South African boards heading into 2026 face a stark, immediate choice: treat technology spending as an engine for growth — or as the single greatest controllable threat to next year’s balance sheet. The plain truth, argued in recent commentary from local industry leaders, is that routine IT behaviours from the past decade — over‑provisioning, fixed long‑term contracts, and tolerance for “shadow” subscriptions — are no longer affordable. This article takes that argument further: it summarizes five practical fixes for tech spend, verifies the underlying claims with independent evidence, and offers a step‑by‑step playbook CIOs and finance leaders can implement right now to protect the 2026 balance sheet.
For much of the cloud era enterprises accepted a benign myth: “pay only for what you use.” In reality, multi‑cloud complexity, inactive resources, and ungoverned AI usage turned consumption‑based pricing into a slow leak on corporate cash flow. Independent industry surveys now converge on the same uncomfortable figure — between roughly 27% and 32% of cloud budgets are routinely wasted on idle, oversized, or forgotten resources. This is not a rounding error; it is a systemic problem that FinOps and ITAM teams must show they can fix if boards are to trust ongoing investment in AI and digital transformation.
At the same time, the operating environment for IT has shifted. Microsoft’s formal end‑of‑support date for mainstream Windows 10 (October 14, 2025) creates new compliance and refresh pressures for any organisation still running legacy endpoints, and hyperscale AI expansion is reshaping both compute economics and electricity demand. These are not theoretical: the Windows lifecycle notice and Microsoft support guidance are explicit about the change in support status and the limited transitional options available to customers.
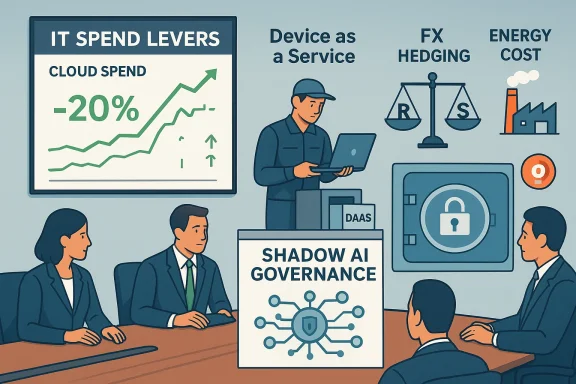
Against that backdrop, five focused levers — each practical, measurable, and vendor‑agnostic — will determine whether your 2026 P&L shows growth or erosion. They are: (1) stop the “lazy tax” on cloud spend with modern FinOps, (2) stop bleeding cash on Windows 10 ESUs and re‑think hardware funding with Device‑as‑a‑Service, (3) hedge currency exposure in vendor contracts, (4) treat energy as an explicit IT cost when comparing on‑premise vs cloud, and (5) consolidate and govern shadow AI to eliminate small recurring leaks and data risk. Each lever is explained, validated with independent sources, and accompanied by an actionable checklist.
Boards should require concrete milestones (30‑, 60‑, 90‑day) and measurable KPIs: % cloud spend reclaimed, number of devices moved to DaaS, FX exposure reduced, energy cost delta modelled, and shadow AI subscriptions consolidated. These metrics convert good intention into stewardship.
The era of “growth at all costs” is over. The real discipline for 2026 will be economical engineering — not austerity for its own sake, but ruthless prioritisation of where technology delivers measurable business value. Execute the five fixes above, measure the results, and treat tech spend as a controllable instrument of resilience rather than an open tap on the balance sheet.
Conclusion: protect the balance sheet by making tech spending accountable, automated, and auditable. The savings and reduced risk you achieve will be paid out not in press releases, but in operating margin — the currency that boards understand best.
