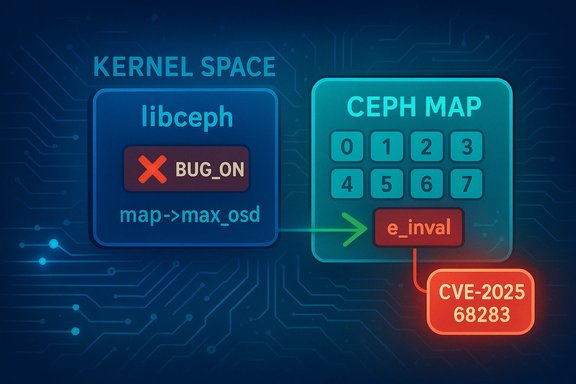
A quiet but consequential fix landed in the Linux kernel tree on December 16, 2025: a defensive coding change in the Ceph client library (libceph) replaced several fatal assertions with proper bounds checks to block untrusted OSD indexes from network packets — a change recorded as CVE-2025-68283 and classified by vendors as an important-to-moderate kernel vulnerability. The patch removes dangerous BUG_ON assertions in ceph_get_primary_affinity and related code paths and substitutes explicit checks against map->max_osd, closing an out‑of‑bounds access vector that could lead to memory corruption or denial-of-service in systems processing malicious or malformed Ceph map updates.
Ceph is widely used as an open‑source, distributed object and block storage system. The kernel’s libceph contains code used by kernel clients to consume Ceph monitor and OSD (object storage daemon) maps received from the network. Those maps contain lists of OSD indexes and associated metadata that the client uses to route IO and maintain cluster state.
The change that triggered the CVE was committed to the kernel’s stable trees in mid‑December 2025. Upstream maintainers removed multiple occurrences of BUG_ON(osd >= map->max_osd) and instead added explicit checks that validate OSD indexes decoded from network packets. Where an index is out of range, the code now jumps to an error path (e_inval) instead of triggering a kernel BUG, which would crash the kernel immediately.
Key facts verified against public kernel commits and multiple vulnerability trackers:
Ceph map updates — notably OSD indexes embedded in monitor or OSD map messages — originate from the network and must be treated as untrusted. If those indexes are not validated before use, an attacker who can inject or spoof map messages (or craft malformed packets when an attacker has adjacent network access) could send values that index past array bounds, causing memory corruption or invoking BUG_ON and crashing the machine.
This changes behavior in two important ways:
Recommended steps, in order of priority:
Administrators should treat the CVE as actionable: inventory affected systems, apply vendor kernel updates when available, and harden network boundaries around Ceph control traffic. Developers and reviewers should treat this incident as a reminder to eliminate crash-first assertions from any code path that handles untrusted input, and to invest in fuzzing and rigorous bounds checking for protocol parsers inside the kernel.
The good news is that upstream fixed the logic quickly and in a relatively small patch; the remaining work — getting those fixes into distribution kernels and cloud images — is routine but must be done conscientiously. Systems that are patched will be materially more resilient to malformed Ceph map data and less likely to experience kernel-level denial-of-service or memory-safety issues stemming from unchecked OSD indexes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Ceph is widely used as an open‑source, distributed object and block storage system. The kernel’s libceph contains code used by kernel clients to consume Ceph monitor and OSD (object storage daemon) maps received from the network. Those maps contain lists of OSD indexes and associated metadata that the client uses to route IO and maintain cluster state.The change that triggered the CVE was committed to the kernel’s stable trees in mid‑December 2025. Upstream maintainers removed multiple occurrences of BUG_ON(osd >= map->max_osd) and instead added explicit checks that validate OSD indexes decoded from network packets. Where an index is out of range, the code now jumps to an error path (e_inval) instead of triggering a kernel BUG, which would crash the kernel immediately.
Key facts verified against public kernel commits and multiple vulnerability trackers:
- The commit author and message reference removing BUG_ON checks in ceph_get_primary_affinity and adjacent decoding functions.
- The defensive code added checks of the form: if (osd >= map->max_osd) goto e_inval;
- The CVE identifier CVE-2025-68283 was assigned and publicly listed on December 16, 2025.
- Several distribution security teams and vulnerability feeds categorized the issue as Important/Moderate and began tracking vendor advisories and backporting work.
