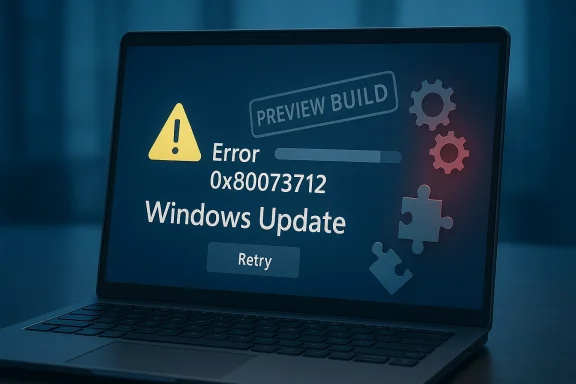
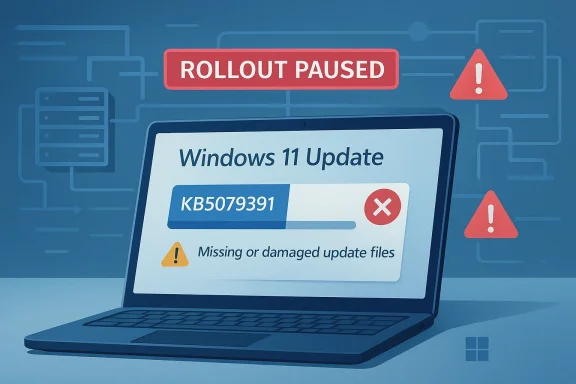
Microsoft has paused rollout of Windows 11 preview update KB5079391 after some devices hit an installation failure, and the move lands at an awkward moment for a company trying to convince users that Windows quality is improving. The issue is tied to error 0x80073712, with Microsoft saying affected users may see a message that some update files are missing or corrupted and that the company has temporarily limited availability while it investigates. The update is not a security patch, but it was being offered as a production-quality preview for Windows 11 version 24H2 and 25H2. (support.microsoft.com)
Microsoft’s Windows servicing model has long revolved around a predictable monthly rhythm: a security-heavy Patch Tuesday release, followed by optional preview updates that let interested users and administrators test fixes and features before they become part of the next security cumulative update. KB5079391 fits squarely into that second category. It was released on March 26, 2026 as a non-security preview for Windows 11 versions 24H2 and 25H2, and Microsoft described it as carrying production-quality improvements. (support.microsoft.com)
That wording matters because preview updates occupy a gray zone in user perception. They are optional, but they are not throwaway builds. Microsoft’s own support page frames them as releases that are meant to preview the next month’s security update content, which makes a failed rollout more embarrassing than a simple lab-only bug. In practice, users installing these updates are often the ones trying to stay current, validate hardware, or catch improvements early. (support.microsoft.com)
The current episode also follows a separate out-of-band update, KB5085516, which Microsoft shipped on March 21, 2026 to address Microsoft account sign-in problems introduced by the March 10 update. That sequence reinforces a familiar Windows pattern: a base update, an emergency follow-up, and then a preview release that itself needs to be paused. For enterprise admins, that is not a catastrophic story, but it is absolutely a confidence story. (support.microsoft.com)
Microsoft has publicly been trying to reposition Windows reliability as a priority. In a March 20 blog post, Windows chief Pavan Davuluri told Insiders, “Thank you for holding us to a high standard,” while promising that the company is committed to strengthening the platform’s foundation. That makes this latest pause feel less like a routine servicing hiccup and more like an immediate test of whether that promise is translating into fewer user-visible failures. (blogs.windows.com)
The fact that the problem was caught at install time is important. According to Microsoft’s support page, the affected update did not appear to break devices after installation, because the failure happened before the update could be applied. That distinction won’t comfort users who hit the error, but it does mean this is not a destructive outage in the way some past Windows updates have been. That is a relief, but only a partial one. (support.microsoft.com)
That message is consistent with a class of Windows servicing problems that usually point toward component store corruption, missing files, or a package composition problem somewhere in the update chain. Microsoft does not disclose the exact root cause on the support page, which is unsurprising, but it also means users and admins are left to infer whether the fault is in the package metadata, the staging mechanism, or a backend distribution issue. The company is acknowledging the symptom, not the mechanism. (support.microsoft.com)
There is a subtle but important distinction here. A failed installation error is much less severe than a regression that bricks a machine, but it is still a signal that the update pipeline is not resilient enough. When Microsoft pauses a preview update, it is usually trying to avoid compounding the problem by pushing the same package to more machines before understanding whether the issue is localized or systemic. (support.microsoft.com)
That approach is sensible because preview updates are as much about confidence as functionality. If a non-security optional update cannot reliably install, then it ceases to serve its intended role as a testbed for quality improvements. In that sense, the pause is not just damage control; it is also Microsoft preserving the credibility of its update channel. A preview that can’t preview is worse than no preview at all. (support.microsoft.com)
Among the headline items, Microsoft said the update lets monitors report refresh rates higher than 1000 Hz, improves HDR reliability for displays with non-compliant DisplayID 2.0 blocks, and enhances reliability around opening the Settings home page and downloading required updates. It also includes changes for narrator voices, file blocking in File Explorer, and safe mode taskbar loading. That is a lot of surface area for one preview release. (support.microsoft.com)
The display changes are especially interesting because they hint at the pace of hardware evolution. Support for monitors above 1000 Hz is niche today, but it signals that Microsoft wants Windows to be ready for extreme gaming and high-refresh professional displays before the market fully normalizes them. That is forward-looking engineering, even if most users will never see the benefit directly. (support.microsoft.com)