Source: IOL Protecting the 2026 balance sheet: five ways to fix your tech spend
 Background / Overview
Background / Overview
For much of the cloud era enterprises accepted a benign myth: “pay only for what you use.” In reality, multi‑cloud complexity, inactive resources, and ungoverned AI usage turned consumption‑based pricing into a slow leak on corporate cash flow. Independent industry surveys now converge on the same uncomfortable figure — between roughly 27% and 32% of cloud budgets are routinely wasted on idle, oversized, or forgotten resources. This is not a rounding error; it is a systemic problem that FinOps and ITAM teams must show they can fix if boards are to trust ongoing investment in AI and digital transformation.At the same time, the operating environment for IT has shifted. Microsoft’s formal end‑of‑support date for mainstream Windows 10 (October 14, 2025) creates new compliance and refresh pressures for any organisation still running legacy endpoints, and hyperscale AI expansion is reshaping both compute economics and electricity demand. These are not theoretical: the Windows lifecycle notice and Microsoft support guidance are explicit about the change in support status and the limited transitional options available to customers.
Against that backdrop, five focused levers — each practical, measurable, and vendor‑agnostic — will determine whether your 2026 P&L shows growth or erosion. They are: (1) stop the “lazy tax” on cloud spend with modern FinOps, (2) stop bleeding cash on Windows 10 ESUs and re‑think hardware funding with Device‑as‑a‑Service, (3) hedge currency exposure in vendor contracts, (4) treat energy as an explicit IT cost when comparing on‑premise vs cloud, and (5) consolidate and govern shadow AI to eliminate small recurring leaks and data risk. Each lever is explained, validated with independent sources, and accompanied by an actionable checklist.
1) Stop paying the lazy tax on cloud: operationalize FinOps and automation
Why the lazy tax exists
Cloud billing is granular, opaque, and noisy. Engineering teams provision capacity to avoid performance risk; test and staging environments are left running; snapshots, unattached volumes, and forgotten reserved IPs accumulate. The result is predictable: a large share of monthly cloud invoices pays for resources that deliver no business value. Flexera and other industry reports place the typical waste figure in the high‑20s percentage range, and dozens of FinOps case studies show rightsizing and simple scheduling can reclaim double‑digit percentages of spend. This supports the claim that a “lazy tax” is being paid across many estates.Why manual audits no longer scale
Modern cloud estates are dynamic: autoscaling groups, serverless functions, ephemeral containers, managed platform services and complex pricing (commitments, savings plans, spot markets) create a velocity that manual, spreadsheet‑driven cost reviews cannot match. Human audits are slow, error‑prone, and incapable of acting in real time on fast‑moving spend spikes driven by AI workloads or data lakes. Industry commentary and vendor tooling trends underline that automation and continuous governance are now the baseline for cost accountability.The AI‑driven FinOps model
Transition from episodic cost reviews to continuous, automated FinOps:- Real‑time spend telemetry: centralised cost streaming and tagging so every dollar is attributed to a product, team, or project.
- Policy automation: automated suspend/resize policies for non‑prod environments (shutdown after hours, schedule‑based rightsizing).
- Autonomous agents: use policy agents to auto‑scale or replace oversized instances based on observed load patterns.
- Chargeback with accountability: integrate cost signals into engineering OKRs so teams own the economics of the services they run.
Practical Playbook (Immediate)
- Run a 30‑day cloud‑spend snapshot and validate the “waste” baseline (look for idle VMs, unattached storage, overallocated DB instances).
- Prioritize the top 10 workloads by spend and apply targeted rightsizing/commitment adjustments.
- Implement automated schedules for non‑prod stops (weekdays and business hours only).
- Deploy a FinOps dashboard with real‑time alerts for anomalous spend.
- Establish an engineering cost review cadence and tie cost KPIs to team performance reviews.
Risks and trade‑offs
- Over‑aggressive automation can affect reliability if policies are mis‑scoped. Start with non‑prod and burstable workloads.
- Some savings (e.g., long‑term commitments) require careful forecasts; commit only after stable usage patterns are proven.
