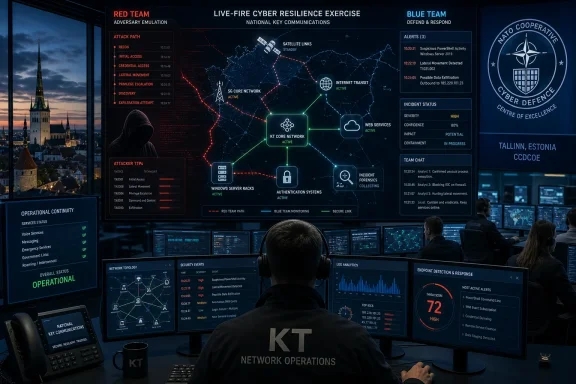
KT said on May 10 that it joined NATO CCDCOE’s Locked Shields 2026 cyber-defense exercise for a second consecutive year, participating as South Korea’s only domestic telecommunications company among 47 Korean civilian, government, and military organizations in the April 20–24 training event. The announcement is easy to file as another corporate security press release, but that would miss the point. A national carrier showing up in a NATO-run live-fire cyber exercise is not just polishing its incident-response résumé. It is a sign that telecom security is being treated less like back-office risk management and more like national resilience under pressure.
Locked Shields has become one of the cyber world’s most elaborate stress tests: a multinational exercise run by the NATO Cooperative Cyber Defence Centre of Excellence in Tallinn, Estonia, built around real-time attacks against simulated national infrastructure. The scenario changes, the fictional country changes, and the scoreboard changes, but the premise is consistent. Defenders must keep systems alive while facing technical compromise, operational confusion, legal constraints, public messaging demands, and the fatigue that comes with a crisis unfolding in real time.
KT’s role matters because telecommunications companies occupy a strange place in modern cyber defense. They are private companies, but their networks behave like public infrastructure. They sell connectivity, but that connectivity underwrites emergency response, cloud access, banking, logistics, military coordination, and almost every supposedly “digital-first” public service.
That is why KT’s framing of the exercise is more interesting than the usual language of participation. The company did not simply say it practiced patching servers or detecting malware. It said it focused on validating an integrated response capability as a national key communications network operator. That phrase may sound bureaucratic, but it is doing heavy lifting: KT is placing itself in the same operational category as power grids, satellite links, identity systems, and command networks.
For WindowsForum readers, the Windows server angle will naturally jump out. KT said it defended areas including satellite communications infrastructure, Windows server security, web service security, and digital forensics and incident response. But the deeper Windows story is not just whether a domain controller was hardened or a server was segmented. It is that Windows remains embedded in the administrative, operational, and hybrid environments that attackers will target when they want to move from “breach” to “disruption.”
That distinction matters. A vulnerability scan tells an organization that a door exists. A red-team operation asks whether an attacker can find the door, open it quietly, move through the building, steal the master keys, and reach the room everyone assumed was isolated. The first is compliance-friendly. The second is uncomfortable by design.
KT says its Red Team works through the full chain: reconnaissance, initial access, privilege escalation, lateral movement, and access to core systems. That language tracks the way modern intrusions actually unfold. The catastrophic part of a breach is often not the first exploit; it is the attacker’s ability to turn one foothold into many, then convert administrative access into operational leverage.
For a telecom carrier, that chain is especially dangerous because “core systems” is not an abstract phrase. It can mean authentication infrastructure, network management platforms, billing systems, cloud environments, customer portals, operational processes, and the trust relationships between them. Attackers do not need to break every system if they can find one path that crosses from corporate IT into a more sensitive operational plane.
The company’s statement that it tests complex attack paths spanning IT, network, authentication, billing, cloud, and operating processes is the part administrators should underline. This is where many real organizations remain weaker than their slide decks suggest. Security teams may have good visibility into endpoints, reasonable controls on web apps, and a documented cloud posture, yet still fail to understand how an attacker could chain small weaknesses across organizational boundaries.
A useful red-team exercise tells defenders where they were blind, where alerts were noisy, where escalation paths were slow, and where assumptions about containment did not survive contact with an adversary. The defender’s job is not to “beat” the red team in a single exercise. It is to become harder to surprise the next time.
