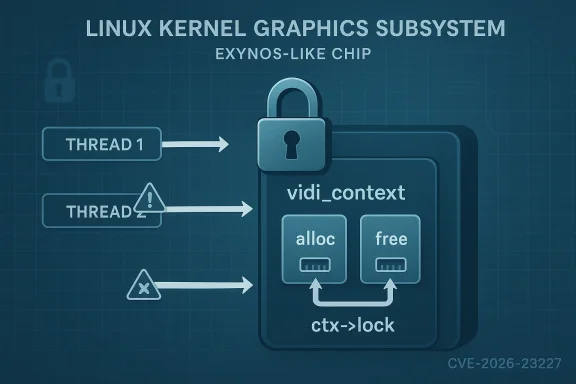
The CVE page for CVE-2026-23227 is currently unavailable, so the only reliable starting point is the upstream kernel fix description: “drm/exynos: vidi: use ctx->lock to protect struct vidi_context member variables related to memory alloc/free.” That wording points to a concurrency bug in the Exynos DRM vidi path, not a flashy exploit chain, but the sort of race condition that can quietly destabilize devices if memory ownership is not serialized correctly. In practical terms, the patch suggests the driver was touching context state tied to allocation and release without a strong enough lock boundary, creating a window for inconsistent state, use-after-free, or double-free style failures.
The Exynos DRM stack sits in the Linux graphics subsystem and serves Samsung’s Exynos SoCs, especially in embedded and mobile-class hardware where display reliability matters as much as raw performance. The vidi component is part of that ecosystem and is tied to virtual display or display-interface logic used by the driver. When a kernel graphics path handles memory allocation and teardown incorrectly, the result is rarely just a cosmetic glitch; it can become a system-wide crash, a persistent boot issue, or a security boundary failure.
The phrase “use
That matters because graphics drivers are not isolated utilities; they are deeply integrated into the kernel’s device lifecycle, memory subsystem, and userspace interfaces. A bug in teardown logic can be triggered during display reconfiguration, device close, suspend-resume transitions, or error recovery paths. In other words, the patch is not just about correctness in a narrow function, but about restoring coherent lifetime management in a shared subsystem.
This kind of fix also fits a broader pattern visible across recent Linux security disclosures: small synchronization mistakes in kernel subsystems are increasingly being elevated to tracked CVEs because the operational impact is real even when the code change is modest. We have seen similar patch-driven advisories where a single missing lock, stale pointer, or unsafe lifetime transition becomes the root cause of a denial-of-service or privilege boundary problem. That is why these fixes deserve attention even when the original advisory page is unavailable.
The practical risks include:
The key nuance is that this is not necessarily a memory allocator bug in the abstract; it is a lifetime coordination bug. That distinction matters for defenders because it tells them the trigger may be a legitimate driver operation rather than malformed input alone. In kernel land, legitimate API usage at the wrong time can still be enough to trigger a crash.
This is especially relevant for devices that depend on vendor kernels or downstream trees. Exynos platforms commonly ship through OEM-integrated stacks, which means patches may not arrive uniformly across all products. The result is a fragmented risk profile where one model is protected and another, superficially similar one, is still exposed.
Key implications include:
If the bug was reachable from userspace through an ioctl or other standard DRM interface, the attack surface becomes more interesting. An authenticated local user might be able to trigger the race repeatedly, increasing the odds of a crash or corruption event. That said, without the missing vendor page or a full commit trail, any statement about privilege escalation would be speculative.
The operational pain points are predictable:
The important takeaway is that the kernel community continues to treat these issues as security-relevant even when they start life as reliability defects. That is a healthy trend. It reflects the reality that on a modern system, a crash bug in privileged code is often only a short step away from a broader attack primitive.