2) The Windows 10 deadline has passed — stop funding the ESU drip and rethink hardware refresh
The crisis: end of support is real and immediate
Microsoft’s lifecycle calendar confirms the end of mainstream support for the mainstream Windows 10 editions on October 14, 2025. After that date, free security updates cease; organisations have very limited options: migrate to Windows 11, buy Extended Security Updates (ESU) for a short, costed bridge, or accept rising operational risk. The Microsoft support pages and lifecycle announcements document the mechanics and implications clearly.Why ESUs can be “dead money”
Paying for ESUs is a short‑term safety net — not a long‑term strategy. ESU fees are recurring and typically punitive by design: they buy time, not modernization. Many enterprises that held onto ESU coverage discovered their hardware and management stacks were the real bottleneck; continuing to pay for legacy OS support often delays the inevitable and diverts capital from transformative projects. Coverage windows are finite, and for most organisations ESU costs are a cash‑drain that does not improve security posture long term. Observers and IT practitioners have called the ESU path a tactical, not strategic, move.Device‑as‑a‑Service: convert CapEx spikes into predictable OpEx
Instead of a lump‑sum fleet refresh to meet Windows 11 hardware requirements, consider Device‑as‑a‑Service (DaaS). DaaS converts episodic capital outlays into monthly subscriptions, bundles lifecycle services (staging, imaging, repair, secure disposal), and shifts e‑waste responsibility to the vendor. Vendors and analysts list predictable cashflow, lifecycle management, and sustainability as primary benefits — all especially relevant where e‑waste regulation and disposal logistics are local pain points. Industry guides and vendors document these benefits and case studies.Implementation checklist (Windows refresh without breaking the bank)
- Inventory endpoints by capability and Windows 11 readiness; segregate by risk and productivity impact.
- Map users to device profiles (high‑compute vs knowledge workers vs kiosk) and prioritise migration cohorts.
- Test a DaaS pilot (100–500 devices) to validate real total cost of ownership (TCO), support SLAs, and refurb/disposal practices.
- Negotiate DaaS terms to include secure data‑erasure certificates and end‑of‑life recycling to meet local e‑waste obligations.
- Reframe procurement and finance: move hardware approvals from CapEx committees into Opex budgets for smoother scaling.
Cautions
- DaaS pricing varies widely; a poorly negotiated contract can be more expensive than phased CapEx refresh.
- Assess vendor ITAD (IT Asset Disposition) certifications — secure data destruction and certified recycling matter for compliance and reputation.
3) Hedge against currency: re‑structure contracts to remove forex exposure
The exposure
Most enterprise software and hardware are dollar‑ or euro‑denominated. When the Rand weakens, a local IT budget shrinks in real terms. This is not hypothetical in South Africa; currency moves can instantly change procurement economics. Organisations cannot control exchange rates, but they can control contract design to allocate risk appropriately.Contract levers to reduce forex risk
- Local currency billing: where vendors have local subsidiaries or partners, insist on Rand denominated invoices (shift forex risk to the vendor).
- Indexed escalation caps: limit annual currency or price escalation to fixed bands rather than open formulae tied to exchange rates.
- Flexibility clauses: avoid fixed headcount or license volume commitments; demand scale‑down rights so you are not paying for departed staff.
- Escape / rebalance clauses: include review windows to re‑negotiate pricing if market currency moves exceed material thresholds.
Practical negotiation steps (short list)
- Audit contracts to find all FX‑linked liabilities (SaaS, perpetual licenses, maintenance, hardware).
- Prioritise near‑term renewals and seek local currency options.
- Use multi‑year deals only when they include price‑reset or volume flexibility triggers.
- Work with finance to model FX breakpoints and include those thresholds in vendor negotiations.
Risks
- Vendors may prefer to remain USD/EUR priced; pushing to Rand can carry higher headline cost if vendors price the forex risk conservatively.
- Legal and tax implications of currency swaps or hedges require treasury oversight.
