FreeBSD 15.0-RELEASE is a watershed update: it trims long‑standing 32‑bit support, introduces a componentized base system install via pkgbase, and hardens the build and release pipeline with reproducible, no‑root image builds — changes that reshape how the OS is built, packaged, and deployed for both servers and desktops.
FreeBSD has long been organized as a single, integrated base system: kernel and userland developed together, released as coordinated distribution sets, and updated with separate tooling from the ports/packages ecosystem. That model has delivered tight integration and predictable upgrades, but it also imposes rigidity: base components are distributed as monolithic sets (base.txz, kernel.txz) requiring a different update mechanism than third‑party packages. FreeBSD 15 begins a deliberate transition away from that model toward a package‑first base, while simultaneously aligning release engineering practices with modern supply‑chain expectations. This article examines the technical specifics of the 15.0 release, verifies key claims against project documentation and independent commentary, and evaluates the practical implications for sysadmins, embedded maintainers, desktop users, and vendors. Where claims cannot be verified or remain community‑contested, they are flagged and discussed.
At the same time, the transition brings operational friction: embedded and legacy users must plan migrations; administrators must learn pkgbase workflows and conversion safety; and the ecosystem must keep aligning ports, kernel modules, and driver stacks with the new baseline. Organizations should treat 15.0 as an opportunity to modernize their FreeBSD deployments, but do so using staged testing, rebuilds of critical artifacts, and careful migration plans.
FreeBSD 15.0 is not merely a maintenance update; it is a structural step toward a more modular, auditable, and cloud‑ready operating system — one that honors FreeBSD’s traditional strengths while acknowledging the realities of modern infrastructure.
Source: theregister.com FreeBSD 15 trims legacy fat and revamps how OS is built
 Background
Background
FreeBSD has long been organized as a single, integrated base system: kernel and userland developed together, released as coordinated distribution sets, and updated with separate tooling from the ports/packages ecosystem. That model has delivered tight integration and predictable upgrades, but it also imposes rigidity: base components are distributed as monolithic sets (base.txz, kernel.txz) requiring a different update mechanism than third‑party packages. FreeBSD 15 begins a deliberate transition away from that model toward a package‑first base, while simultaneously aligning release engineering practices with modern supply‑chain expectations. This article examines the technical specifics of the 15.0 release, verifies key claims against project documentation and independent commentary, and evaluates the practical implications for sysadmins, embedded maintainers, desktop users, and vendors. Where claims cannot be verified or remain community‑contested, they are flagged and discussed.Overview of the headline changes
- 32‑bit platform retirement: i386, armv6 and 32‑bit PowerPC kernels/builds have been retired as first‑class targets; 32‑bit compatibility is maintained via 32‑bit userland compatibility on 64‑bit hosts, while armv7 remains the last supported 32‑bit architecture for this cycle.
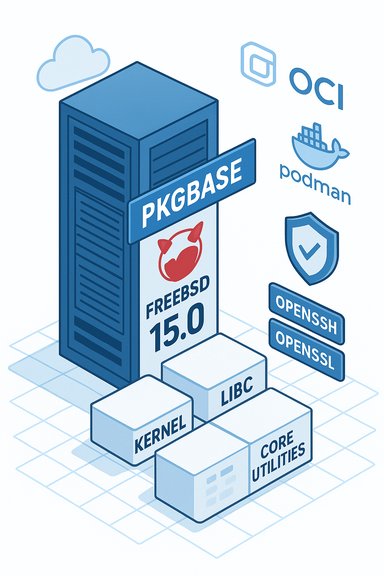
- Packaged base system (pkgbase): the base OS can be installed and managed entirely with pkg(8), enabling updates of kernel and core userland from the package manager, and offering the option to build and install a componentized system rather than monolithic distribution sets. The installer supports installing a pkgbase system and offline pkgbase images are available for installation media.
- Reproducible and no‑root release builds: the release artifacts (ISOs, VM images) were generated without requiring root privileges, and reproducible build guarantees were advanced to reduce supply‑chain risk. These steps aim to improve verifiability of release binaries and lower the blast radius of build‑time threats.
- Security and cryptography upgrades: OpenZFS upgraded to 2.4.0‑rc4, OpenSSL moved to 3.5.4 (with support for new quantum‑resistant algorithms), and OpenSSH updated to 10.0p2 with quantum‑resistant key agreement support.
- Developer and runtime compatibility features: a native inotify(2) API compatible with Linux semantics was added, improving portability for tools that watch filesystem events. OCI container support and a maturing Podman/tooling story make FreeBSD a viable target for cloud‑native deployments.
Why retire 32‑bit platforms now?