The pause on KB5079391 is especially awkward because Microsoft explicitly markets these updates as production-quality. That phrase is meant to reassure users that preview does not mean experimental. When the package itself is then blocked due to installation issues, the marketing language starts to sound aspirational rather than operational. (support.microsoft.com)
That tension is not unique to Microsoft. Operating system updates are inherently risky because they touch everything from drivers to network stacks to security policies. But Windows carries a special burden because it powers both consumer machines and fleet-managed enterprise endpoints, where even a minor update problem can ripple into help desk tickets and delayed deployments. (support.microsoft.com)
That perception matters because trust is an operational asset. If users delay updates out of fear, Microsoft has to work harder to achieve coverage, which in turn increases exposure windows for security fixes. So a failed optional update can have consequences beyond the direct bug itself. Reliability is not just a quality metric; it is a delivery mechanism for security. (support.microsoft.com)
Enterprise teams are also more likely to care about the update’s bundled changes, especially reliability improvements in Settings, Remote Desktop, and the servicing stack itself. When the update is blocked, those improvements remain out of reach, which can prolong known pain points and complicate validation schedules. The biggest cost is often not the failure itself, but the delay it forces downstream. (support.microsoft.com)
This sequence illustrates the challenge of modern Windows servicing: security deadlines, hotfix urgency, and optional feature staging all happening in parallel. Microsoft is trying to keep the pipeline moving while also preventing one issue from cascading into another. But when multiple update events appear in close succession, each one makes the next one harder to trust.
There is also a communication issue. Microsoft’s support page says additional information will be shared when available, but users are rarely patient with vague servicing language. They want to know whether the issue is widespread, whether reinstalling helps, and whether the update will return in the same form or as a revised package. Silence in a servicing incident tends to be interpreted as uncertainty, even when engineers are simply still investigating. (support.microsoft.com)
That said, pulling the update is also evidence that Microsoft’s internal and external monitoring is working. It is better to pause a flawed package than to keep shipping it in the hope that the problem stays hidden. The hard part is not deciding to pause; it is avoiding the pattern that requires pausing too often. (support.microsoft.com)
Still, the error can be confusing because the phrasing suggests missing or damaged files, which can make users think their machines are broken. That can prompt unnecessary cleanup attempts, system restore experiments, or frantic online searches. The average user does not differentiate between a bad update payload and a local component store problem; they just see Windows failing. (support.microsoft.com)
Administrators will likely interpret the pause more conservatively. If a deployment is already in progress, they may freeze rings, hold off on manual installation, or wait for a revised release before resuming rollout. That is especially true in managed environments where change control matters more than curiosity about a preview feature. (support.microsoft.com)
The servicing stack is the plumbing behind Windows Update. Users rarely think about it until something goes wrong, but every cumulative update depends on it. If the pipeline misbehaves, even a well-crafted package can fail to stage correctly. That is why Microsoft keeps adding SSU updates alongside LCUs: the company knows the installer itself is part of the product experience. (support.microsoft.com)
The support page also shows that Microsoft still expects advanced users and admins to use catalog downloads, DISM, and WUSA in some circumstances. That is useful for controlled environments, but it also underscores how complex Windows servicing remains. The more manual escape hatches there are, the more obvious it becomes that the default experience has not fully earned one-click trust. (support.microsoft.com)
This is especially relevant in hybrid workplaces, where the operating system is just one layer of a larger device strategy. A stable Windows update story helps Microsoft sell the notion that it can manage endpoints, identities, and productivity services as an integrated stack. A troubled update story makes that integration look more fragile than seamless. Confidence in the OS often spills into confidence in the whole ecosystem. (support.microsoft.com)
It also affects Microsoft’s credibility when pitching continuous innovation. The company wants Windows to feel modern, serviceable, and actively improved rather than frozen in a once-a-year cadence. But continuous innovation only works if each step forward is dependable enough that admins are willing to keep walking. One bad step can make the entire path feel slippery. (support.microsoft.com)
The broader opportunity is to turn this incident into a demonstration of better transparency and faster remediation. If Microsoft follows up with a clear root cause, a revised package, and stronger pre-release validation, it can show that the reliability initiative is more than branding. The response matters almost as much as the failure. (blogs.windows.com)
