Kepware’s twin releases — a new Linux, container-first runtime called Kepware Edge and a consolidated Windows product rebranded as Kepware Server — mark a deliberate shift in how industrial connectivity vendors are responding to the demands of edge-first, data-driven manufacturing. The changes promise easier scaling, centralized oversight with Kepware+ Manager, and tighter security posture for both greenfield container deployments and mature Windows estates, but they also introduce migration friction, certificate and interoperability challenges, and new operational responsibilities for IT/OT teams.
Industrial organizations have spent the last decade trying to reconcile two conflicting trends: vast installed bases of Windows-hosted connectivity stacks and a rapid move toward containerized, Linux-based edge compute that supports orchestration, improved deployment velocity, and modern DevOps practices. Kepware’s announcement addresses both realities at once: a purpose-built containerized Linux runtime for distributed, edge-first use cases, and a consolidated Windows server to simplify migrations for customers who remain Windows-first. This dual approach recognizes that the path to digital transformation is heterogeneous and often incremental.
Adopt the following playbook:
Kepware’s two-pronged release is a recognition that industrial connectivity must be both modern and practical: containerized where agility and scale matter, and unified and managed where stability and backward compatibility remain paramount. The technical foundations are sound, but the return on investment will depend on strong PKI governance, orchestration maturity, and disciplined migration execution.
Source: ARC Advisory Group Kepware Introduces Kepware Edge and Kepware Server for Modern Industrial Connectivity
 Background: why this matters now
Background: why this matters now
Industrial organizations have spent the last decade trying to reconcile two conflicting trends: vast installed bases of Windows-hosted connectivity stacks and a rapid move toward containerized, Linux-based edge compute that supports orchestration, improved deployment velocity, and modern DevOps practices. Kepware’s announcement addresses both realities at once: a purpose-built containerized Linux runtime for distributed, edge-first use cases, and a consolidated Windows server to simplify migrations for customers who remain Windows-first. This dual approach recognizes that the path to digital transformation is heterogeneous and often incremental. Overview of the releases
Kepware Edge — containerized industrial connectivity for Linux
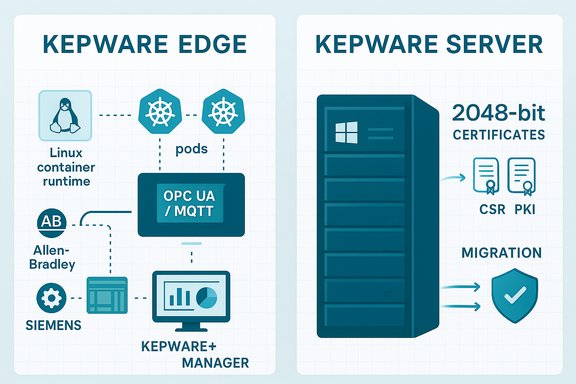
Kepware Edge is introduced as a Linux-based, containerized connectivity server designed to run in distributed environments where portability, orchestration, and low operational overhead matter. The product is packaged for container deployment and exposes a configuration API and remote management through Kepware+ Manager, making it suitable for modern Kubernetes or edge-device orchestrations. The initial driver and interface set targets high-value cores of industrial automation: Allen‑Bradley ControlLogix, Siemens TCP/IP, Modbus Ethernet, OPC UA Server interface, and MQTT client integration via IoT Gateway plug‑ins. The Edge product also exposes event logs, audit capabilities, and a transaction log through the configuration API to meet governance and troubleshooting requirements. Key technical highlights:- Containerized Linux runtime designed for distributed factory and edge deployments.
- Initial device drivers for common PLCs (Allen‑Bradley ControlLogix, Siemens TCP/IP, Modbus Ethernet).
- Client interfaces include OPC UA Server and MQTT (via IoT Gateway), plus ThingWorx native integration.
- Management and governance via the Configuration API and Kepware+ Manager, with audit and transaction logging.
Kepware Server — unified Windows platform
Kepware Server consolidates KEPServerEX and ThingWorx Kepware Server into a single Windows-based product line. The consolidation simplifies the product portfolio, provides a common upgrade path, and centralizes security and certificate handling. Notable updates include support for Windows Server 2025, defaulting instance certificates to 2048‑bit keys on new installs, improved certificate import/export APIs, and migration tooling to carry Program Data forward from older installations. The product also drops legacy interfaces (for example, removal of the deprecated OPC .NET / OPC XI interface) and formally classifies KEPServerEX 5.x as legacy and unsupported. Important technical points:- Unified, single Windows server architecture combining previous KEPServerEX and ThingWorx products.
- Support for Windows Server 2025 and an installer option to migrate existing Program Data.
- Default issuance of 2048‑bit instance certificates in the 7.x series with APIs for certificate import and CSR support.
- Removal of older OPC .NET (OPC XI) interface and deprecation of older 5.x series.
