtimes, channel differences, and vendor-specific version schemes.
For Chrome itself, the mapping is straightforward enough. Chrome before 148.0.7778.96 is vulnerable. But the real world is full of “Chromium-based” products that do not always map cleanly to the Chrome CPE. Edge gets its own MSRC treatment and own version number. Other browsers and embedded frameworks may inherit the vulnerable code on their own schedules, or may not expose the same feature set in the same way.
This is where security operations often becomes anthropology. You need to know not only what software is installed, but how it is built, who updates it, what channel it tracks, and whether the vulnerable component is reachable. A CPE entry can start the conversation, but it cannot finish it.
The practical implication is that administrators should not wait for scanner certainty before handling obvious browser updates. If Chrome is present, update Chrome. If Edge is present, update Edge. If Chromium-derived applications are mission-critical or exposed to untrusted content, track vendor advisories for those applications rather than assuming the Chrome CVE tells the whole story.
CVE-2026-7954 fits that model. On its own, it is a data leak after renderer compromise. In a chain, it could help an attacker learn something they should not know across an origin boundary. That information might not be dramatic in the abstract, but exploitation is often about converting small primitives into leverage.
A cross-origin leak can matter because web applications increasingly carry the business. Identity providers, internal dashboards, HR portals, source-code systems, cloud consoles, finance tools, and collaboration suites all live behind browser tabs. The browser’s origin model is the invisible line keeping one authenticated context from bleeding into another.
Attackers understand this better than users do. They do not need to “own the machine” in the classic malware sense if they can manipulate or observe enough of a high-value browser session. The industry’s obsession with endpoint compromise sometimes misses the fact that a great deal of enterprise authority now resides in bearer tokens, web sessions, OAuth flows, and browser-mediated trust.
That is why confidentiality bugs in browsers deserve a more nuanced reading than confidentiality bugs in many desktop applications. A small leak in the wrong browser context can disclose more than a file path or a preference. It can expose state, identity, or cross-site signals that help defeat assumptions built into web application security.
Those decisions are not irrational. Browser updates can break workflows, especially in organizations with legacy web apps, internal certificate oddities, brittle extensions, or kiosk deployments. The problem is that the threat model has changed faster than many update policies. Holding a browser back is no longer like delaying a media player patch. It is delaying the repair of the primary interpreter for hostile code.
The May 2026 Chrome 148 release makes that tradeoff vivid. A single update carried more than 100 security fixes and multiple critical vulnerabilities. Even if CVE-2026-7954 is not the headline, the release bundle as a whole argues against long deferrals. The more security fixes packed into a browser update, the more expensive each day of delay becomes.
For managed Windows fleets, the answer is not blind instant deployment everywhere. It is disciplined rings with tight timelines. A small validation group can catch breaking issues, but the production rollout should move in days, not weeks, unless a concrete compatibility blocker exists. Security exceptions should be documented as risk decisions, not hidden inside “standard change windows.”
The same logic applies to relaunch enforcement. A browser can download an update and still run vulnerable code until the process restarts. User-friendly nagging is not always enough. For high-risk populations, admins should consider policies that require relaunch after a defined grace period, particularly when Chrome or Edge releases include exploited-in-the-wild flaws or large security bundles.
That boringness is exactly why it matters. Security failures often accumulate in the gap between “the vendor patched it” and “our actual machines are running the patched build.” Browser patching looks easy from the outside because users see a relaunch button. Inside a real environment, that button competes with uptime expectations, locked-down profiles, VDI images, packaging systems, browser extensions, and users who keep sessions open for weeks.
There is also a communication challenge. Calling CVE-2026-7954 “low score” may encourage complacency. Calling it a “cross-origin data leak after renderer compromise” may cause eyes to glaze over. The defensible message is simpler: update Chromium-based browsers because the current stable releases close a large batch of security issues, including a Shared Storage bug that weakens browser data isolation under compromised-renderer conditions.
