Gravitee’s push to bring traditional API management into the “agentic” era marks a notable inflection point: the infrastructure that once simply routed calls and enforced quotas is now being reshaped to govern conversations between autonomous AI agents, event streams, and enterprise systems—and Microsoft’s Azure partnership puts that evolution squarely in the spotlight.
Background
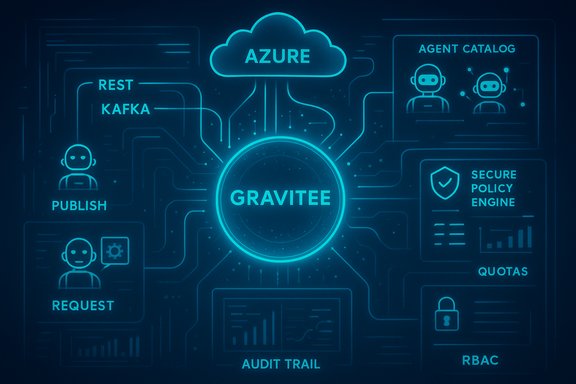
Gravitee has spent the last few years repositioning its API platform around real-time, event-driven architectures and now asserts a broader mission: secure, discoverable, and observable connectivity for APIs, event streams, and AI agents. Recent product advances—Agent Mesh, Kafka/Event gateways, and deeper protocol support for standards like the Model Context Protocol (MCP) and Agent-to-Agent (A2A) communications—signal an intent to make API management the connective tissue of agentic systems. Microsoft’s endorsement and a one‑click Azure Marketplace listing amplify that message for enterprise buyers seeking production-ready paths to deploy and govern agent ecosystems on Azure.This article unpacks what Gravitee’s strategy means in practical terms for IT leaders and architects, examines the security and governance implications of agent-first architectures, and offers a pragmatic checklist for adopting API management at scale in environments populated by autonomous agents.
Overview: Why API management matters for AI agents
AI agents—whether user-facing copilots, background automations, or multi-agent orchestrators—don’t just call APIs; they interpret user intent, plan multi-step workflows, and autonomously decide which services to invoke. That raises three demands on the connectivity layer that differ from classic API management:- Dynamic discovery and tooling: Agents need a catalog and machine-readable descriptions of tools, endpoints, costs, and permissions so they can discover and safely invoke services.
- Fine-grained runtime control: Policies must be able to govern not just per-user calls but per-agent identities, quotas, and contextual constraints.
- Observability and auditability: Chain-of-thought, tool invocations, and cross-agent conversations must be traceable for compliance, debugging, and accountability.
Gravitee’s evolution: from API gateway to agent governance
From REST-first to event-native API management
Gravitee has steadily invested in native support for streaming and event brokers, adding gateways and features designed to treat event streams as first-class APIs. That shift matters because modern enterprises increasingly rely on asynchronous messaging and streaming pipelines; making those streams governable with the same controls as REST endpoints reduces blind spots and governance friction.Key attributes of this evolution include:
- Native Kafka and MQ support so event topics can be exposed and secured without protocol breaks.
- Message-level policies—filtering, transformation, and enrichment—applied in real time.
- Developer portals and catalogs where streaming APIs appear alongside traditional endpoints.
Agent Mesh: a governance layer for agents, LLMs and A2A
The Gravitee Agent Mesh is the company’s most explicit product-level response to agentic architectures. It is positioned to provide:- An Agent Catalog that lets teams publish agent capabilities and understand ownership.
- An Agent Gateway / A2A proxy to control agent-to-agent traffic, enforce quotas, and mediate protocols.
- An Agent Tool Server that turns existing APIs into agent-actionable tools—commonly via MCP—so agents can use enterprise services without bespoke integrations.
Technical context: MCP, A2A and the plumbing of agentic systems
Two complementary protocols have emerged as de facto plumbing for agentic systems: the Model Context Protocol (MCP) and the Agent-to-Agent (A2A) protocol.- Model Context Protocol (MCP) standardizes how models and agents access external tools and data sources. It gives tools a predictable interface—inputs, outputs, and metadata—so an agent can invoke capabilities programmatically without bespoke adapters for every model or tool.
