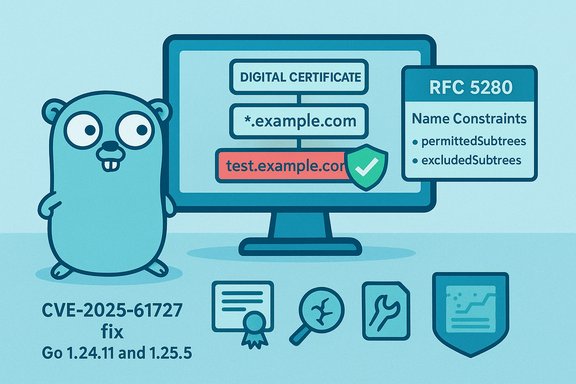
An important validation bug has been published against the Go standard library’s certificate-handling code: CVE-2025-61727 describes an improper application of excluded DNS name constraints when verifying wildcard names in crypto/x509, meaning that an excluded-subdomain constraint in a certificate chain can fail to stop a leaf certificate from using a wildcard Subject Alternative Name (SAN) such as *.example.com. In short, a certificate chain that intends to exclude test.example.com from being matched can still be bypassed if the leaf presents a wildcard SAN that covers that subdomain. This is a library-level certificate validation vulnerability that affects the Go standard library’s crypto/x509 prior to the fixes released in Go 1.24.11 and Go 1.25.5.
Name constraints are a critical X.509/X.509v3 extension used by certificate authorities and intermediate CAs to limit the namespace a subordinate CA or certificate may certify for. Two complementary fields are defined in RFC 5280: permittedSubtrees (what the subject is allowed to issue) and excludedSubtrees (what the subject is forbidden from issuing). These rules apply to subject names and SAN entries and are enforced by certificate path validation routines to prevent subordinate CAs from issuing certificates for names outside their allowed namespace — or to explicitly forbid issuance for certain subdomains. In correctly implemented validators, an excluded-subtree entry for test.example.com must prevent any downstream certificate from asserting a name that would match test.example.com, including names covered by wildcards. Wildcard SAN semantics are subtle and historically a common source of implementation mistakes. A wildcard like .example.com is intended to match host.example.com and test.example.com, but RFCs require that validators correctly interpret label boundaries and name-constraint semantics when comparing names to constraints. If a validator applies excludedSubtrees to literal names but fails* to apply the same logic to wildcard SANs, a leaf certificate can effectively get around an exclusion by presenting a wildcard that covers the excluded name. That is exactly the behavioral mismatch recorded in CVE-2025-61727.
The fix is available in the Go releases noted above; organizations must rebuild and redeploy compiled artifacts to be secure. Prioritize remediation for services that perform certificate-based authentication, mutual TLS, and any deployment that relies on internal PKI boundaries or subordinate CA policies. Finally, treat this case as a reminder: certificate validation and PKI are brittle and require both correct implementations and disciplined issuance policies to provide dependable trust assurances.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Name constraints are a critical X.509/X.509v3 extension used by certificate authorities and intermediate CAs to limit the namespace a subordinate CA or certificate may certify for. Two complementary fields are defined in RFC 5280: permittedSubtrees (what the subject is allowed to issue) and excludedSubtrees (what the subject is forbidden from issuing). These rules apply to subject names and SAN entries and are enforced by certificate path validation routines to prevent subordinate CAs from issuing certificates for names outside their allowed namespace — or to explicitly forbid issuance for certain subdomains. In correctly implemented validators, an excluded-subtree entry for test.example.com must prevent any downstream certificate from asserting a name that would match test.example.com, including names covered by wildcards. Wildcard SAN semantics are subtle and historically a common source of implementation mistakes. A wildcard like .example.com is intended to match host.example.com and test.example.com, but RFCs require that validators correctly interpret label boundaries and name-constraint semantics when comparing names to constraints. If a validator applies excludedSubtrees to literal names but fails* to apply the same logic to wildcard SANs, a leaf certificate can effectively get around an exclusion by presenting a wildcard that covers the excluded name. That is exactly the behavioral mismatch recorded in CVE-2025-61727. What the vulnerability actually is
Technical summary
- The vulnerability is an improper certificate validation bug in the Go standard library implementation of crypto/x509.
