A timing-and-lifecycle bug in the Linux traffic‑control scheduler (sch_hfsc) has been assigned CVE‑2025‑38177 after upstream maintainers patched a non‑idempotent qlen_notify pathway that could leave parent qdiscs operating on stale class pointers and, in the worst case, trigger a kernel use‑after‑free. The fix is small and surgical — making hfsc_qlen_notify idempotent — but its implications reach into how distributions backport patches, how multi‑tenant cloud and appliance environments are risk‑prioritized, and how operators should hunt, verify, and remediate.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
What HFSC and qlen_notify are, in plain language
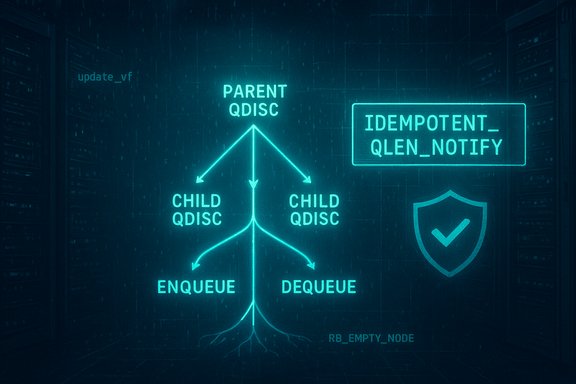
The Hierarchical Fair Service Curve (HFSC) qdisc is a classful traffic‑control discipline in the Linux kernel that provides hierarchical shaping and rate guarantees. In classful qdiscs, children report their backlog and state transitions to parent qdiscs using a small API surface that includes counters and a notification callback, qlen_notify. That callback is critical to keeping parent/child state consistent across enqueue/dequeue sequences. A subtle runtime ordering can arise when an enqueue operation causes internal dequeues (for example, fairness adjustments or shaping actions). If a child qdisc becomes empty as the side effect of such a dequeue, the kernel must notify the parent at a time and in a way that does not confuse later re‑activation or accounting logic. CVE‑2025‑38177 concerns a case where the HFSC implementation’s qlen_notify sequence could be invoked in ways that are not idempotent, allowing re‑activation sequences to observe stale pointers and the parent qdisc to dereference freed memory.Overview of the vulnerability and fix
The core defect
Upstream maintainers summarized the root cause concisely: hfsc_qlen_notify was not idempotent and therefore unfriendly to its callers (like fq_codel_dequeue. Two concrete operations inside the HFSC code were the focus of the fix:- update_vf decreases cl->cl_nactive, so callers can check that counter and avoid unnecessary or duplicate notifications.
- eltree_remove unconditionally removed an RB node cl->el_node; changing the logic to use RB_EMPTY_NODE and RB_CLEAR_NODE makes the removal safe when the node may already have been removed.
Where the patch landed
The kernel CVE announcement and stable‑tree notifications map the fix into multiple kernel trees; fixes were applied to a range of stable branches and mainline series. Upstream maintainer notes list specific commits and kernel series that received the patch, demonstrating the expected backporting into stable releases used by distributions and vendors.Technical analysis: why idempotency matters here
Notification semantics vs. lifecycle semantics
Classful qdiscs rely on sequences of operations: enqueue → possible internal dequeue(s) → class state changes → parent notification. Many implementations assumed notifications only happen in specific, narrow sequences. When an internal dequeue causes a child to become empty at an earlier point, a notification can arrive ahead of the expected window. If the notification handler and parent logic are not tolerant of duplicate or out‑of‑order notifications, the parent may attempt to use class pointers that have been freed or are otherwise invalid — a textbook use‑after‑free scenario. This is precisely the lifecycle/timing mismatch the patch addresses by ensuring notifications are safe to repeat.Concrete codeguard changes
The two technical levers used in the patch are conservative and low‑risk:- Check cl->cl_nactive before calling update_vf so the routine does not decrement the active counter into invalid ranges and does not trigger unnecessary re‑activation paths.
- Use RB_EMPTY_NODE to verify the RB node is still present before attempting removal and RB_CLEAR_NODE after removal to avoid double‑remove races.
Scope and exposure: who should care
Affected components
The vulnerability lives in net/sched/sch_hfsc.c — the HFSC scheduler implementation in the Linux kernel. Any kernel build that includes classful qdiscs (HFSC, DRR, netem) and compiles the scheduler codepaths in question is in scope. This includes many general‑purpose distributions, network appliances, embedded systems with full net/sched support, and cloud VM images that ship full networking stacks.Attack model and practicality
The realistic attack vector is local or tenant‑adjacent: an attacker needs the ability to run code or manipulate traffic‑control state on the host (for example, via tc/netlink operations, unprivileged containers that are permitted to alter qdiscs, or tenant workloads in a misconfigured multi‑tenant environment). For single‑user, well‑hardened desktops without untrusted local execution, the practical risk is lower. For cloud hosts, NFV platforms, CI runners, or multi‑tenant appliances where untrusted actors can manipulate qdisc state, the risk is materially higher because a single kernel oops or UAF can destabilize the host and affect all tenants.Distribution and vendor tracking
Major distribution trackers and CVE mirrors ingested the entry and mapped vendor fixes and package updates. Debian, Ubuntu, SUSE, and major vendors have published advisories or package mappings that mark kernels and package versions as fixed or patched. Administrators must consult their vendor’s security advisories because backporting policies vary and numeric kernel versions alone are not a reliable indicator of whether the fix is present.Practical remediation and mitigation
Definitive remediation: update the kernel (and reboot)
The only reliable fix is to install vendor‑supplied kernel updates that contain the upstream stable commit(s) addressing CVE‑2025‑38177, and then reboot into the patched kernel. Because the changes are present in multiple stable trees, most mainstream vendor kernels will carry the patch either as a backport or as part of a regular stable update; confirm by checking package changelogs for the upstream commit hashes where provided.Short‑term mitigations when updating is delayed
- Restrict who can run tc or manipulate netlink interfaces (use sudoers, RBAC, or container runtime capability restrictions).
