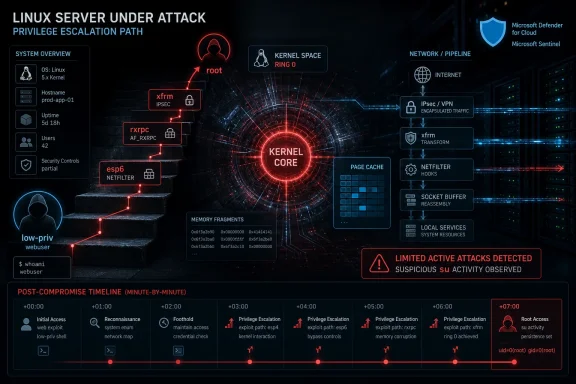
Microsoft disclosed on May 8, 2026, that “Dirty Frag,” a Linux local privilege escalation vulnerability chain involving esp4, esp6, and rxrpc kernel components, is being investigated in limited active attacks that can turn low-privileged local execution into root control. The unpleasant part is not simply that another Linux kernel bug exists; it is that this one lives in the post-compromise lane where defenders often have the least time and the most assumptions. Dirty Frag is a reminder that “local” does not mean “low priority” when every serious intrusion tries to become local as quickly as possible.
The industry still talks about compromise as if the front door is the decisive moment. A password works, a web shell lands, a container gives up a foothold, and the story begins. Dirty Frag argues that the more important question is what happens in the next minute.
Microsoft’s report frames Dirty Frag as a local privilege escalation path: an attacker already has some form of code execution, but not yet full control of the machine. That is the zone where modern intrusions either stall or become operational campaigns. Root access changes everything because it gives the attacker the ability to disable agents, read secrets, alter logs, implant persistence, and turn one Linux host into a staging point for the rest of the estate.
That is why this bug matters even if it is not a remote-code-execution flaw. A remote flaw gets the headline because it sounds like the breach. A reliable local privilege escalation is often what makes the breach durable.
Dirty Frag also lands at an awkward moment for defenders. It arrives shortly after CopyFail, another Linux privilege escalation issue involving page-cache manipulation, and it appears to extend the same class of concern into additional kernel paths. When two related bugs appear close together, the operational problem becomes larger than one CVE: administrators must ask whether their Linux patching, module-hardening, and container-boundary assumptions are keeping pace with the way attackers actually chain vulnerabilities.
The esp4 and esp6 paths sit in the orbit of IPsec and xfrm processing. RxRPC, meanwhile, is a remote procedure call mechanism used by systems such as AFS-related workflows. Many administrators may never have knowingly configured these components, but kernel modules often exist because a distribution needs broad capability out of the box. The distance between “we do not use that” and “that module can be loaded” is where many mitigation plans become wishful thinking.
Microsoft describes Dirty Frag as abusing kernel networking and page-cache behavior to reach root. Public reporting has described the vulnerability chain as more deterministic than classic race-condition privilege escalations, which is an important distinction. Race bugs can be noisy, fragile, and environment-dependent; a more reliable logic bug is easier to operationalize.
That reliability changes the defender’s risk calculation. If exploitation is brittle, monitoring for crashes and failed attempts may give defenders a chance to notice trouble. If exploitation is stable, the first visible sign may be a root shell, a tampered authentication file, or missing session artifacts.
Dirty Frag is useful to an attacker who has already obtained limited execution. That could be a compromised SSH account, a web shell on an exposed application, a foothold inside a container, or a service account with enough permissions to run code but not enough to own the host. In other words, it fits naturally into the messy middle of real incidents.
This is why Linux local privilege escalation has become a cloud security problem, not just a server-hardening problem. The modern Linux host is frequently a node in a Kubernetes cluster, a VM underneath a managed service, a jump box, a build agent, or a database server carrying secrets that unlock something larger. Root on that host can mean access to tokens, mounted volumes, logs, configuration files, and credentials that were never meant to be available to a low-privileged process.
The container angle deserves special attention. Containers reduce the blast radius only when the surrounding controls are correctly configured and enforced. A host-kernel privilege escalation does not care much about a team’s diagram if the vulnerable kernel is shared and the workload has a path to the relevant primitive.
The reported sequence is familiar in the way bad incident timelines often are. An external connection gains SSH access and spawns an interactive shell. A staged ELF binary named
That GLPI detail is especially telling. GLPI is an IT asset and service management platform, which means it can sit near identity, inventory, support workflows, and administrative context. An attacker who pivots from root escalation into GLPI files is not just defacing a box; they are hunting for business logic, authentication paths, sessions, and operational leverage.