- Specifically, an excluded subdomain constraint in the certificate chain does not prevent a leaf certificate from claiming a wildcard SAN that would match that excluded subdomain (e.g., excluded: test.example.com; leaf SAN: *.example.com).
Where it lives and how it shows up
- The problem is in the implementation of Certificate.Verify and associated name-constraint checks inside crypto/x509.
- A validator should refuse a leaf certificate whose SANs match any excluded subtree; in this case it did not properly apply the excluded-subtree rule to wildcard SAN entries. The Go project tracked this as GO-2025-4175 and published the CVE record.
A concrete illustration (conceptual)
- An intermediate CA issues an intermediate certificate to a subordinate with a name-constraint that includes an excluded subtree: test.example.com.
- The subordinate issues a leaf certificate containing the SAN *.example.com.
- A correctly-implemented validator should reject the leaf for matching an excluded name (test.example.com) — the wildcard should not defeat the exclusion.
- With the bug present, Go’s crypto/x509 could fail to treat the wildcard SAN as matching the excluded name, allowing validation to succeed when it should not.
Affected versions, fixes and vendor guidance
- Affected component: Go standard library — crypto/x509.
- Affected releases: versions of Go before go1.24.11 and in the 1.25 series before go1.25.5. The Go project released fixes as part of the Go 1.24.11 and Go 1.25.5 point releases.
- Fix summary: upstream changes apply stricter name-constraint verification so excluded subtrees are correctly enforced against wildcard SANs, preventing wildcard SANs in leaves from matching excluded names. The change was included in the Go point releases announced by the project.
- Upgrade Go toolchain and rebuild any binaries compiled with affected toolchains: move to Go 1.24.11 or Go 1.25.5 (or later). Static or statically built binaries that were compiled with a vulnerable stdlib must be recompiled with an updated toolchain to remove the vulnerable logic.
- If you rely on third-party binaries or vendor-supplied appliances that embed Go, contact vendors to verify build-time toolchain versions or obtain patched builds. Do not assume a host is fixed just because upstream sources are patched — rebuild / redeploy is required for compiled artifacts.
Exploitability, attacker model and practical risk
What an attacker needs
- To benefit directly from this bug, an attacker must obtain or cause a leaf certificate to be issued that includes a wildcard SAN covering an excluded name, or otherwise control a CA or signing process in a trust chain that contains an excluded-subdomain constraint. In practice that means:
- either a subordinate CA or internal CA that can be coerced into issuing a wildcard that should be disallowed, or
- a misconfigured or malicious CA that issues certs outside its permitted namespace.
Realistic scenarios
- Public CAs are generally constrained by strict issuance policies and auditing (Certificate Transparency, CA/Browser Forum rules), so practical risk from a public-CA misissuance is lower but not impossible — history shows CAs can and do make mistakes.
- The higher-risk, realistic scenario is internal PKI and delegated CAs inside organizations: an internal CA or subordinate may have been given constrained scope but still be able to issue wildcard SANs. If such a subordinate is allowed to issue *.example.com while an excluded constraint existed for a sensitive label, an attacker with access to that subordinate could produce a certificate that bypasses the intended exclusion in Go-based validators.
Exploitability rating and public PoC
- Public tracking entries and the NVD list the vulnerability and its technical description, but as of publication there are no widely reported, confirmed public proof-of-concept exploits specifically weaponizing CVE-2025-61727. That absence does not mean no one can weaponize it; it means public telemetry has not shown broad exploitation. Treat the lack of PoC as absence of public proof rather than evidence of safety.