This is where Locked Shields is unusually relevant. A live-fire multinational exercise forces participants to defend under artificial but meaningful stress. Teams do not have the luxury of turning every alert into a root-cause analysis seminar. They must triage, communicate, preserve services, and decide what risk is acceptable while other teams and exercise injects complicate the picture.
That is closer to the real world than the tidy incident-response tabletop that ends with everyone agreeing the plan looks solid. In a telecom crisis, the problem is rarely one machine. It is the dependency graph. Which systems must be restored first? Which logs can be trusted? Which credentials are now suspect? Which partner connections should be throttled or severed? Which outage will create cascading public harm?
The telecom operator that understands those dependencies before a crisis has an advantage. The one that discovers them during an attack becomes a spectator in its own network.
The 2026 edition reportedly brought together more than 4,000 cyber defenders from more than 40 nations, with teams defending critical infrastructure in a wartime-style scenario. That scale matters because cyber defense is increasingly coalition defense. No major country, carrier, software vendor, or cloud operator can pretend that its security problems stop at the edge of its own network.
South Korea’s participation is also geopolitically notable. Korea is not a NATO member, but it has deepened cyber cooperation with NATO-aligned institutions over the past several years, and CCDCOE has served as a venue for countries outside the alliance to participate in shared cyber-defense work. KT’s involvement fits that pattern: a private-sector operator participating in a multinational defense exercise because the infrastructure it runs would be part of any serious crisis.
This year KT participated as part of a Korea-Hungary joint team. Last year, according to the company, it joined a Korea-Canada team focused on defending 5G networks and major information and communications infrastructure in a virtual country. That continuity is more important than the pairing itself. One year of participation is exposure. Two consecutive years suggest institutional learning.
The useful question is not whether KT “won.” The useful question is what it brought home. Exercises matter only if their lessons survive the flight back from Tallinn and become changes in architecture, playbooks, tooling, escalation authority, and engineering culture.
That is why the industry’s security posture must be judged differently from that of an ordinary enterprise. A ransomware incident at a retailer can be financially damaging and operationally ugly. A serious compromise at a national carrier can interfere with emergency communications, authentication, roaming, industrial connectivity, public-sector services, and the cloud-dependent businesses riding on top of the network.
The attack surface is also broader than outsiders tend to assume. Telecom networks include legacy systems, virtualized network functions, cloud-native components, identity platforms, customer-facing apps, roaming relationships, vendor management channels, physical infrastructure, lawful intercept obligations, and operational technology-adjacent management systems. The result is not one network but a federation of old and new systems tied together by necessity.
That complexity is exactly what sophisticated attackers exploit. They rarely need cinematic zero-days if they can abuse misconfiguration, stale credentials, exposed management interfaces, over-permissive service accounts, weak segmentation, and delayed detection. In a telecom environment, even small trust mistakes can become large operational problems.
KT’s emphasis on attack paths crossing IT, network, authentication, billing, cloud, and operations is therefore not decorative. It is a sober description of how modern telecom risk actually behaves. The border between “business system” and “critical system” is often thinner than executives would like to admit.
For defenders, this creates a paradox. Windows Server is mature, extensively documented, and supported by an enormous security ecosystem. Yet the very ubiquity that makes it manageable also makes it attractive. Attackers understand the terrain, defenders inherit years of configuration drift, and the blast radius of a compromised privileged account can be enormous.
In a live-fire exercise involving national infrastructure, Windows security is not just about patch levels. It is about whether administrators can detect credential theft, prevent lateral movement, isolate compromised hosts, preserve domain integrity, and continue operating when trust in parts of the environment has collapsed. That is a much harder problem than applying the latest cumulative update.
The Windows community has spent years discussing the right controls: tiered administration, privileged access workstations, multifactor authentication, hardened baselines, attack surface reduction, endpoint detection and response, constrained delegation, certificate authority hygiene, and aggressive logging. The hard part is not knowing that these controls exist. The hard part is implementing them consistently across a sprawling enterprise where business units, legacy apps, and uptime pressures all push back.
Locked Shields-style scenarios punish partial implementation. If a team has logging but no analyst workflow, it drowns. If it has segmentation but undocumented exceptions, attackers find the exceptions. If it has identity controls but too many standing privileges, the attacker’s path remains open. The exercise format forces a blunt question: does the security architecture work as a system, or only as a collection of good intentions?