4) Treat energy as an IT cost: compare total energy and resilience economics, not just sticker price
The energy problem is also a resilience problem
In jurisdictions with unreliable grids and high backup fuel costs, on‑premise hosting has hidden operational costs. Running a server room in South Africa — factoring the diesel for backup generators, UPS losses, and increased cooling during outages — can make total cost of ownership materially higher than expected. Hyperscale cloud and colocation providers invest heavily in PUE improvements, advanced cooling (liquid, immersion), and renewable sourcing, yielding improved energy economics and operational reliability for many workloads. Industry analyses and sustainability pages from major providers and telcos document these efficiencies.What the numbers say (directional guidance)
- Hyperscale data centres typically report lower PUE (closer to 1.2–1.4 in modern facilities) compared with older on‑premise deployments where PUE can exceed 2.0.
- Cooling, UPS inefficiency and generator fuel during outages are often underestimated; in some cases these operational components double the effective power cost of on‑premise racks versus cloud colocations.
- For device fleets (laptops, desktops), Energy Star and modern silicon deliver measurable ongoing electricity savings at scale; on a 500‑device fleet small per‑device improvements compound into a tangible line item on the electricity bill.
How to fold energy into procurement decisions
- Include PUE, renewable sourcing percentage, and resilience SLAs in TCO models for hosting decisions.
- Quantify the cost of generator fuel and maintenance for on‑premise recovery scenarios and compare to cloud SLA guarantees and regional redundancy options.
- For endpoint refresh: add per‑device energy consumption and embodied carbon into the TCO (DaaS vendors often include this data in proposals).
Risks and caveats
- Not all workloads should move to public cloud; latency‑sensitive and data‑ sovereignty constrained applications may still require on‑premise or hybrid models.
- Cloud is not free of energy impact; large AI workloads will increase provider energy needs and may change price dynamics long term.
5) Consolidate the shadow AI sprawl: centralise procurement, governance, and prosecution
Shadow AI is different — and more dangerous — than Shadow IT
Employees are already using consumer GenAI tools and paying for subscriptions on corporate cards. The operational risk is twofold: small recurring costs accumulate, and corporate data—often sensitive—is uploaded to third‑party models with unknown retention or training policies. Gartner and multiple security studies warn that shadow AI became a systemic security blind spot in 2024–25, with a large share of organisations admitting unsanctioned use and a material risk of data leakage. This is not hypothetical; security vendors and analyst houses have documented the trend and its consequences.Consolidation benefits
- Lower unit cost: wholesale enterprise licenses are usually cheaper per seat than dozens of retail subscriptions.
- Data governance: enterprise contracts often include contractual assurances about training data, retention, and model privacy.
- Centralised control: consolidated procurement prevents malware or risky third‑party integrations accessing corporate repositories.
- Visibility and chargeback: a central billing model eliminates dozens of small, uncontrolled charges and gives procurement and finance control.
Immediate tactical plan
- Run an urgent shadow‑AI discovery: collect corporate credit card charges and run an expense audit focused on AI tools.
- Map exposure: identify where proprietary data has been pasted into public tools (by interviewing teams and analysing logs where possible).
- Centralise procurement: create an enterprise AI catalogue and move high‑value consumer subscriptions into an enterprise plan.
- Enforce policy: require that any AI use with corporate data occur only through approved, logged services and within contractual data protections.
- Educate and train: roll out concise, role‑based AI guidelines and mandatory quick training for high‑risk functions (legal, sales, engineering).
Risks and governance trade‑offs
- Centralising can reduce agility for creative teams; preserve a low‑friction path for experimentation with sandboxed, approved tools.
- Enterprise AI pricing sometimes follows consumption; control the cost by carefully restricting access to heavy compute endpoints (inference vs training).
Critical analysis: strengths, gaps, and latent risks
Strengths of the five‑point approach
- The prescription is pragmatic and measurable. Each lever ties to an explicit balance‑sheet metric: reclaimed cloud spend, avoided ESU fees, reduced FX exposure, lower energy and EV costs, and eliminated shadow subscription leakage.
