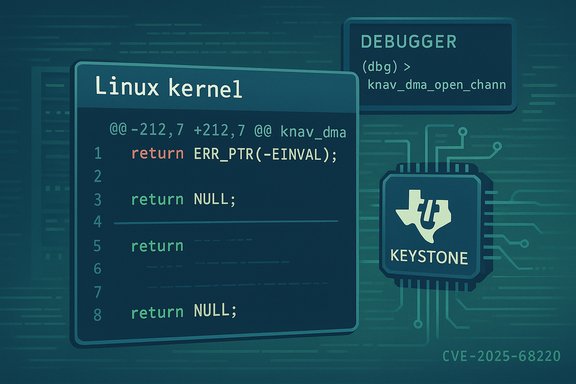
The Linux kernel received a small but important corrective patch that standardizes the error semantics of the Keystone/TI knav DMA helper: knav_dma_open_channel will now consistently return NULL on failure instead of using error-pointer conventions or (worse) casting error codes to pointers — a behavioral mismatch that led to a kernel crash in the TI netcp driver and was recorded as CVE-2025-68220.
Background
The affected API, knav_dma_open_channel(…), is part of TI’s (Texas Instruments) Keystone navigator DMA support (drivers/soc/ti/knav_dma.c) and is used by the TI netcp (network coprocessor) Ethernet driver to obtain DMA channels for packet I/O. Historically the API surface and header-level declarations were inconsistent: the header signaled a NULL return when the DMA support was absent, while the implementation used different conventions (including casting error codes to void*), and some callers expected either NULL or ERR_PTR-encoded errors. That inconsistency produced a real-world crash path in the netcp driver during cleanup (netcp_free_navigator_resources), leading to an alignment exception and an oops on affected ARM platforms. This change — made via a small kernel patch series submitted and discussed on the kernel mailing lists — standardizes the function to return NULL on all error conditions and adjusts the callers accordingly. The fix is intentionally minimal: it converts fragile, ambiguous error returns into a single, well-known sentinel (NULL) and updates the few places that used the function so they check for NULL rather than treating the return as an ERR_PTR or direct-cast error value. The change was tracked and recorded as CVE-2025-68220 on December 16, 2025.What happened technically
The root cause in plain English
- The knav_dma_open_channel API had inconsistent and non-idiomatic return behavior.
- In some situations the implementation returned (void *)-EINVAL (a direct cast of an integer error code into a pointer), in other places the header or callers assumed NULL for the absence of a channel, and yet other callers expected ERR_PTR-style error pointers.
- Because of those mixed conventions, a caller (netcp_core.c) could misinterpret whatever it received as a valid pointer and subsequently call knav_dma_close_channel or otherwise dereference the pointer.
- That misinterpretation produced an alignment exception and kernel oops trace that surfaced during automated testing and in kernel logs, ultimately causing host instability.
The specific observable symptom
The crash trace documented in the advisory shows an alignment exception originating from knav_dma_close_channel and a call chain ending in netcp_free_navigator_resources called during net device open/initialization flows. The net effect: a kernel oops/panic that can bring down the host or at least the networking subsystem on affected TI SoC platforms. The defect was easy to reproduce in certain test environments (kernelci, board farm) because the error path triggered during device initialization/cleanup when DMA channel allocation failed.The patch and how it fixes the problem
What the patch does
- Replace return values like (void *)-EINVAL with a consistent NULL return on all failure paths inside knav_dma_open_channel.
- Update the function’s comment and documentation to state explicitly: “Returns pointer to appropriate DMA channel on success or NULL on error.”
- Update callers (notably the netcp core) to check for NULL and handle allocation/open failures safely, avoiding subsequent calls that assume a valid channel pointer.
- The patch removes an ugly and unsafe pattern of encoding error numbers as pointers and restores clear, conventional kernel idioms for pointer-return helpers.
Why this is a safe fix
The change is small, local to the TI knav_dma helper and its immediate caller(s), and preserves the intended behavior for success paths while eliminating ambiguous error encodings. Upstream reviewers favored the minimal approach because it is low-risk to land and easy to backport to stable kernel trees, and it prevents a deterministic kernel oops without changing normal runtime behavior for correctly functioning hardware. The patch also effectively undoes a prior change that attempted to use different error conventions and unintentionally introduced the mismatch.Who and what are affected
- Primary exposure: Linux kernels that include the TI Keystone navigator DMA support (drivers/soc/ti/knav_dma.c) and the TI netcp Ethernet code (drivers/net/ethernet/ti/netcp_core.c) prior to the patch being merged.
- Typical devices: TI Keystone family SoCs and board support packages (networking appliances, embedded gateways, development boards) that build and load the netcp driver.
- Distribution and vendor permutations: standard distribution kernels that include the in-tree driver are eligible for the fix via stable backports; however, vendor-supplied forks, OEM Android kernels, and embedded BSPs that lag upstream are at the highest residual risk because they often delay or omit backports.
Severity and exploitability assessment
- Attack vector: local — the bug manifests when kernel initialization or runtime code attempts to open DMA channels and then mistakenly dereferences an invalid pointer.
- Impact: primary impact is Availability (kernel oops, potential panic), not Confidentiality or Integrity.
- Exploitability: converting a NULL dereference or misinterpreted pointer into a remote code execution or privilege escalation primitive would require additional, unrelated vulnerabilities; there is no public evidence of RCE in the wild for this CVE at disclosure. The immediate and realistic risk is denial-of-service / host instability.