Satellite communications are no longer a niche backup channel reserved for remote outposts. They increasingly intersect with defense, maritime, aviation, emergency response, and resilient connectivity planning. At the same time, 5G networks have pulled more network logic into software-defined, cloud-oriented architectures. That shift creates flexibility, but it also creates new places for identity, configuration, and management-plane security to fail.
The old telecom mental model treated the network as specialized hardware run by specialized engineers in specialized environments. That model has not disappeared, but it is no longer sufficient. Modern telecom increasingly looks like a hybrid of carrier engineering, cloud operations, enterprise IT, software supply-chain management, and national security planning.
That hybrid reality changes the defender’s job. A security team must understand not only packets and malware, but also orchestration, APIs, CI/CD pipelines, vendor dependencies, identity federation, and operational recovery. It must know how an attacker could pivot from an administrative tool into a network-management function, or from a cloud misconfiguration into a service-impacting outage.
KT’s exercise participation is therefore less about any single technology than about convergence. Satellite, 5G, Windows servers, web services, billing systems, and cloud platforms are not separate worlds during a crisis. They become one contested environment.
Generative AI does not magically turn every low-skill attacker into an elite operator. Real intrusions still require targeting, persistence, operational judgment, infrastructure, and the ability to adapt when defenses behave unexpectedly. But AI can lower friction in meaningful ways. It can help attackers generate phishing variants, summarize stolen documentation, write or modify scripts, triage exposed services, and accelerate reconnaissance.
For defenders, AI is most useful when it compresses repetitive work without replacing human judgment. Vulnerability diagnosis, log summarization, alert enrichment, malware triage, and playbook assistance are all plausible areas where AI can help. The danger is pretending that faster analysis equals better defense if the underlying data is incomplete or the response authority is unclear.
In a telecom environment, AI-assisted defense must also be treated as an operational system with its own failure modes. Models can hallucinate. Automation can amplify mistakes. Sensitive logs and incident data can create privacy and sovereignty concerns if handled carelessly. The more important the network, the less acceptable it is to bolt on AI as a novelty layer.
The more realistic promise is not autonomous cyber defense. It is reducing the time between signal and action. In a live-fire scenario, minutes matter. If AI can help analysts connect weak signals, prioritize likely attack paths, or generate a first-pass incident timeline, it can buy defenders time. But the final measure remains operational: did the service stay up, did the attacker get contained, and did leadership make better decisions?
This trend is not limited to Korea. Across NATO countries and partners, cyber resilience has become a shared burden among militaries, civilian agencies, regulators, vendors, and infrastructure operators. The state may set priorities, issue warnings, and coordinate crisis response, but it cannot directly operate every network, patch every server, or rewrite every recovery plan.
That reality is awkward for companies. Participation in national exercises can improve readiness, but it can also expose uncomfortable gaps. It may reveal that escalation paths are unclear, that executives do not understand technical tradeoffs, that legal approvals are too slow, or that dependencies on suppliers are more brittle than assumed. The value of the exercise is precisely that it creates those discoveries in a survivable setting.
For telecom carriers, the policy pressure will only increase. As networks become more central to defense, emergency management, digital identity, and cloud access, regulators and governments will demand more evidence of resilience. Annual audits and compliance attestations will not be enough. Operators will be expected to prove that they can function under attack.
KT’s second consecutive year at Locked Shields positions the company inside that emerging expectation. The bigger question is whether such participation becomes routine for other major carriers. If telecom networks are national infrastructure, then live-fire rehearsal should not be exceptional. It should be part of the operating model.
This is especially relevant in Windows-heavy and hybrid environments. Many organizations own endpoint tools, SIEM platforms, vulnerability scanners, identity products, backup systems, and cloud security dashboards. The issue is not tool scarcity. It is whether those tools produce a coherent operating picture when an attacker is moving quickly.
Defenders need to know which alerts are trustworthy, which systems are authoritative, and which dashboards reflect reality rather than inventory lag. They need forensic access without destroying evidence, segmentation controls that can be changed quickly but safely, and identity systems that allow emergency privilege management without creating new backdoors. Those needs should shape procurement long before the next breach.
