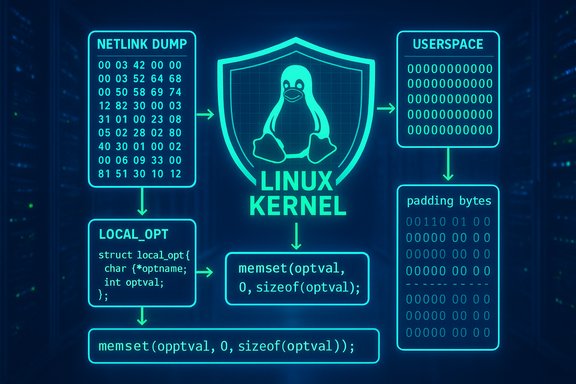
A compact but consequential Linux kernel information‑leak fix has been published under CVE‑2025‑40279: a small change in the traffic‑control connmark action (act_connmark) zero‑initializes a local struct (tc_ife / opt) in tcf_connmark_dump to stop uninitialized padding bytes from being copied into netlink replies via nla_put, closing a kernel→userspace leak vector that static analysis and runtime sanitizers flagged.
The Linux kernel’s traffic‑control (net/sched) subsystem exposes configuration and runtime state to userspace through netlink dump routines. These dump functions build structured replies containing C structs that are serialized and sent to tools such as tc and iproute2. If a structure used for building a netlink attribute contains uninitialized padding, those padding bytes are copied wholesale into the netlink message and can leak kernel memory contents to the unprivileged user that requests the dump. This class of problem has been repeatedly caught by KMSAN and other sanitizer/coverage tooling and is considered an information‑disclosure hazard in multi‑tenant or sensitive environments. CVE‑2025‑40279 describes exactly this pattern in the act_connmark implementation: the local variable (named N variations in the tree; here referred to as the outgoing option structure) was partially initialized with a designated initializer, leaving padding bytes indeterminate. Because the code path uses nla_put to copy the entire struct into a netlink message, those indeterminate bytes could reach userspace. The upstream remediation is straightforward: explicitly zero the structure (for example via memset) before assigning its fields, ensuring padding is deterministic (all zero) prior to copying. This kind of hygiene fix is small, low‑risk, and easily backportable; nevertheless, information‑leak fixes carry operational significance in environments where KASLR or other kernel secrecy matters for attack chains. The kernel community has historically handled these with short, conservative patches that do not change ABI or runtime semantics beyond the initialization.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux kernel’s traffic‑control (net/sched) subsystem exposes configuration and runtime state to userspace through netlink dump routines. These dump functions build structured replies containing C structs that are serialized and sent to tools such as tc and iproute2. If a structure used for building a netlink attribute contains uninitialized padding, those padding bytes are copied wholesale into the netlink message and can leak kernel memory contents to the unprivileged user that requests the dump. This class of problem has been repeatedly caught by KMSAN and other sanitizer/coverage tooling and is considered an information‑disclosure hazard in multi‑tenant or sensitive environments. CVE‑2025‑40279 describes exactly this pattern in the act_connmark implementation: the local variable (named N variations in the tree; here referred to as the outgoing option structure) was partially initialized with a designated initializer, leaving padding bytes indeterminate. Because the code path uses nla_put to copy the entire struct into a netlink message, those indeterminate bytes could reach userspace. The upstream remediation is straightforward: explicitly zero the structure (for example via memset) before assigning its fields, ensuring padding is deterministic (all zero) prior to copying. This kind of hygiene fix is small, low‑risk, and easily backportable; nevertheless, information‑leak fixes carry operational significance in environments where KASLR or other kernel secrecy matters for attack chains. The kernel community has historically handled these with short, conservative patches that do not change ABI or runtime semantics beyond the initialization.What the CVE says — technical summary
- Vulnerability identifier: CVE‑2025‑40279.
- Component: Linux kernel, net/sched (traffic control), action: act_connmark (connmark action).
- Function and code path: tcf_connmark_dump — the netlink dump routine that assembles an option struct (opt / tc_ife) and uses nla_put to serialize it into the reply.
- Fault: partial initialization via designated initializer leaves padding bytes uninitialized; nla_put copies full struct bytes to netlink buffer, leaking those uninitialized bytes to userspace.
- Fix: initialize the struct (memset opt to zero) before assigning fields; serialize deterministic data with no uninitialized padding.
- Exploitability: local information‑disclosure only (not a direct remote RCE); an attacker must be able to request or provoke the relevant netlink dump (typically local or containerized userspace). Public trackers list this as an info‑leak fix; no public exploit chain for remote code execution is reported at disclosure.