Scoring and impact
- The advisory record and vendor metadata associate the issue with improper certificate validation (CWE-295). The CISA-ADP enrichment attached a CVSSv3.1 vector of AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:N with a base score of 6.5 (Medium), reflecting a network vector with low complexity but limited impact unless a certificate trusted path can be abused. NVD’s listing is consistent with the Go project’s publication and references the Go CL and issue for details.
Operational impact and who should care most
This vulnerability is primarily relevant to:- Developers who build network services, TLS clients, or mutual-TLS endpoints using Go’s standard library (crypto/x509).
- DevOps and SRE teams that deploy statically compiled Go binaries into production, especially those that handle certificate-based authentication, mTLS, or that perform certificate validation on externally-provided certificates.
- Organizations running internal PKI or delegated subordinate CAs where name-constraint semantics were relied upon as part of a trust model.
- Vendors who ship appliances, SDKs, or agents compiled with vulnerable Go toolchains (they must recompile and ship updates).
- Go is not a Linux-only runtime — Go programs and agents are widely used on Windows servers, developer tools, CI/CD agents, network appliances, and cloud-native workloads that operate on Windows. If you run services that perform certificate verification using Go-built components, they may be affected. Recompilation and redeployment are required to fully remediate.
Detection, mitigation, and remediation roadmap
Immediate (0–24 hours)
- Identify Go-built artifacts across your estate:
- Query inventories for Go binaries, container images, installed agents, and vendor packages.
- Search for known Go runtime version strings in binary metadata or Docker layers.
- Prioritize network-facing services and mutual-authentication endpoints for patching.
- Apply the Go project updates:
- Upgrade to Go 1.24.11 or Go 1.25.5 (or later) and rebuild your binaries and container images. Patching the runtime source alone is insufficient for already-compiled artifacts.
Short-term compensating controls (while you patch)
- Restrict which CAs you will accept for critical authentication paths — prefer pinned or known-good CA chains where practical.
- If feasible, place protocol-aware TLS terminators (reverse proxies, load balancers) in front of vulnerable Go services, and let those terminators perform certificate validation using a patched, hardened stack.
- Audit internal CAs and subordinate CA policies to ensure forbidden exclusion constraints are actually enforceable at issuance time; revoke or reissue certificates that violate intended constraints.
- Add monitoring rules for anomalous certificate chains: certificates that contain wildcards covering excluded labels, or certificates announced outside CT logs for public domains.
Long-term fixes (1–4 weeks)
- Rebuild and redeploy all Go binaries compiled with vulnerable stdlib versions.
- For vendor-supplied or third-party appliances, request patched builds or rebuild images if you have the source.
- Harden internal PKI issuance policies to prevent issuance of wildcard SANs that violate organizational constraints; add enforcement in CA issuance workflows.
- Add unit and integration tests that assert name-constraint behavior (including wildcard interactions) to prevent regression.
Detection and forensic guidance
- Hunt for certificates in your trust chains where:
- An intermediate has an excludedSubtree for a specific label but the leaf contains a wildcard that would match it.
- Certificate Transparency (CT) logs show unexpected wildcard issuance for your domains (public CT watchers can help here).
- Monitor TLS logs and mTLS negotiation patterns for unexpected client certificates or sudden shifts in certificate chains.
- For high-assurance deployments, temporarily require clients to present only explicitly enumerated SANs (avoid accepting wildcards) where business constraints allow it.
- Query CT feeds (public and internal mirrors) for wildcard certs matching your domains.
- Scan your fleet for certificate chains that contain name-constraint extensions; flag any that include excludedSubtrees plus downstream wildcard SANs.
- When incident investigating, collect the full certificate chains, PCAPs of TLS handshakes, and any CA issuance logs — these artifacts will show whether a wildcard leaf matched an excluded subtree.