The observed deletion and wiping of PHP session files has two possible readings, and neither is comforting. It may be an attempt to disrupt active user sessions, cover tracks, force reauthentication, or manipulate the application state. It may also reflect a search for session contents before or during cleanup. Either way, the attacker’s focus moves quickly from “can I become root?” to “what can root help me steal or change?”
The affected landscape is broad: Microsoft names Ubuntu, RHEL, CentOS Stream, AlmaLinux, Fedora, openSUSE, and OpenShift among environments that may be affected. Public reports have also emphasized the breadth of major distribution exposure, though exact kernel versions, vendor backports, default module behavior, and distribution-specific mitigations can change the answer for a given system.
This is where Linux patch management becomes harder than Windows patch management in practice, even for teams that love Linux. There is no single Patch Tuesday moment that answers the entire estate. A fleet may include vendor kernels, cloud provider kernels, container hosts, appliances, long-term-support releases, custom builds, and images that are rebuilt only when someone remembers that images are also infrastructure.
The right response is not panic, but it is also not waiting for perfect clarity. Dirty Frag sits in the category of vulnerability where partial mitigation can be useful, provided administrators understand the operational tradeoffs. Blocking vulnerable modules may reduce exposure, but it can also break workloads that depend on IPsec, VPN functionality, RxRPC, or related networking behavior.
This is why Dirty Frag forces administrators to distinguish inventory from assumption. It is not enough to say “we do not run IPsec.” Teams need to know whether the modules are loaded, whether they can be autoloaded, whether a vendor agent or VPN dependency expects them, and whether container workloads can trigger the relevant paths. The answer may vary across laptop fleets, VPN concentrators, Kubernetes nodes, CI runners, and legacy application servers.
Microsoft also warns that mitigation does not necessarily reverse changes made before the mitigation was applied. That point deserves more attention than it will probably get. If exploitation already occurred, disabling a module may close the door behind the intruder without removing what the intruder left in the room.
The page-cache angle further complicates response. Microsoft suggests that organizations validate critical file integrity and evaluate whether cache clearing is appropriate, while noting that dropping caches can affect performance by increasing disk I/O. That is not a command to paste blindly into every production host; it is a reminder that kernel-memory side effects can outlive the first exploit step.
That matters for WindowsForum readers because the Windows-vs-Linux framing is increasingly obsolete in enterprise defense. Windows endpoints, Linux servers, Microsoft 365 identities, Azure workloads, third-party SaaS, and Kubernetes clusters are usually part of the same incident graph. An attacker who roots a Linux host may still be moving toward Active Directory, Entra credentials, source code, backup infrastructure, or a Windows management plane.
Microsoft lists Defender Antivirus detections for DirtyFrag-labeled exploit and Trojan families, Defender for Endpoint behavioral coverage around suspicious SUID and SGID process launches, Defender for Cloud detection for potential Dirty Frag exploitation, and Vulnerability Management surfacing of devices linked to the relevant CVEs. That coverage is useful, but it also illustrates the layered nature of the problem. Signature names help when exploit artifacts are known; behavioral detections help when the actor’s next move is visible; vulnerability management helps only if the asset is enrolled and accurately assessed.
Security Copilot also appears in Microsoft’s positioning, as expected. The practical value there will depend less on generative polish and more on whether the tool can accelerate the unglamorous work: correlating SSH access, process execution, privilege escalation, file edits, session deletion, package state, kernel version, and module status across many machines. Dirty Frag is exactly the type of incident where the winner is not the team with the prettiest dashboard, but the team that can answer “which hosts were exposed, which were touched, and which are still dangerous?” before the attacker pivots again.
Dirty Frag does not need mythology. It needs asset inventory, kernel version mapping, module state checks, patch tracking, container posture review, and post-exploitation hunting. Those are not glamorous tasks, but they are the tasks that determine whether a flashy exploit becomes a contained maintenance event or an incident report.
The temptation will be to ask whether a given host is “vulnerable” as if the answer were binary. In practice, risk sits across several dimensions: whether the kernel contains the vulnerable code, whether the relevant modules are available or loaded, whether unprivileged users or workloads can reach the primitives, whether local execution is plausible, whether compensating controls such as seccomp or AppArmor change exploitability, and whether an attacker already had a foothold before the team started asking these questions.
That is why the most mature response to Dirty Frag will look less like a single emergency command and more like a short campaign. Patch where patches exist. Mitigate where patching lags. Hunt where exposure was real. Rebuild where trust is gone.
Attackers do not need every machine to be vulnerable forever. They need one exposed path from low privilege to high privilege during the window between disclosure and remediation. That window is where proof-of-concept code, public reporting, vendor advisories, and opportunistic scanning collide.
