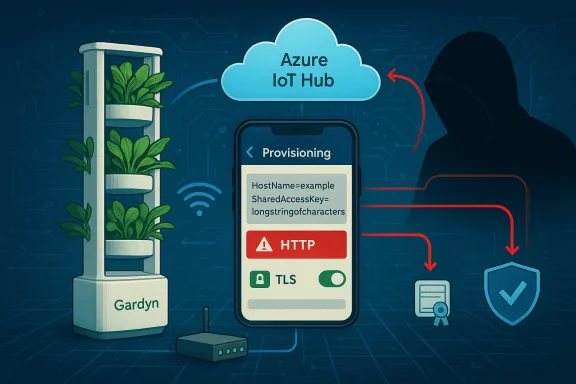
A newly documented vulnerability affecting the Gardyn Home Kit family of smart indoor gardens puts a critical piece of device authentication — the Azure IoT Hub connection string — at risk by delivering it over an insecure HTTP channel, enabling straightforward Man‑in‑the‑Middle (MITM) interception and the potential capture or manipulation of device credentials that can lead to unauthorized control of home kits and associated cloud resources.
Gardyn makes vertically oriented, camera‑equipped hydroponic systems that rely on a companion mobile application and cloud services to manage watering schedules, lighting, camera feeds and the product’s AI gardening assistant. The devices connect to Microsoft Azure IoT Hub for device‑to‑cloud and cloud‑to‑device communication; that integration depends on connection strings and shared access keys that effectively serve as device credentials. Microsoft’s documentation states clearly that a device connection string contains the IoT Hub host name, the device ID and a symmetric key (SharedAccessKey) and that these connection strings are sensitive credentials which must be protected.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) published an Industrial Control Systems advisory describing the Gardyn issue and the vendor’s recommended remediations, noting that the affected connection string was delivered over plain HTTP which exposes it to interception and modification by an on‑path attacker. Gardyn’s public guidance — repeated in that advisory — points users to update the Gardyn mobile application and ensure devices are running firmware master.619 or later to receive the vendor fixes. The vendor also directs customers to their support channels for assistance. (Vendor text and advisory excerpts were supplied with the advisory notification.)
Why this matters: Azure IoT Hub shared access policies and device connection strings grant scoped permissions — in some cases broad, hub‑level capabilities — and any secret that enables the creation of valid SAS tokens or direct service calls must be treated as highly sensitive. A stolen connection string can be used to generate tokens that let an attacker send cloud‑to‑device commands, receive or tamper with device messages, or in some configurations register or manage devices.
Gardyn’s published help and privacy pages document their support paths and product pages; the vendor also directs customers to their security information pages and support email for additional questions.
Caveat: the precise CVE assignment and scoring may be updated after public disclosure and vendor patches; always consult the official advisory entries for the authoritative identifier and timeline.
In short: this is a high‑impact, preventable class of vulnerability caused by insecure handling of secrets during provisioning. Gardyn owners should update immediately, assume earlier secrets might have been exposed, and follow up with the vendor for credential rotation and confirmation that provisioning channels now fully enforce TLS and best‑practice authentication. For vendors and device developers, the incident reinforces fundamental rules: never ship secrets over HTTP, prefer short‑lived or certificate‑based credentials, and bake secure provisioning and update paths into the product from day one.
Source: CISA Gardyn Home Kit | CISA
 Background
Background
Gardyn makes vertically oriented, camera‑equipped hydroponic systems that rely on a companion mobile application and cloud services to manage watering schedules, lighting, camera feeds and the product’s AI gardening assistant. The devices connect to Microsoft Azure IoT Hub for device‑to‑cloud and cloud‑to‑device communication; that integration depends on connection strings and shared access keys that effectively serve as device credentials. Microsoft’s documentation states clearly that a device connection string contains the IoT Hub host name, the device ID and a symmetric key (SharedAccessKey) and that these connection strings are sensitive credentials which must be protected.The U.S. Cybersecurity and Infrastructure Security Agency (CISA) published an Industrial Control Systems advisory describing the Gardyn issue and the vendor’s recommended remediations, noting that the affected connection string was delivered over plain HTTP which exposes it to interception and modification by an on‑path attacker. Gardyn’s public guidance — repeated in that advisory — points users to update the Gardyn mobile application and ensure devices are running firmware master.619 or later to receive the vendor fixes. The vendor also directs customers to their support channels for assistance. (Vendor text and advisory excerpts were supplied with the advisory notification.)
