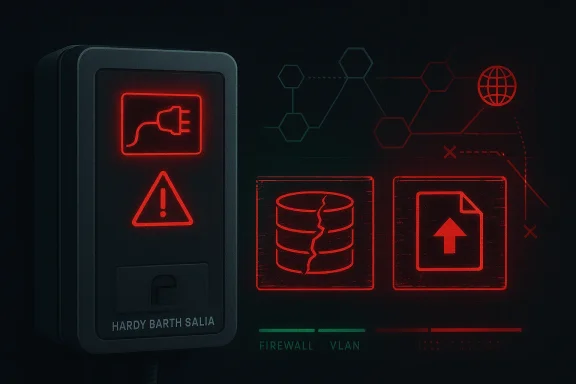
The recent CISA advisory on the Hardy Barth Salia EV Charge Controller is a reminder that EV charging infrastructure is now firmly part of the industrial attack surface. CISA says versions of the Salia Board Firmware up to 2.3.81 are affected by two vulnerabilities, including a buffer overflow that could permit remote code execution and a dangerous file upload issue. The agency also noted a public proof of concept and said it had not seen confirmed public exploitation at the time of publication.
The Hardy Barth Salia family sits in a category that has grown far more important than many organizations initially expected: network-connected EV charging equipment. Chargers are often treated like facilities gear rather than IT assets, yet they sit at the intersection of power, networking, remote management, and billing. That makes them a tempting target for attackers who want to pivot from a seemingly mundane device into a larger operational environment.
CISA has spent the last several years repeatedly warning that EV charging systems belong in the same defensive conversation as other critical infrastructure components. Its broader ICS advisory stream shows that charger-related vulnerabilities are not isolated events but part of a wider pattern affecting vendors across the EV ecosystem. The agency has previously published advisories for other charger families, underscoring that this is now a recurring security discipline, not a one-off scare.
The new Hardy Barth notice matters because it combines two common but serious classes of weakness. An unrestricted upload of a dangerous file type can create a path for malware placement, web shell deployment, or privilege escalation. A buffer overflow can be even more severe, because it can sometimes be chained into code execution, depending on memory protections and the surrounding architecture.
There is also a practical lesson in the way CISA framed the issue. The agency did not describe a broad internet campaign or a confirmed real-world intrusion wave. Instead, it emphasized mitigation: reduce exposure, segment control networks, use VPNs carefully, and apply defensive best practices before exploitation becomes operationally significant. That is a familiar CISA posture, but in the EV charging context it carries unusual weight because the equipment is often deployed in mixed-use environments where convenience has outrun segmentation.
For German manufacturer Hardy Barth, the disclosure lands in a market that increasingly expects connected charging hardware to behave like a managed endpoint. Customers now want remote monitoring, firmware updates, telemetry, and cloud integration, but every one of those features expands the threat model. In that sense, the advisory is not only about one product line; it reflects the ongoing maturity crisis of embedded EV charging security.
The narrow version range also suggests that patch management may be the most reliable mitigation path. In embedded environments, there is often no practical “security agent” to install, no EDR telemetry to watch, and no rich logging stack to mine. That makes knowing the exact vulnerable firmware baseline a significant operational advantage. Precision matters when the recovery path is firmware, not software.
The buffer overflow issue is more concerning from a security engineering perspective because it can break the boundary between malformed input and device execution. CISA’s wording indicates that successful exploitation could crash the device and may also allow remote code execution. That combination is exactly why buffer overflows remain so feared: the damage envelope depends on how the target handles memory corruption, not merely on whether the bug exists.
The advisory also says there has been no known public exploitation specifically targeting these vulnerabilities at the time of release. That is reassuring, but only in a narrow sense. In security terms, “not yet exploited broadly” is not the same as “safe”; it often just means defenders still have a small window to act. That window can close quickly once scanners and exploit kits catch up.
The market’s biggest mistake has been to assume that charge controllers are only power devices. In reality, they are often embedded computers with web interfaces, update mechanisms, and remote management hooks. Those features are useful, but they create the same classes of risk seen in other Internet of Things and OT-adjacent products: weak authentication, poor segmentation, and firmware that ships before the security model is mature.