There is also the risk that the error is symptomatic of a larger update pipeline weakness rather than a one-off defect. If the issue turns out to involve packaging, component-store assumptions, or a distribution quirk, then similar problems could recur in later previews. A single paused rollout is manageable; a pattern of paused rollouts is reputationally corrosive. (support.microsoft.com)
April’s Patch Tuesday now carries extra weight because it will be judged not only on its own merits, but also against the backdrop of this paused preview. If Microsoft can land the next cumulative update cleanly, the company can argue that the system is improving. If not, the narrative of a reliability push will continue to collide with real-world servicing failures. (support.microsoft.com)
For now, KB5079391 is a reminder that Windows reliability is still a work in progress, even when the features are interesting and the intentions are sound. Microsoft may yet resolve the issue and move on, but the story it tells today is familiar: the update system is becoming more ambitious, while the trust required to ship that ambition remains fragile. That is the gap Redmond still has to close.
Source: theregister.com Microsoft pulls Windows update after installation problems
 Background
Background
Microsoft’s Windows servicing model has long revolved around a predictable monthly rhythm: a security-heavy Patch Tuesday release, followed by optional preview updates that let interested users and administrators test fixes and features before they become part of the next security cumulative update. KB5079391 fits squarely into that second category. It was released on March 26, 2026 as a non-security preview for Windows 11 versions 24H2 and 25H2, and Microsoft described it as carrying production-quality improvements. (support.microsoft.com)That wording matters because preview updates occupy a gray zone in user perception. They are optional, but they are not throwaway builds. Microsoft’s own support page frames them as releases that are meant to preview the next month’s security update content, which makes a failed rollout more embarrassing than a simple lab-only bug. In practice, users installing these updates are often the ones trying to stay current, validate hardware, or catch improvements early. (support.microsoft.com)
The current episode also follows a separate out-of-band update, KB5085516, which Microsoft shipped on March 21, 2026 to address Microsoft account sign-in problems introduced by the March 10 update. That sequence reinforces a familiar Windows pattern: a base update, an emergency follow-up, and then a preview release that itself needs to be paused. For enterprise admins, that is not a catastrophic story, but it is absolutely a confidence story. (support.microsoft.com)
Microsoft has publicly been trying to reposition Windows reliability as a priority. In a March 20 blog post, Windows chief Pavan Davuluri told Insiders, “Thank you for holding us to a high standard,” while promising that the company is committed to strengthening the platform’s foundation. That makes this latest pause feel less like a routine servicing hiccup and more like an immediate test of whether that promise is translating into fewer user-visible failures. (blogs.windows.com)
The fact that the problem was caught at install time is important. According to Microsoft’s support page, the affected update did not appear to break devices after installation, because the failure happened before the update could be applied. That distinction won’t comfort users who hit the error, but it does mean this is not a destructive outage in the way some past Windows updates have been. That is a relief, but only a partial one. (support.microsoft.com)
What Microsoft Says Happened
Microsoft’s support entry for KB5079391 is unusually direct for a paused rollout. Under “Known issues,” the company says the rollout is temporarily paused due to installation error 0x80073712 and adds that some devices may encounter the message: “Some update files are missing or have problems. We’ll try to download the update again later.” Microsoft further states that it has temporarily limited availability while the issue is investigated. (support.microsoft.com)That message is consistent with a class of Windows servicing problems that usually point toward component store corruption, missing files, or a package composition problem somewhere in the update chain. Microsoft does not disclose the exact root cause on the support page, which is unsurprising, but it also means users and admins are left to infer whether the fault is in the package metadata, the staging mechanism, or a backend distribution issue. The company is acknowledging the symptom, not the mechanism. (support.microsoft.com)
Why 0x80073712 matters
The 0x80073712 code has a long history in Windows troubleshooting, and Microsoft’s own support materials often associate similar update failures with damaged component store files. In the practical world, that means a failed update might be caused by the device, the package, or both, which makes broad support messaging difficult. For end users, the result is the same: the update does not install, and Windows suggests trying again later.There is a subtle but important distinction here. A failed installation error is much less severe than a regression that bricks a machine, but it is still a signal that the update pipeline is not resilient enough. When Microsoft pauses a preview update, it is usually trying to avoid compounding the problem by pushing the same package to more machines before understanding whether the issue is localized or systemic. (support.microsoft.com)
- The update was optional, not mandatory.