Code-level and developer guidance
- If your code calls crypto/x509.Certificate.Verify or similar path validation APIs, treat the Go runtime version as a dependency that must be patched and rebuilt. Do not assume runtime-level fixes are applied automatically to already-built artifacts.
- Prefer defensive programming patterns:
- Avoid accepting arbitrary certificates from untrusted peers unless strictly necessary.
- Truncate or avoid logging entire certificate fields in high-volume paths — this helps mitigate unrelated DoS/complexity risks.
- Add explicit checks in application logic where certificate validation needs to be stricter than the standard library’s defaults (for example, avoid blanket wildcards for critical services).
- Add test cases simulating excluded-subtree + wildcard combinations to validate both your code and your dependencies’ behavior during CI.
Critical analysis — strengths of the response and remaining risks
What’s good:- The Go project published targeted fixes and bundled them into small point releases (Go 1.24.11 and 1.25.5), enabling straightforward remediation for developers who can rebuild artifacts. Public advisories and vulnerability databases have recorded the CVE and the fixed releases, allowing tracking and coordinated patching.
- Rebuild inertia and supply-chain lag. Because Go binaries are compiled artifacts, simply updating the source code on developer machines is not enough — organizations must rebuild and redeploy production artifacts. Long-lived container images, vendor appliances, and pre-built agents can remain vulnerable until their maintainers or vendors deliver rebuilt artifacts. This is the primary operational friction point for this class of library-level fixes.
- Internal PKI and delegated subordinate CAs remain the highest-risk contexts. If your organization uses internal CA hierarchies or delegates issuance to external parties, the vulnerability increases in practical impact — particularly where wildcard issuance is permissive or poorly constrained.
- Detection blind spots. Without telemetry that specifically flags mismatches between constraints and wildcard SANs, exploitation may be silent and only discovered during audits or after an incident.
- There is no widespread public proof-of-concept demonstrating active exploitation of CVE-2025-61727 at the time of writing; however, lack of a public PoC does not equal lack of private weaponization. Treat public PoC absence cautiously and prioritize patching based on your exposure model.
- Some public vulnerability feeds or vendor pages (including MSRC/Windows Security Update Guide pages) may require full browser rendering and can behave differently for automated crawlers; verify mapping of CVE→product KBs manually when applying Microsoft guidance. If you followed the MSRC link you supplied, be aware some pages require JavaScript to render fully.
Quick operational checklist (prioritized)
- Inventory:
- Find all Go-built binaries, containers, and artifacts across the organization.
- Patch & Rebuild:
- Upgrade the Go toolchain to 1.24.11 or 1.25.5 (or later). Rebuild and redeploy all artifacts.
- Vendor coordination:
- Contact third-party vendors for patch timelines where you cannot rebuild images yourself.
- Short-term controls:
- Limit acceptance of wildcard leaf certificates in critical flows; proxy TLS termination to patched stacks where possible.
- Monitoring:
- Watch CT logs and internal CA issuance logs for unexpected wildcard issuance.
- Hardening:
- Tighten internal CA issuance policies; require stronger policy controls preventing wildcard SAN issuance when excluded constraints exist.
Final takeaways
CVE-2025-61727 is a concrete example of how subtle mismatches between protocol semantics (name constraints) and implementation details (wildcard matching code paths) can break intended security policies. The vulnerability sits at the intersection of CA policy, certificate semantics, and runtime validation logic — a triad that makes such bugs operationally meaningful even if they are not trivially exploitable from the open internet.The fix is available in the Go releases noted above; organizations must rebuild and redeploy compiled artifacts to be secure. Prioritize remediation for services that perform certificate-based authentication, mutual TLS, and any deployment that relies on internal PKI boundaries or subordinate CA policies. Finally, treat this case as a reminder: certificate validation and PKI are brittle and require both correct implementations and disciplined issuance policies to provide dependable trust assurances.
Source: MSRC Security Update Guide - Microsoft Security Response Center