Admins should also remember that browser security posture is cumulative. Enhanced security modes, extension controls, site isolation policies, safe browsing, download protections, application control, and phishing-resistant authentication all shape the likelihood that a browser bug becomes an incident. Patching is essential, but it is one layer in a model that assumes web content cannot be trusted.
For Windows shops, Edge’s integration with the operating system cuts both ways. It gives Microsoft strong update distribution channels and policy management. It also means Edge is present almost everywhere, even where Chrome is the user-preferred browser. Treating Edge as “unused” because employees click a different icon is a familiar mistake.
The vulnerability is a race condition in Shared Storage, categorized under CWE-362, and the described impact is cross-origin data leakage via crafted HTML after renderer compromise. The published Chromium severity is Medium, while CISA’s ADP CVSS vector rates it Low at 3.1. There is no advisory language in the available record saying that this specific CVE is known to be exploited in the wild.
Those details are not trivia. They let defenders calibrate urgency without either shrugging or catastrophizing. The priority is to confirm browser versions, not to write an incident report for every machine that was a few hours behind.
Here is the concrete shape of the response:
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Medium Bug in a High-Stakes Part of the Browser
A Medium Bug in a High-Stakes Part of the Browser
CVE-2026-7954 is not the kind of vulnerability that normally sets off executive war rooms. The published scoring from CISA’s ADP process puts it at a low CVSS 3.1 base score of 3.1, with high attack complexity, required user interaction, no privileges required, and limited confidentiality impact. NVD had not yet assigned its own score at the time the record appeared, but the broad outline is clear enough: this is an information disclosure flaw, not a one-click machine takeover.That does not make it ignorable. The bug is described as a race condition in Chromium’s Shared Storage implementation, allowing an attacker who had already compromised the renderer process to leak cross-origin data using a crafted HTML page. In plain English, the attack assumes the adversary has already won one round inside the browser’s rendering engine and is then using this flaw to press further against origin separation.
That “already compromised renderer” clause is doing a lot of work. It is the reason the severity is not higher, and it is also the reason defenders should not dismiss the issue too quickly. Modern browser exploitation is often chained: one bug gets execution in a constrained place, another weakens the sandbox or privacy boundary, and a third turns the whole thing into something operationally useful.
Shared Storage itself is part of the browser’s attempt to square a circle. Advertisers, publishers, and web platforms want measurement and personalization; users and regulators want fewer third-party cookies and less cross-site tracking; browser vendors want APIs that promise controlled, privacy-preserving alternatives. When those new APIs malfunction, the failure mode is rarely as simple as “a page crashes.” It is more likely to involve data boundaries that only security engineers, web platform specialists, and ad-tech lawyers can fully diagram.
The Renderer Was Supposed to Be the Blast Wall
The most important phrase in the CVE description is not “race condition.” It is “compromised the renderer process.” Chrome, Edge, and other Chromium-based browsers rely on site isolation, sandboxing, process separation, and origin rules to prevent a malicious page from seeing what it should not see. The renderer is where web content lives, but it is also supposed to be a dangerous neighborhood with walls around it.A vulnerability that requires renderer compromise does not start the fire; it helps the fire spread. That matters because exploit writers do not think in CVSS rows. They think in chains, reliability, primitives, and payoff. If an attacker can use a separate Blink, V8, graphics, media, or IPC flaw to gain a foothold in the renderer, a bug like CVE-2026-7954 may become a way to harvest information that should have remained fenced off.
The race condition angle is also telling. Races are notoriously awkward to reason about because the vulnerable behavior depends on timing, concurrency, and state transitions rather than a single obviously bad input. In a browser, where dozens of subsystems are negotiating storage, permissions, frames, workers, navigations, and site isolation, timing bugs can become especially subtle.