The security challenge is not just remote exploitation. It is also reliability. If a flaw can crash a charger, the impact may be immediate and visible even without a sophisticated attacker. A denial-of-service condition on a charging point can cause operational disruption, customer frustration, missed fleet schedules, and repair costs, all without any persistent malware being deployed.
That is why advisories like this one deserve attention beyond the EV sector. They illustrate a broader truth about modern infrastructure: every smart device is both a feature and a potential ingress path. Convenience is not free; it comes with a control-plane burden that many organizations still underestimate.
The practical exploitation path depends on many unknowns, including compiler settings, operating system hardening, and whether the vulnerable component can be triggered remotely without authentication. CISA’s warning that remote code execution may be possible indicates that defenders should treat the issue as more than theoretical, even if the exact exploit chain is vendor-specific. The details matter, but the action is the same: patch and isolate.
In many embedded products, upload validation is brittle because it was designed for administrator convenience rather than hostile conditions. Developers may assume that only trusted operators can access the interface, which is a dangerous assumption once any authentication weakness, credential reuse, or exposed management port enters the picture. This is one reason CISA keeps emphasizing network exposure reduction.
A layered response is therefore more appropriate than a purely patch-oriented one. Patch quickly, yes, but also confirm whether the devices are internet-exposed, whether management interfaces are segregated, and whether the charger network has unnecessary routes into enterprise resources. Those controls reduce risk even if a vulnerable device remains online for a short period.
That trend matters because EV charging deployment is accelerating in both public and private environments. Each new installation expands the number of networked endpoints that must be inventoried, segmented, updated, and monitored. The security challenge scales faster than many operators expected, especially when chargers are treated as capital equipment rather than as patchable digital assets.
Another lesson is that internet exposure is frequently the difference between a manageable bug and a real incident. CISA’s recommendation to keep control system devices out of direct internet reach may sound obvious, but in practice many field devices are still reachable through overly generous port forwarding, cloud bridges, or poorly documented remote support paths. Obvious advice is often the hardest to execute.
There is also a procurement problem. Buyers often compare chargers on price, power output, compatibility, and installation convenience, while cybersecurity criteria are treated as secondary. That works until the first advisory forces a fleet-wide firmware review. After that, security becomes visible—but usually at a higher cost and under more urgency than if it had been a purchase requirement from the start.
Enterprises also need to consider incident response boundaries. If a charger is placed in the same network zone as building systems or internal administrative services, a compromise can force broader containment actions. That can mean taking down network segments, cutting remote access, or freezing changes while teams determine whether the device was used as a foothold.
That pressure is not necessarily negative. It can motivate organizations to finally classify charging equipment as part of their operational technology footprint. Once that happens, the controls become more coherent: asset inventory, update policy, network zoning, and vendor assurance stop being optional extras and become part of normal governance.
From there, they should review remote-access architecture and maintenance workflows. If third-party support requires access to charger management interfaces, that access should be tightly controlled, logged, and limited to the minimum necessary. The goal is to reduce the blast radius of both unpatched vulnerabilities and weak credentials.
The most important issue is probably trust. Consumers assume that a charging product is close to an appliance: install it, use it, forget it. Security advisories remind us that the appliance metaphor is incomplete. Any device that accepts input over a network, stores configuration, and can be updated remotely is part of the modern software supply chain.
This is also a moment to rethink how connected infrastructure is purchased. Small businesses often buy whatever the electrician or installer recommends, but they should ask about update cadence, vulnerability disclosure policy, and support timelines. Those questions are simple, yet they often reveal whether the product has been designed with long-term operational security in mind. Procurement is security.
That said, segmentation only works if it is maintained. A lot of organizations create a separate VLAN and then let exceptions accumulate until the security boundary becomes decorative. The lesson here is not just to build segmentation, but to govern it like an actual control.