The technical and maintenance case
FreeBSD’s move to retire legacy 32‑bit kernels and builds (i386, armv6, 32‑bit PowerPC) reflects a long‑running, pragmatic evaluation of developer resources, hardware footprint, and real‑world deployment patterns. The FreeBSD project made the deprecation plan public, citing limited maintainer interest and the burden of keeping legacy targets buildable and tested as core reasons for removal. The decision leaves armv7 as the last supported 32‑bit platform for the 15.x window, while 64‑bit hosts retain the ability to run 32‑bit binaries via compatibility layers. This is not abrupt: the roadmap and mailing‑list discussion show the team staged the changes (kernel configs disabled for some targets, release images stopped for others) to reduce surprises for downstream users. But the practical upshot is clear: organizations running production fleets on 32‑bit builds must plan migration, and hobbyists with vintage hardware will need to keep older branches or community forks alive.Impact and mitigation
- For servers and cloud images, the move simplifies testing matrices and allows the project to focus QA on the architectures that matter most for modern deployments.
- Embedded users and operators of long‑lived hardware must either:
- Remain on FreeBSD 14.x or 13.x LTS branches; or
- Migrate hardware to 64‑bit platforms (amd64 or aarch64) where possible; or
- Maintain local forks/backports for device‑specific support.
The pkgbase story — packaging the base system
What changes and why it matters
Historically, FreeBSD distributed the OS as a set of distribution tarballs which the installer would unpack. Starting with experimental packages in 14.x, FreeBSD 15 formalizes the pkgbase approach: the base system (kernel, libc, core utilities) can be distributed, installed, and updated as binary packages via pkg(8). The installer (bsdinstall) now offers a dialog to select a pkgbase installation, and offline pkgbase package sets were prepared so installations can proceed without internet access. The Handbook and status reports document conversion tools such as pkgbasify to transform monolithic installs to pkgbase. Why this matters:- Single‑tool patching: kernel and userland can be updated through pkg, enabling a unified package‑driven update workflow rather than separate freebsd-update steps and pkg updates.
- Smaller, more modular installs: components previously locked into the base image can now be omitted or replaced, enabling leaner server or embedded images.
- Automation and CI friendliness: packages are far easier to manage in automated build pipelines and reproducible packaging workflows.
Migration path and operational notes
Converting an existing host is supported via the pkgbasify tool (Handbook guidance warns about temporary additional disk requirements). The project intends to phase out the legacy distribution sets and freebsd-update over the 15→16 timeframe, with pkgbase becoming the default installation and update mechanism for the base system. Administrators will need to test conversion in isolated environments before rolling it out widely.Reproducible builds and no‑root release artifacts: new release engineering
The FreeBSD 15 release engineering emphasized supply‑chain protections. Two interlinked initiatives stand out:- Reproducible builds: deterministic compilation of release artifacts such that identical sources and build inputs produce bit‑identical binaries across independent build hosts. This is a modern countermeasure against tampering and accidental build divergence.
- No‑root release builds: building release images without root privileges reduces the risk of elevated privilege compromises in the release pipeline.
Security and cryptography — quantum‑aware upgrades
FreeBSD 15 ships with up‑to‑date crypto stacks:- OpenSSL 3.5.4 (LTS point release) and OpenSSH 10.0p2 were included in the base. The announcement highlights experimental support for quantum‑resistant algorithms (e.g., ML‑KEM, ML‑DSA, SLH‑DSA) and default quantum‑resistant key agreement in OpenSSH. Meanwhile, OpenZFS was advanced to 2.4.0‑rc4.
- Systems exposing SSH and TLS endpoints will benefit from newer algorithms and fixed CVEs present in the upgraded libraries.
- Enterprises with compliance requirements will welcome the documented shift toward algorithm agility; however, the deployment of quantum‑resistant algorithms in production should be treated as experimental and carefully tested for interoperability. The project’s release notes and announcements make clear these are newly included options, not default replacements for established schemes.
Containers, cloud, and the modern runtime story
FreeBSD’s integration into the OCI ecosystem has been steadily improving, and 15.0 benefits from that momentum. The FreeBSD Foundation and project teams have worked to bring Podman/buildah/ocijail support to the platform, and the OCI runtime specification added FreeBSD as a supported platform in the v1.3 spec — a milestone that recognizes FreeBSD as a viable host/target for OCI‑format images. The project also publishes official OCI images for FreeBSD. Practical implications:- Podman and the Podman toolchain run on FreeBSD; Linux containers can run when the Linux compatibility layer is enabled, and ocijail/containers support maps containers to jails or bhyve VMs depending on the requested OS.
- For organizations standardizing on OCI images and orchestration, FreeBSD is increasingly a first‑class platform. That said, the breadth of Linux‑native containers and some kernel features still favor Linux hosts in complex orchestration scenarios; FreeBSD’s path uses different kernel primitives (jails and bhyve) and occasionally requires configuration adjustments.