Kepware+ Manager — single control plane
Kepware+ Manager has been updated to manage both Kepware Edge and Kepware Server, providing a centralized control plane to oversee distributed deployments. The Manager adds remote configuration, project backup and restore capabilities, audit logs, and the ability to apply configuration changes across edge and server instances. This centralized management is critical for scaling deployments and maintaining operational governance across hybrid estates.What Kepware is solving — strengths and practical benefits
1) A pragmatic dual-track modernization strategy
Kepware’s two-pronged approach acknowledges the reality that industrial estates are mixed: some sites will adopt containerized, Linux-based edge nodes while many others will stay on Windows for years because of existing toolchains, vendor support expectations, or regulatory constraints. Providing both a container-first Edge and a consolidated Windows Server eases procurement and migration planning. This reduces the “rip-and-replace” pressure and allows customers to adopt an incremental modernization path.2) Containerization brings operational advantages
Containerized deployments reduce variability between environments, enable repeatable CI/CD pipelines, and allow orchestration (for example, Kubernetes at the plant edge) to deliver consistent rollouts, scaling, and lifecycle management. For organizations building pipelines for digital transformation and AI-driven analytics, containers enable rapid, automated deployment of connectivity services closer to data sources. Kepware Edge’s container model fits this emerging architecture.3) Protocol breadth and practical interoperability
The initial driver set covers the most commonly encountered PLC fleets and legacy protocols — Allen‑Bradley, Siemens, and Modbus — alongside enterprise-friendly client interfaces such as OPC UA and MQTT. This mix lets Kepware act as the canonical translator between OT devices and cloud or analytics platforms, reducing the number of bespoke gateways or custom adapters operators must maintain. The ThingWorx interface keeps PTC’s analytics/IoT integrations straightforward.4) Governance and security improvements
Kepware Server’s move to 2048‑bit instance certificates by default, together with explicit APIs for importing certificates and CSRs, demonstrates a focus on PKI hygiene and more modern cryptographic defaults. Audit logging, event logs, and configuration transaction logs — surfaced both via the configuration API and Kepware+ Manager — support compliance and forensic needs. These are nontrivial for regulated manufacturing environments.5) Centralized management for scale
Kepware+ Manager as a central control plane allows administrators to roll configuration changes, manage certificate lifecycles, and push tag normalization or conditional monitoring rules across a fleet. This is essential for industrial digital-transformation programs where repeatability and consistency across multiple sites are required to realize ROI.Critical analysis: where the announcement shines and where caution is warranted
Strengths — solid, necessary engineering
- Modern deployment model: Containerization is the right architectural step for scaling OT connectivity across edge clusters and enabling automated lifecycle operations. Kepware Edge fills a market need for a standardized, vendor-backed containerized connector.
- Portfolio rationalization: Consolidating Windows products into Kepware Server reduces product fragmentation and lowers administrative burden when planning upgrades. The migration tooling in the installer demonstrates operational practicality.
- Security-first defaults: Moving to 2048‑bit certificates and exposing PKI APIs shows an emphasis on stronger cryptographic defaults and manageability — a welcome step for OT environments increasingly targeted by adversaries.
- Management parity: Extending Kepware+ Manager to cover both Edge and Server creates a single pane of glass for hybrid estates, which is essential for controlled scale.
Risks and operational trade-offs — what IT and OT teams must weigh
- Certificate migration friction: Because Kepware Server 7.x defaults new instance certificates to 2048‑bit keys, upgrades from older versions will require explicit migration steps and client trusts to be updated. In complex estates, failing to plan certificate trust rollover can break production integrations. The release notes explicitly warn administrators to consult the Migration Guide and prepare for client-side trust changes. This is a real operational risk during upgrades.
- Container orchestration demands: Containerizing the connectivity layer shifts some operational burden from Windows desktop/host patching to container orchestration and Linux-based lifecycle operations. Organizations without Kubernetes or container-management expertise will need to upskill or engage integrators to manage edge clusters, networking, and offline resilience. Kepware Edge is optimized for that model, but customers must invest in orchestration tooling and observability.
- Legacy protocol and driver gaps: The initial Edge driver set is practical but not exhaustive. Many industrial sites rely on a long tail of niche drivers and specialized interfaces; these will need staged support or fallbacks to Windows-based servers until feature parity is achieved. Kepware’s roadmap signals additional drivers (OPC UA Client, Siemens S7 Plus, Mitsubishi) are planned, but organizations must validate whether critical drivers are available before wholesale migration. Where those claims are listed as future items, treat them as roadmap intentions rather than guaranteed deliverables.
- Vendor and architectural lock‑in: Adopting Kepware+ Manager as the centralized control plane and tightly coupling services to Kepware Server/Edge can accelerate operations, but it increases dependency on PTC-managed tooling and licensing. For multi-vendor, multi-cloud strategies, customers should clarify migration/export paths, API openness, and exit strategies.
- Operational complexity of distributed connectivity: More distributed points of connectivity increase the surface for outages, misconfiguration, and security exposure. Effective deployment requires robust PKI, strict network segmentation, and tight IAM mapping between OT and IT. Kepware’s audit and logging features help, but they’re tools — not a substitute for organizational processes and runbooks.
Practical migration and deployment guidance
1. Plan a phased pilot
- Identify a single high-value production line or pilot site with a well-understood PLC estate and clear KPIs (MTTR, data latency, quality yield).