Why this is important (operational impact)
Even though the fix is a one‑line memset in most trees, the operational consequences are meaningful in several contexts:- Multi‑tenant servers and cloud hosts: leaked kernel bytes can reveal kernel memory layout and partial pointers, aiding local privilege escalation or escape efforts when chained with other primitives. Attackers value any kernel memory disclosure that reduces entropy for exploit primitives.
- Secure/forensic environments: systems that rely on KASLR, kernel stack confidentiality, or similar defenses should treat any kernel‑to‑user information leak as high‑value. A modest leak can significantly lower the cost of follow‑on attacks.
- Compliance and risk: data handling policies that classify kernel memory as sensitive will require remediation and evidentiary validation to close the gap. Even if the leak is not directly user data, it can be material to overall security posture.
- Low patch risk but possible long tail: the upstream change is trivial and low‑risk, but vendor and OEM kernels (embedded appliances, vendor forks, marketplace images) can lag. The distribution mapping is the crucial step for operations; don’t assume a kernel version number implies safety — check vendor changelogs for the specific upstream commit.
Technical analysis — what went wrong, in detail
- Designated initializer partiality and implicit padding:
- C designated initializers allow named member initialization while leaving unspecified bytes untouched. In many cases this is fine, but when the resulting struct is copied as raw bytes (e.g., by nla_put, any padding or uninitialized bytes are included in the output message. Because the kernel code path did not zero the struct before filling the documented fields, padding bytes remained nondeterministic and derived whatever garbage was present on stack memory.
- Netlink serialization semantics:
- nla_put is a raw-copy helper: it copies the given object bytes into the netlink attribute payload. It does not inspect struct member semantics or trim padding. Therefore, the only safe guarantees are either to build attribute payloads from explicitly serialized fields or to ensure the entire struct memory is deterministic (commonly by zeroing first). The upstream patch follows the latter approach.
- Class of vulnerability:
- This is a kernel‑to‑userspace information leak (confidentiality), not an immediate code‑execution or privilege escalation vector. However, information leaks are frequently used as the first step in exploit chains (e.g., by leaking kernel pointers to resolve KASLR), and therefore they receive timely fixes.
- Root cause and fix mechanics:
- The correct defensive pattern is trivial: declare the struct and immediately memset it to zero (or use an explicit initializer that guarantees all bytes set) before assigning documented fields. The kernel patch adds that zeroing to the dump routine so the padding bytes are known zeros and not stack remnants. This is a surgical fix with near‑zero regression risk.
Who is affected — scope and footprint
- Any Linux kernel build that includes the traffic‑control connmark action (act_connmark) and that predates the stable commit that applied this fix is potentially affected. Because the code lives in net/sched, affected hosts include routers, gateways, network appliances, cloud hosts running tc‑based configurations, and general server/desktop kernels with full net/sched support compiled in.
- Practical exposure prioritization:
- High priority: multi‑tenant infrastructure, cloud VM hosts, network appliances exposing management interfaces to untrusted users or containers.
- Medium priority: workstation or single‑tenant servers where local untrusted code may run (CI runners, shared developer machines).
- Low priority: locked‑down machines with no untrusted local access and hardened kernel configurations that exclude net/sched features.
- Important caveat: vendor backports vary. Distribution packages may include the upstream stable commit under different package/version numbering. The authoritative verification is the vendor kernel changelog or the presence of the commit hash in the packaged kernel source tree, not a heuristic kernel version alone.
Detection and verification — how to confirm exposure and remediation
A practical detection and verification workflow:- Inventory and prioritization:
- List hosts that run kernels with full net/sched support or that act as network gateways (tc is commonly used on those). Start with multi‑tenant hosts, cloud infrastructure, and appliances.
- Check package changelogs and upstream commits:
- For each affected kernel package, consult the vendor’s security advisory or package changelog for the upstream commit that zeroed the tc_ife / opt structure in tcf_connmark_dump. If vendor docs map to the upstream stable commit, the kernel is patched. When vendor mapping is absent, inspect your kernel’s source tree for the commit hash or use distribution package metadata.
- Reproduce in a controlled environment (developer/test only):
- Build a minimal test case that requests the connmark dump (tc filter dump) on a test kernel and capture the netlink reply. Prior to patching, repeated tests and memory pressure may produce non‑zero padding bytes in the attribute payload; after patching the padding should be deterministic zero.
- Note: do not run stress or characterizing tests on production systems. Reproduce only in controlled testbeds.
- Hunting for evidence in logs and telemetry:
- Information leaks do not leave standard kernel oops traces. Instead, use controlled dump output capture and compare expected struct fields to full payload hex dumps to detect stray non‑zero padding. Centralized logging and retained netlink dump captures (from automated audits) are helpful.
- Verify vendor package:
- Confirm the patched package version is installed and that the system was rebooted into the updated kernel if necessary. For kernels shipped as modules or out‑of‑tree drivers, contact the vendor for confirmation. Do not assume a distribution upgrade removed the vulnerability without checking the changelog.
