Microsoft’s December cumulative—KB5072033—promised security and reliability fixes, but a seemingly minor configuration change to the AppX Deployment Service (AppXSVC) has produced tangible slowdowns, monitoring noise, and management headaches across some Windows 11 and Server 2025 installations.
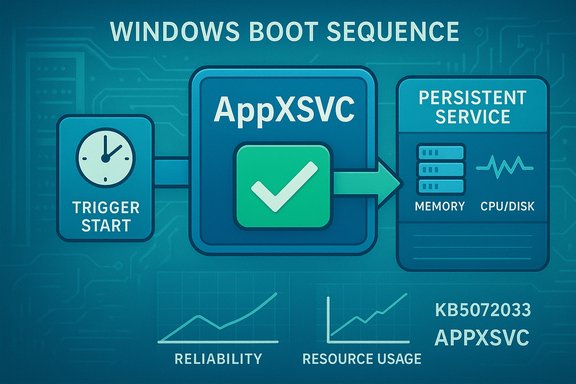
Microsoft shipped the December 9, 2025 cumulative update identified as KB5072033 (OS builds 26100.7462 for 24H2 and 26200.7462 for 25H2). The official change log in the update’s notes includes a concise but consequential line: “The AppX Deployment Service (Appxsvc) has moved to Automatic startup type to improve reliability in some isolated scenarios.” This single-sentence change is the root cause of the community and IT response now circulating across forums and vendor blogs. Put simply, a service that previously started on demand now launches at boot on many devices, which alters early-session behavior, memory residency, and disk I/O timing. For many modern PCs this will be invisible. For others—particularly devices with limited RAM, older storage, or monitored server images—the difference can be meaningful.
Source: Gizmochina Microsoft’s December update frustrates some Windows 11 users with slower performance - Gizmochina
 Background / Overview
Background / Overview
Microsoft shipped the December 9, 2025 cumulative update identified as KB5072033 (OS builds 26100.7462 for 24H2 and 26200.7462 for 25H2). The official change log in the update’s notes includes a concise but consequential line: “The AppX Deployment Service (Appxsvc) has moved to Automatic startup type to improve reliability in some isolated scenarios.” This single-sentence change is the root cause of the community and IT response now circulating across forums and vendor blogs. Put simply, a service that previously started on demand now launches at boot on many devices, which alters early-session behavior, memory residency, and disk I/O timing. For many modern PCs this will be invisible. For others—particularly devices with limited RAM, older storage, or monitored server images—the difference can be meaningful. What is AppXSVC and why startup type matters
The role of AppX Deployment Service (AppXSVC)
AppXSVC (service name AppXSVC) is the Windows service responsible for installing, registering, updating and removing Microsoft Store packages (AppX / MSIX / UWP). It unpacks packages, registers app containers and coordinates background provisioning tasks for Store-distributed and some system-provided modern apps. Under normal operation the service is invoked only when package work is needed.Trigger-start vs Automatic: a behavioral difference that matters
- Trigger-start (Manual): the service remains dormant until a specific event (Store activity, a scheduled task, or an installer action) starts it. Work is done, the service exits, and the system returns to a low steady-state footprint.
- Automatic: the service is launched during boot and remains resident (or is at least present in the process lifecycle), introducing timers, queues and periodic checks into the early-session window.
The official change: what Microsoft published
Microsoft’s KB documentation for KB5072033 records the startup-type change in the System Components section. The vendor frames the alteration as intended to “improve reliability in some isolated scenarios,” but offers no public engineering detail about which scenarios or device classes inspired the decision. The short public rationale has left administrators requesting more context as they weigh the trade-offs of the change. Microsoft Q&A threads and the update notes confirm the change is deliberate in the shipped package; those community posts have become a primary locus for technical detail, real-world telemetry and remediation ideas even as Microsoft collects telemetry from broader deployments.Real-world impact: symptoms observed in the field
Multiple independent community reports and forum threads converged on the same symptom set shortly after the December rollup:- Higher idle RAM shortly after boot with AppXSVC visible as a resident process in Task Manager or Process Explorer.
- Longer boot times and early-session sluggishness as disk, CPU and I/O are used for package enumeration or manifest validation.
- Elevated disk I/O during login, worst on HDDs or congested NVMe drives, which can delay app launches and increase perceived lag.