For now, the safest reading is simple: this is a real kernel synchronization correction with plausible security implications, and organizations that ship or manage Exynos-based Linux systems should treat it as a patch-priority item rather than a routine code cleanup. Even when the CVE page goes dark, the upstream fix tells a clear story, and the story is one of protecting privileged memory state before it can be raced into failure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The Exynos DRM stack sits in the Linux graphics subsystem and serves Samsung’s Exynos SoCs, especially in embedded and mobile-class hardware where display reliability matters as much as raw performance. The vidi component is part of that ecosystem and is tied to virtual display or display-interface logic used by the driver. When a kernel graphics path handles memory allocation and teardown incorrectly, the result is rarely just a cosmetic glitch; it can become a system-wide crash, a persistent boot issue, or a security boundary failure.The phrase “use
ctx->lock to protect struct vidi_context member variables related to memory alloc/free” is classic kernel-synchronization language. It implies that one or more fields in the per-context state were being read, written, or freed from multiple execution paths without a single authoritative lock guarding them. In kernel drivers, that kind of omission is often invisible in normal use until timing, load, or error handling lines up just wrong.That matters because graphics drivers are not isolated utilities; they are deeply integrated into the kernel’s device lifecycle, memory subsystem, and userspace interfaces. A bug in teardown logic can be triggered during display reconfiguration, device close, suspend-resume transitions, or error recovery paths. In other words, the patch is not just about correctness in a narrow function, but about restoring coherent lifetime management in a shared subsystem.
This kind of fix also fits a broader pattern visible across recent Linux security disclosures: small synchronization mistakes in kernel subsystems are increasingly being elevated to tracked CVEs because the operational impact is real even when the code change is modest. We have seen similar patch-driven advisories where a single missing lock, stale pointer, or unsafe lifetime transition becomes the root cause of a denial-of-service or privilege boundary problem. That is why these fixes deserve attention even when the original advisory page is unavailable.
What the Fix Suggests
The shortest reading of the patch is that the driver needed a more disciplined critical section around thevidi_context object. The lock name matters: using ctx->lock implies the maintainers already had a context-scoped synchronization primitive available and are now extending its coverage to allocation and free-related members. That is usually a sign of a targeted remediation rather than a redesign.Why allocation and free paths are fragile
Memory lifetime bugs are common in kernel code because alloc/free logic is rarely linear. One path may allocate a structure, another may partially initialize it, a third may tear it down on error, and a fourth may free it during device removal. If those paths do not agree on a lock, a reference can vanish while another CPU still believes it is valid.The practical risks include:
- use-after-free when one thread dereferences memory already returned to the allocator,
- double-free when teardown is triggered twice,
- state corruption when one path sees half-initialized fields,
- NULL dereference if the object is cleared concurrently, and
- heisenbug-style crashes that appear only under load or specific timing.
Why a lock is the right first move
Using a lock to protect member variables is the kernel’s standard answer when state must be mutated by multiple call paths. It does not eliminate bugs by magic, but it makes ownership explicit. If the driver’s prior behavior allowed alloc/free-related fields to be updated without that protection, then the fix likely closes a race between worker contexts, ioctl handlers, or lifecycle callbacks.The key nuance is that this is not necessarily a memory allocator bug in the abstract; it is a lifetime coordination bug. That distinction matters for defenders because it tells them the trigger may be a legitimate driver operation rather than malformed input alone. In kernel land, legitimate API usage at the wrong time can still be enough to trigger a crash.
Why Kernel Graphics Bugs Matter
Graphics drivers often get treated as “just display code,” but in the kernel they are part of a privileged execution environment. A crash in DRM can take down the whole machine, and a memory-safety flaw can sometimes be shaped into a more serious compromise depending on the surrounding conditions. That is why the security community treats kernel graphics bugs with the same seriousness as networking or filesystem flaws.Reliability and security overlap
The most important thing to understand about this advisory is that stability and security are not separate categories here. A race in memory allocation may first present as a flaky hang, but the same primitive can expose corruption or lifetime confusion that attackers can exploit. That overlap is one reason vendors often publish these issues through security channels even when the immediate symptom looks like a crash.This is especially relevant for devices that depend on vendor kernels or downstream trees. Exynos platforms commonly ship through OEM-integrated stacks, which means patches may not arrive uniformly across all products. The result is a fragmented risk profile where one model is protected and another, superficially similar one, is still exposed.