That is why remote access should be least-privilege, time-bound, and logged. If support vendors need access, that access should be tightly scoped and reviewed. The more the organization can confine access to the management plane, the less likely a charger issue will become a whole-network issue.
The bigger point is that defenders should not wait for proof of exploitation before acting. In embedded environments, the cost of acting early is usually far lower than the cost of a coordinated recovery later. Delay is its own risk factor.
For defenders, the next few weeks should be about inventory, exposure reduction, and patch verification. For vendors, the lesson is that security disclosures now shape market trust as much as product features do. For buyers, especially enterprises and fleet operators, the episode is another reminder that connected infrastructure is software infrastructure, and it has to be managed that way.
Source: CISA Hardy Barth Salia EV Charge Controller | CISA
 Background
Background
The Hardy Barth Salia family sits in a category that has grown far more important than many organizations initially expected: network-connected EV charging equipment. Chargers are often treated like facilities gear rather than IT assets, yet they sit at the intersection of power, networking, remote management, and billing. That makes them a tempting target for attackers who want to pivot from a seemingly mundane device into a larger operational environment.CISA has spent the last several years repeatedly warning that EV charging systems belong in the same defensive conversation as other critical infrastructure components. Its broader ICS advisory stream shows that charger-related vulnerabilities are not isolated events but part of a wider pattern affecting vendors across the EV ecosystem. The agency has previously published advisories for other charger families, underscoring that this is now a recurring security discipline, not a one-off scare.
The new Hardy Barth notice matters because it combines two common but serious classes of weakness. An unrestricted upload of a dangerous file type can create a path for malware placement, web shell deployment, or privilege escalation. A buffer overflow can be even more severe, because it can sometimes be chained into code execution, depending on memory protections and the surrounding architecture.
There is also a practical lesson in the way CISA framed the issue. The agency did not describe a broad internet campaign or a confirmed real-world intrusion wave. Instead, it emphasized mitigation: reduce exposure, segment control networks, use VPNs carefully, and apply defensive best practices before exploitation becomes operationally significant. That is a familiar CISA posture, but in the EV charging context it carries unusual weight because the equipment is often deployed in mixed-use environments where convenience has outrun segmentation.
For German manufacturer Hardy Barth, the disclosure lands in a market that increasingly expects connected charging hardware to behave like a managed endpoint. Customers now want remote monitoring, firmware updates, telemetry, and cloud integration, but every one of those features expands the threat model. In that sense, the advisory is not only about one product line; it reflects the ongoing maturity crisis of embedded EV charging security.
What CISA Disclosed
CISA’s advisory identifies Hardy Barth Salia EV Charge Controller devices running Salia Board Firmware 2.3.81 and earlier as affected. The agency lists two CVEs in the advisory, CVE-2025-5873 and CVE-2025-10371, and assigns the vulnerability set a vendor equipment score of 7.3. That places the issue solidly in the high-severity range, though not in the catastrophic band reserved for the most trivially weaponized flaws.The affected versions
The advisory is narrowly scoped in a way that should help defenders focus their response. Rather than describing a sprawling product family with uncertain boundaries, it points directly to Salia Board Firmware <= 2.3.81. That is important because firmware versioning in embedded fleets is often messy, with field units lagging behind headquarters assumptions by months or years.The narrow version range also suggests that patch management may be the most reliable mitigation path. In embedded environments, there is often no practical “security agent” to install, no EDR telemetry to watch, and no rich logging stack to mine. That makes knowing the exact vulnerable firmware baseline a significant operational advantage. Precision matters when the recovery path is firmware, not software.
The two vulnerability classes
The dangerous file upload issue is typically the easier one to conceptualize. If an attacker can place a malicious file where the device later interprets, executes, or exposes it, the upload channel becomes an attack surface instead of a convenience feature. On many embedded systems, that can be enough to achieve persistence or set up a second-stage payload.The buffer overflow issue is more concerning from a security engineering perspective because it can break the boundary between malformed input and device execution. CISA’s wording indicates that successful exploitation could crash the device and may also allow remote code execution. That combination is exactly why buffer overflows remain so feared: the damage envelope depends on how the target handles memory corruption, not merely on whether the bug exists.