Telecom operators also face a vendor-chain problem that is more complex than most enterprises. Network equipment, operational support systems, cloud providers, software suppliers, and managed service partners all create dependencies. A carrier’s incident-response plan is only as good as the weakest critical dependency it assumes will behave perfectly.
KT’s red-team emphasis suggests it understands that the decisive weakness may be a process, not a product. A billing workflow, an authentication exception, a shared administrative credential, or an undocumented vendor access path can matter as much as an exploitable CVE. The mature security organization looks for those seams before an adversary does.
In a real cyber crisis, government agencies may hold threat intelligence that private operators need. Private operators may hold telemetry that government defenders need. Legal teams may be asked to approve actions at machine speed. Communications staff may need to explain an outage while engineers still do not know the full scope. International partners may be dealing with the same adversary from different legal and political positions.
Those tensions cannot be solved by exchanging business cards during peacetime. They require rehearsed channels, pre-negotiated authorities, trusted contacts, and a shared vocabulary for severity and action. Exercises provide a way to discover where cooperation breaks down before the failure is public.
For Korea, a joint-team format with Hungary this year and Canada last year also has a quiet diplomatic function. Cyber defense cooperation builds relationships that are less visible than military exercises but increasingly important. When the systems at stake include satellites, 5G, Windows servers, and web infrastructure, the divide between civilian and defense technology becomes more procedural than technical.
That is why KT’s presence is significant beyond the company itself. It represents a model in which national carriers are not merely regulated entities waiting for guidance. They are active participants in the rehearsal of national and allied cyber resilience.
That is the right direction. Cybersecurity has spent too many years rewarding documentation over demonstrated performance. Policies are necessary, but attackers do not read them. Compliance is useful, but it is not the same as continuity. A locked-down server is good, but a recoverable service is better.
For Windows administrators, the story lands close to home. The same themes that appear in a national telecom exercise also appear in ordinary enterprises: identity is the prize, lateral movement is the danger, logging without response is noise, segmentation without testing is hope, and backups without restoration drills are decoration. The scale changes, but the logic does not.
The telecom-specific lesson is sharper. A carrier cannot defend only the network layer, only the cloud layer, only the server estate, or only the customer-facing applications. It must defend the paths between them. That is where modern attackers live.
Source: 매일경제 KT announced on the 10th that it has participated in the International Cyber Defense Training "Locks.. - MK
 KT’s Exercise Was a Telecom Story Wearing a NATO Badge
KT’s Exercise Was a Telecom Story Wearing a NATO Badge
Locked Shields has become one of the cyber world’s most elaborate stress tests: a multinational exercise run by the NATO Cooperative Cyber Defence Centre of Excellence in Tallinn, Estonia, built around real-time attacks against simulated national infrastructure. The scenario changes, the fictional country changes, and the scoreboard changes, but the premise is consistent. Defenders must keep systems alive while facing technical compromise, operational confusion, legal constraints, public messaging demands, and the fatigue that comes with a crisis unfolding in real time.KT’s role matters because telecommunications companies occupy a strange place in modern cyber defense. They are private companies, but their networks behave like public infrastructure. They sell connectivity, but that connectivity underwrites emergency response, cloud access, banking, logistics, military coordination, and almost every supposedly “digital-first” public service.
That is why KT’s framing of the exercise is more interesting than the usual language of participation. The company did not simply say it practiced patching servers or detecting malware. It said it focused on validating an integrated response capability as a national key communications network operator. That phrase may sound bureaucratic, but it is doing heavy lifting: KT is placing itself in the same operational category as power grids, satellite links, identity systems, and command networks.
For WindowsForum readers, the Windows server angle will naturally jump out. KT said it defended areas including satellite communications infrastructure, Windows server security, web service security, and digital forensics and incident response. But the deeper Windows story is not just whether a domain controller was hardened or a server was segmented. It is that Windows remains embedded in the administrative, operational, and hybrid environments that attackers will target when they want to move from “breach” to “disruption.”