- A2A (Agent-to-Agent) defines a higher-level pattern for agent discovery, task delegation, and multi-agent collaboration. Where MCP is agent→tool, A2A is agent→agent.
Built for Azure: procurement, compliance, and enterprise scale
The practical benefit of a marketplace listing and official partnership with Microsoft is more than branding: for enterprise procurement teams, Azure Marketplace listings simplify procurement, billing, and compliance checks. Deploying Gravitee on Azure also opens architectural choices:- Run control planes in a multi-region Azure environment for regional compliance and low latency.
- Integrate Gravitee’s access management with Azure AD / Entra ID for centralized identity and SSO.
- Leverage Azure-native security controls, policy management, logging, and SIEM integration.
Governance and security in the agentic era
Core control surfaces you must enforce
To keep agent interactions safe, predictable, and auditable, an enterprise platform needs to enforce controls across several dimensions:- Identity & authentication: Agents must be first‑class identities with scoped credentials and lifecycle controls.
- Authorization & fine-grained RBAC: Not all agents should reach all tools; role-based and attribute-based controls matter.
- Rate limiting & spend control: Agents can be chatty and expensive—policy enforcement must include quotas and cost-aware throttling.
- Data boundaries & masking: Preventing leakage of PII, secrets, or high-risk data requires contextual redaction and schema-aware filters.
- Observability & tamper‑proof logging: Capture invocation traces, tool inputs/outputs, and agent decisions for audit and incident response.
- Policy-based fail-safe behavior: Define how agents degrade or rollback on errors or anomalous behavior.
Real risks: agent sprawl, prompt injection, and unintended actions
The agentic model introduces several operational risks that differ from traditional microservice sprawl:- Agent sprawl: Without governance, ad‑hoc agents proliferate, often duplicate capabilities, and make ownership and auditability unclear.
- Prompt injection and MCP abuse: MCP’s ability to give models direct access to tools and data is powerful but expands the attack surface; misconfigured MCP servers risk unintended data exposure.
- Chain-of-action risk: Agents can combine actions (e.g., call a service to move money, then notify other systems); each chained call compounds the risk surface and increases blast radius.
- Cost runaway: Uncontrolled agent activity can drive unexpected cloud costs—especially when agents call external models, storage, or streaming tiers.
What Gravitee + Azure realistically solve—and what remains hard
Strengths and immediate value
- Unified governance across sync and async: Having the same policy engine applying to REST calls and Kafka topics removes class-of-traffic blind spots.
- Agent-aware identity and catalogs: Treating agents as managed entities simplifies lifecycle management, auditing, and developer self-service.
- Production-grade deployment path: Azure Marketplace availability and integration with Azure IAM and observability stacks speeds enterprise adoption and procurement.
- Protocol support: Supporting MCP and A2A helps organizations adopt community protocols rather than invent one-off integrations.
Limitations and open questions
- Standards maturity: MCP and A2A are evolving standards. Enterprises should assess how stable these protocols are for their long-term architecture and whether vendor implementations interoperate cleanly.
- Third‑party model governance: Controlling costs and data flow when agents call external LLM providers still requires robust spend monitoring and contractual guardrails outside an API gateway.
- Operational complexity: Managing a catalog of agents, their credentials, and lifecycle at scale introduces new platform engineering responsibilities.
- Data governance subtleties: Policy enforcement needs to operate on contextual semantics (e.g., PII within nested JSON) not just surface-level keys—this remains a challenging engineering problem.
Critical observations and cautions
- The claim that Gravitee is a recognized leader in API Management (Gartner 2025) aligns with vendor announcements and public analyst coverage; recognition is real and reflects the company’s strategic momentum. However, analyst positioning is one data point: evaluate Gartner placement alongside independent customer references and technical pilots to validate fit for your environment.