- Harden container runtimes so unprivileged containers cannot alter host qdiscs (drop NET_ADMIN capability for untrusted workloads).
- Move critical workloads off shared hosts or force tenancy isolation until the patch is deployed.
These are compensating controls, not replacements for a kernel update.
Operational checklist for administrators
- Inventory: identify hosts with classful qdisc support; query kernel package changelogs via package manager tooling and configuration management systems.
- Vendor advisory check: consult your distribution’s security portal for CVE mappings and fixed package versions.
- Test: validate patches in a staging environment using a safe reproducer; do not run reproduction sequences on production hosts.
- Patch: deploy patched kernels in waves (test → pilot → broad rollout) and reboot hosts.
- Monitor: after patching, watch kernel logs (dmesg / journalctl -k) for residual OOPS or qdisc-related traces.
Detection, reproduction and forensics
How administrators will likely observe the bug
Unpatched hosts may emit kernel OOPS or WARN traces involving net/sched functions, or experience instability after tc/qdisc changes. Logs that reference qdisc_tree_reduce_backlog, qlen_notify, or related frames are the most direct indicators. Preserved vmcore/kernel crash dumps, uname -a, and kernel build IDs are critical triage artifacts.The reproducer and safe testing guidance
Upstream and distributor advisories describe a compact reproducer (safe to read, not for production) that exercises the bug on loopback by creating nested classful qdiscs, sending specific packets, deleting a parent class, and then sending another packet to trigger dequeue/enqueue interactions and the stale pointer dereference. Reproduce only in isolated labs — never on production systems.Critical appraisal: strengths and residual risks
Notable strengths of the upstream approach
- The fix is minimal and defensive: making qlen_notify idempotent addresses the root lifecycle mismatch rather than repeatedly patching individual qdisc accounting paths.
- The patch is intentionally small to ease backporting into stable trees, which improves the likelihood that operators will quickly receive vendor-delivered fixes.
Potential weaknesses and operational caveats
- The net/sched area has a long history of subtle timing and lifecycle bugs; a successful idempotency fix reduces one class of problems but does not preclude other timing-based defects appearing elsewhere in the scheduler code. Vigilance and post‑patch monitoring are required.
- Vendor backport schedules vary. Some OEM kernels, embedded images, or marketplace appliances may lag behind mainstream distro updates. Do not assume a kernel is fixed purely based on version number — verify the presence of the upstream commit or CVE mapping in vendor changelogs.
- The attack model is local; many enterprise risk processes deprioritize local-only issues. For multi‑tenant platforms, though, the effective risk can be far higher and warrants elevated priority.
What this means for WindowsForum readers (operators, admins, and enthusiast sysadmins)
- Network gateways, routers, cloud host images, NFV platforms, and shared CI runners should prioritize patching. These systems are most likely to host workloads or tenants capable of triggering the necessary tc sequences.
- Single‑user desktops and tightly controlled servers without untrusted local execution capabilities can be assigned a lower immediate priority, but they should still be tracked and updated as part of normal maintenance cycles.
- Containerized environments: ensure untrusted containers do not possess NET_ADMIN or other capabilities that allow manipulation of host qdiscs; use capability bounding to reduce attack surface.
Final recommendations — a straight, actionable plan
- Verify: check your vendor advisory or kernel package changelog to see if the fix for CVE‑2025‑38177 (sch_hfsc: make hfsc_qlen_notify idempotent) has been applied. If the changelog includes the upstream commit IDs referenced by kernel maintainers, you are likely fixed.
- Patch: apply vendor kernel updates that include the stable commits addressing the issue; reboot into the patched kernel as soon as practical.
- Compensate: if you cannot patch immediately, restrict who may call tc/netlink on the host, and harden container capabilities to remove NET_ADMIN from untrusted workloads.
- Monitor: after patching, review kernel logs for residual net/sched traces and confirm the absence of the reproduceable OOPS behavior in a staging environment. Capture vmcore artifacts if you observe crashes.
Conclusion
CVE‑2025‑38177 is a classic example of a small semantics bug in a complex, concurrent kernel subsystem producing outsized operational risk. The upstream remedy — making hfsc_qlen_notify idempotent and guarding RB node removal and active counters — is thoughtful, minimal, and designed to be easy to backport. That said, operational safety depends on timely vendor updates, careful verification that the fix is present in your specific kernel package, and short‑term compensating controls for multi‑tenant or less‑managed environments. Operators should treat this as a targeted kernel stability and Denial‑of‑Service risk with a concrete remediation path: apply the patched kernels, reboot, and monitor.Source: MSRC Security Update Guide - Microsoft Security Response Center