For Windows administrators who also manage Linux estates, this should feel familiar. The lesson of years of Microsoft patching is not that every update is painless; it is that predictable operational machinery beats heroic improvisation. Linux environments need the same discipline: emergency kernel rollout plans, tested rollback paths, module-deny policies, container security baselines, and visibility that does not depend on a single vendor console.
The uncomfortable truth is that many mixed estates still treat Linux as the quieter platform. It gets fewer helpdesk tickets, fewer desktop complaints, and fewer visible user disruptions. Dirty Frag is a reminder that quiet is not the same as safe.
Source: Microsoft Active attack: Dirty Frag Linux vulnerability expands post-compromise risk | Microsoft Security Blog
 Dirty Frag Turns the Second Step Into the Real Breach
Dirty Frag Turns the Second Step Into the Real Breach
The industry still talks about compromise as if the front door is the decisive moment. A password works, a web shell lands, a container gives up a foothold, and the story begins. Dirty Frag argues that the more important question is what happens in the next minute.Microsoft’s report frames Dirty Frag as a local privilege escalation path: an attacker already has some form of code execution, but not yet full control of the machine. That is the zone where modern intrusions either stall or become operational campaigns. Root access changes everything because it gives the attacker the ability to disable agents, read secrets, alter logs, implant persistence, and turn one Linux host into a staging point for the rest of the estate.
That is why this bug matters even if it is not a remote-code-execution flaw. A remote flaw gets the headline because it sounds like the breach. A reliable local privilege escalation is often what makes the breach durable.
Dirty Frag also lands at an awkward moment for defenders. It arrives shortly after CopyFail, another Linux privilege escalation issue involving page-cache manipulation, and it appears to extend the same class of concern into additional kernel paths. When two related bugs appear close together, the operational problem becomes larger than one CVE: administrators must ask whether their Linux patching, module-hardening, and container-boundary assumptions are keeping pace with the way attackers actually chain vulnerabilities.
The Kernel’s Networking Plumbing Becomes an Attack Surface
Dirty Frag is tied to Linux kernel networking and memory-fragment handling components, specifically esp4, esp6, and rxrpc. Those names do not sound like the usual material of emergency boardroom briefings, which is precisely the problem. The Linux kernel is a vast accumulation of subsystems built to support real workloads, and attackers love the parts of a platform that are present, powerful, and rarely discussed.The esp4 and esp6 paths sit in the orbit of IPsec and xfrm processing. RxRPC, meanwhile, is a remote procedure call mechanism used by systems such as AFS-related workflows. Many administrators may never have knowingly configured these components, but kernel modules often exist because a distribution needs broad capability out of the box. The distance between “we do not use that” and “that module can be loaded” is where many mitigation plans become wishful thinking.
Microsoft describes Dirty Frag as abusing kernel networking and page-cache behavior to reach root. Public reporting has described the vulnerability chain as more deterministic than classic race-condition privilege escalations, which is an important distinction. Race bugs can be noisy, fragile, and environment-dependent; a more reliable logic bug is easier to operationalize.
That reliability changes the defender’s risk calculation. If exploitation is brittle, monitoring for crashes and failed attempts may give defenders a chance to notice trouble. If exploitation is stable, the first visible sign may be a root shell, a tampered authentication file, or missing session artifacts.
“Local” Is Where Cloud Attacks Go to Grow Up
For years, many vulnerability triage programs have treated local privilege escalation as second-tier risk. That made sense in an older model where the local attacker was imagined as a person with physical access or a disgruntled user on a shared server. It makes much less sense in the cloud-native reality of SSH keys, CI runners, web applications, service accounts, containers, and developer tooling.Dirty Frag is useful to an attacker who has already obtained limited execution. That could be a compromised SSH account, a web shell on an exposed application, a foothold inside a container, or a service account with enough permissions to run code but not enough to own the host. In other words, it fits naturally into the messy middle of real incidents.
This is why Linux local privilege escalation has become a cloud security problem, not just a server-hardening problem. The modern Linux host is frequently a node in a Kubernetes cluster, a VM underneath a managed service, a jump box, a build agent, or a database server carrying secrets that unlock something larger. Root on that host can mean access to tokens, mounted volumes, logs, configuration files, and credentials that were never meant to be available to a low-privileged process.
The container angle deserves special attention. Containers reduce the blast radius only when the surrounding controls are correctly configured and enforced. A host-kernel privilege escalation does not care much about a team’s diagram if the vulnerable kernel is shared and the workload has a path to the relevant primitive.