Why this matters: Azure IoT Hub shared access policies and device connection strings grant scoped permissions — in some cases broad, hub‑level capabilities — and any secret that enables the creation of valid SAS tokens or direct service calls must be treated as highly sensitive. A stolen connection string can be used to generate tokens that let an attacker send cloud‑to‑device commands, receive or tamper with device messages, or in some configurations register or manage devices.
What the vulnerability actually is — technical anatomy
The core weakness
At the center of the problem is insecure transport of a secret: the Gardyn mobile application (and/or associated device provisioning flow) obtains an Azure IoT Hub connection string from Gardyn’s cloud back end using an unencrypted HTTP request. Because that request is not protected by TLS, anyone who can intercept or modify traffic between the app/device and the vendor’s server can:- Read the full connection string (HostName, DeviceId, SharedAccessKey).
- Modify the payload to inject a malicious connection string or configuration.
- Return corrupted data that causes devices to misconfigure or reveal further secrets.
Attack chains and realistic scenarios
- Local MITM on a home network: an attacker sets up a rogue Wi‑Fi hotspot or abuses an untrusted guest network. A Gardyn app or device provisioning attempt runs over that network and requests the connection string. The attacker harvests the key and later connects to the IoT Hub or crafts tokens to impersonate the device.
- Compromised router / ISP interception: some home routers allow interception of HTTP traffic for ad injection or captive portals. If a router is compromised or misconfigured, the connection string can be intercepted without the user’s knowledge.
- Active payload replacement: because the attacker can modify the HTTP response, they could replace a legitimate connection string with one that points devices to a malicious service or to a differently provisioned device identity. That allows command injection or remote re‑provisioning.
- Supply‑chain extension: if an attacker can scale interception (for example by compromising an update server or a CDN misconfiguration), they might affect multiple devices at once.
Why this is high‑impact for Gardyn owners and cloud tenants
- Secrets = keys to the kingdom. Azure IoT Hub connection strings often include symmetric keys that can be used to generate SAS tokens. SAS tokens with ServiceConnect or RegistryReadWrite scope permit device management actions and cloud‑initiated commands. Microsoft’s security guidance stresses that shared access keys are sensitive and that token scopes matter. An exposed connection string can allow an attacker to impersonate devices, send unauthorized commands, or enumerate and manage device identities.
- Physical safety and privacy. Gardyn devices include cameras and controls for pumps and lights. Unauthorized control could allow an attacker to disable watering (leading to drowned/dying plants), enable continuous lighting, or access camera feeds — creating both physical damage risks and privacy violations.
- Lateral risk to cloud infrastructure. If a captured string grants high privileges (hub‑level), attackers can read telemetry, inject malicious configuration across many devices, or use the IoT Hub as a pivot point to target backend systems that consume device data.
- Scale: consumer IoT deployed in homes. Consumers often place many connected devices on the same home network, and owners rarely run segmented networks for IoT. That makes opportunistic interception (rogue Wi‑Fi, malicious coffee‑shop hotspot) a practical attack vector.
What Gardyn says and the vendor response
Gardyn’s remediation guidance — included in the advisory material and on their support touchpoints — recommends:- Update the Gardyn mobile application to the latest supported version (the vendor states fixes are bundled into the most recent app release).
- Ensure home kit devices are upgraded to firmware master.619 or later; the vendor says devices with network connectivity will auto‑download firmware updates.
- Confirm devices have internet connectivity so automatic updates can apply; unconnected devices will update once put online.
- Use the Gardyn app to check current app and firmware versions and contact Gardyn support (support@mygardyn.com) for help.
Gardyn’s published help and privacy pages document their support paths and product pages; the vendor also directs customers to their security information pages and support email for additional questions.
