The Linux kernel received a targeted fix for CVE-2025-68193 that changes how the Intel Xe GuC control transport (CT) is torn down: maintainers added a devm-managed release action to ensure the CT is disabled before its backing buffer object (CTB) is freed, closing a deterministic use‑after‑free that could crash systems during GGTT TLB invalidation flows.
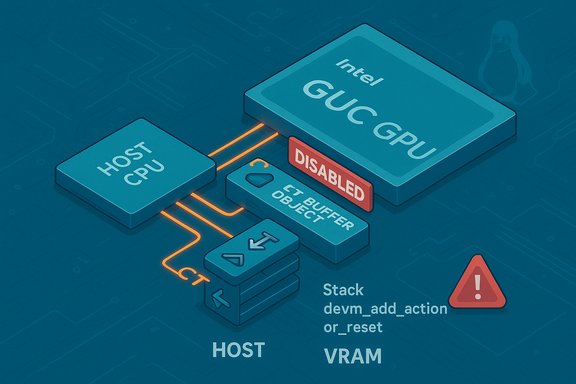
The affected code sits in the DRM Xe driver stack: specifically in the GuC (Graphics microcontroller) CT teardown logic used by Intel Xe GPUs. The GuC implements a control transport (CT) used for command and message traffic between the host CPU and GuC firmware; parts of the GuC flow interact with the Global Graphics Translation Table (GGTT) and use a CT buffer object (CTB) to submit TLB invalidation requests. Under normal operation the CT is enabled and used for low-latency GuC traffic; when disabled, the driver falls back to a safe MMIO path for equivalent operations.
The bug arises when a buffer object (BO) is allocated with the XE_BO_FLAG_GGTT_INVALIDATE flag: while releasing the BO the driver issues TLB invalidation requests via the CT path. If the CTB backing object is freed prematurely, worker callbacks or CT send routines can dereference freed memory and produce kernel oopses. The crash stacks reported at triage show GuC CT send pathways (h2g_write / guc_ct_send_locked / xe_guc_ct_send_locked / send_tlb_invalidation) involved in the faults. This vulnerability was catalogued as CVE‑2025‑68193 on December 16, 2025 and classified in public trackers as a memory‑corruption / use‑after‑free style defect in the kernel’s drm/xe/guc tree.
Practically, the patch introduces a new action (guc_action_disable_ct) that calls guc_ct_change_state(ct, XE_GUC_CT_STATE_DISABLED) and registers it with devm_add_action_or_reset during xe_guc_ct_init and after hardware reconfiguration (xe_guc_ct_init_post_hwconfig. When VRAM reinitialization reallocates CT buffers into different memory regions (for dGFX for instance), the devm action is removed and re-added so the disable action sits last in the devres stack and therefore executes first during teardown — ensuring CT traffic is quiesced before buffer release. This ordering removes the window that previously allowed CT sends to touch freed CTB memory.
For administrators the priorities are clear: inventory where Xe GuC code runs, confirm vendor package mappings, apply kernel updates and reboot, and restrict GPU device exposure on untrusted hosts if immediate patching is infeasible. While the vulnerability primarily enables a local denial‑of‑service, the presence of a deterministic kernel crash is a serious operational risk in multi‑tenant or CI environments and merits prompt remediation.
Acknowledgement of sources: this analysis synthesizes the public CVE record and kernel-stable patch communications describing drm/xe/guc teardown changes and the linked kernel commit narrative.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The affected code sits in the DRM Xe driver stack: specifically in the GuC (Graphics microcontroller) CT teardown logic used by Intel Xe GPUs. The GuC implements a control transport (CT) used for command and message traffic between the host CPU and GuC firmware; parts of the GuC flow interact with the Global Graphics Translation Table (GGTT) and use a CT buffer object (CTB) to submit TLB invalidation requests. Under normal operation the CT is enabled and used for low-latency GuC traffic; when disabled, the driver falls back to a safe MMIO path for equivalent operations.The bug arises when a buffer object (BO) is allocated with the XE_BO_FLAG_GGTT_INVALIDATE flag: while releasing the BO the driver issues TLB invalidation requests via the CT path. If the CTB backing object is freed prematurely, worker callbacks or CT send routines can dereference freed memory and produce kernel oopses. The crash stacks reported at triage show GuC CT send pathways (h2g_write / guc_ct_send_locked / xe_guc_ct_send_locked / send_tlb_invalidation) involved in the faults. This vulnerability was catalogued as CVE‑2025‑68193 on December 16, 2025 and classified in public trackers as a memory‑corruption / use‑after‑free style defect in the kernel’s drm/xe/guc tree.
What went wrong — technical anatomy
GuC CT, GGTT and TLB invalidation: the key pieces
- GuC CT (Control Transport): a mechanism the host uses to send GuC-specific control messages (for example, to manage GuC state or execute firmware-managed operations).
- CT Buffer Object (CTB): the memory object GuC uses to stage CT messages. It can be reallocated or moved into VRAM during hardware post-init flows.