Detection and triage: how to know if you were hit
Look for the following signals on machines that use TI netcp/netcp_core or knav DMA:- Kernel logs containing an oops with stack traces referencing:
- knav_dma_close_channel
- netcp_free_navigator_resources
- netcp_ndo_open or other netcp symbols
- Alignment exception or “Unhandled fault” traces during device initialization or during netif/device open flows.
- Repeated crashes or reboots correlated with network interface initialization on TI platforms.
- Inspect kernel messages:
- journalctl -k | grep -iE "knav_dma|netcp|Unhandled fault|alignment exception"
- dmesg | less (search for the same symbols)
- Confirm kernel configuration/source:
- Check if the kernel includes TI knav DMA: grep -R "knav_dma_open_channel" /usr/src/linux-headers-$(uname -r) (or search the installed kernel source tree)
- If you cannot find the symbol in packaged source, check vendor BSPs or device images for in-tree drivers.
Remediation and mitigation guidance
Definitive remediation
- Install vendor or distribution kernel packages that include the upstream fix and reboot into the patched kernel. The change has been merged upstream and is being absorbed into stable kernel branches and downstream distributions; package updates or vendor advisories that reference the fix, the CVE number, or related commit IDs are the authoritative remediation artifacts.
Short-term mitigations (if you cannot patch immediately)
- If the netcp driver is built as a module, consider unloading the module or blacklisting it until you can apply the fix. That will remove the code path entirely but will also disable the affected network interface.
- For embedded appliances, isolate impacted devices from critical networks or schedule a maintenance window to update vendor images.
- Restrict untrusted local users from initiating operations that could exercise driver initialization flows (for example, prevent nonprivileged users from using dev nodes or triggering early network brings on platforms where those capabilities can be abused).
How to confirm you’re patched
- Check your kernel changelog or distribution security advisory for an explicit mention of the upstream commit or CVE-2025-68220.
- Inspect the kernel source tree shipped with your package for the knav_dma_open_channel code and confirm the error-returns are NULL-based rather than ERR_PTR or integer-cast returns. The patch changes explicit return sites from constructs like return (void *)-EINVAL to return NULL.
Why small kernel fixes matter — operational analysis
Small changes like this one are deceptively important because kernel code runs in privileged mode and a single NULL pointer dereference or improperly handled pointer is often a one-shot host-wide failure. In cloud or multi-tenant environments, a single kernel oops affects all tenants on the host and may trigger automated recovery actions, job restarts, or cascading failures. Embedded and vendor-supplied kernels are particularly at risk because they frequently lag upstream and may not get stable backports quickly. The upstream approach — minimal, semantics-preserving patches that are easy to backport — is the correct operational response for this class of bug.Developer/maintainer perspective: what to look for in similar driver work
- Consistently document and enforce a single error-return convention for pointer-returning helpers:
- Either always return error-encoded pointers with ERR_PTR/IS_ERR/PTR_ERR (and document that), or
- Always return NULL for errors and communicate error details by other means.
- Never cast error integers into pointers (for example (void *)-EINVAL) — this pattern is fragile, nonportable, and easy to misinterpret.
- Validate caller assumptions in code reviews: when a helper returns a pointer, reviewers should enforce that callers check for the documented sentinel before dereferencing.
- Prefer minimal, defensive fixes in stable trees to reduce backport friction and regression risk.
Risk summary and final recommendations
- Risk profile: local denial-of-service / host instability due to a NULL/invalid pointer dereference in the TI knav DMA / netcp cleanup path. Not a remote RCE at disclosure.
- Who should prioritize patching:
- High priority: vendors and operators of embedded TI Keystone-based devices, network appliance maintainers, and any environment that uses vendor kernels derived from in-tree code.
- Medium priority: distribution package maintainers and cloud image owners that include TI netcp/knav code in their kernels.
- Lower priority: desktop/server workloads that do not build or load the TI netcp driver.
- Immediate action: confirm whether your kernel includes the TI knav DMA driver; if so, plan for a kernel update that includes the committed fix. If you cannot update immediately, consider unloading or disabling the module or isolating affected hosts.
Appendix — Practical checklist for operators
- Inventory:
- uname -r to identify running kernel.
- grep -R "knav_dma_open_channel" /usr/src/linux-headers-$(uname -r) or inspect your kernel source package.
- lsmod | grep netcp or check for netcp driver presence.
- Triage:
- journalctl -k | grep -iE "knav_dma|netcp|alignment exception|Unhandled fault"
- Preserve logs/vmcore if an oops is observed.
- Patch:
- Look for distribution advisories or vendor BSP updates listing CVE-2025-68220 or the upstream commit(s).
- Install the vendor/distribution kernel update and reboot.
- Validate:
- After update, re-check that the installed kernel source contains the NULL-based knav_dma_open_channel returns or the package changelog references the fix.
- Reproduce any previously observed device initialization that triggered the oops in a test environment to confirm remediation.
Small, surgical fixes like this one are the unsung maintenance work that keeps embedded and in-tree drivers stable. CVE-2025-68220 is a textbook example: a short, low-risk correction that removes an ambiguous return convention and closes a deterministic crash path. For operators running TI Keystone-based networking code, the fix should be applied promptly; for the broader community the case is a timely reminder of why consistent API contracts and careful error-handling matter at kernel level — a single pointer mistake in privileged code can still take down an entire device.
Source: MSRC Security Update Guide - Microsoft Security Response Center