The Red Team Detail Is the Real Signal
The most revealing part of KT’s announcement is its emphasis on the Red Team. In corporate security marketing, red team has often become an overused badge attached to anything more serious than a vulnerability scan. KT’s description is more specific: an attacker-perspective unit that validates infiltration routes and the effectiveness of defensive systems using tactics and techniques associated with real hacking groups.That distinction matters. A vulnerability scan tells an organization that a door exists. A red-team operation asks whether an attacker can find the door, open it quietly, move through the building, steal the master keys, and reach the room everyone assumed was isolated. The first is compliance-friendly. The second is uncomfortable by design.
KT says its Red Team works through the full chain: reconnaissance, initial access, privilege escalation, lateral movement, and access to core systems. That language tracks the way modern intrusions actually unfold. The catastrophic part of a breach is often not the first exploit; it is the attacker’s ability to turn one foothold into many, then convert administrative access into operational leverage.
For a telecom carrier, that chain is especially dangerous because “core systems” is not an abstract phrase. It can mean authentication infrastructure, network management platforms, billing systems, cloud environments, customer portals, operational processes, and the trust relationships between them. Attackers do not need to break every system if they can find one path that crosses from corporate IT into a more sensitive operational plane.
The company’s statement that it tests complex attack paths spanning IT, network, authentication, billing, cloud, and operating processes is the part administrators should underline. This is where many real organizations remain weaker than their slide decks suggest. Security teams may have good visibility into endpoints, reasonable controls on web apps, and a documented cloud posture, yet still fail to understand how an attacker could chain small weaknesses across organizational boundaries.
The Blue Team Cannot Win If the Company Draws the Wrong Map
KT also described its Red Team as working in connection with the Blue Team, the defenders responsible for detection, monitoring, and incident response. That may sound obvious, but it is one of the most persistent gaps in enterprise security. Offensive testing that produces a PDF and defensive operations that continue unchanged are not a security program. They are theater.A useful red-team exercise tells defenders where they were blind, where alerts were noisy, where escalation paths were slow, and where assumptions about containment did not survive contact with an adversary. The defender’s job is not to “beat” the red team in a single exercise. It is to become harder to surprise the next time.
This is where Locked Shields is unusually relevant. A live-fire multinational exercise forces participants to defend under artificial but meaningful stress. Teams do not have the luxury of turning every alert into a root-cause analysis seminar. They must triage, communicate, preserve services, and decide what risk is acceptable while other teams and exercise injects complicate the picture.
That is closer to the real world than the tidy incident-response tabletop that ends with everyone agreeing the plan looks solid. In a telecom crisis, the problem is rarely one machine. It is the dependency graph. Which systems must be restored first? Which logs can be trusted? Which credentials are now suspect? Which partner connections should be throttled or severed? Which outage will create cascading public harm?
The telecom operator that understands those dependencies before a crisis has an advantage. The one that discovers them during an attack becomes a spectator in its own network.
Locked Shields Has Outgrown the Capture-the-Flag Mental Model
There is a temptation to imagine Locked Shields as an elite capture-the-flag competition with better uniforms and more acronyms. That undersells the exercise. CCDCOE describes Locked Shields as a live-fire cyber-defense exercise that tests technical, operational, and strategic capabilities, including legal and communications dimensions. The exercise has grown into a rehearsal for national cyber stress, not merely a tournament for keyboard warriors.The 2026 edition reportedly brought together more than 4,000 cyber defenders from more than 40 nations, with teams defending critical infrastructure in a wartime-style scenario. That scale matters because cyber defense is increasingly coalition defense. No major country, carrier, software vendor, or cloud operator can pretend that its security problems stop at the edge of its own network.
South Korea’s participation is also geopolitically notable. Korea is not a NATO member, but it has deepened cyber cooperation with NATO-aligned institutions over the past several years, and CCDCOE has served as a venue for countries outside the alliance to participate in shared cyber-defense work. KT’s involvement fits that pattern: a private-sector operator participating in a multinational defense exercise because the infrastructure it runs would be part of any serious crisis.
This year KT participated as part of a Korea-Hungary joint team. Last year, according to the company, it joined a Korea-Canada team focused on defending 5G networks and major information and communications infrastructure in a virtual country. That continuity is more important than the pairing itself. One year of participation is exposure. Two consecutive years suggest institutional learning.