Why the advisory is high priority
CISA noted that it discovered a public proof of concept attributed to YZS17 and reported it to Hardy Barth. Public PoCs often change the risk conversation because they reduce the effort required for less sophisticated attackers to understand the flaw. Even if exploitation has not yet been observed at scale, the existence of proof-of-concept code usually shortens the timeline between disclosure and opportunistic probing.The advisory also says there has been no known public exploitation specifically targeting these vulnerabilities at the time of release. That is reassuring, but only in a narrow sense. In security terms, “not yet exploited broadly” is not the same as “safe”; it often just means defenders still have a small window to act. That window can close quickly once scanners and exploit kits catch up.
- High severity does not automatically mean widespread compromise, but it does mean the exposure is serious.
- Public PoC availability usually lowers the attacker skill threshold.
- Version-specific guidance makes asset inventory the first defense.
- Operational impact may include crash, loss of charging availability, or worse.
- Remote code execution risk moves the issue beyond nuisance-level reliability bugs.
Why EV Chargers Are a Special Target
EV chargers look simple from the outside, but modern charging controllers are deeply networked. They may manage authentication, remote service, billing logic, load balancing, and sometimes integration with building systems or fleet software. That makes them an attractive compromise target because a successful intruder can gain both operational leverage and a foothold inside a trusted network segment.The market’s biggest mistake has been to assume that charge controllers are only power devices. In reality, they are often embedded computers with web interfaces, update mechanisms, and remote management hooks. Those features are useful, but they create the same classes of risk seen in other Internet of Things and OT-adjacent products: weak authentication, poor segmentation, and firmware that ships before the security model is mature.
The bridge between IT and OT
EV charging infrastructure is especially tricky because it often lives in the seam between IT and OT. A charger may be physically installed by a facilities team, managed by an energy contractor, monitored by an IT or cybersecurity group, and depended upon by employees or customers every day. That shared ownership model can blur accountability, which is exactly where vulnerabilities linger longer.The security challenge is not just remote exploitation. It is also reliability. If a flaw can crash a charger, the impact may be immediate and visible even without a sophisticated attacker. A denial-of-service condition on a charging point can cause operational disruption, customer frustration, missed fleet schedules, and repair costs, all without any persistent malware being deployed.
Attackers care about embedded trust
Attackers often prefer devices that are trusted but not closely watched. Chargers fit that description well because many organizations monitor servers and laptops aggressively but leave field equipment on a lighter security diet. Once compromised, a charger can become a quiet pivot point into adjacent systems, especially if the same network also carries other facility or building-management traffic.That is why advisories like this one deserve attention beyond the EV sector. They illustrate a broader truth about modern infrastructure: every smart device is both a feature and a potential ingress path. Convenience is not free; it comes with a control-plane burden that many organizations still underestimate.
- Chargers can be more than endpoints; they can become network footholds.
- Reliability bugs and security bugs often overlap in embedded gear.
- Mixed ownership between facilities and IT can slow remediation.
- Remote management features expand the attack surface.
- Segmentation is not optional when chargers touch enterprise networks.
Technical Risk Profile
The technical language in CISA’s advisory points to two distinct failure modes. One is exploitation that leads to code execution. The other is exploitation that simply crashes the device. Both matter, but for different reasons. A crash is often enough to cause business disruption, while code execution creates the possibility of persistence, surveillance, or lateral movement.Buffer overflow implications
A buffer overflow means untrusted input exceeds the space intended to hold it. In embedded systems, that can be especially dangerous because memory protections may be lighter, the hardware may be less forgiving, and the software stack may not have been built with modern exploit resistance in mind. If the flaw is reachable over the network, the attacker may not need physical access at all.The practical exploitation path depends on many unknowns, including compiler settings, operating system hardening, and whether the vulnerable component can be triggered remotely without authentication. CISA’s warning that remote code execution may be possible indicates that defenders should treat the issue as more than theoretical, even if the exact exploit chain is vendor-specific. The details matter, but the action is the same: patch and isolate.