That subtlety is why “Medium” Chromium bugs deserve more respect than they often get. They may not be the exploit chain’s opening act, but they can be the supporting role that turns a browser bug from annoying into useful. A confidentiality leak may expose tokens, identifiers, browsing-state signals, measurement outputs, or other data that helps an attacker understand or personalize the next step.
The web security model is built around the same-origin policy, but the lived reality is a stack of exceptions, special cases, postMessage pathways, embedded content, fenced frames, storage APIs, and privacy mitigations. CVE-2026-7954 appears to live in that messy middle. It is a vulnerability in the machinery that decides what one context can learn about another.
Chrome 148 Was a Security Release Wearing a Routine Update Costume
Chrome 148’s desktop update was not built around this single CVE. Google’s stable-channel release pushed Chrome to 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS, and reporting around the release counted 127 security fixes. Three were classified as Critical, including an integer overflow in Blink and use-after-free bugs in Mobile and Chromoting.That broader context matters because CVE-2026-7954 is easy to lose in the pile. In a patch bundle with more than 100 fixes, administrators naturally triage toward Critical and High severity items. Yet the bundle is also a map of the browser’s attack surface: rendering, remote desktop plumbing, mobile components, storage, privacy APIs, and the glue between them.
Chrome’s update cadence can make these releases feel ordinary. For consumers, the browser quietly patches itself and offers a relaunch button. For enterprise IT, that normalcy is both a blessing and a trap. The blessing is that most endpoints should receive the fix with little drama. The trap is that “automatic” is not the same as “verified,” especially across virtual desktops, kiosk systems, server-hosted browsers, golden images, offline machines, and tightly managed update rings.
The version numbers are the operational fact that matters. Chrome prior to 148.0.7778.96 is the vulnerable line identified for CVE-2026-7954, with Windows and macOS seeing 148.0.7778.96/97 in the stable release stream. Edge, because it rides Chromium but ships on Microsoft’s cadence and versioning, fixed the relevant Chromium batch in Edge Stable 148.0.3967.54 on May 7.
That one-day gap between Google’s stable release and Microsoft’s Edge note is not scandalous. It is the normal reality of a shared engine moving through multiple vendors’ build, validation, and distribution systems. But it is exactly why Windows shops need to track both Chrome and Edge as first-class patch targets instead of assuming “Chromium” is a single monolithic product.
Edge Turns Chromium Risk Into a Windows Fleet Issue
For WindowsForum readers, the Microsoft angle is not incidental. Microsoft’s security update guide entry for CVE-2026-7954 points back to the Chromium issue, and Edge’s May 7 security release says version 148.0.3967.54 incorporates the most recent Chromium security updates. That means the practical question in many environments is not “Do we run Chrome?” but “How many Chromium engines do we run, and who owns each update path?”A Windows 11 endpoint can easily have Edge as the default managed browser, Chrome installed for compatibility, WebView2 powering desktop apps, Electron-based applications embedding Chromium-derived code, and third-party browsers with their own update logic. CVE-2026-7954 is formally about Google Chrome before a specific version, but the surrounding ecosystem is bigger than the product name in the CVE entry.
Edge’s release also contained Microsoft Edge-specific fixes, which is a useful reminder that Microsoft is not merely copying Google’s bits and changing the icon. The browser has its own update channel, enterprise policy surface, account integrations, sync behavior, security features, and platform hooks. Chromium vulnerabilities may arrive through the shared engine, while Edge-specific issues travel alongside them.
The admin problem is that users experience all of this as “the browser,” while defenders have to inventory the pieces. A user may open a phishing link in Chrome, authenticate through Edge, launch an app that embeds WebView2, and preview content inside Teams or Outlook flows that rely on web components. From the attacker’s point of view, any renderable web surface is interesting.
This is why browser patch management has quietly become endpoint security work, not desktop convenience work. It belongs in the same operational rhythm as Defender updates, Windows cumulative updates, Office servicing, and third-party application patching. If the browser is the primary place where untrusted code enters the enterprise, then browser version drift is not cosmetic debt. It is exposure.
