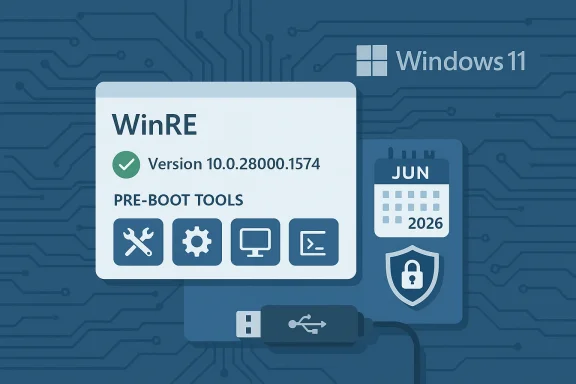
Microsoft published KB5077178 on February 10, 2026 — a Safe OS Dynamic Update that refreshes the Windows Recovery Environment (WinRE) for Windows 11, version 26H1, and it carries two operationally important declarations: the updated WinRE image should report version 10.0.28000.1574 after installation, and administrators must pay attention to an imminent Secure Boot certificate expiration window beginning in mid‑2026. (support.microsoft.com)
Safe OS Dynamic Updates are Microsoft’s surgical mechanism for keeping the small, pre‑boot recovery footprint current without forcing full ISO rebuilds or wholesale image recaptures. They target the trimmed set of binaries and drivers WinRE uses for Reset this PC, Automatic Repair, cloud reinstall, and BitLocker unlock flows — the last line of defense when a device will not boot normally. Microsoft documents the role and acquisition of dynamic updates and emphasizes their use for media hygiene and setup reliability.
Operationally, Safe OS DUs differ from typical monthly cumulative updates in three key ways:
Practically, the risks of a stale WinRE are not theoretical:
Best practices for handling the Secure Boot angle:
In short:
Source: Microsoft Support KB5077178: Safe OS Dynamic Update for Windows 11, version 26H1: February 10, 2026 - Microsoft Support
 Background / Overview
Background / Overview
Safe OS Dynamic Updates are Microsoft’s surgical mechanism for keeping the small, pre‑boot recovery footprint current without forcing full ISO rebuilds or wholesale image recaptures. They target the trimmed set of binaries and drivers WinRE uses for Reset this PC, Automatic Repair, cloud reinstall, and BitLocker unlock flows — the last line of defense when a device will not boot normally. Microsoft documents the role and acquisition of dynamic updates and emphasizes their use for media hygiene and setup reliability. Operationally, Safe OS DUs differ from typical monthly cumulative updates in three key ways:
- They modify the recovery image (winre.wim) or the safe operating system used during setup, not the running desktop runtime.
- Once injected into an image (install media or winre.wim), the change is typically non‑removable from that image; rollback generally requires restoring ge.
- Failures are high‑impact but often dormant — a problem appears only when an upgrade or recovery task exercises the updated pre‑boot code. These characteristics make Safe OS DUs essential for image hygiene but also demanding to deploy safely.
What KB5077178 actually does — the essentials
The KB page’s public summary is intentionally concise — “This update makes improvements to the Windows recovery environment (WinRE)” — but the update page and catalog artifacts are where the operational details live. From Microsoft’s published KB you should note the following authoritative facts:- Applies to: Windows 11, version 26H1 (all editions). (support.microsoft.com)
- Delivery channels: Windows Update, Microsoft Update Catalog (standalone CAB), WSUS. (support.microsoft.com)
- Post‑install WinRE target version: 10.0.28000.1574. Use GetWinReVersion.ps1 or DISM to confirm this value after servicing. (support.microsoft.com)
- Restart: No host restart is required after applying this update to the on‑disk WinRE image. ([suppops://support.microsoft.com/en-us/topic/kb5077178-safe-os-dynamic-update-for-windows-11-version-26h1-february-10-2026-040babb2-5a34-452f-9691-34e21399a0d4))
- Removal: Cannot be removed once applied to a Windows image; rolling back an injected change requires reverting to a preserved pre‑DU image. (support.microsoft.com)
- Secure Boot advisory: Microsoft warns that Secure Boot certificates used by many Windows devices will begin expiring in June 2026, and administrators must review the guidance anertificates to avoid boot disruption. That advisory is explicitly called out on the KB page and directly affects how you plan recoverability and Secure Boot changes. (support.microsoft.com)
Why this matters now: recovery hygiene and the 26H1 context
Windows 11’s servicing cadence in 2026 introduced a device‑specific platform branch, 26H1, targeted at new Arm silicon and select launch devices. That created a scenario where recovery tooling must match platform baselines on devices that ship with different preinstalled branches. Safe OS DUs like KB5077178 away to keep WinRE aligned with the running OS and with thesetup runtime used during upgrades and device provisioning — particularly important where a device ships with a new platform baseline or where engineers have applied recent LCUs to offline images.Practically, the risks of a stale WinRE are not theoretical:
- USB input not working inside WinRE, rendering keyboard or mouse unresponsive during a recovery.