- The rollout was paused, not canceled outright.
- The error occurred before installation completed, which reduced the risk of damage.
- Microsoft has not named a root cause, at least not yet.
- Affected systems are Windows 11 24H2 and 25H2, the current mainstream client branches. (support.microsoft.com)
How Microsoft framed the response
Microsoft’s wording is telling. The company says it has temporarily limited the availability of this update to prevent additional impact while investigation continues. That is classic servicing language, but it also signals that the company is treating the problem as distribution-wide enough to justify pulling back the release, rather than leaving it on offer and instructing users to manually retry. (support.microsoft.com)That approach is sensible because preview updates are as much about confidence as functionality. If a non-security optional update cannot reliably install, then it ceases to serve its intended role as a testbed for quality improvements. In that sense, the pause is not just damage control; it is also Microsoft preserving the credibility of its update channel. A preview that can’t preview is worse than no preview at all. (support.microsoft.com)
What KB5079391 Was Supposed to Deliver
The irony of this incident is that KB5079391 was not a trivial package. Microsoft’s release notes list a wide range of improvements across Settings, File Explorer, Display, Voice Access, Start menu behavior, Remote Desktop, Audio, Windows Hello, and servicing-related reliability. In other words, this was the kind of update Microsoft wants users to notice for the right reasons: not just bug fixes, but platform polish. (support.microsoft.com)Among the headline items, Microsoft said the update lets monitors report refresh rates higher than 1000 Hz, improves HDR reliability for displays with non-compliant DisplayID 2.0 blocks, and enhances reliability around opening the Settings home page and downloading required updates. It also includes changes for narrator voices, file blocking in File Explorer, and safe mode taskbar loading. That is a lot of surface area for one preview release. (support.microsoft.com)
The feature mix tells a story
This update’s contents show how broad Windows servicing has become. Microsoft is not just fixing a single bug or one product area; it is tuning the shell, display stack, input accessibility, remote desktop behavior, and installer pipeline all in one monthly cycle. That creates more opportunity for regression, but it also reflects the reality that modern Windows is an ecosystem of interdependent subsystems. (support.microsoft.com)The display changes are especially interesting because they hint at the pace of hardware evolution. Support for monitors above 1000 Hz is niche today, but it signals that Microsoft wants Windows to be ready for extreme gaming and high-refresh professional displays before the market fully normalizes them. That is forward-looking engineering, even if most users will never see the benefit directly. (support.microsoft.com)
- Settings received reliability and usability improvements.
- File Explorer gained better handling for internet-downloaded files.
- Display got higher refresh-rate reporting and improved HDR behavior.
- Voice Access and Narrator got accessibility-related refinements.