Dangerous file uploads
The file upload flaw deserves just as much attention because it is often a stepping stone to full compromise. If an attacker can upload a file of a dangerous type and get the device to store or process it, they may be able to smuggle executable content into a trusted environment. That is particularly risky on appliances where the upload directory doubles as a web-accessible or script-executable location.In many embedded products, upload validation is brittle because it was designed for administrator convenience rather than hostile conditions. Developers may assume that only trusted operators can access the interface, which is a dangerous assumption once any authentication weakness, credential reuse, or exposed management port enters the picture. This is one reason CISA keeps emphasizing network exposure reduction.
How defenders should think about it
Security teams should treat the two vulnerabilities as complementary rather than separate. The file-upload issue may help establish persistence or plant a payload, while the buffer overflow may provide the execution primitive. Together, they create the kind of chain that turns a modest advisory into a serious incident response problem.A layered response is therefore more appropriate than a purely patch-oriented one. Patch quickly, yes, but also confirm whether the devices are internet-exposed, whether management interfaces are segregated, and whether the charger network has unnecessary routes into enterprise resources. Those controls reduce risk even if a vulnerable device remains online for a short period.
- Crash impact means availability can be lost even without full compromise.
- Remote code execution raises the issue from nuisance to critical.
- Upload flaws are often ideal for persistence and staging.
- Embedded devices may have weaker memory protections.
- Defense-in-depth is required because any single control may fail.
Historical Context and the Broader EV Charging Pattern
CISA’s latest warning should be read against a larger timeline of EV charging security advisories. The agency has already issued multiple notices involving chargers and charger-adjacent platforms from other vendors, which suggests a persistent security debt across the sector rather than an isolated Hardy Barth problem. In other words, the market has entered a phase where charger vulnerabilities are becoming a routine part of ICS disclosure.That trend matters because EV charging deployment is accelerating in both public and private environments. Each new installation expands the number of networked endpoints that must be inventoried, segmented, updated, and monitored. The security challenge scales faster than many operators expected, especially when chargers are treated as capital equipment rather than as patchable digital assets.
Recurring lessons from prior advisories
The recurring theme in these advisories is not simply that chargers are vulnerable. It is that they are often vulnerable in ways that are familiar to anyone who has studied embedded and ICS security: hardcoded assumptions, insufficient input validation, and update processes that lag the threat environment. That pattern is now visible enough that buyers should be demanding security posture from vendors during procurement, not after deployment.Another lesson is that internet exposure is frequently the difference between a manageable bug and a real incident. CISA’s recommendation to keep control system devices out of direct internet reach may sound obvious, but in practice many field devices are still reachable through overly generous port forwarding, cloud bridges, or poorly documented remote support paths. Obvious advice is often the hardest to execute.
Why the sector keeps repeating the same mistakes
The EV charging industry has grown quickly, and rapid growth tends to expose the gap between engineering speed and security maturity. Vendors are under pressure to support smart features, fleet analytics, and remote serviceability, all of which are market advantages. But every new interface is also a new place for input validation failures, access control mistakes, and update-chain weaknesses to emerge.There is also a procurement problem. Buyers often compare chargers on price, power output, compatibility, and installation convenience, while cybersecurity criteria are treated as secondary. That works until the first advisory forces a fleet-wide firmware review. After that, security becomes visible—but usually at a higher cost and under more urgency than if it had been a purchase requirement from the start.
- Charger advisories are becoming a recurring category, not a novelty.
- Security often lags behind feature growth in fast-moving markets.
- Internet exposure is the multiplier that turns bugs into incidents.
- Procurement decisions shape downstream cybersecurity costs.
- Post-deployment remediation is usually more expensive than upfront scrutiny.