- GGTT invalidation: when the driver removes or moves a BO that is mapped into the Global Graphics Translation Table, the GPU’s TLB entries must be invalidated. On Xe hardware this invalidation can be performed by submitting requests via the CT path (fast, firmware-assisted) or by falling back to a safe MMIO path if CT is not available.
Why a devm action fixes ordering
The kernel’s device-managed resource API (devm_) gives an easy, predictable ordering for teardown: devm_add_action_or_reset registers a callback that the kernel will invoke during device teardown in reverse order (LIFO) of registration. By registering a disable CT* action that explicitly transitions the CT to a disabled state and cancels any pending CT activity, maintainers can guarantee the CT disable runs before the CT buffer object is released by other devres-managed frees.Practically, the patch introduces a new action (guc_action_disable_ct) that calls guc_ct_change_state(ct, XE_GUC_CT_STATE_DISABLED) and registers it with devm_add_action_or_reset during xe_guc_ct_init and after hardware reconfiguration (xe_guc_ct_init_post_hwconfig. When VRAM reinitialization reallocates CT buffers into different memory regions (for dGFX for instance), the devm action is removed and re-added so the disable action sits last in the devres stack and therefore executes first during teardown — ensuring CT traffic is quiesced before buffer release. This ordering removes the window that previously allowed CT sends to touch freed CTB memory.
What the patch changes — implementation summary
- Add a new devm-managed action (guc_action_disable_ct) that:
- Cancels outstanding CT fences and workers.
- Transitions the CT state to disabled so future TLB invalidation requests will use the MMIO fallback.
- Register this action in the CT init code paths (xe_guc_ct_init and xe_guc_ct_init_post_hwconfig) using devm_add_action_or_reset so teardown ordering is handled by devres.
- On VRAM reinitialization path (where CT BO is reallocated into VRAM for dGFX), remove and re-add the devm action so it remains last-registered and thus first-run on teardown (LIFO semantics).
- Avoid relying on ad-hoc manual ordering or ad-hoc synchronisation; instead convert the teardown contract into a devres-managed guarantee.
Affected versions and upstream mapping
Public vulnerability trackers and OSV list the fix as applied to the upstream kernel with reference commit IDs in the stable tree; the CVE entry maps to the commit range where the fix was introduced. The vulnerability was assigned and published on December 16, 2025. The referenced stable commits appear in the kernel stable branches and have been propagated into the autoselected stable updates for recent series. Note: exact fixed-package versions for downstream distributions vary by vendor and branch. Administrators must confirm their distribution or vendor kernel changelog for the presence of the relevant stable commit ID before declaring machines remediated. The kernel commit references supplied by public trackers are the canonical way to map a distribution package to the upstream fix.Severity, attack surface and exploitability
Principal impact: Availability / Host local crash
The flaw produces a deterministic kernel crash (use-after-free) when the CT path attempts to use a CTB that has already been freed. That makes the primary impact class availability — a local denial‑of‑service against a host or a single-tenant workstation relies on being able to provoke the GT driver’s GGTT invalidation path. CVE trackers list the bug as a memory‑corruption / UAF category.Attack vector: local / host‑adjacent
- The attack requires a process to exercise GPU driver code paths that trigger GGTT TLB invalidations (for example by removing or relocating BOs mapped into GGTT).
- On many desktop or workstation setups the vector is local but requires only low privileges if /dev/dri devices are exposed to unprivileged users or containers.
- In multi‑tenant or CI environments that intentionally grant GPU access to untrusted containers or VMs, the risk becomes operationally significant because an attacker can trigger a reproducible kernel oops.
Exploitation potential: DoS is realistic; escalation is theoretical
At disclosure the public record focuses on kernel oops traces and deterministic crashes rather than an exploit chain to escalate privileges or execute arbitrary code. While kernel use‑after‑free conditions can sometimes be leveraged in sophisticated chains to escalate privileges, doing so generally requires additional allocator-shaping primitives and favorable memory layout conditions. There are no widely reported in‑the‑wild exploit campaigns for this particular CVE at publication, but the presence of a simple, repeatable crash primitive is sufficient cause for prompt remediation in shared infrastructure.Detection, triage and hunting guidance
Operational detection should focus on kernel logs and telemetry. Practical indicators include:- dmesg/journalctl traces showing crash stacks containing symbols such as:
- h2g_write, guc_ct_send_locked, xe_guc_ct_send_locked, send_tlb_invalidation, xe_gt_tlb_invalidation_ggtt, ggtt_invalidate_gt_tlb, ggtt_node_remove, xe_ggtt_remove_bo.
- Repeated compositor crashes, display failures, or unexpected kernel oopses correlated with GPU-heavy workloads or BO lifecycle operations.
- If your organization runs kernels compiled with sanitizers (KASAN/UBSAN) in test fleets, sanitizer traces pointing to CT send or GGTT invalidation paths are direct signals.
- Capture and preserve full dmesg and kernel logs immediately when crashes occur.