Mitigation and remediation guidance
Immediate and medium‑term steps for administrators and security teams:- Definitive remediation:
- Install the vendor/distribution kernel update that includes the upstream commit which zero‑initializes the tc_ife/tcf_connmark_dump opt structure. Reboot into the patched kernel if the update requires it.
- Short‑term compensating controls (if you cannot patch immediately):
- Restrict local access: Limit the set of users that can run tc or issue privileged netlink queries. Tighten sudoers/role separation to reduce untrusted access to traffic‑control tools.
- Isolate sensitive hosts: For multi‑tenant designs, temporarily isolate tenants or schedule maintenance windows to apply patches.
- Audit netlink usage: Increase logging/auditing of netlink requests that request tc dumps and watch for suspicious or frequent dump invocations by untrusted users.
- Validation checklist (post‑patch):
- Confirm kernel package changelog references upstream fix commit(s) or CVE mapping.
- Reproduce a connmark dump in a test environment and verify payloads’ padding bytes are zeroed.
- Monitor for anomalous netlink activity and keep a short-term watch on audit logs for unusual tc dump frequency.
Risk analysis — strengths of the fix, residual risks, and attacker model
Strengths- The upstream fix is minimal, local, and deterministic — a zero initialization before struct population is a canonical defense that carries virtually no regression risk.
- Because the fix is small, it is highly amenable to backporting into stable kernels and vendor packages; many distributions will accept it quickly.
- Vendor lag: embedded appliances, custom vendor kernels, and some cloud marketplace images may not receive the backport promptly. These long‑tail artifacts are the most likely to remain vulnerable.
- Chained exploitation: while a single small leak is not by itself an RCE, attackers can and do chain multiple small leaks and timing primitives. Treat any kernel info leak seriously in high‑value or multi‑tenant environments.
- Detection limitations: unlike kernel oopses, information leaks are silent; they require proactive auditing or test harnesses to detect. Ensure you can capture netlink payloads used by diagnostic tooling if you want retrospective detection.
- The likely adversary is a local, low‑privilege user or container tenant that can issue netlink dump requests or can trick an agent with netlink privileges to perform the dump on behalf of the attacker.
- Remote unauthenticated exploitation is not applicable unless some networked service exposes the vulnerable dump API on behalf of remote users (an uncommon and avoidable misconfiguration).
Verification performed and cross‑checks
The technical description of CVE‑2025‑40279 (uninitialized padding in a tc_ife struct copied by nla_put is recorded in multiple independent trackers and vulnerability databases, including the National Vulnerability Database and OSV; distribution trackers (Debian/others) have imported the entry and referenced upstream stable commits. These independent records agree on the root cause and the fix approach (zero the struct before copying). Where the public CVE record refers to upstream commit hashes in the kernel stable tree, the distribution advisories and downstream OSV entries list those same commits as the canonical remediation targets. Administrators should map those commits to their vendor kernels for final confirmation. If a vendor changelog is absent or ambiguous, treat the host as potentially vulnerable until proven otherwise. Note on Microsoft’s attestation model: Microsoft publishes CSAF/VEX attestations for specific Linux artifacts (Azure Linux first), and those attestations describe inventory results for the product family — they are authoritative for that product but are not blanket statements about every Microsoft‑shipped Linux kernel artifact. Validate WSL2, CBL‑Mariner, Azure Marketplace images and custom kernels separately if they are in scope for your estate.Recommended action plan (concise checklist)
- Inventory: identify hosts with net/sched/connmark support and prioritize by tenancy and sensitivity.
- Vendor confirmation: check distribution/kernel package changelogs for the upstream commit or CVE mapping.
- Patch: apply vendor kernel updates that include the upstream fix and reboot as required.
- Validate: reproduce a connmark dump in a test environment and confirm padding bytes are zero in netlink replies.
- Monitor: add short‑term monitoring for unusual netlink dump activity and retain evidence for any suspicious behavior.
- Document: record the mapping between upstream commits and packaged kernel versions for audit and compliance.
Conclusion
CVE‑2025‑40279 is an archetypal kernel‑hygiene information‑leak: small and easily fixed by zero‑initialization, but potentially impactful in threat models that prize any kernel memory disclosure. The upstream patch is straightforward and low risk, and distributions are expected to accept it rapidly; the operational work is inventory and vendor mapping. Prioritize multi‑tenant and network‑facing hosts, verify vendor packages include the upstream commit, and treat any lingering unpatched appliances or vendor kernels as higher risk until remediated. The fix itself is simple, but the wider lesson persists: always zero or otherwise deterministically initialize structures destined for userspace serialization — a tiny line of code prevents subtle, high‑value leaks.Source: MSRC Security Update Guide - Microsoft Security Response Center