- Validate that required device drivers exist in Kepware Edge; if not, confirm whether Kepware Server on Windows will bridge those devices during a phased migration.
2. Certificate and PKI playbook
- Audit existing instance certificates and client trust stores before upgrading any Windows servers to Kepware Server 7.x. Expect to import new 2048‑bit certificates or update trust anchors on clients; consult the Migration Guide. Test certificate rollovers in a staging environment to avoid surprise production disruptions.
3. Build container/edge operational capabilities
- Deploy a small container orchestration footprint (for example, an Arc-enabled Kubernetes or lightweight edge Kubernetes distribution) and validate offline behaviors, secret/Key Vault integration, and automated agent updates. Ensure your observability stack captures container logs, audit events, and configuration transactions that Kepware surfaces.
4. Centralize configuration and governance
- Use Kepware+ Manager to manage projects, enforce backups, and centralize audit logs. Implement an approvals policy and change control that maps configuration changes in Kepware+ Manager to plant‑floor change windows. Back up projects and validate restore procedures regularly.
5. Harden network and identity
- Enforce segmentation between OT control networks and corporate IT, implement least-privilege service identities, and adopt automated certificate rotation where possible. Treat remote management channels (Kepware+ Manager, configuration API) as high-value assets and protect them with multi-factor access controls, IP allow lists, and private endpoints.
Roadmap and vendor commitments — what to watch for
Kepware has signalled continued expansion of protocol coverage and the Edge driver catalog. The vendor lists potential future additions such as OPC UA Client functionality, Siemens S7 Plus, and Mitsubishi drivers, along with improvements to containerized deployment workflows and configuration management. These are logical next steps to reach feature parity with mature Windows offerings, but they must be verified against published release notes before making migration decisions that depend on them. Customers should track release notes and Kepware+ Manager support updates to validate delivery timelines.Security posture: improvements and residual responsibilities
Kepware’s moves to modernize certificate handling and surface audit logs are positive. Defaulting to stronger certificate keys and adding APIs for certificate import/export and CSRs reduces manual key management friction. Kepware+ Manager’s audit and backup features provide better forensic posture for distributed deployments. However, the company’s enhancements do not remove the need for strong organizational cybersecurity practices: network segmentation, robust PKI policies, least‑privilege access, and independent security auditing remain essential. The most serious upgrade risk comes from certificate trust changes and improperly sequenced rollouts that temporarily break trusted connections. Plan upgrades, perform staged certificate trust updates, and validate failover and client reconnection behavior.What this means for Windows-first customers
For enterprises that operate primarily in Windows environments, Kepware Server provides a clearer migration path by consolidating previous product lines and adding migration options in the installer (Program Data migration, assisted upgrade flags). The Windows Server 2025 support is practical for data centers that standardize on that platform. Still, administrators should note the removal of legacy OPC .NET interfaces and the deprecation of KEPServerEX 5.x — these changes require pre-upgrade inventories to ensure no unsupported interfaces remain in critical projects.Vendor analyst perspective and market signal
Industry analysts see Kepware Edge as part of a broader trend: the industrial connectivity layer is evolving to meet AI-driven manufacturing and distributed analytics needs. ARC Advisory Group’s commentary highlighted Kepware Edge’s containerized architecture and protocol support as foundational for secure, scalable data flows in AI-enabled factories. Analysts frame this as an enabling, not immediate, step toward “future-ready” smart manufacturing; the real gains hinge on robust rollout plans and operational governance. Analyst endorsements can help validate the technical direction, but buyers should still demand pilot metrics and SOW-based guarantees for measurable outcomes.Bottom line — recommendation for IT/OT decision makers
Kepware’s Edge and Server releases are an important, pragmatic step toward hybrid modernization of industrial connectivity. The package addresses both the need for containerized, orchestration-friendly edge runtimes and the reality of large Windows-installed bases that require controlled migration. The combination of strengthened certificate practices, centralized Kepware+ Manager capabilities, and initial driver coverage makes the offering compelling for organizations planning multi-site digital transformation.Adopt the following playbook:
- Run a focused pilot that exercises the exact drivers and interfaces you need. Validate resilience, certificate handling, and monitoring.
- Plan certificate migration with conservative sequencing and clear rollback procedures. Expect to update client trust stores during upgrades to Kepware Server 7.x.
- Invest in edge orchestration capabilities or partner with integrators for container lifecycle operations. Kepware Edge’s benefits are realized only when orchestration and observability are in place.
- Use Kepware+ Manager to standardize project backups, policy enforcement, and bulk configuration changes, but maintain governance controls and runbooks around changes.
Kepware’s two-pronged release is a recognition that industrial connectivity must be both modern and practical: containerized where agility and scale matter, and unified and managed where stability and backward compatibility remain paramount. The technical foundations are sound, but the return on investment will depend on strong PKI governance, orchestration maturity, and disciplined migration execution.
Source: ARC Advisory Group Kepware Introduces Kepware Edge and Kepware Server for Modern Industrial Connectivity