- Windows Hello fingerprint reliability was improved on certain devices. (support.microsoft.com)
Why preview releases matter
Optional preview updates are often dismissed as “just optional,” but they are critical to Microsoft’s servicing strategy. They allow Redmond to test fixes in the wild, surface compatibility issues, and roll known-good improvements into Patch Tuesday. If the preview channel becomes unreliable, the entire monthly cadence loses one of its best pressure valves. (support.microsoft.com)The pause on KB5079391 is especially awkward because Microsoft explicitly markets these updates as production-quality. That phrase is meant to reassure users that preview does not mean experimental. When the package itself is then blocked due to installation issues, the marketing language starts to sound aspirational rather than operational. (support.microsoft.com)
The Reliability Problem Microsoft Wants to Leave Behind
This latest hiccup lands in the middle of a larger campaign by Microsoft to present Windows as more dependable. The company has been talking openly about quality, and Davuluri’s recent Insider note was unusually self-aware, thanking users for holding Microsoft to a high standard. The phrase suggests a cultural reset, but the servicing calendar keeps producing reminders that the reset is still in progress. (blogs.windows.com)That tension is not unique to Microsoft. Operating system updates are inherently risky because they touch everything from drivers to network stacks to security policies. But Windows carries a special burden because it powers both consumer machines and fleet-managed enterprise endpoints, where even a minor update problem can ripple into help desk tickets and delayed deployments. (support.microsoft.com)
A pattern users notice
What frustrates users is not one isolated failure, but the perception of recurrence. In March alone, Microsoft had to address a Microsoft account sign-in bug with an out-of-band update and then pause a preview release because of installation errors. Even if the issues are unrelated technically, the user experience is cumulative. Each episode reinforces the belief that Windows updates are something to be managed cautiously rather than welcomed eagerly. (support.microsoft.com)That perception matters because trust is an operational asset. If users delay updates out of fear, Microsoft has to work harder to achieve coverage, which in turn increases exposure windows for security fixes. So a failed optional update can have consequences beyond the direct bug itself. Reliability is not just a quality metric; it is a delivery mechanism for security. (support.microsoft.com)
- Trust affects how quickly users apply security updates later.
- Reliability issues create support burden for enterprises.
- Repeated pauses make preview channels feel less authoritative.
- Delayed adoption can fragment the installed base.
- Fragility in the update pipeline affects Microsoft’s broader platform credibility. (support.microsoft.com)
Consumer versus enterprise impact
For consumers, the immediate impact is mostly annoyance. If the update fails before installation, the device stays functional and users are mostly left with a retry loop and a confusing error message. For enterprises, however, the implications are broader because admins must decide whether to hold back deployment, adjust rings, or wait for Microsoft to restore availability. (support.microsoft.com)Enterprise teams are also more likely to care about the update’s bundled changes, especially reliability improvements in Settings, Remote Desktop, and the servicing stack itself. When the update is blocked, those improvements remain out of reach, which can prolong known pain points and complicate validation schedules. The biggest cost is often not the failure itself, but the delay it forces downstream. (support.microsoft.com)
The Broader March 2026 Update Chain
To understand why this pause feels so significant, it helps to look at the update chain around it. On March 10, 2026, Microsoft released KB5079473, the monthly security update for Windows 11 versions 24H2 and 25H2. That release later required an out-of-band fix, KB5085516, after Microsoft account sign-in issues were reported. KB5079391 then arrived as the preview release on March 26, only to be paused days later.This sequence illustrates the challenge of modern Windows servicing: security deadlines, hotfix urgency, and optional feature staging all happening in parallel. Microsoft is trying to keep the pipeline moving while also preventing one issue from cascading into another. But when multiple update events appear in close succession, each one makes the next one harder to trust.
Why the timing is bad
The timing is especially sensitive because April Patch Tuesday is approaching. Optional previews are supposed to give Microsoft an opportunity to validate improvements before they become part of the next mandatory update cycle. If the preview itself is unstable, the company risks entering the next month with less confidence in its rollout readiness. (support.microsoft.com)There is also a communication issue. Microsoft’s support page says additional information will be shared when available, but users are rarely patient with vague servicing language. They want to know whether the issue is widespread, whether reinstalling helps, and whether the update will return in the same form or as a revised package. Silence in a servicing incident tends to be interpreted as uncertainty, even when engineers are simply still investigating. (support.microsoft.com)
- March 10: security update KB5079473.
- March 21: out-of-band fix KB5085516 for Microsoft account sign-in.
- March 26: preview update KB5079391.
- Late March: rollout paused due to 0x80073712.
- Early April: Patch Tuesday pressure rises.