- Service start/stop “flapping” in some Server 2025 images where the binary appears to expect trigger semantics: SCM starts the service, it exits quickly, and SCM restarts it—triggering monitoring alerts.
Why some environments are disproportionately affected
Low-spec client devices
Small increases in resident working set (tens to hundreds of MB) on devices with limited RAM can push systems into paging and swap activity, causing noticeable UI lag and longer response times. Because AppXSVC can trigger package validation and manifest scans early in a session, that I/O is particularly disruptive on HDDs.Virtualization and session hosts
Density-sensitive VDI hosts and session hosts rely on predictable, low-footprint images. Any additional resident process reduces session density or triggers false monitoring alerts, especially where orchestration expects AppXSVC to be trigger-start.Monitored servers
Monitoring platforms like Zabbix, Nagios, and similar products can interpret repeated start/stop cycles as failures. When AppXSVC is set to Automatic but the binary exits quickly because it was designed as an on-demand task, monitoring dashboards light up with flapping alerts and incident noise. This is a practical operations problem—alerts flood helpdesks and obscure genuine incidents. Microsoft Q&A and community threads document these monitoring impacts.What’s verified, what’s unconfirmed
- Verified: KB5072033 explicitly documents the AppXSVC startup-type change. That fact is confirmed by Microsoft’s official KB entry.
- Verified: Community reporting from multiple independent outlets and forum captures shows real users and administrators experienced higher memory use, early-session disk and CPU spikes, and monitoring alerts after installing the December cumulative.
- Unverified / caution: Broader claims about a specific memory leak in Delivery Optimization (DoSvc) or an outright persistent runaway process are observationally consistent with user traces, but Microsoft has not publicly confirmed a DoSvc memory-leak root cause at the time of reporting. Treat memory-leak assertions as observed symptoms pending a vendor-level engineering advisory.
Practical mitigations and trade-offs
Enterprises, SMBs and power users landed quickly on a set of mitigations—some safe and reversible, others riskier. Below is a practical, prioritized list built from community-tested steps and Microsoft Q&A guidance.Quick, reversible troubleshooting steps (recommended first)
- Confirm whether KB5072033 is installed:
- Settings → Windows Update → Update history, or
- Win + R → winver to confirm OS build.
- Check AppXSVC startup type and status (elevated command prompt):
- sc qc AppXSVC
- sc qtriggerinfo AppXSVC
These show the configured START_TYPE and any trigger events. - Temporarily stop the service (short-term only):
- net stop AppXSVC
This stops the service until the next boot and is useful for quick reproduction tests. - Revert startup type for troubleshooting:
- sc config AppXSVC start= demand
Reboot and observe performance. This sets the service back to demand start (manual/trigger) without permanently disabling it. It’s reversible and the recommended first step for pilots.
Administrative and rollout guidance (for IT)
- Pilot the change in a small ring before wide deployment. Measure end-user responsiveness, boot times, application latency and monitoring alerts.
- For VDI and non-persistent images, evaluate the image with AppXSVC set to Manual in the golden image to preserve density and reduce alerting noise.
- Collect structured diagnostics before and after mitigation: ETW traces (Windows Performance Recorder), Process Explorer dumps, CBS logs, and monitoring logs for Zabbix/Nagios correlation. These artifacts are essential if Microsoft support engagement is required.
What not to do — risky or irreversible actions
- Do not permanently disable AppXSVC using services.msc or registry edits unless you accept breakage. Disabling AppXSVC can prevent Store app installations/updates and affect some modern-system flows. Microsoft documentation for service configuration highlights that AppXSVC supports deploying Store applications and notes potential feature breakage when it’s disabled.
- Avoid heavy-handed ACL changes or forcing ownership changes on system service binaries; these may conflict with TrustedInstaller protections and can cause servicing or security issues. Community “deep hacks” are reversible only with strong OS expertise and are not recommended for production images.
Technical steps IT teams should include in a remediation playbook
- Baseline collection (before patching)
- Boot time trace capture (WPR), Process Explorer snapshot, memory working set dump, Event Logs, monitoring alert baselines.
- Controlled deployment
- Pilot KB5072033 on a small percentage of machines across hardware classes (thin clients, low-end laptops, desktops, VM images).
- Collect post-install telemetry for 48–72 hours to detect steady-state effects.
- Reversion and rollback
- For images where AppXSVC is problematic, set startup back to demand for the image: sc config AppXSVC start= demand, update golden image, redeploy.