Why this matters: BUG_ON vs. bounds checks
What BUG_ON does and why it’s dangerous in I/O paths
In kernel code, BUG_ON(condition) is an assertion macro that deliberately crashes the kernel when its condition evaluates true. It’s a blunt instrument useful for catching developer errors during development or flagging impossible conditions in deeply controlled contexts. But in code paths that parse and act on untrusted external input — such as network packets or user-supplied data — invoking BUG_ON gives attackers a reliable mechanism to induce a kernel panic.Ceph map updates — notably OSD indexes embedded in monitor or OSD map messages — originate from the network and must be treated as untrusted. If those indexes are not validated before use, an attacker who can inject or spoof map messages (or craft malformed packets when an attacker has adjacent network access) could send values that index past array bounds, causing memory corruption or invoking BUG_ON and crashing the machine.
The safer pattern: explicit validation
The patch replaces BUG_ON with explicit validation against map->max_osd, verifying that decoded OSD indexes are less than the declared maximum. When a decoded index fails the check, the code gracefully rejects the offending data and returns an error rather than panicking the kernel.This changes behavior in two important ways:
- Eliminates immediate kernel crashes caused by malformed map data.
- Prevents potential out-of-bounds reads/writes that could otherwise lead to memory corruption andUndefined Behavior, possibly exploitable for privilege escalation or arbitrary code execution in extreme circumstances.
Technical analysis of the patch
Where the change was applied
The modifications touch multiple functions in libceph’s map decoding flow:- ceph_get_primary_affinity: removed BUG_ON assertion and uses safe path when map->osd_primary_affinity is absent.
- decode_new_primary_affinity, decode_new_up_state_weight, and other decoding helpers: after decoding OSD indices from the packet stream, the code now performs an explicit bounds check of the form:
- ceph_decode_32_safe(p, end, osd, e_inval);
- if (osd >= map->max_osd) goto e_inval;
Consequences for error handling
Replacing BUG_ON with goto e_inval consolidates error behavior: invalid packets are rejected with a controlled return code rather than destabilizing the entire kernel. This is the correct defensive posture for network-facing decoding logic.Memory safety impact
From a memory-safety perspective, the changes convert a deterministic crash condition into a defensive check that prevents out-of-bounds accesses in array reads and writes that depend on osd indexes. This reduces the attack surface for memory corruption and denial-of-service vectors stemming from malformed Ceph maps.Severity and vendor responses
Severity assessments vary slightly by vendor and database — a typical pattern for newly assigned CVEs while maintainers and downstream vendors evaluate the concrete impact. Public records and vendor trackers show the following picture:- Upstream kernel commit and CVE assignment occurred on December 16, 2025.
- Some vendors and trackers classify the issue as Important (CVSSv3 ~6.3–7.0) while others label it Moderate, reflecting differences in assumed attack vector (local vs. adjacent network) and exploit complexity.
- Major Linux distribution maintainers and cloud vendors listed the CVE in their security feeds and began triage; many indicated "pending fix" status for distribution kernels pending backport or release of updated kernel packages.
- Hosts running kernel-level Ceph clients (e.g., RBD, CephFS mounts).
- Systems that consume and process Ceph monitor/OSD maps from untrusted network segments.
Exploitation potential and realistic threat model
Attack surface
- The vulnerable code consumes OSD indexes from network packets. That makes the most realistic attack vector network-originated map data — i.e., only systems that receive Ceph map updates externally are meaningfully exposed.
- For exploitation, an attacker generally needs to:
- Be on the same Ceph control plane network (adjacent network access), or
- Compromise a monitor or OSD process that can inject crafted maps, or
- Control a component that delivers Machiavellian map data to clients.
Likelihood of remote exploitation
- The change prevents immediate kernel panics caused by malformed data; however, whether memory corruption before the added checks could be exploited to achieve arbitrary code execution is non-trivial and depends on surrounding invariants. Public analysis to date indicates the primary risk is memory-corruption/denial-of-service rather than a straightforward remote root exploit.
- Vendors and trackers have rated the attack complexity as high and privileges required as low to limited, implying exploitation is non-trivial and likely requires adjacency or specific cluster conditions.
Real-world threat summary
- Immediate risk: denial-of-service via kernel panic if a vulnerable kernel still uses BUG_ON in that code path and processes crafted map data.
- Medium-term risk: potential memory corruption leading to data confidentiality or availability issues; exploitation to achieve code execution is plausible but non-trivial and would likely require chaining with other bugs.