- Collect ftrace or kdump/vmcore if available — backtraces help map the exact code path.
- Verify whether the running kernel includes the xe GuC CT source tree in question (inspect /boot/config-$(uname -r) or check module presence: lsmod | grep xe).
- Correlate crashes with workload patterns (hotplug, BO relocation, test harnesses that allocate GGTT-mapped BOs).
Remediation and mitigations
Definitive fix
- Install a kernel update from your distribution or vendor that includes the stable commit implementing the devm release action for CT.
- Reboot hosts into the updated kernel — kernel-level fixes only take effect after a reboot.
Interim mitigations (if patching cannot be immediate)
- Restrict access to GPU device nodes: tighten udev rules and group permissions so /dev/dri/* is not accessible to untrusted users or containers.
- Remove GPU passthrough or --device=/dev/dri bindings from multi‑tenant containers and CI runners.
- Increase telemetry and alerting for kernel oops traces referencing the GuC/CT stack frames.
- Where possible, limit use of GPU‑accelerated untrusted workloads on machines that cannot be patched quickly.
Vendor and backport note
- The patch is intentionally small and backport-friendly; mainstream distributions typically propagate such fixes quickly into stable packages.
- Embedded OEMs and vendor‑forked kernels can lag — inventory custom kernels and confirm backport status with the vendor if you run appliance images or vendor-supplied kernels.
Why this patch is a sensible engineering choice
- Surgical and low-risk: The change consolidates a teardown contract via device-managed resources rather than introducing wide behavioral changes. That limits regression risk.
- Deterministic ordering: devm-managed actions provide a simple, well-understood ordering guarantee (LIFO) that naturally ensures the CT disable runs before buffer release.
- Backport friendliness: Small code deltas are easier to review and accept into stable branches — this accelerates distribution-level remediation and shortens the long tail of exposure.
- Preserves functionality: The patch does not alter the run-time semantics of CT operations in the happy path; it only ensures safe behavior during teardown/unbind and reinit flows.
Potential gaps and residual risks — critical analysis
While the fix addresses the immediate use‑after‑free window, several operational caveats remain:- Long‑tail vendor lag: Embedded devices, vendor kernels (Android OEMs, appliance images) and custom builds can remain unpatched for months or longer. That “long tail” is the primary residual exposure for driver fixes.
- Other race paths: The devm action protects the CTB teardown sequences registered via device-managed resources, but it’s possible other code paths or manual frees outside devres could still have ordering issues. Comprehensive triage should examine all CT usage sites.
- Requires reboot: Kernel updates require reboots; in high-availability environments patch scheduling and testing are necessary, and operators should plan staged rollouts with validation.
- Detection sensitivity: Kernel oopses can be noisy and intermittent; without consolidated kernel crash telemetry, occurrences can be missed on large fleets. Investing in centralized kernel log aggregation aids fast detection and response.
- Exploit potential: Although no public PoC was reported at disclosure, complex exploit chains could theoretically reuse such primitives in highly engineered attacks. Treat absence of public exploitation as reassurance, but not proof of safety.
Practical operator checklist — step by step
- Inventory:
- Run uname -r on fleet hosts and capture kernel versions.
- Check for Xe driver presence: lsmod | grep -i xe or inspect /sys/module/ for xe/guc components.
- Identify hosts that expose /dev/dri to untrusted users or containers.
- Verify vendor mapping:
- Consult your distribution’s security tracker or package changelogs for the stable commit(s) that correspond to the CT teardown patch.
- Patch:
- Schedule and roll out kernel package updates that include the upstream stable commits noted in advisories.
- Reboot hosts into the patched kernel during planned windows.
- Validate:
- Reproduce representative GPU workloads (modeset, BO allocation/relocation) and confirm no CT-related oopses appear in kernel logs for 7–14 days post‑deployment.
- Compensate where necessary:
- While waiting for patch windows, restrict access to /dev/dri nodes, remove device passthrough from containers, and increase kernel oops alerting.
Conclusion
CVE‑2025‑68193 is a narrowly scoped but operationally important kernel bug in the Intel Xe GuC CT teardown path. The upstream remediation — adding a devm-managed release action that explicitly disables CT before buffer object release — is a small, robust fix that eliminates the timing window that caused deterministic use‑after‑free crashes. The change is straightforward to map to stable kernel trees and is well suited for backporting.For administrators the priorities are clear: inventory where Xe GuC code runs, confirm vendor package mappings, apply kernel updates and reboot, and restrict GPU device exposure on untrusted hosts if immediate patching is infeasible. While the vulnerability primarily enables a local denial‑of‑service, the presence of a deterministic kernel crash is a serious operational risk in multi‑tenant or CI environments and merits prompt remediation.
Acknowledgement of sources: this analysis synthesizes the public CVE record and kernel-stable patch communications describing drm/xe/guc teardown changes and the linked kernel commit narrative.
Source: MSRC Security Update Guide - Microsoft Security Response Center