The useful question is not whether KT “won.” The useful question is what it brought home. Exercises matter only if their lessons survive the flight back from Tallinn and become changes in architecture, playbooks, tooling, escalation authority, and engineering culture.
Telecom Is Where Cyber Incidents Become Public Incidents
Most companies can suffer a cyberattack and contain the damage within corporate boundaries, at least for a while. A telecom operator does not have that luxury. When communications infrastructure fails, the public experiences it immediately, and the affected services often include other organizations’ ability to recover from their own crises.That is why the industry’s security posture must be judged differently from that of an ordinary enterprise. A ransomware incident at a retailer can be financially damaging and operationally ugly. A serious compromise at a national carrier can interfere with emergency communications, authentication, roaming, industrial connectivity, public-sector services, and the cloud-dependent businesses riding on top of the network.
The attack surface is also broader than outsiders tend to assume. Telecom networks include legacy systems, virtualized network functions, cloud-native components, identity platforms, customer-facing apps, roaming relationships, vendor management channels, physical infrastructure, lawful intercept obligations, and operational technology-adjacent management systems. The result is not one network but a federation of old and new systems tied together by necessity.
That complexity is exactly what sophisticated attackers exploit. They rarely need cinematic zero-days if they can abuse misconfiguration, stale credentials, exposed management interfaces, over-permissive service accounts, weak segmentation, and delayed detection. In a telecom environment, even small trust mistakes can become large operational problems.
KT’s emphasis on attack paths crossing IT, network, authentication, billing, cloud, and operations is therefore not decorative. It is a sober description of how modern telecom risk actually behaves. The border between “business system” and “critical system” is often thinner than executives would like to admit.
Windows Server Remains a Battlefield Because Identity Remains the Prize
KT’s mention of Windows server security deserves special attention because it points to a persistent truth in enterprise defense: attackers still chase identity, and Windows environments still sit at the center of identity for many organizations. Active Directory, hybrid identity, privileged access, group policy, administrative workstations, certificate services, and legacy server roles remain deeply woven into corporate operations.For defenders, this creates a paradox. Windows Server is mature, extensively documented, and supported by an enormous security ecosystem. Yet the very ubiquity that makes it manageable also makes it attractive. Attackers understand the terrain, defenders inherit years of configuration drift, and the blast radius of a compromised privileged account can be enormous.
In a live-fire exercise involving national infrastructure, Windows security is not just about patch levels. It is about whether administrators can detect credential theft, prevent lateral movement, isolate compromised hosts, preserve domain integrity, and continue operating when trust in parts of the environment has collapsed. That is a much harder problem than applying the latest cumulative update.
The Windows community has spent years discussing the right controls: tiered administration, privileged access workstations, multifactor authentication, hardened baselines, attack surface reduction, endpoint detection and response, constrained delegation, certificate authority hygiene, and aggressive logging. The hard part is not knowing that these controls exist. The hard part is implementing them consistently across a sprawling enterprise where business units, legacy apps, and uptime pressures all push back.
Locked Shields-style scenarios punish partial implementation. If a team has logging but no analyst workflow, it drowns. If it has segmentation but undocumented exceptions, attackers find the exceptions. If it has identity controls but too many standing privileges, the attacker’s path remains open. The exercise format forces a blunt question: does the security architecture work as a system, or only as a collection of good intentions?
Satellite and 5G Push the Same Lesson From Different Directions
KT’s stated 2026 focus included satellite communications infrastructure. Its 2025 participation involved 5G networks and major information and communications infrastructure. These are different technical domains, but they converge on the same strategic point: connectivity is becoming more distributed, more software-defined, and more dependent on complex orchestration layers.Satellite communications are no longer a niche backup channel reserved for remote outposts. They increasingly intersect with defense, maritime, aviation, emergency response, and resilient connectivity planning. At the same time, 5G networks have pulled more network logic into software-defined, cloud-oriented architectures. That shift creates flexibility, but it also creates new places for identity, configuration, and management-plane security to fail.
The old telecom mental model treated the network as specialized hardware run by specialized engineers in specialized environments. That model has not disappeared, but it is no longer sufficient. Modern telecom increasingly looks like a hybrid of carrier engineering, cloud operations, enterprise IT, software supply-chain management, and national security planning.