Shared Storage Shows the Privacy Sandbox Is Also an Attack Surface
Shared Storage is not a household name, even among many power users. It is part of the broader movement to replace older, more invasive cross-site tracking mechanisms with APIs that put limits around what can be stored, computed, and revealed. The idea is to let sites perform certain measurement or selection tasks without handing them the full set of cross-site identifiers that made third-party cookies so toxic.That is the noble version of the story. The engineering version is harder: browsers are adding new primitives that deliberately allow limited cross-context computation while trying to prevent uncontrolled cross-origin leakage. Every new primitive has state, timing, permissions, lifecycle behavior, and edge cases. Every edge case is a place where a race condition can hide.
CVE-2026-7954 should therefore be read as part of a larger pattern. The web platform is not getting simpler as it becomes more privacy-conscious. It is getting more elaborate. Instead of a blunt third-party cookie jar, browsers now ship an expanding suite of privacy-preserving APIs, anti-fingerprinting defenses, storage partitioning schemes, attribution tools, fenced contexts, and isolated execution models.
Security teams should not hear that as an argument against privacy engineering. The old tracking model was indefensible from a user trust perspective. But the replacement model asks browser vendors to become not just software companies, but governors of extremely delicate information flows. When those flows are controlled by complex asynchronous browser internals, race bugs become governance failures as much as code defects.
There is a broader irony here. The Privacy Sandbox era was supposed to reduce cross-origin leakage by design. A Shared Storage race that can leak cross-origin data after renderer compromise does not invalidate that project, but it does reveal the cost of moving privacy guarantees deeper into browser implementation details. The promise becomes only as strong as the synchronization logic enforcing it.
The CVSS Score Tells the Truth and Still Misses the Point
The low CVSS score is defensible. A remote attacker needs the victim to interact with a crafted page, the attack complexity is high, and the attacker must already have compromised the renderer. There is no stated impact on integrity or availability, and the confidentiality impact is limited. In the taxonomy of browser bugs, this is not the monster under the bed.But CVSS is a measurement framework, not a patching strategy. It is especially awkward for browser-chain vulnerabilities, where individual bugs often look modest in isolation and dangerous in combination. A renderer-only leak may be low severity until paired with an actively exploited renderer bug, a sandbox escape, a phishing campaign, or a target with valuable authenticated web sessions.
The exploitability language also deserves careful reading. There is no public indication in the available advisory language that CVE-2026-7954 is being exploited in the wild. That distinction matters. This is not one of those Chrome advisories where the browser vendor explicitly says an exploit exists in the wild and everyone should assume active attack pressure.
Still, the absence of known exploitation is not a permission slip to wait indefinitely. Browser vulnerabilities age poorly after patches ship. Attackers can diff open-source code, study bug references as they become available, and look for users who lag behind automatic updates. The window between patch availability and broad fleet adoption is where “Medium” bugs become useful tools for selective exploitation.
The right response is proportionate urgency. Home users should relaunch Chrome and Edge and verify they are current. Enterprise teams should check telemetry, update rings, and any frozen channels. Security teams should prioritize systems that process untrusted web content, handle sensitive SaaS sessions, or sit in high-value user groups such as finance, engineering, legal, identity administration, and executive staff.
The CPE Note Is a Small Database Detail With Real Consequences
The NVD record’s CPE configuration is more interesting than it looks. It identifies Google Chrome versions up to, but excluding, 148.0.7778.96, and associates that application entry with Windows, Linux, and macOS operating-system platforms. The record also carries the familiar “Are we missing a CPE here?” prompt, which is easy to ignore unless you have ever depended on vulnerability scanners for compliance.CPEs are the plumbing behind a lot of automated vulnerability management. If the product mapping is incomplete, too broad, too narrow, or slow to update, scanners may miss affected assets or flag systems incorrectly. In browser land, that problem is amplified by forks, embedded runtimes, channel differences, and vendor-specific version schemes.