Mitigation and guidance for administrators
System administrators and security teams should treat CVE-2025-68283 as an actionable kernel security item for systems that use kernel-level Ceph clients.Recommended steps, in order of priority:
- Inventory: Identify hosts that run kernel-level Ceph clients or mount CephFS/attach RBD devices. These are the systems at risk.
- Patch: Apply vendor-provided kernel updates as soon as they are released. Prioritize kernels where the vulnerable libceph code is present (consult your distro’s advisory or package changelog).
- Isolate: If patching cannot be immediate, restrict network access to Ceph monitor/OSD ports and isolate Ceph client traffic to trusted networks. Reduce the attack surface by ensuring only authorized hosts can supply map updates.
- Monitor: Increase monitoring of kernel oops/panic logs, Ceph client logs, and network anomalies in the Ceph control plane. Look for symptoms like repeated kernel panics, OSD map decode errors, or unexpected drops in CephFS mounts.
- Workarounds: Where timely updates are impossible, consider moving Ceph clients to userspace alternatives (e.g., ceph‑common tools, userspace clients) where feasible, or using supported kernel parameter hardening to reduce attack surface — but be aware these are often partial mitigations.
- Validate: After updating, verify that the kernel package includes the patch (check vendor changelog or kernel git commit inclusion) and run integration tests for Ceph mounts and RBD devices.
Developer and security lessons
Defensive coding in kernel space
This CVE is a textbook example of why assume input is untrusted matters in kernel space. Developers should avoid using crash‑first macros like BUG_ON in any code that operates on external input, especially network‑facing parsers and decoders. Instead:- Use safe decoding primitives that validate buffer boundaries.
- Return controlled errors for malformed input.
- Prefer fail‑closed logic that rejects untrusted values without destabilizing the kernel.
Audit priorities for storage code
Code paths that parse cluster maps, routing tables, or other protocol state from the network deserve targeted code review and fuzzing. Storage stacks often contain complex binary protocols and state machines — both fertile ground for subtle indexing and length‑checking bugs.Backporting and patch distribution
Distributions should adopt a coordinated approach to backporting upstream fixes into their LTS kernels, with transparent advisories that indicate which patched commit was backported. This reduces confusion for administrators trying to assess exposure.What to watch next
- Vendor advisories and kernel package releases: Monitor your distribution’s security portal for the CVE’s status and patched kernel package versions.
- Downstream backports: Some distributions will backport the fix into older kernel series; check changelogs to confirm inclusion.
- Related Ceph CVEs: There were other libceph fixes rolled concurrently in December 2025 for races and potential use‑after‑free conditions; administrators should treat the set of libceph CVEs holistically when planning updates.
- Public exploit code: No public exploit was widely reported at the time of the patch landing, but the presence of easily reproducible crashes can prompt weaponization; a timely patch is the safest course.
Practical checklist for Windows‑adjacent admins running Linux workloads
Many Windows shops that consume Linux-based storage (for example, via virtual machines or container hosts) will need to coordinate with Linux teams. A practical checklist:- Confirm which virtualization hosts or NAS heads mount Ceph storage at the kernel level.
- If kernel patching requires scheduled maintenance, prioritize hosts that expose Ceph control plane traffic to untrusted networks.
- For cloud-hosted Linux VMs that rely on vendor kernel packages, enable automatic security updates or coordinate with cloud vendor advisories to schedule kernel upgrades.
- Validate backups and snapshots before kernel updates; although the patch itself is safe, kernel upgrades carry standard maintenance risks.
Final assessment
CVE-2025-68283 is an important instance of a systemic coding practice being corrected: assertions that crash the kernel were replaced with robust input validation. The immediate technical fix is simple and effective — validate decoded indexes against map->max_osd and reject invalid data — yet the operational implications are meaningful because the change reduces the risk of kernel panic and potential memory corruption on systems processing Ceph maps.Administrators should treat the CVE as actionable: inventory affected systems, apply vendor kernel updates when available, and harden network boundaries around Ceph control traffic. Developers and reviewers should treat this incident as a reminder to eliminate crash-first assertions from any code path that handles untrusted input, and to invest in fuzzing and rigorous bounds checking for protocol parsers inside the kernel.
The good news is that upstream fixed the logic quickly and in a relatively small patch; the remaining work — getting those fixes into distribution kernels and cloud images — is routine but must be done conscientiously. Systems that are patched will be materially more resilient to malformed Ceph map data and less likely to experience kernel-level denial-of-service or memory-safety issues stemming from unchecked OSD indexes.
Source: MSRC Security Update Guide - Microsoft Security Response Center