Microsoft’s Telemetry Shows the Shape of a Real Intrusion
Microsoft says Defender is seeing limited in-the-wild activity where privilege escalation involvingsu may be associated with Dirty Frag or CopyFail techniques. That caveat matters. The company is not claiming universal exploitation across the Internet; it is saying that telemetry shows behavior consistent with these techniques in active campaign investigation.The reported sequence is familiar in the way bad incident timelines often are. An external connection gains SSH access and spawns an interactive shell. A staged ELF binary named
update runs, immediately followed by privilege escalation activity involving su. The actor then moves into application-level territory, including GLPI-related files and PHP session data.That GLPI detail is especially telling. GLPI is an IT asset and service management platform, which means it can sit near identity, inventory, support workflows, and administrative context. An attacker who pivots from root escalation into GLPI files is not just defacing a box; they are hunting for business logic, authentication paths, sessions, and operational leverage.
The observed deletion and wiping of PHP session files has two possible readings, and neither is comforting. It may be an attempt to disrupt active user sessions, cover tracks, force reauthentication, or manipulate the application state. It may also reflect a search for session contents before or during cleanup. Either way, the attacker’s focus moves quickly from “can I become root?” to “what can root help me steal or change?”
The Patch Story Is Messy Because the Vulnerability Story Is Messy
Microsoft states that Linux Kernel Organization patches for CVE-2026-43284 were released on May 8, 2026, with NVD links available, while CVE-2026-43500 was reportedly reserved for the RxRPC issue but not yet published in NVD as of that same date. That is the kind of sentence that makes administrators sigh, because it means the remediation state is not reducible to one clean dashboard light.The affected landscape is broad: Microsoft names Ubuntu, RHEL, CentOS Stream, AlmaLinux, Fedora, openSUSE, and OpenShift among environments that may be affected. Public reports have also emphasized the breadth of major distribution exposure, though exact kernel versions, vendor backports, default module behavior, and distribution-specific mitigations can change the answer for a given system.
This is where Linux patch management becomes harder than Windows patch management in practice, even for teams that love Linux. There is no single Patch Tuesday moment that answers the entire estate. A fleet may include vendor kernels, cloud provider kernels, container hosts, appliances, long-term-support releases, custom builds, and images that are rebuilt only when someone remembers that images are also infrastructure.
The right response is not panic, but it is also not waiting for perfect clarity. Dirty Frag sits in the category of vulnerability where partial mitigation can be useful, provided administrators understand the operational tradeoffs. Blocking vulnerable modules may reduce exposure, but it can also break workloads that depend on IPsec, VPN functionality, RxRPC, or related networking behavior.
Module Mitigation Is a Scalpel, Not a Magic Spell
The most immediate mitigation guidance revolves around disabling or preventing the loading of rxrpc, esp4, esp6, and related functionality where it is not operationally required. That sounds simple enough until it meets production. Plenty of environments do not use these modules directly; some absolutely do, and some only discover that they do after something important stops working.This is why Dirty Frag forces administrators to distinguish inventory from assumption. It is not enough to say “we do not run IPsec.” Teams need to know whether the modules are loaded, whether they can be autoloaded, whether a vendor agent or VPN dependency expects them, and whether container workloads can trigger the relevant paths. The answer may vary across laptop fleets, VPN concentrators, Kubernetes nodes, CI runners, and legacy application servers.
Microsoft also warns that mitigation does not necessarily reverse changes made before the mitigation was applied. That point deserves more attention than it will probably get. If exploitation already occurred, disabling a module may close the door behind the intruder without removing what the intruder left in the room.
The page-cache angle further complicates response. Microsoft suggests that organizations validate critical file integrity and evaluate whether cache clearing is appropriate, while noting that dropping caches can affect performance by increasing disk I/O. That is not a command to paste blindly into every production host; it is a reminder that kernel-memory side effects can outlive the first exploit step.
Defender’s Linux Story Is Now Part of Microsoft’s Security Story
There is a broader industry signal in Microsoft’s handling of Dirty Frag. A Microsoft security blog post about an active Linux privilege escalation campaign is not an oddity anymore. It is a normal consequence of Microsoft’s enterprise security business, where Defender, Sentinel, Entra, Intune, Security Copilot, and cloud workload protection all pull the company into operating systems it does not own.That matters for WindowsForum readers because the Windows-vs-Linux framing is increasingly obsolete in enterprise defense. Windows endpoints, Linux servers, Microsoft 365 identities, Azure workloads, third-party SaaS, and Kubernetes clusters are usually part of the same incident graph. An attacker who roots a Linux host may still be moving toward Active Directory, Entra credentials, source code, backup infrastructure, or a Windows management plane.