Independent verification and CVE tracking (what we can confirm)
At the time this article was prepared, independent vulnerability aggregators and CERTs have begun to catalogue Gardyn‑related issues: one tracker referenced a Gardyn CVE recorded in late February 2026 that links to the same advisory themes (delivery of secrets over HTTP and subsequent vendor remediation guidance), while other vulnerability trackers and national CERT postings have documented related Gardyn CVE entries from 2025 that describe different but related issues in the Gardyn software stack. These tracker listings corroborate that multiple Gardyn security advisories have appeared over the last year and that the vendor has been issuing firmware and app updates in response. Readers should note the specific CVE identifiers and technical details may differ between advisories; confirm the exact CVE number for your device generation before acting.Caveat: the precise CVE assignment and scoring may be updated after public disclosure and vendor patches; always consult the official advisory entries for the authoritative identifier and timeline.
Practical remediation checklist for Gardyn owners (step‑by‑step)
If you own a Gardyn Home Kit, follow these prioritized actions immediately:- Update the Gardyn mobile app right now. Use your platform’s official app store and verify the app version is the vendor’s current release. Gardyn says fixes are included in the most recent mobile app; install updates before pairing or provisioning devices on untrusted networks.
- Ensure your Gardyn device firmware is master.619 or later. In the Gardyn app, check the device firmware version and force an update if the device is online. If your device is offline, connect it to a trusted, private network temporarily to allow the update to download and apply. Gardyn’s guidance calls out master.619 specifically as the minimum patched firmware.
- Assume any earlier cleartext secret was exposed — rotate keys. After applying updates, perform a credential rotation:
- If you control the IoT Hub (unlikely for consumer devices), revoke and regenerate shared access keys and update devices to use new credentials.
- If you are a consumer with only a Gardyn device and no direct IoT Hub access, contact Gardyn support and request confirmation that the cloud‑side keys used for your device were rotated and that your device’s identity was re‑provisioned safely.
- Check for unexpected device behavior or cloud activity. Look for:
- Unexpected watering, lighting changes, or camera access.
- Notifications from the app showing re‑provisioning or device resets.
- If Gardyn offers a log or activity history in the app, review it for anomalies.
- Use segmented Wi‑Fi for IoT. Place your Gardyn on a guest or IoT VLAN isolated from your primary work and personal devices. Reduce exposure to lateral compromise if another device is breached.
- Avoid using public or untrusted Wi‑Fi for setup or provisioning. Configure devices only on private, trusted home networks with WPA2/WPA3 and a strong unique password.
- Contact Gardyn support for confirmation and assistance. Use the vendor support channel to verify your unit’s status and request guidance on credential rotation, device re‑provisioning, or a replacement if you suspect compromise.
Recommended actions for IT‑savvy owners and integrators
If you’re comfortable with more advanced steps or you run multiple devices, consider:- Requesting proof of remediation from the vendor. Ask Gardyn whether the specific provisioning endpoint was hardened (moved to HTTPS), whether they adopted TLS enforcement and HSTS, and whether they rotate hub‑level shared access keys during the update rollout.
- Detecting MITM attempts on your network. Use an IDS that monitors for TLS stripping, HTTP-to-HTTPS downgrades, or suspicious ARP activity. Inspect logs for unexpected connection string retrieval attempts.
- Monitoring cloud logs. If you have access to the backend IoT Hub telemetry or otherwise receive Gardyn developer support for enterprise deployments, look for unfamiliar SAS token usage, device re‑registrations, or unusual cloud‑to‑device commands. Microsoft’s documentation shows how ServiceConnect and RegistryWrite permissions allow broad actions; monitoring those endpoints is critical.
- Move to certificate‑based authentication where possible. Symmetric keys are easier to leak. Microsoft recommends X.509 certificates or Microsoft Entra‑based identity for stronger, auditable authentication models for IoT devices. If Gardyn offers device certificate provisioning in future updates, prefer that over long‑lived symmetric keys.