- Missing NVMe or RAID storage drivers preventiks in pre‑boot.
- BitLocker prompts or key handling mismatches that stall automated cloud reinstall or Reset flows.
These issues increase helpdesk time and can create a “no‑recovery” situation for critical endpoints — the very scenarios Safe OS DUs are designed to prevent.
How administratohecklist and process
The following checklist condenses best practices observed across Microsoft guidance and community operational playbooks. It’s deliberately prescriptive: Safe OS DUs are low blast radius only if you validate and stage them carefully.- Back up golden images and recovery artifacts.
- Preserve an immutable copy of your pre‑DU winre.wim and install.wim and record their checksums. Safe OS DU injections are commonly non‑removable from images, so a preserved backup is your rollback plan.
- Acquire the standalone CAB from the Microsoft Update Catalog.
- Use the catalog entry to download the CAB and record the SHA‑256alog. Validate your download before using it. Microsoft Learn and the KB both point to the Update Catalog as the source for oarn.microsoft.com]
- Verify packn Get‑FileHash -Path .\KB5077178.cab -Algorithm SHA256 and match ate Catalog manifest.
- Mount a copy of winre.wim for inspection.t, then inspect Windows\System32 file versions (for example winpeshl.exe, winload, securekernel), and compare them to the catalog manifest. Example: dism /Mount-Image /ImageFile:"C:\recovery\winre.wim" /Index:1 /MountDir:C:\mnt\winre.
- Inject the CAB into the mounted image.
- DISM /Image:C:\mnt\winre /Add-Package /PackagePath:C:\downloads\KB5077178.cab then commit with dism /Unmount-Image /MountDir:C:\mnt\winre /Commit. Follow Microsoft’s “Add an update package to Windows RE” guidance if your environment uses BitLocker or other managed settings. (support.microsoft.com)
- Recreate deployment media and test.
- Replace the winre.wim in your install media, update PXE/MDT/SCCM shares, then exercise recovery and provisioning flows on representative hardware. Test and cloud), Automatic Repair, BitLocker unlock, and USB input under WinRE.
- Download KB5077178 CAB from the Update Catalog and validate SHA‑256.
- Back up pre‑DU winre.wim (immount the winre.wim via DISM and inspect file versions.
- Apply the CAB to the mounted image with DISM /Add‑Package.
- Commit/unmount, replace media, and stage for pilot testing.
Verifying success and troubleshooting: concrete checks
KB5077178 ships Microsoft’s recommended verification toolbox. Use these exact checks to assert success and to gather forensic data if issues appear:- GetWinReVersion.ps1: The KB includes a Microsoft‑published script that mounts the active winre.wim and extracts the internal WinRE version from a core binary. After successful servicing, the script should report 10.0.28000.1574. Use it first as a quick sanity check. (support.microsoft.com)
- WinREAgent event logs: Event ID 4501 — Servicing succeeded will be recorded in the System log when WinRE is updated on a running device. Search for WinREAgent events in Event Viewer. (support.microsoft.com)
- DISM image info: Use dism /Get-ImageInfo /ImageFile:<path to winre.wim> /index:1 to check the image metadata and file timestamp list. Compare binary versions inside the mounted image against the Update Catalog manifest.
- Functional tests inside WinRE: Perform Reset this PC (local and cloud), Automatic Repair, and BitLocker unlock to ensure UX and driver behavior meet expectations. These functional flows are the only reliable end‑to‑end validation.
- Revert media from your preserved golden backup; do not attempt a partial “undo” inside an image that has had a Safe OS DU baked into it.
- If a running device fails to boot into a responsive WinRE (USB input not working), attempt booting from external WinPE / recovery USB to recover data or restore winre.wim.
- Inspect WinREAgent logs and DISM output for package application errors. Community guidance documents a small number of edge cases that required emergency fixes in past cycles, typically tied to very specific USB controller or storage driver families.