Preview updates are supposed to reduce surprises
The preview channel exists to make Patch Tuesday less surprising, not more. By staging fixes early, Microsoft hopes to catch compatibility issues before they hit the broader population. When a preview release itself must be pulled, the intended safety net has failed in a very visible way. (support.microsoft.com)That said, pulling the update is also evidence that Microsoft’s internal and external monitoring is working. It is better to pause a flawed package than to keep shipping it in the hope that the problem stays hidden. The hard part is not deciding to pause; it is avoiding the pattern that requires pausing too often. (support.microsoft.com)
What the Error Means for Users
For most affected users, the practical effect is simple: the update fails, Windows retries, and the package may disappear from offer while Microsoft investigates. Because the failure occurs during installation, systems are not being destabilized by partially applied changes, which is the silver lining in an otherwise frustrating episode. (support.microsoft.com)Still, the error can be confusing because the phrasing suggests missing or damaged files, which can make users think their machines are broken. That can prompt unnecessary cleanup attempts, system restore experiments, or frantic online searches. The average user does not differentiate between a bad update payload and a local component store problem; they just see Windows failing. (support.microsoft.com)
What users should infer, not assume
Users should infer that Microsoft is treating the issue as widespread enough to justify pausing the rollout, but they should not assume their own machine is defective. That distinction is important because the same error code can appear in different contexts. Microsoft’s support page is talking about this specific preview update, not issuing a universal verdict on the health of every affected PC. (support.microsoft.com)Administrators will likely interpret the pause more conservatively. If a deployment is already in progress, they may freeze rings, hold off on manual installation, or wait for a revised release before resuming rollout. That is especially true in managed environments where change control matters more than curiosity about a preview feature. (support.microsoft.com)
- Home users may simply wait for the update to reappear.
- Power users may try manual installation, but the rollout pause could still block availability.
- IT admins will likely suspend deployment rings.
- Help desks may see questions about 0x80073712 and missing files.
- Enterprise teams may prioritize the next security update over the preview entirely. (support.microsoft.com)
The human side of update failure
There is also a psychological effect. Every failed update chips away at the assumption that “checking for updates” is a routine act, not a risk event. Users who hit repeated errors become more likely to delay future maintenance, and that hesitation can linger long after Microsoft resolves the immediate issue. That’s how a temporary bug becomes a durable trust problem. (support.microsoft.com)Microsoft’s Servicing Stack and Why It Matters
Buried in the KB5079391 page is one of the more important details: the update includes KB5079387, a servicing stack update. Microsoft describes the servicing stack as the component that installs Windows updates, and it emphasizes that SSUs are meant to keep the update mechanism robust and reliable. That makes the irony of an SSU-bundled package hitting installation trouble even sharper. (support.microsoft.com)The servicing stack is the plumbing behind Windows Update. Users rarely think about it until something goes wrong, but every cumulative update depends on it. If the pipeline misbehaves, even a well-crafted package can fail to stage correctly. That is why Microsoft keeps adding SSU updates alongside LCUs: the company knows the installer itself is part of the product experience. (support.microsoft.com)
Why this is more than a technical footnote
When an update includes servicing stack improvements but still fails to install on some systems, it undercuts the idea that each monthly release is tightening the system’s reliability. Microsoft may be improving the internals incrementally, but the end-user experience still depends on flawless coordination between package metadata, component store state, and delivery infrastructure. Windows Update is only as strong as its weakest dependency chain. (support.microsoft.com)The support page also shows that Microsoft still expects advanced users and admins to use catalog downloads, DISM, and WUSA in some circumstances. That is useful for controlled environments, but it also underscores how complex Windows servicing remains. The more manual escape hatches there are, the more obvious it becomes that the default experience has not fully earned one-click trust. (support.microsoft.com)
- SSUs are foundational to update reliability.
- LCUs and SSUs increasingly ship together.
- Manual install options remain part of the recovery path.
- Complex servicing flows raise the odds of edge-case failures.
- A paused rollout can be a sign that Microsoft is protecting the servicing stack’s reputation. (support.microsoft.com)
Competitive and Market Implications
At first glance, a Windows preview update failure might seem like a niche story. In reality, it sits at the center of Microsoft’s broader platform credibility, which affects not only consumer sentiment but also enterprise procurement, support costs, and the comparative appeal of alternative operating environments. If Windows updates are seen as unpredictable, that becomes a quiet but persistent sales argument for rival platforms and device management models. (support.microsoft.com)This is especially relevant in hybrid workplaces, where the operating system is just one layer of a larger device strategy. A stable Windows update story helps Microsoft sell the notion that it can manage endpoints, identities, and productivity services as an integrated stack. A troubled update story makes that integration look more fragile than seamless. Confidence in the OS often spills into confidence in the whole ecosystem. (support.microsoft.com)
The enterprise lens
Enterprise buyers care less about the novelty of monitor refresh rates and more about predictable deployment behavior. A failed preview update means more caution around rings, more validation work, and potentially more reluctance to embrace “get the latest updates as soon as they’re available” settings. That may sound minor, but multiplied across large fleets, it alters how Microsoft’s own release strategy is consumed in the field. (support.microsoft.com)It also affects Microsoft’s credibility when pitching continuous innovation. The company wants Windows to feel modern, serviceable, and actively improved rather than frozen in a once-a-year cadence. But continuous innovation only works if each step forward is dependable enough that admins are willing to keep walking. One bad step can make the entire path feel slippery. (support.microsoft.com)
- Better reliability helps Microsoft defend its ecosystem.