Developer‑level remediation and secure design lessons
For Gardyn and for any IoT vendor, this vulnerability illustrates multiple, well‑known secure‑development principles that must be enforced:- Never transmit secrets over HTTP. All endpoints that return credentials must use TLS (HTTPS) with strict transport security (HSTS) and server‑side enforcement.
- Avoid bundling long‑lived secrets in application logic. Use short‑lived tokens, token services, and per‑device credentials. Microsoft’s token service pattern and the use of SAS tokens with short expirations are relevant mitigations.
- Use certificate validation / pinning for client apps where feasible. Mobile apps that provision devices should validate the server TLS certificate chain and, where appropriate, implement certificate pinning to reduce the risk of trusted CA‑based interceptors. Implementations and pitfalls of SSL/TLS pinning and certificate thumbprint checks are a known defensive pattern.
- Log and rotate credentials after incident or patch. Apply immediate rotation of any credentials that may have been exposed, and design update flows to support automated and verifiable key revocation.
- Segment configuration and provisioning APIs. Separate the provisioning channel from day‑to‑day operational channels and limit the scope of any credentials returned during provisioning.
- Use managed identity where possible. Replace shared keys with more granular, tokenized auth (for example, Microsoft Entra tokens for services) to reduce the blast radius of a leaked key.
Detection and forensic guidance for suspected compromises
If you suspect your Gardyn device or account was compromised before you applied the fix:- Preserve logs: do not factory reset the device until you have captured whatever logs, screenshots or app histories are available; these may aid vendor triage.
- Note timeframes: document when you first connected the device, when the app downloaded the connection string (if visible), and when you update the app and firmware.
- Watch cloud activity: ask Gardyn support whether they can provide device activity logs — look for unusual commands or remote re‑provisioning.
- Rotate credentials: insist on a credential rotation on vendor side even if you have updated the firmware. A software update prevents future leakage but does not revoke previously leaked secrets.
Wider implications: consumer IoT, trust, and responsible disclosure
This vulnerability is another reminder that consumer IoT devices are only as secure as their provisioning and update mechanisms. Many manufacturers focus on the user experience for device onboarding (fast, seamless setup) but inadvertently trade away critical security controls by using insecure transport or leaving secrets exposed. For vendors:- Rapid, security‑first release cycles are essential.
- Public, verifiable disclosures and patch timelines build user trust.
- Independent security audits and bug bounty programs help find issues before widespread consumer exposure.
- Treat device provisioning and first‑time setup as high‑risk operations. Use trusted networks and apply updates before you allow a device to manage critical functions in your home.
- Demand transparency and concrete mitigation steps from vendors when security advisories are issued.
Final assessment and recommended priorities
- Severity: High for exposed devices. The delivery of Azure IoT Hub connection strings over HTTP substantially increases the risk of credential theft and device takeover, because the strings permit token generation and device impersonation. The precise impact on any single user depends on the privileges tied to the leaked string (per‑device vs hub‑level), but the potential for privacy invasion and device control is clear.
- Vendor response: Gardyn’s immediate guidance to push fixes through the mobile app and to require firmware master.619 or later is appropriate as a rapid mitigation; however, credential rotation and clear proof that the provisioning endpoint now enforces TLS and rejects non‑TLS requests must follow. Users should demand confirmation of those steps if they suspect prior exposure.
- User action: Update the app, ensure firmware master.619+, connect devices only to trusted networks, rotate or request rotation of credentials, and monitor for anomalous device/camera behavior. If you are an enterprise or manage multiple deployments, perform a forensic review and consider segmenting IoT networks immediately.
In short: this is a high‑impact, preventable class of vulnerability caused by insecure handling of secrets during provisioning. Gardyn owners should update immediately, assume earlier secrets might have been exposed, and follow up with the vendor for credential rotation and confirmation that provisioning channels now fully enforce TLS and best‑practice authentication. For vendors and device developers, the incident reinforces fundamental rules: never ship secrets over HTTP, prefer short‑lived or certificate‑based credentials, and bake secure provisioning and update paths into the product from day one.
Source: CISA Gardyn Home Kit | CISA