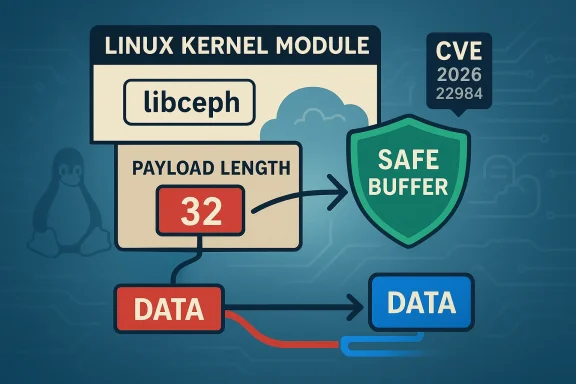
The Linux kernel received a targeted, surgical fix on 23 January 2026 for a bounds‑checking bug in the Ceph client library (libceph) that could allow an out‑of‑bounds read during authentication processing; the issue has been assigned CVE‑2026‑22984 and is addressed by an explicit check on the authentication payload length in handle_auth_done()/process_auth_done().
Ceph is a widely used open‑source distributed storage system, and the Linux kernel contains a client‑side component, libceph, that implements the kernel-side messaging and protocol logic for nodes that talk to Ceph monitors (MONs) and object storage daemons (OSDs). Because libceph parses networked protocol records received from remote storage servers, it must be defensive about lengths and bounds to avoid reading past the intended buffers. The newly recorded CVE addresses a failure to perform a required length check on an authentication payload field, which could allow a kernel code path to read beyond the supplied buffer.
The CVE was publicly recorded on 23 January 2026; downstream distribution advisories and trackers (Ubuntu, Debian, SUSE, Amazon Linux, and others) have cataloged the issue and the upstream kernel commits that remedied it. Distributors are shipping or preparing vendor patches and kernel updates; administrators running Ceph clients or kernel variants that include libceph should plan to apply vendor updates as they become available.
Two additional operational facts increase the importance of the patch:
Action plan in order of priority:
Conclusion: treat CVE‑2026‑22984 as actionable for any host that participates in Ceph client activity; apply vendor updates as they become available, monitor for related kernel oopses, and use network controls to reduce exposure while you update.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Ceph is a widely used open‑source distributed storage system, and the Linux kernel contains a client‑side component, libceph, that implements the kernel-side messaging and protocol logic for nodes that talk to Ceph monitors (MONs) and object storage daemons (OSDs). Because libceph parses networked protocol records received from remote storage servers, it must be defensive about lengths and bounds to avoid reading past the intended buffers. The newly recorded CVE addresses a failure to perform a required length check on an authentication payload field, which could allow a kernel code path to read beyond the supplied buffer.The CVE was publicly recorded on 23 January 2026; downstream distribution advisories and trackers (Ubuntu, Debian, SUSE, Amazon Linux, and others) have cataloged the issue and the upstream kernel commits that remedied it. Distributors are shipping or preparing vendor patches and kernel updates; administrators running Ceph clients or kernel variants that include libceph should plan to apply vendor updates as they become available.
What the vulnerability is (technical summary)
- Vulnerable component: kernel libceph; the code paths that parse and complete authentication messages.
- Vulnerability type: out‑of‑bounds read (CWE‑125).
- Affected function(s): the upstream fix references handle_auth_done()/process_auth_done() inside net/ceph/messenger_v2.c. The bug manifests when the code decodes a 32‑bit payload length from a message but does not then ensure that the decoded length is available in the buffer before using it — a classical missing bounds check.
Patch details: what changed in the code
The upstream stable‑tree patch adds two simple operations to the authentication completion path:- it decodes the 32‑bit payload length into payload_len using the same safe decoder used elsewhere in the function, and
- it immediately enforces that the rest of the message contains payload_len bytes (using a ceph_decode_need or equivalent helper), which returns an error rather than permitting a callout with an out‑of‑range pointer.
Severity, exploitability and impact
- Official publication date: 23 January 2026.
- CVSS v3.1 severity reported by NVD and several trackers: 7.1 (High) with vector CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:H — i.e., adjacent network/low complexity/low privileges, with high impact against availability and some confidentiality impact flagged by some vendors. Different vendor trackers have slightly different ratings (for example, Ubuntu initially marked the priority as medium while Amazon Linux and other trackers published an Important/High rating); these vendor‑level differences reflect local policy and distribution packaging details.