- If uninstalling KB5072033 is considered, understand that removing a cumulative may also remove security fixes; prefer per-service mitigations where possible.
- Microsoft escalation
- If start/stop flapping or memory growth affects production, gather the trace artifacts and open a formal support case with Microsoft. Attach ETW captures, Process Explorer dumps and a timeline correlated to KB install time. Microsoft Q&A and support processes are tracking the issue and provide a channel for engineered fixes.
Monitoring and alert tuning to reduce noise
If Zabbix (or similar) is flagging AppXSVC flapping after KB5072033, administrators can take short-term steps:- Adjust monitoring thresholds or suppress repeated alerts from services known to be in diagnostic change windows.
- Create a targeted rule to suppress automated restart alerts for AppXSVC for a brief maintenance window while pilots and mitigations run.
- Log and retain the original alerts so that noise suppression doesn’t hide unrelated genuine failures.
Analysis: strengths, risks, and Microsoft’s communication gap
Notable strengths behind Microsoft’s change
- The move to automatic startup likely targets real race conditions where app provisioning or Store updates fail because the deploy service wasn’t running early enough—an operational reliability improvement for certain edge scenarios.
- Bundling fixes into a cumulative ensures critical security and quality patches are delivered together, which simplifies patch management for many organizations.
Real risks and trade-offs
- The lack of public detail about which “isolated scenarios” motivated the flip left many admins guessing whether their fleets were targeted, increasing cautious reaction and operational overhead.
- A seemingly small configuration change in a widely distributed cumulative caused disproportionate impact on low-spec and density-sensitive environments—illustrating how micro-changes can cascade.
- Communication could have been clearer: advanced notice, advisory ranges (device classes or SKUs) or opt-in pilot channels would have reduced confusion.
The communication gap
Microsoft’s KB entry is accurate but terse. The absence of explicit guidance describing the targeted scenarios or rollout plan created a vacuum rapidly filled by forums, vendor blogs and community labs. That vacuum generated operational churn—pilot restarts, mitigations, and monitoring workarounds—that could have been minimized with more detailed vendor commentary.Long-term implications and guidance for Windows administrators
- Treat cumulative updates as packages that can change default runtime characteristics—not only binaries and bug fixes but also configuration defaults that can alter runtime behavior.
- Build disciplined pilot rings: consumer, low-end, mainstream and server images should be represented in early rings so configuration-sensitive changes are detected early.
- Maintain a short-term mitigation playbook for all critical images: quick commands to revert service startup types, isolated suppression rules for monitoring noise, and a structured diagnostics checklist to escalate to vendor engineering.
- Advocate for better vendor transparency: request deeper KB notes or a “what changed and why” companion advisory that details the operational scope and device types that motivated configuration changes.
Quick reference: commands and checks
- Check KB install / build:
- Win + R → winver or Settings → Windows Update → Update history.
- Check AppXSVC config (elevated):
- sc qc AppXSVC
- sc qtriggerinfo AppXSVC
- Revert to demand start:
- sc config AppXSVC start= demand
- net stop AppXSVC (optional, until next boot)
- Temporary stop:
- net stop AppXSVC
- Collect diagnostics:
- Windows Performance Recorder (WPR) → capture boot & CPU/IO traces
- Process Explorer snapshot and memory dump
- CBS and WindowsUpdate logs for servicing correlation
Conclusion
A short line in a cumulative update—changing AppXSVC to Automatic—has reminded administrators and power users that small defaults matter. The technical trade-off Microsoft describes—reliability in some isolated scenarios—is plausible, and the vendor did make the change intentionally; however, the practical consequence is real for a subset of systems. Community reporting, Microsoft Q&A threads and independent outlets all converge on an actionable picture: some machines are slower, some servers generate monitoring noise, and some administrators must temporarily revert startup behavior while telemetry and fixes mature. For IT teams, the path forward is clear: pilot, measure, and use reversible mitigations rather than blunt-force changes. For Microsoft, clearer communication on why a configuration flip was necessary and which device classes benefited would reduce operational friction and restore confidence more quickly. Until then, administrators should treat KB5072033 as a case study in why service startup semantics deserve as much attention as binaries and patches when planning maintenance windows and update rings.Source: Gizmochina Microsoft’s December update frustrates some Windows 11 users with slower performance - Gizmochina