Embedded and mobile implications
For phones, tablets, kiosks, and embedded Linux devices, graphics-path bugs can have outsized operational consequences. A display subsystem crash may look like a user-interface annoyance, but in a managed fleet it can mean failed check-ins, restart loops, or field service calls. In a kiosk or industrial deployment, it can become a business interruption.Key implications include:
- possible kernel panics during display lifecycle changes,
- increased risk during suspend/resume or hotplug events,
- harder troubleshooting because the fault may be timing-dependent,
- patch lag in OEM firmware trees, and
- potential security exposure in environments that expose graphics interfaces broadly.
What We Can Infer About the Attack Surface
Because the original CVE page is missing, we should be careful not to overstate exploitability. Still, the patch wording gives a fair amount away. If memory allocation and free-related fields instruct vidi_context were not properly guarded, then the bug likely lived at the boundary between object lifetime and concurrent access.Likely trigger conditions
The most plausible triggers are normal driver operations that happen at awkward moments. Think context creation and destruction, display reconfiguration, device close, or error cleanup while another thread is still touching the same state. That pattern is common in kernel work because many operations are asynchronous even when the user sees a simple, synchronous API.If the bug was reachable from userspace through an ioctl or other standard DRM interface, the attack surface becomes more interesting. An authenticated local user might be able to trigger the race repeatedly, increasing the odds of a crash or corruption event. That said, without the missing vendor page or a full commit trail, any statement about privilege escalation would be speculative.
What defenders should assume
Even if exploitation is unproven, defenders should treat this as a kernel memory-safety issue with availability impact at minimum. The safe assumption is that any system using the affected Exynos DRM vidi code should be updated as soon as a fixed kernel or vendor package is available. Where patching is delayed, reducing exposure to unnecessary graphics transitions may slightly lower risk, but it is not a substitute for the fix itself.Enterprise Impact
Enterprise environments rarely think about display drivers until the fleet starts behaving erratically. Thin clients, kiosks, digital signage, hardened terminals, and ruggedized edge devices often rely on exactly these kinds of kernels. A race in a graphics context object can become a service desk event long before it is recognized as a security issue.Fleet management consequences
If the affected code is present in vendor kernels distributed through appliance or device OEM channels, patching may require coordinated firmware updates rather than a simple package refresh. That can slow response times significantly. Enterprises with mixed fleets should verify which devices actually include Exynos-based components and which kernels inherit the vulnerable code path.The operational pain points are predictable:
- patch validation across hardware variants,
- delayed vendor backports,
- reboot requirements for kernel updates,
- potential regressions in graphics behavior after patching, and
- the need to stage fixes in maintenance windows.
Risk management perspective
From a security-management standpoint, this advisory reinforces a familiar lesson: kernel bugs in device drivers are not “edge” issues. They sit in the same trust boundary as the rest of the OS. If an attacker can reach the vulnerable path locally, the consequences can be severe enough to warrant urgent remediation even when the primary symptom is instability.Consumer Impact
For consumers, the problem is less about compliance and more about trust in everyday reliability. A graphics-related kernel bug can manifest as random reboots, display freezes, or a device that behaves perfectly until a specific sequence of screen changes or power events occurs. Users often blame the monitor, cable, or app long before they suspect the kernel.What users might notice
Symptoms could include:- sudden black screens or display resets,
- freezes after sleep or resume,
- application crashes that coincide with graphics activity,
- sporadic boot instability, and
- rare but repeatable hangs tied to certain workloads.