- It aligns IT behaviours with finance and procurement — a cultural shift that boards can credibly demand.
- The approach reinforces security: tighter procurement and governance reduces both financial and data risk.
What the IOL piece gets right
- The article’s framing — that efficiency is a board‑level survival strategy — is accurate. Multiple industry reports show cloud waste and shadow AI are board‑relevant exposures. The Windows 10 timeline and the logic for DaaS also check out against Microsoft and vendor documentation.
Where the piece is optimistic or needs caveats
- The suggestion to “push for billing in Rands” is sensible, but may be impossible for some global suppliers without a local entity. Expect a negotiation premium where vendors take on FX risk.
- Moving workloads to the hyperscale cloud can reduce energy costs, but it does not remove all sustainability responsibilities; AI growth is changing provider economics and may alter unit pricing for heavy inference workloads. Cite the need to model high‑GPU workloads explicitly before migration.
Unverifiable or variable claims (flagged)
- Exact waste percentages vary by report and by organisation maturity. Industry estimates sit in a band (~27–32%), but your estate may be better or worse — conduct an internal audit rather than assuming the headline number. Flexera and peer reports are a reliable market signal, but the single number is not a substitute for a home audit.
Executive checklist: immediate steps to protect the 2026 balance sheet
- Board / CFO level (1–2 weeks)
- Mandate a 30‑day tech‑spend audit covering cloud, SaaS, licensing, and device spend.
- Require procurement to present FX‑risk mitigation options for all USD/EUR‑priced contracts.
- Approve a DaaS pilot budget for a portion of the fleet to test Opex vs CapEx scenarios.
- CIO / FinOps (30–60 days)
- Deploy a FinOps tool or expand cloud cost automation policies; target 10–20% quick wins via scheduling and rightsizing.
- Pause discretionary, long‑term licensing or hardware commitments until modelled with currency and energy inputs.
- Audit credit card and expense systems for AI tool purchases; centralise and consolidate as priority.
- IT Ops / Security (60–90 days)
- Map endpoints still on Windows 10; decommission high‑risk devices or enroll in ESU only as a last resort for tightly identified exceptions.
- Implement approved AI catalogue and block public GenAI endpoints from corporate networks until governance is in place.
- Model hosting decisions using PUE, resilience, and generator fuel assumptions in your TCO.
Final assessment and the stakes for 2026
The choices CIOs and finance leaders make now are determinative: small line‑item leaks compound into large P&L hits over months, not years. The five levers described here are not theoretical blueprints — they are operational, evidence‑backed actions that numerous enterprises and vendors are already recommending and implementing. FinOps automation and cloud cost governance recover predictable spend; moving hardware procurement off CapEx spikes via Device‑as‑a‑Service smooths cashflow and improves lifecycle accountability; currency clauses protect balance sheets from external shocks; systematic energy accounting changes the calculus for on‑premise vs cloud; and consolidating shadow AI eliminates both cost and data leakage.Boards should require concrete milestones (30‑, 60‑, 90‑day) and measurable KPIs: % cloud spend reclaimed, number of devices moved to DaaS, FX exposure reduced, energy cost delta modelled, and shadow AI subscriptions consolidated. These metrics convert good intention into stewardship.
The era of “growth at all costs” is over. The real discipline for 2026 will be economical engineering — not austerity for its own sake, but ruthless prioritisation of where technology delivers measurable business value. Execute the five fixes above, measure the results, and treat tech spend as a controllable instrument of resilience rather than an open tap on the balance sheet.
Conclusion: protect the balance sheet by making tech spending accountable, automated, and auditable. The savings and reduced risk you achieve will be paid out not in press releases, but in operating margin — the currency that boards understand best.
Source: IOL Protecting the 2026 balance sheet: five ways to fix your tech spend