For Chrome itself, the mapping is straightforward enough. Chrome before 148.0.7778.96 is vulnerable. But the real world is full of “Chromium-based” products that do not always map cleanly to the Chrome CPE. Edge gets its own MSRC treatment and own version number. Other browsers and embedded frameworks may inherit the vulnerable code on their own schedules, or may not expose the same feature set in the same way.
This is where security operations often becomes anthropology. You need to know not only what software is installed, but how it is built, who updates it, what channel it tracks, and whether the vulnerable component is reachable. A CPE entry can start the conversation, but it cannot finish it.
The practical implication is that administrators should not wait for scanner certainty before handling obvious browser updates. If Chrome is present, update Chrome. If Edge is present, update Edge. If Chromium-derived applications are mission-critical or exposed to untrusted content, track vendor advisories for those applications rather than assuming the Chrome CVE tells the whole story.
The Exploit Chain Is the Browser’s Real Unit of Risk
Browser security has spent the last decade making single-bug compromise harder. Sandboxes, site isolation, memory safety work, exploit mitigations, hardened allocators, process boundaries, and permission prompts all exist because a browser is expected to parse hostile content every minute of every day. The result is that many serious attacks now require chains instead of lone silver bullets.CVE-2026-7954 fits that model. On its own, it is a data leak after renderer compromise. In a chain, it could help an attacker learn something they should not know across an origin boundary. That information might not be dramatic in the abstract, but exploitation is often about converting small primitives into leverage.
A cross-origin leak can matter because web applications increasingly carry the business. Identity providers, internal dashboards, HR portals, source-code systems, cloud consoles, finance tools, and collaboration suites all live behind browser tabs. The browser’s origin model is the invisible line keeping one authenticated context from bleeding into another.
Attackers understand this better than users do. They do not need to “own the machine” in the classic malware sense if they can manipulate or observe enough of a high-value browser session. The industry’s obsession with endpoint compromise sometimes misses the fact that a great deal of enterprise authority now resides in bearer tokens, web sessions, OAuth flows, and browser-mediated trust.
That is why confidentiality bugs in browsers deserve a more nuanced reading than confidentiality bugs in many desktop applications. A small leak in the wrong browser context can disclose more than a file path or a preference. It can expose state, identity, or cross-site signals that help defeat assumptions built into web application security.
Automatic Updates Are a Policy, Not a Guarantee
Chrome and Edge both have mature automatic update systems, and most consumer users will be protected quickly if they let the browser relaunch. In enterprise environments, however, automatic update behavior is frequently modified by policy. Admins defer updates to preserve compatibility, freeze versions for line-of-business apps, stage rollouts, or rely on software distribution tools that run behind the browser vendor’s own cadence.Those decisions are not irrational. Browser updates can break workflows, especially in organizations with legacy web apps, internal certificate oddities, brittle extensions, or kiosk deployments. The problem is that the threat model has changed faster than many update policies. Holding a browser back is no longer like delaying a media player patch. It is delaying the repair of the primary interpreter for hostile code.
The May 2026 Chrome 148 release makes that tradeoff vivid. A single update carried more than 100 security fixes and multiple critical vulnerabilities. Even if CVE-2026-7954 is not the headline, the release bundle as a whole argues against long deferrals. The more security fixes packed into a browser update, the more expensive each day of delay becomes.
For managed Windows fleets, the answer is not blind instant deployment everywhere. It is disciplined rings with tight timelines. A small validation group can catch breaking issues, but the production rollout should move in days, not weeks, unless a concrete compatibility blocker exists. Security exceptions should be documented as risk decisions, not hidden inside “standard change windows.”