Enterprise Impact
For enterprises, the Hardy Barth disclosure is mostly about risk management and operational continuity. A vulnerable charger is not just a security issue; it is a facilities uptime issue, a user-experience issue, and potentially a network governance issue. If chargers are integrated into employee parking, fleet depots, or public-facing services, downtime can quickly become visible to customers and staff.Fleet and campus environments
Fleet operators have the most immediate exposure because they depend on charging availability as part of daily operations. A compromised or crashing charger can disrupt dispatch schedules, maintenance windows, and energy management strategies. In a campus environment, the impact may be less about revenue and more about reputation, but the operational annoyance can still be significant.Enterprises also need to consider incident response boundaries. If a charger is placed in the same network zone as building systems or internal administrative services, a compromise can force broader containment actions. That can mean taking down network segments, cutting remote access, or freezing changes while teams determine whether the device was used as a foothold.
Insurance, audit, and compliance pressure
Security disclosures like this one often ripple beyond technical teams. Risk managers may ask whether the chargers were inventoried, whether firmware baselines were tracked, and whether the organization can demonstrate due diligence. Auditors may focus on segmentation and patch governance. Insurers may view the exposure as another marker of under-managed connected infrastructure.That pressure is not necessarily negative. It can motivate organizations to finally classify charging equipment as part of their operational technology footprint. Once that happens, the controls become more coherent: asset inventory, update policy, network zoning, and vendor assurance stop being optional extras and become part of normal governance.
Practical enterprise priorities
Enterprises should begin with discovery. They need to know where Hardy Barth equipment is deployed, which firmware versions are present, who manages updates, and whether the devices are internet-reachable. Without that baseline, every other action is guesswork. You cannot patch what you cannot find.From there, they should review remote-access architecture and maintenance workflows. If third-party support requires access to charger management interfaces, that access should be tightly controlled, logged, and limited to the minimum necessary. The goal is to reduce the blast radius of both unpatched vulnerabilities and weak credentials.
- Confirm every deployed Salia firmware version.
- Identify whether chargers are exposed to the internet.
- Separate charging networks from business and guest networks.
- Review third-party support paths and admin credentials.
- Treat chargers as managed assets, not passive electrical fixtures.
Consumer and Small-Business Impact
For consumers and small businesses, the risk profile is different but still meaningful. A home or small commercial charger may not sit inside a complex corporate network, yet it can still be a point of service disruption and a source of privacy or safety concerns. If the charger is remotely managed, the same vulnerability logic applies even if the environment is smaller.Convenience versus control
Residential and light-commercial buyers often prioritize convenience, app integration, and automatic updates. Those are reasonable goals, but they should not obscure the fact that the charger is still a connected device with an attack surface. In a small-business setting, a compromised charger may be enough to disrupt customer charging availability or create support headaches that the owner is not equipped to troubleshoot.The most important issue is probably trust. Consumers assume that a charging product is close to an appliance: install it, use it, forget it. Security advisories remind us that the appliance metaphor is incomplete. Any device that accepts input over a network, stores configuration, and can be updated remotely is part of the modern software supply chain.
What smaller operators should do
Small operators may not have a security team, but they can still apply basic containment principles. Router-level segmentation, strong admin passwords, and a disciplined approach to vendor support access can go a long way. If firmware updates are available, they should be installed promptly, ideally after verifying release notes and backup options.This is also a moment to rethink how connected infrastructure is purchased. Small businesses often buy whatever the electrician or installer recommends, but they should ask about update cadence, vulnerability disclosure policy, and support timelines. Those questions are simple, yet they often reveal whether the product has been designed with long-term operational security in mind. Procurement is security.
- Home and small-business users still need network segmentation.
- Remote management features increase convenience and risk together.
- Firmware updates should be treated as maintenance, not an afterthought.
- Vendor support access should be limited and audited.
- Security questions should be part of the buying decision.