- Update failures increase the appeal of delayed rollout strategies.
- Enterprise customers may become more conservative with preview channels.
- Support burden rises when update trust declines.
- Productivity and identity services are indirectly affected by OS confidence. (support.microsoft.com)
Strengths and Opportunities
Despite the embarrassment, Microsoft still has a few strengths to lean on here. The company detected a problem quickly enough to pause the release, its support page is explicit about the error, and the update itself contains genuinely useful fixes and improvements rather than cosmetic changes. That gives Microsoft room to recover without rewriting the whole servicing story from scratch. (support.microsoft.com)The broader opportunity is to turn this incident into a demonstration of better transparency and faster remediation. If Microsoft follows up with a clear root cause, a revised package, and stronger pre-release validation, it can show that the reliability initiative is more than branding. The response matters almost as much as the failure. (blogs.windows.com)
- Microsoft can use the pause to reinforce a quality-first message.
- The update contains real value, so users have reason to come back.
- Clearer incident communication would improve trust.
- Stronger validation could reduce future preview regressions.
- The servicing stack work may still pay off in later releases.
- The company can show it is willing to halt bad rollouts rather than force them through.
- Enterprise teams may appreciate the caution if follow-up guidance is solid. (support.microsoft.com)
Risks and Concerns
The main risk is that this becomes another data point in a long memory of Windows update oddities. Even if KB5079391 is ultimately fixed quickly, users remember the failure mode more vividly than the correction. That is especially dangerous when Microsoft is asking people to trust a monthly release cadence that blends security, features, and servicing improvements. (support.microsoft.com)There is also the risk that the error is symptomatic of a larger update pipeline weakness rather than a one-off defect. If the issue turns out to involve packaging, component-store assumptions, or a distribution quirk, then similar problems could recur in later previews. A single paused rollout is manageable; a pattern of paused rollouts is reputationally corrosive. (support.microsoft.com)
- Repeated update failures erode user patience.
- Help desks may face more support calls about installation errors.
- Enterprises may avoid preview channels altogether.
- Security update adoption can slow if trust declines.
- Microsoft’s quality messaging can sound disconnected from lived experience.
- The issue may hint at broader servicing fragility.
- Users may conflate this failure with unrelated Windows problems. (support.microsoft.com)
Looking Ahead
The next step is straightforward in theory and complicated in execution: Microsoft needs to diagnose the cause, restore the rollout, and explain what changed. If the company ships a revised package, the key question will be whether it simply bypasses the error or genuinely resolves the underlying condition that caused 0x80073712 in the first place. (support.microsoft.com)April’s Patch Tuesday now carries extra weight because it will be judged not only on its own merits, but also against the backdrop of this paused preview. If Microsoft can land the next cumulative update cleanly, the company can argue that the system is improving. If not, the narrative of a reliability push will continue to collide with real-world servicing failures. (support.microsoft.com)
What to watch
- Whether Microsoft publishes a clearer root-cause explanation.
- Whether KB5079391 reappears unchanged or as a revised package.
- Whether installation error 0x80073712 shows up elsewhere in March or April servicing.
- How enterprises respond in deployment rings and update policies.
- Whether the next Patch Tuesday reflects lessons learned from this pause. (support.microsoft.com)
For now, KB5079391 is a reminder that Windows reliability is still a work in progress, even when the features are interesting and the intentions are sound. Microsoft may yet resolve the issue and move on, but the story it tells today is familiar: the update system is becoming more ambitious, while the trust required to ship that ambition remains fragile. That is the gap Redmond still has to close.
Source: theregister.com Microsoft pulls Windows update after installation problems