- Attack vector and privileges: most public analyses indicate this is not trivially remotely exploitable as a completely unauthenticated internet attack. The vector is described as adjacent network or local in vendor pages, which means an attacker typically needs network adjacency to the affected Ceph endpoint or a low‑privilege local account that can provoke the vulnerable code path (for example, by initiating or manipulating a Ceph session). This reduces broad remote threat surface but does not eliminate risk in multi‑tenant, cloud, or shared storage environments.
- Impact: the most likely impact is denial of service (DoS) — kernel crashes or oopses resulting from invalid reads and subsequent error paths. Some trackers also flag potential for limited information disclosure in certain contexts, although public evidence of data exfiltration via this specific bug has not appeared. As of the latest public advisories, there are no confirmed, publicly available exploits exploiting CVE‑2026‑22984 in the wild. EPSS/exploitation likelihood scores are low. That said, attackers have historically chained seemingly low‑level parsing bugs into privilege escalations or reliability attacks when other conditions are met, so conservatism is warranted.
Which systems are affected
Not every Linux installation is exposed. The risk depends on whether the kernel in use contains the vulnerable libceph code and whether the host participates in Ceph activity (client mounts, rbd devices, kernel clients talking to Ceph monitor/OSD). Public trackers and package trackers list affected kernel ranges and distribution statuses:- NVD and Debian trackers show kernels in a range of upstream versions as potentially affected; Debian has catalogued fixed and vulnerable package versions by release.
- Ubuntu’s advisory lists the CVE and the package statuses by release and assigns a distribution priority.
- SUSE and Amazon Linux trackers have issued notices and are producing or planning kernel updates for their supported channels; SUSE’s advisory also documents their internal severity mapping.
Vendor response and distribution status
Major distribution and vendor trackers have recorded the CVE and referenced the upstream kernel commits:- NVD and MITRE list the CVE and point to upstream kernel patches.
- Ubuntu published a security entry summarizing the fix and distribution status.
- Debian’s security tracker maps vulnerable and fixed kernel packages by release.
- SUSE, Amazon Linux and several other vendors have published advisory entries or are preparing fixes; the pace of backports varies by vendor and kernel tree.
Practical remediation steps (recommended)
- Identify affected systems
- Inventory Linux hosts that mount Ceph filesystems, use rbd block devices, or otherwise run Ceph client stacks, and check kernel versions and distribution kernel package versions against your vendor’s CVE tracker. Use package management queries (apt/yum/zypper) or host inventory tools to gather kernel versions.
- Apply vendor kernel updates
- Install the vendor/OS kernel update that contains the stable backport of the upstream fix. For many organizations that will mean installing a distribution kernel update and rebooting to load the new kernel. Vendors such as Ubuntu, Debian and SUSE have recorded fixed package versions in their trackers.
- For appliances and long‑running hosts
- If a reboot is operationally disruptive, consult your vendor for livepatch alternatives (kpatch, ksplice, livepatch kernels) or vendor-supplied hotpatches. Note that not all kernel fixes are available via livepatch mechanisms and some distributions require a full reboot to apply updated kernels safely.
- Test before mass rollout
- Because kernel changes can interact with in‑house drivers and custom modules, stage updates in test or canary environments first. Track for regressions tied to storage paths, rbd devices, and Ceph client workflows.
- Hardening and network controls
- Where feasible, limit network adjacency to Ceph control and monitor ports (segmentation, firewalling, and private management networks). Minimizing exposure reduces the practical attack surface in multi‑tenant or hybrid environments.
- Monitor for signs of exploitation
- Watch for unusual kernel oopses, Ceph client crashes, or authentication anomalies in Ceph logs during or after attempted connections. See detection guidance below.
Detection, hunting and indicators
Because the most likely impact of an out‑of‑bounds read in a kernel context is a crash or OOPS, detection focuses on stability, logs and unusual Ceph behavior:- Kernel logs: inspect dmesg and /var/log/kern.log for oopses, "BUG" traces, or stack traces referencing net/ceph/messenger_v2.c, handle_auth_done, process_auth_done, or libceph symbols. Kernel oopses will often include the call trace and the offending instruction pointer.
- Ceph client logs: check the Ceph client-side logs and system journal for repeated authentication errors, unexpected disconnects, or repeated session re‑establishment failures that coincide with kernel instability.
- Crash frequency: a sudden uptick in kernel crashes on nodes that interact with Ceph services — especially those that share a particular monitor or OSD — may indicate attempts to trigger parsing edges.
- KASAN/KMSAN results: in test environments, enabling memory safety sanitizers (KASAN/KMSAN) can reveal read/write errors during fuzzing or protocol stimulation. Vendors and maintainers typically use KASAN during patch verification.