Microsoft lists Defender Antivirus detections for DirtyFrag-labeled exploit and Trojan families, Defender for Endpoint behavioral coverage around suspicious SUID and SGID process launches, Defender for Cloud detection for potential Dirty Frag exploitation, and Vulnerability Management surfacing of devices linked to the relevant CVEs. That coverage is useful, but it also illustrates the layered nature of the problem. Signature names help when exploit artifacts are known; behavioral detections help when the actor’s next move is visible; vulnerability management helps only if the asset is enrolled and accurately assessed.
Security Copilot also appears in Microsoft’s positioning, as expected. The practical value there will depend less on generative polish and more on whether the tool can accelerate the unglamorous work: correlating SSH access, process execution, privilege escalation, file edits, session deletion, package state, kernel version, and module status across many machines. Dirty Frag is exactly the type of incident where the winner is not the team with the prettiest dashboard, but the team that can answer “which hosts were exposed, which were touched, and which are still dangerous?” before the attacker pivots again.
The Dirty Name Should Not Distract From the Boring Work
The “Dirty” branding inevitably recalls Dirty COW, and that is both helpful and misleading. It is helpful because it tells administrators this is a kernel privilege escalation issue involving memory semantics that can have broad impact. It is misleading if it turns the vulnerability into lore rather than work.Dirty Frag does not need mythology. It needs asset inventory, kernel version mapping, module state checks, patch tracking, container posture review, and post-exploitation hunting. Those are not glamorous tasks, but they are the tasks that determine whether a flashy exploit becomes a contained maintenance event or an incident report.
The temptation will be to ask whether a given host is “vulnerable” as if the answer were binary. In practice, risk sits across several dimensions: whether the kernel contains the vulnerable code, whether the relevant modules are available or loaded, whether unprivileged users or workloads can reach the primitives, whether local execution is plausible, whether compensating controls such as seccomp or AppArmor change exploitability, and whether an attacker already had a foothold before the team started asking these questions.
That is why the most mature response to Dirty Frag will look less like a single emergency command and more like a short campaign. Patch where patches exist. Mitigate where patching lags. Hunt where exposure was real. Rebuild where trust is gone.
The Hardest Hosts to Patch Are the Ones Attackers Like Best
Dirty Frag also exposes a familiar asymmetry in Linux operations. The hosts most attractive to attackers are often the ones most annoying to patch. They run business applications, carry long uptimes, sit behind change-control gates, or support workloads that no one wants to restart during business hours.Attackers do not need every machine to be vulnerable forever. They need one exposed path from low privilege to high privilege during the window between disclosure and remediation. That window is where proof-of-concept code, public reporting, vendor advisories, and opportunistic scanning collide.
For Windows administrators who also manage Linux estates, this should feel familiar. The lesson of years of Microsoft patching is not that every update is painless; it is that predictable operational machinery beats heroic improvisation. Linux environments need the same discipline: emergency kernel rollout plans, tested rollback paths, module-deny policies, container security baselines, and visibility that does not depend on a single vendor console.
The uncomfortable truth is that many mixed estates still treat Linux as the quieter platform. It gets fewer helpdesk tickets, fewer desktop complaints, and fewer visible user disruptions. Dirty Frag is a reminder that quiet is not the same as safe.
The Practical Signal Hidden Inside Microsoft’s Warning
The operational message from Dirty Frag is narrower than the headlines and broader than the CVE entry. It is not “every Linux box is doomed,” and it is not “wait for your distro and move on.” It is that post-compromise privilege escalation is now a first-order cloud and enterprise risk, especially when it hits broadly deployed kernel subsystems.- Organizations should identify Linux hosts where esp4, esp6, rxrpc, xfrm, IPsec, VPN, or AFS-related functionality is available, loaded, or required.
- Administrators should apply vendor kernel updates for CVE-2026-43284 as soon as tested packages are available for their distributions and cloud images.
- Teams should treat CVE-2026-43500 as an evolving RxRPC-related concern and track vendor advisories even where NVD publication or scoring lags behind operational reality.
- Security teams should hunt for post-compromise sequences involving SSH access, staged ELF binaries, sudden
suactivity, suspicious SUID or SGID launches, and application-session tampering. - Container platforms should be reviewed for host-kernel exposure, seccomp posture, unnecessary privileges, and workloads that can reach vulnerable kernel paths.
- Systems that may have been exploited before mitigation should receive integrity checks and incident-response scrutiny rather than being declared clean because a module was later disabled.
Source: Microsoft Active attack: Dirty Frag Linux vulnerability expands post-compromise risk | Microsoft Security Blog