That hybrid reality changes the defender’s job. A security team must understand not only packets and malware, but also orchestration, APIs, CI/CD pipelines, vendor dependencies, identity federation, and operational recovery. It must know how an attacker could pivot from an administrative tool into a network-management function, or from a cloud misconfiguration into a service-impacting outage.
KT’s exercise participation is therefore less about any single technology than about convergence. Satellite, 5G, Windows servers, web services, billing systems, and cloud platforms are not separate worlds during a crisis. They become one contested environment.
Generative AI Raises the Tempo, Not Just the Threat Level
KT also linked its security work to the spread of generative AI, saying it is strengthening AI-assisted vulnerability diagnosis, analysis streamlining, and verification quality to prepare for the possibility of AI-based attack automation. This is the part of the announcement most likely to attract hype, so it deserves careful handling.Generative AI does not magically turn every low-skill attacker into an elite operator. Real intrusions still require targeting, persistence, operational judgment, infrastructure, and the ability to adapt when defenses behave unexpectedly. But AI can lower friction in meaningful ways. It can help attackers generate phishing variants, summarize stolen documentation, write or modify scripts, triage exposed services, and accelerate reconnaissance.
For defenders, AI is most useful when it compresses repetitive work without replacing human judgment. Vulnerability diagnosis, log summarization, alert enrichment, malware triage, and playbook assistance are all plausible areas where AI can help. The danger is pretending that faster analysis equals better defense if the underlying data is incomplete or the response authority is unclear.
In a telecom environment, AI-assisted defense must also be treated as an operational system with its own failure modes. Models can hallucinate. Automation can amplify mistakes. Sensitive logs and incident data can create privacy and sovereignty concerns if handled carelessly. The more important the network, the less acceptable it is to bolt on AI as a novelty layer.
The more realistic promise is not autonomous cyber defense. It is reducing the time between signal and action. In a live-fire scenario, minutes matter. If AI can help analysts connect weak signals, prioritize likely attack paths, or generate a first-pass incident timeline, it can buy defenders time. But the final measure remains operational: did the service stay up, did the attacker get contained, and did leadership make better decisions?
The Corporate Press Release Hints at a Bigger Policy Shift
KT’s announcement is written in the familiar language of corporate achievement, but the subtext is policy. Governments increasingly expect critical-infrastructure operators to behave as part of national defense ecosystems. The private sector owns and operates much of the infrastructure that states must protect, and exercises like Locked Shields create a controlled environment where those relationships can be tested before a real incident forces the issue.This trend is not limited to Korea. Across NATO countries and partners, cyber resilience has become a shared burden among militaries, civilian agencies, regulators, vendors, and infrastructure operators. The state may set priorities, issue warnings, and coordinate crisis response, but it cannot directly operate every network, patch every server, or rewrite every recovery plan.
That reality is awkward for companies. Participation in national exercises can improve readiness, but it can also expose uncomfortable gaps. It may reveal that escalation paths are unclear, that executives do not understand technical tradeoffs, that legal approvals are too slow, or that dependencies on suppliers are more brittle than assumed. The value of the exercise is precisely that it creates those discoveries in a survivable setting.
For telecom carriers, the policy pressure will only increase. As networks become more central to defense, emergency management, digital identity, and cloud access, regulators and governments will demand more evidence of resilience. Annual audits and compliance attestations will not be enough. Operators will be expected to prove that they can function under attack.
KT’s second consecutive year at Locked Shields positions the company inside that emerging expectation. The bigger question is whether such participation becomes routine for other major carriers. If telecom networks are national infrastructure, then live-fire rehearsal should not be exceptional. It should be part of the operating model.
The Exercise Should Change Procurement as Much as Playbooks
One of the under-discussed benefits of exercises like Locked Shields is that they expose procurement mistakes. Security architecture is often constrained by products bought years earlier, vendor promises that did not survive deployment, and integration gaps that nobody noticed until a crisis. A live-fire exercise can reveal whether tools actually support the workflows defenders need.This is especially relevant in Windows-heavy and hybrid environments. Many organizations own endpoint tools, SIEM platforms, vulnerability scanners, identity products, backup systems, and cloud security dashboards. The issue is not tool scarcity. It is whether those tools produce a coherent operating picture when an attacker is moving quickly.