Realistic risk scenarios and attack surface
- Multi‑tenant storage hosts: in shared hosting or cloud contexts where multiple tenants can mount or access Ceph endpoints, a low‑privilege actor with the ability to initiate client‑side authentication to a Ceph monitor could be problematic if the monitor or an OSD returns crafted data. Attackers might attempt to craft or coerce a Ceph peer into sending malformed authentication payloads. Because the code sits in the kernel client, a triggered crash affects host availability.
- Local users with access to Ceph client paths: on systems where unprivileged users can trigger rbd device operations or connect to Ceph services, local exploitation vectors may allow denial‑of‑service against the host kernel. In that model, traditional host‑level hardening and access controls reduce exposure.
- Cloud/VM images and distribution kernels: cloud images and vendor kernels that include libceph code are a distribution consideration — if a cloud image bundles a vulnerable kernel and is published to many customers, the exposure multiplies until images are refreshed. Vendors maintainers have recorded this CVE and are rolling updates; verify cloud provider attestations about which artifacts include the patched kernel.
Why the fix matters (analysis)
The fix is a textbook example of defense‑in‑depth: a single explicit bounds check prevents a class of memory‑safety bugs (out‑of‑bounds reads) that can produce crashes or, in unusual circumstances, information leakage. Because Ceph’s protocol parsing occurs in kernel context and affects block and filesystem semantics, the ability to cause a kernel crash is materially important for availability and reliability in production storage clusters.Two additional operational facts increase the importance of the patch:
- The fix is small and low‑risk to backport, so vendors can reasonably include it in many kernel branches without a large regression risk. That makes timely patching practical.
- Even though public exploitation evidence is absent, protocol parsing bugs are an attractive target for attackers because they can sometimes be chained with other vulnerabilities or misconfigurations to produce greater outcomes than a stand‑alone crash. The conservative posture is to patch promptly.
Caveats and unverifiable aspects (what we don’t know)
- No public exploit samples or proof‑of‑concepts have been disclosed as of the latest advisories; public trackers list low EPSS/exploitability scores, suggesting little observed weaponization to date. However, absence of public exploit code does not prove absence of targeted or private exploitation. Administrators should assume the vulnerability is actionableto risk posture.
- Distribution‑specific exposure depends on exact kernel package versions and vendor backporting policies. Always check your vendor’s package tracker for precise affected/fixed versions before making operational decisions. Debian, SUSE, Ubuntu and others have published per‑release status pages.
Quick checklist for administrators
- Inventory: find hosts that mount Ceph or use rbd, and list kernel versions.
- Patch: apply vendor kernel updates that contain the upstream fix; reboot where necessary.
- Temporary mitigation: restrict access to Ceph monitor/OSD traffic with network segmentation or firewall rules if immediate kernel updates are not possible.
- Monitor: watch dmesg, kernel logs and Ceph client logs for crashes or authentication anomalies.
- Test: validate in staging before broad rollout, especially on systems with specialized kernel modules.
Broader context: libceph maintenance and similar fixes
This CVE is one in a sequence of careful libceph hardening and memory‑safety fixes that kernel maintainers and community researchers have addressed over recent months. Upstream kernel maintainers have prioritized small, defensive corrections (bounds checks, safe decoders, and removal of fragile assertions) to reduce the risk that malformed network messages can cause kernel crashes or memory corruption. The community’s approach — small, reviewable fixes merged into stable trees — reduces regression risk and allows vendors to backport quickly. Forum and tracker activity shows a cluster of related libceph CVEs and fixes in recent updates, underscoring the attention the code path has received.Final assessment
CVE‑2026‑22984 is a meaningful but contained kernel vulnerability: the fix is small, the attack surface is specific to Ceph client activity, and there is no public evidence of exploitation in the wild at the time of writing. That said, the potential for availability impact (kernel crashes) in storage‑heavy environments — where uptime and data access are critical — makes this a high‑priority remediation for affected hosts.Action plan in order of priority:
- Identify Ceph‑using hosts and check vendor trackers for fixed kernel package versions.
- Apply vendor kernel updates (or vendor hotpatch/livepatch where available), test, and reboot if required.
- For environments where rebooting is infeasible immediately, reduce network exposure of Ceph control and monitor ports and escalate patch schedules.
Conclusion: treat CVE‑2026‑22984 as actionable for any host that participates in Ceph client activity; apply vendor updates as they become available, monitor for related kernel oopses, and use network controls to reduce exposure while you update.
Source: MSRC Security Update Guide - Microsoft Security Response Center