Desktop and developer experience: inotify, desktops, and ports
FreeBSD 15’s native inotify(2) implementation improves portability of Linux‑centric tools that rely on filesystem event notifications (development servers, hot‑reload cycles, file indexers, malware scanners). The inotify man page documents the interface and notes compatibility caveats; this lowers friction for developers porting Linux tools to FreeBSD or running them in Linux compatibility environments. On the desktop front, FreeBSD’s installer continues to provide a rich set of desktop environment choices through ports and packages. Community reporting and hands‑on testing highlight that desktop‑installer scripts and the Lumina desktop remain available and that FreeBSD 15 works well in virtualized setups with guest additions detected. However, FreeBSD’s application ecosystem still lacks several commercial, closed‑source desktop apps and Electron‑based tooling common on Linux (for example, native VS Code and many proprietary clients). This remains a trade‑off between minimalism and broad user‑space compatibility.Strengths: what FreeBSD 15 delivers well
- System coherence and provenance: shifting the base to packages retains FreeBSD’s integrated userland while enabling the package manager to manage the OS itself, improving traceability and reproducibility.
- Improved supply‑chain posture: reproducible builds and no‑root image generation materially reduce risk and enable independent reproduction of release artifacts.
- Container and cloud readiness: official OCI support, Podman tooling, and cloud image improvements make FreeBSD a more practical choice for cloud and edge deployments.
- Security‑minded crypto updates: the inclusion of modern OpenSSL/OpenSSH releases and experimentation with quantum‑resistant algorithms positions FreeBSD for future cryptographic transitions.
Risks, trade‑offs, and unanswered questions
- Migration cost for 32‑bit users: retired 32‑bit targets shift the maintenance burden to users and vendors who still rely on those platforms. While compatibility modes exist, embedded deployments tied to 32‑bit hardware face non‑trivial migration paths.
- pkgbase growing pains: converting the base to packages is powerful but introduces operational risks — misusing pkg commands (for example, bulk package deletes without understanding the base vs. packages distinction) can produce catastrophic system states. Community discussion has flagged incidents where historic pkg behavior was insufficiently cautious; administrators must learn new patterns and test conversion thoroughly. This is an area where clear documentation, safe‑guards, and default installer behavior will be critical.
- Ecosystem parity with Linux: despite OCI support and better container tooling, the breadth and freshness of device drivers, GPU stacks, and some userland apps still lag Linux. Projects requiring the very latest proprietary GPU drivers or anti‑cheat kernels for gaming are more likely to remain Linux‑first.
- Reproducibility completeness: while core artifacts show reproducibility improvements, reproducing complex third‑party ports or vendor kernel modules across different infrastructures may still fail. Ongoing community investment is required to extend reproducibility guarantees across all release artifacts.
Practical advice for administrators and hobbyists
- Inventory and plan: identify any production systems running 32‑bit targets and decide whether to remain on 14.x/13.x, migrate to 64‑bit hardware, or maintain custom backports.
- Test pkgbase conversion: use the pkgbasify tool in a lab, verify a full rollback strategy, and ensure adequate free disk space during conversion. Read the Handbook guidance before converting production hosts.
- Validate reproducible builds: if your CI/attestation workflows matter, attempt to reproduce the release images in your pipeline and compare checksums.
- Rebuild critical packages: rebuild and test important ports and kmod packages against 15.0 to catch ABI and dependency regressions early.
- Container and cloud testing: exercise the new OCI images and Podman tooling in staging before adopting in production; test Linux container compatibility scenarios if you rely on Linux‑only images.
Conclusion — an evolutionary, not revolutionary, moment
FreeBSD 15.0 is a carefully engineered release that modernizes both the way the OS is built and the way it is delivered. By trimming legacy 32‑bit platform support, adopting a package‑driven base system, and improving supply‑chain assurances with reproducible and no‑root builds, the project reduces developer overhead and raises the bar for verifiable releases. Those changes make FreeBSD a stronger candidate for cloud deployments, modern container workflows, and environments that value deterministic build artifacts.At the same time, the transition brings operational friction: embedded and legacy users must plan migrations; administrators must learn pkgbase workflows and conversion safety; and the ecosystem must keep aligning ports, kernel modules, and driver stacks with the new baseline. Organizations should treat 15.0 as an opportunity to modernize their FreeBSD deployments, but do so using staged testing, rebuilds of critical artifacts, and careful migration plans.
FreeBSD 15.0 is not merely a maintenance update; it is a structural step toward a more modular, auditable, and cloud‑ready operating system — one that honors FreeBSD’s traditional strengths while acknowledging the realities of modern infrastructure.
Source: theregister.com FreeBSD 15 trims legacy fat and revamps how OS is built