Defenders need to know which alerts are trustworthy, which systems are authoritative, and which dashboards reflect reality rather than inventory lag. They need forensic access without destroying evidence, segmentation controls that can be changed quickly but safely, and identity systems that allow emergency privilege management without creating new backdoors. Those needs should shape procurement long before the next breach.
Telecom operators also face a vendor-chain problem that is more complex than most enterprises. Network equipment, operational support systems, cloud providers, software suppliers, and managed service partners all create dependencies. A carrier’s incident-response plan is only as good as the weakest critical dependency it assumes will behave perfectly.
KT’s red-team emphasis suggests it understands that the decisive weakness may be a process, not a product. A billing workflow, an authentication exception, a shared administrative credential, or an undocumented vendor access path can matter as much as an exploitable CVE. The mature security organization looks for those seams before an adversary does.
Public-Private Cyber Defense Needs Practice, Not Slogans
The phrase “public-private partnership” has become nearly meaningless through overuse. Everyone supports it in principle; fewer organizations practice it under stress. Locked Shields is valuable because it turns the slogan into a timed exercise with consequences, even if those consequences are simulated.In a real cyber crisis, government agencies may hold threat intelligence that private operators need. Private operators may hold telemetry that government defenders need. Legal teams may be asked to approve actions at machine speed. Communications staff may need to explain an outage while engineers still do not know the full scope. International partners may be dealing with the same adversary from different legal and political positions.
Those tensions cannot be solved by exchanging business cards during peacetime. They require rehearsed channels, pre-negotiated authorities, trusted contacts, and a shared vocabulary for severity and action. Exercises provide a way to discover where cooperation breaks down before the failure is public.
For Korea, a joint-team format with Hungary this year and Canada last year also has a quiet diplomatic function. Cyber defense cooperation builds relationships that are less visible than military exercises but increasingly important. When the systems at stake include satellites, 5G, Windows servers, and web infrastructure, the divide between civilian and defense technology becomes more procedural than technical.
That is why KT’s presence is significant beyond the company itself. It represents a model in which national carriers are not merely regulated entities waiting for guidance. They are active participants in the rehearsal of national and allied cyber resilience.
The Lesson From KT’s Tallinn Test Is That Resilience Has to Be Rehearsed
KT’s announcement is not proof that its networks are impregnable, and it should not be read that way. No serious operator would make that claim. The more meaningful claim is that KT is exposing its people, processes, and assumptions to a demanding multinational exercise that resembles the kind of chaos real attackers try to create.That is the right direction. Cybersecurity has spent too many years rewarding documentation over demonstrated performance. Policies are necessary, but attackers do not read them. Compliance is useful, but it is not the same as continuity. A locked-down server is good, but a recoverable service is better.
For Windows administrators, the story lands close to home. The same themes that appear in a national telecom exercise also appear in ordinary enterprises: identity is the prize, lateral movement is the danger, logging without response is noise, segmentation without testing is hope, and backups without restoration drills are decoration. The scale changes, but the logic does not.
The telecom-specific lesson is sharper. A carrier cannot defend only the network layer, only the cloud layer, only the server estate, or only the customer-facing applications. It must defend the paths between them. That is where modern attackers live.
Five Signals Administrators Should Take From KT’s Locked Shields Run
KT’s Locked Shields participation is a reminder that serious cyber defense is moving from isolated controls toward rehearsed operational resilience. The most practical lessons are not limited to national carriers; they apply to any organization whose Windows estate, cloud services, identity systems, and business processes have grown into one interdependent attack surface.- Red-team work is most valuable when it tests full attack paths rather than isolated vulnerabilities.
- Windows server security remains central because attackers still use identity compromise and lateral movement to turn small breaches into major incidents.
- Telecom networks show why cyber defense must account for operational continuity, not just data confidentiality.
- AI-assisted defense will matter most where it helps analysts move faster without surrendering judgment to automation.
- Public-private cyber cooperation needs live exercises because real crises expose weak relationships as quickly as weak systems.
- The most important output of a major exercise is not the score, but the architectural and procedural changes made afterward.
Source: 매일경제 KT announced on the 10th that it has participated in the International Cyber Defense Training "Locks.. - MK