CISA’s Mitigation Advice
CISA’s recommended practices in the advisory are classic ICS guidance, but they remain relevant precisely because they are so often ignored. The agency advises minimizing network exposure, placing control system networks behind firewalls, isolating them from business networks, and using secure remote-access methods such as VPNs while acknowledging VPNs are not a silver bullet.Segmentation first
Network isolation is the most important defensive theme in the advisory. If the charger management interface is not directly reachable from the public internet, exploitation becomes harder and much more visible. If the device is also isolated from the main business network, a compromise is less likely to become a broader enterprise incident.That said, segmentation only works if it is maintained. A lot of organizations create a separate VLAN and then let exceptions accumulate until the security boundary becomes decorative. The lesson here is not just to build segmentation, but to govern it like an actual control.
Remote access and VPN caveats
CISA’s reminder about VPNs is important because many organizations treat VPN as an all-purpose answer. It is not. A VPN can reduce exposure, but it does not fix weak endpoint security, stolen credentials, or an over-broad access model. In some environments, a compromised remote device is the shortest path straight through the VPN tunnel.That is why remote access should be least-privilege, time-bound, and logged. If support vendors need access, that access should be tightly scoped and reviewed. The more the organization can confine access to the management plane, the less likely a charger issue will become a whole-network issue.
Incident discipline
CISA also urges organizations to report suspicious activity through established internal procedures and to notify CISA when warranted. That recommendation may seem procedural, but it serves an important correlation function. Industrial and infrastructure attacks are often distributed across many victims, and early reporting can help identify whether a local anomaly is part of a larger pattern.The bigger point is that defenders should not wait for proof of exploitation before acting. In embedded environments, the cost of acting early is usually far lower than the cost of a coordinated recovery later. Delay is its own risk factor.
- Minimize internet exposure for charge controllers.
- Place chargers behind firewalls and segmented networks.
- Use tightly controlled remote access.
- Log and review administrative activity.
- Treat reporting and incident handling as part of the mitigation plan.
Strengths and Opportunities
The advisory may be unwelcome news for owners of Hardy Barth equipment, but it also creates an opportunity to improve EV charging governance in a way that many organizations have postponed too long. The most obvious strength of the response path is that the affected firmware range is known, the risk is well described, and CISA has already outlined a practical containment strategy. That gives defenders a concrete action plan rather than a vague warning.- The vulnerable firmware range is clearly identified.
- CISA provided straightforward containment guidance.
- The presence of a public PoC gives urgency and clarity.
- Organizations can use the disclosure to improve asset inventory.
- The issue supports stronger OT/IT segmentation practices.
- Vendors and buyers now have a case for better security requirements.
- Security teams can use this as a tabletop exercise for charger incidents.
Risks and Concerns
The biggest concern is that EV charging systems are still often deployed with inadequate security expectations. Many owners will read the advisory, confirm they are not directly exposed, and then assume they are safe. That is a dangerous mindset because internal pivots, third-party access, or future exploit development can still turn an apparently contained issue into an operational problem.- Public PoCs reduce the time between disclosure and real-world probing.
- Firmware updates may not be easy to deploy across all installations.
- Some chargers may remain exposed through forgotten remote-access paths.
- Small operators may lack the visibility to know what version they run.
- Mixed ownership can delay response and accountability.
- A crash-only outcome can still be a serious business interruption.
- Remote code execution, if achieved, could have broader network consequences.
Looking Ahead
The Hardy Barth advisory is unlikely to be the last EV charging vulnerability of 2026, and that is part of what makes it important. The sector is moving toward richer connectivity, more remote management, and deeper integration with enterprise energy and mobility programs. Those are positive developments, but they will keep producing new security findings unless secure development and disciplined deployment become standard operating practice.For defenders, the next few weeks should be about inventory, exposure reduction, and patch verification. For vendors, the lesson is that security disclosures now shape market trust as much as product features do. For buyers, especially enterprises and fleet operators, the episode is another reminder that connected infrastructure is software infrastructure, and it has to be managed that way.
- Verify firmware versions across all installed chargers.
- Remove unnecessary internet exposure and remote support paths.
- Segment charger networks from business systems.
- Confirm vendor patch availability and upgrade procedures.
- Review incident response plans for charger outages or compromise.
Source: CISA Hardy Barth Salia EV Charge Controller | CISA