- The Microsoft blog and vendor materials reference a Gravitee-conducted survey (October 2025) that reports “82% of companies” experienced problematic agent interactions. That figure appears in vendor and partner messaging but a public, independently verifiable research report underpinning that exact statistic was not located in the public record while researching this article. Treat single-source vendor statistics as directional—use your own audits and pilot telemetry when sizing risk.
- Assertions about revenue multipliers, headcount, or market share are typically company-supplied and may be useful for vendor maturity assessments. Still, every procurement should confirm those claims via due diligence (financial filings, customer references, or validated analyst reports).
Practical guidance: adopting agent-aware API management in seven steps
- Inventory and classify: Start with a full inventory of APIs, event topics, and candidate agent use cases. Classify by sensitivity, compliance requirements, and ownership.
- Define agent identities and governance model: Treat agents as system identities with lifecycle, owners, and mapped roles. Define who can create, register, and retire agents.
- Create an Agent Catalog and tool contract: Publish agent capabilities and MCP tool contracts. Make machine-readable metadata mandatory for any agentable tool.
- Centralize policy enforcement: Enforce identity, quota, data masking, and authorization consistently across REST, streaming, MCP, and A2A via a control plane.
- Instrument observability and audit trails: Ensure structured logging for agent actions, tool invocations, costs, and chain-of-action traces. Feed this into SIEM and cost-monitoring systems.
- Run controlled pilots and chaos tests: Validate guardrails with fault injection, rate-limit stress tests, and simulated malicious MCP inputs to detect blind spots.
- Operationalize lifecycle and incident playbooks: Define the runbook for agent incidents—how to quarantine an agent, revoke keys, and perform root cause analysis.
Vendor & operational due diligence checklist
- Confirm protocol interoperability: run interop tests for MCP and A2A across the models and toolsets you plan to use.
- Validate identity integration: ensure agent credentials can be managed through Azure AD/Entra ID or your chosen identity provider.
- Confirm telemetry and retention: verify logs include structured tool inputs/outputs, and define retention consistent with audit and compliance needs.
- Test cost controls: simulate common agent behaviors and validate throttles, budget alerts, and automated shutdown triggers.
- Verify data protection: run threat models for MCP endpoints and ensure secrets/data are never exposed through standard tool response patterns.
The competitive and ecosystem angle
Gravitee’s strategy—unifying APIs, events, and agents—positions it against incumbents who may focus on ingress/egress or integration middleware. The vendor’s event-native architecture addresses a tangible technical gap for enterprises investing in streaming-first applications. Meanwhile, major cloud and integration vendors have introduced agent-focused governance and tooling of their own, and enterprises should evaluate:- Depth of streaming support (native Kafka vs mediation)
- Ease of turning legacy APIs into MCP tool endpoints
- Integration with existing API gateways and broker fleets
- Cost and scalability at high agent densities
Conclusion: architecture for responsible agentic systems
The shift to agentic systems changes the problem statement for enterprise architecture: it’s no longer only about secure ingress or API lifecycle; it’s about governing autonomous decision‑makers that stitch together services across the enterprise. Gravitee’s blend of event‑native API capabilities, agent cataloging, and protocol-aware gateways—packaged with Azure deployment options—addresses many of the missing operational pieces needed for production-grade agent ecosystems.That said, the era of autonomous agents is still one of active standardization and rapid change. Security teams must treat MCP and A2A as high-value attack surfaces and build layered defenses: identity-first controls, contextual policy enforcement, robust telemetry, and emergency containment. Pilot early, instrument comprehensively, and bake in cost- and data‑controls before scaling.
For architects, the pragmatic stance is clear: adopt a governance-first approach to agent rollouts. Use marketplaces and partner offerings to accelerate initial deployments, but validate vendor claims and run cross-vendor protocol interop tests. The connectivity layer—now elevated to agent governance—is the place to make responsible AI operational, not aspirational. When it’s done right, it converts connectivity from a liability into a measurable competitive advantage.
Source: Microsoft Gravitee API management for the AI agent era