Why patch adoption can be uneven
Consumer devices also depend heavily on OEM support windows. Some handsets and embedded products receive backports quickly; others are effectively abandoned once their mainline support ends. In those cases, the existence of a fix does not guarantee that end users will ever receive it, which leaves security-by-device-lifecycle as the real determining factor.How This Fits the Broader Linux Kernel Pattern
This advisory belongs to a familiar class of Linux fixes where maintainers harden object lifetime rules rather than rethinking the driver from scratch. That is good engineering, but it also highlights how much security debt still accumulates in mature subsystems. Kernel code can be battle-tested and still contain small synchronization gaps that matter.The recurring theme: shared mutable state
Driver state tends to be shared across multiple paths because hardware does not wait for clean software boundaries. Initialization, teardown, power management, and userspace control all converge on the same objects. When the synchronization discipline slips, the bug may survive years of normal use before a rare interleaving exposes it.The important takeaway is that the kernel community continues to treat these issues as security-relevant even when they start life as reliability defects. That is a healthy trend. It reflects the reality that on a modern system, a crash bug in privileged code is often only a short step away from a broader attack primitive.
Why small fixes can have big consequences
A one-line lock change can have a large effect because it changes the ordering guarantees for the entire object lifecycle. That is particularly true in driver code, where races are often timing-sensitive and hard to reproduce. The right lock at the right layer can make the difference between a benign bug and a security incident.Validation and Uncertainty
The missing Microsoft page means we should avoid inventing details that are not supported by the available material. We know the fix title, we know the affected subsystem, and we know the patch is about protectingstruct vidi_context members related to memory allocation and free operations. We do not know from the available evidence whether Microsoft classified it as an elevation-of-privilege, denial-of-service, or information disclosure issue.What is known
- The issue is associated with drm/exynos: vidi.
- The fix uses
ctx->lockfor synchronization. - The protected fields are tied to memory alloc/free state in
struct vidi_context.
What remains unclear
- The exact CVSS or severity label,
- the full attack vector,
- whether exploitation is local-only,
- whether the issue is primarily a crash or a memory corruption primitive, and
- which downstream vendor kernels carry the vulnerable code.
Strengths and Opportunities
The good news is that this looks like a tightly scoped fix rather than a broad rewrite. That makes patching more feasible and lowers the odds of severe regression, assuming the lock coverage is complete. It also gives downstream maintainers a clear backport target and a well-defined place to verify behavior in testing.- The patch appears narrow and surgical rather than invasive.
- The driver already had a context lock available.
- The bug class is understandable and testable through lifecycle and concurrency analysis.
- OEMs can likely validate the fix with targeted regression tests.
- The issue highlights the value of upstream-to-downstream security tracing.
- Fleet operators get a chance to improve kernel update discipline on graphics-heavy devices.
- Security teams can use it as a reminder that driver stability is part of attack surface management.
Risks and Concerns
The main concern is that graphics-driver bugs often hide in downstream trees long after they are fixed upstream. That is especially true for vendor kernels, where backport policy and device support timelines vary. Another concern is that a race condition can be difficult to reproduce, which tempts teams to deprioritize it until it becomes an incident.- Patch lag across OEM and embedded device firmware lines.
- Difficult repro conditions that make validation slow.
- Possible kernel crashes under real-world workload timing.
- Risk of memory corruption if the original race was more than a benign ordering flaw.
- Limited visibility because the Microsoft CVE page is unavailable.
- Potentially uneven consumer remediation on older devices.
- False confidence if teams assume the issue is “just a display bug.”
Looking Ahead
What to watch next is whether the upstream patch appears in stable kernels and how quickly downstream vendors mirror it. If the fix is backported cleanly, the practical risk window will shrink quickly for well-maintained devices. If not, this may linger as a low-visibility but meaningful reliability and security issue across older Exynos-based systems.Next checkpoints
- Confirmation of the CVE entry once the advisory page is restored or mirrored.
- Stable-kernel backports and downstream vendor release notes.
- Any follow-up fixes that widen the lock coverage or address adjacent races.
- Evidence of exploitation, crash reports, or public discussion in kernel channels.
- Device-family coverage, especially for embedded and OEM-managed Exynos products.
For now, the safest reading is simple: this is a real kernel synchronization correction with plausible security implications, and organizations that ship or manage Exynos-based Linux systems should treat it as a patch-priority item rather than a routine code cleanup. Even when the CVE page goes dark, the upstream fix tells a clear story, and the story is one of protecting privileged memory state before it can be raced into failure.
Source: MSRC Security Update Guide - Microsoft Security Response Center