Secure Boot certificaical wrinkle
KB5077178 prominently calls out a broader Microsoft advisory: Secure Boot certificates used by most Windows devices are set to begin expiring in June 2026, and administrators are asked to review and prepare for certificate updates to avoid Secure Boot failureheral note — changes to the Secure Boot DB and to pre‑boot boot managers can trigger validation failures if a device’s DB is reconfigured after the bood with a newer signature. Past Safe OS and Setup DUs have replaced pre‑boot components (for example, a boot manager signed by a later CA), and Microsoft warns administrators that togglinting the DB on devices that received new bootmgr binaries can produce Secure Boot violations. Plan your Secure Boot change windows, and ensure you have tested recovery media and known‑good fallback images before touchinevices that may have received updated pre‑boot binaries. (support.microsoft.com)Best practices for handling the Secure Boot angle:
- Prior to changing the Secure Boot DB (ccertificates), document whether devices have received DUs that replaced pre‑boot binaries. That inventory is a simple comparison between the file manifest in the Update Catalog and a sampled device’s winre.wim/boot manager hash.
- Prefer phased rollouts and validate update signals (successful updates) before applying DB changes at scale.
- Maintain external, signed recovery media and preserve golden images with known‑good pre‑boot artifacts; these are your fallback if a Secure Boot mismatch prevents normal boot.
Risk analysis — strengths and potential failure modeal fixes reduce image rebuild frequency. Injecting a Safe OS DU into winre.wim keeps deployment media current with minimal overhead. This is operationally efficient for large imaging pipelines.
- Improves recovery success for modern hardware. Updated USB and storage drivers in WinRE directly reduce unbootable cases caused by driver mismatch.
- Narrow attack surface. Dynamcused set of binaries and drivers, limiting the scope of change and simplifying validation compared with rebuilding entire OS images.
- Non‑removability: Once the DU is baked into an image, it is effectively permanent for that artifan force a costly restore or rebuild. Always preserve immutable backups.
- Regressions on niche hardware: Any change in pre‑boot drivers or orchestration code can producemmon USB controllers, storage adapters, or OEM firmware interactions. Real‑world reports across past cycles show a small number of edge cases that required follow‑up fixes. Test on representative hardware families.
- Secure Boot coupling: Replacing pre‑boot components that carry new CA signatures creates operational coupling to the Secure Boot DB. Resetting or changing DB entries can render a device unbootable if the new boot manager no longer matches DB expectations. Plan Secure Boot changes carefully. (support.microsoft.com)
- WSUS and catalog propagation: The Update Catalog is the authoritative distribution point for offline injection, but catalog entries may take time to propagate to WSUS or other management tooling. Verify synchronization before relying on server delivery.
A recommended rollout plan (practical, conservative)
- Inventory and categorize devices by hardware family, BitLockeot state. Prioritize machines with high incidence of recovery issues.
- Prepare a lab with representative hardware (USB‑C only laptops, BitLocker‑enabled devices, NVMe/RAID controller families). Exercise full recovery flows.
- Pilot: inject KB5077178 into a small set of golden images and validate by creating ISO/USB, then deploy to a narrow pilot of devices (10–50 units) across multiple OEMs and firmware versions. Collect WinREAgent logs and functional results for 48–72 hours.
- Phased rollout: expand to larger groups, watch helpdesk telemetry for unexplained recovery failures, and keep rollback procedures (preserved winre.wim) at the ready.
- Secure Boot actions: If your rollout requires Secure Boot DB changes, perform those only after confirming devices have successfully updated and after validating recovery media on at least one device per firmware family.
Final verdict and practical takeaway
KB5077178 is a standard, necessary Safe OS Dynamic Update: it modernizes WinRE for the new Windows 11 26H1 servicing family and includes a critical advisory about looming Secure Boot certificate expirations. For organizations that manage imaging pipelines or that support large fleets, the update’s benefits — improved recoverability and fewer setup mismatches — are substantial. But the package’s non‑removable nature and Secure Boot coupling mean that the benefits arrive only if you apply disciplined validation, backup, and pilot practices first. (support.microsoft.com)In short:
- Treat KB5077178 as an image‑hygiene imperative for 26H1 media and devices. (support.microsoft.com)
- Don’t inject it into golden images without backups and representative testing.
- Pay special attention to the Secure Boot certificate advisory; if your environment changes DB/PK/KEK state, plan and test recovery media first. (support.microsoft.com)
Source: Microsoft Support KB5077178: Safe OS Dynamic Update for Windows 11, version 26H1: February 10, 2026 - Microsoft Support