The same logic applies to relaunch enforcement. A browser can download an update and still run vulnerable code until the process restarts. User-friendly nagging is not always enough. For high-risk populations, admins should consider policies that require relaunch after a defined grace period, particularly when Chrome or Edge releases include exploited-in-the-wild flaws or large security bundles.
The Admin Work Is Boring, Which Is Why It Matters
The response to CVE-2026-7954 is not glamorous. There is no magic mitigation to deploy, no registry tweak that turns a Medium race into a non-issue, and no reason to block the entire web in a fit of theater. The work is version verification, update enforcement, asset inventory, and attention to Chromium’s extended ecosystem.That boringness is exactly why it matters. Security failures often accumulate in the gap between “the vendor patched it” and “our actual machines are running the patched build.” Browser patching looks easy from the outside because users see a relaunch button. Inside a real environment, that button competes with uptime expectations, locked-down profiles, VDI images, packaging systems, browser extensions, and users who keep sessions open for weeks.
There is also a communication challenge. Calling CVE-2026-7954 “low score” may encourage complacency. Calling it a “cross-origin data leak after renderer compromise” may cause eyes to glaze over. The defensible message is simpler: update Chromium-based browsers because the current stable releases close a large batch of security issues, including a Shared Storage bug that weakens browser data isolation under compromised-renderer conditions.
Admins should also remember that browser security posture is cumulative. Enhanced security modes, extension controls, site isolation policies, safe browsing, download protections, application control, and phishing-resistant authentication all shape the likelihood that a browser bug becomes an incident. Patching is essential, but it is one layer in a model that assumes web content cannot be trusted.
For Windows shops, Edge’s integration with the operating system cuts both ways. It gives Microsoft strong update distribution channels and policy management. It also means Edge is present almost everywhere, even where Chrome is the user-preferred browser. Treating Edge as “unused” because employees click a different icon is a familiar mistake.
The Version Numbers Are the Message This Week
The immediate facts are clear enough, and they are more useful than the speculation that often fills the space around new CVEs. Google’s fixed Chrome desktop line is 148.0.7778.96 or later, with Windows and macOS also seeing 148.0.7778.97. Microsoft’s fixed Edge Stable release is 148.0.3967.54. The CVE was published and modified on May 6, 2026, and Edge’s corresponding security release followed on May 7.The vulnerability is a race condition in Shared Storage, categorized under CWE-362, and the described impact is cross-origin data leakage via crafted HTML after renderer compromise. The published Chromium severity is Medium, while CISA’s ADP CVSS vector rates it Low at 3.1. There is no advisory language in the available record saying that this specific CVE is known to be exploited in the wild.
Those details are not trivia. They let defenders calibrate urgency without either shrugging or catastrophizing. The priority is to confirm browser versions, not to write an incident report for every machine that was a few hours behind.
A Patch That Belongs in the Browser Habit Loop
CVE-2026-7954 is a useful case study because it is not spectacular. It is the kind of vulnerability that reveals whether an organization’s browser security process runs on habit or heroics. If the only things that get attention are critical zero-days with cable-news energy, then lower-scored chain components will sit around waiting for the next attacker to combine them with something worse.Here is the concrete shape of the response:
- Chrome installations should be updated to 148.0.7778.96 or later, with Windows and macOS systems accepting the 148.0.7778.96/97 stable builds as applicable.
- Microsoft Edge Stable should be updated to 148.0.3967.54 or later so that the latest Chromium security fixes and Edge-specific fixes are present.
- Managed environments should verify actual running browser versions after relaunch, because downloaded updates do not protect sessions that remain open on old code.
- Vulnerability teams should treat CPE data as a starting point and separately track Chromium-based browsers, embedded runtimes, and applications that render untrusted web content.
- Security teams should prioritize faster rollout for users with privileged SaaS access, administrative cloud portals, financial systems, source-code systems, or other high-value browser sessions.
- The absence of known exploitation for this CVE should reduce panic, not delay patching, because browser bugs become more actionable after fixes are public.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center